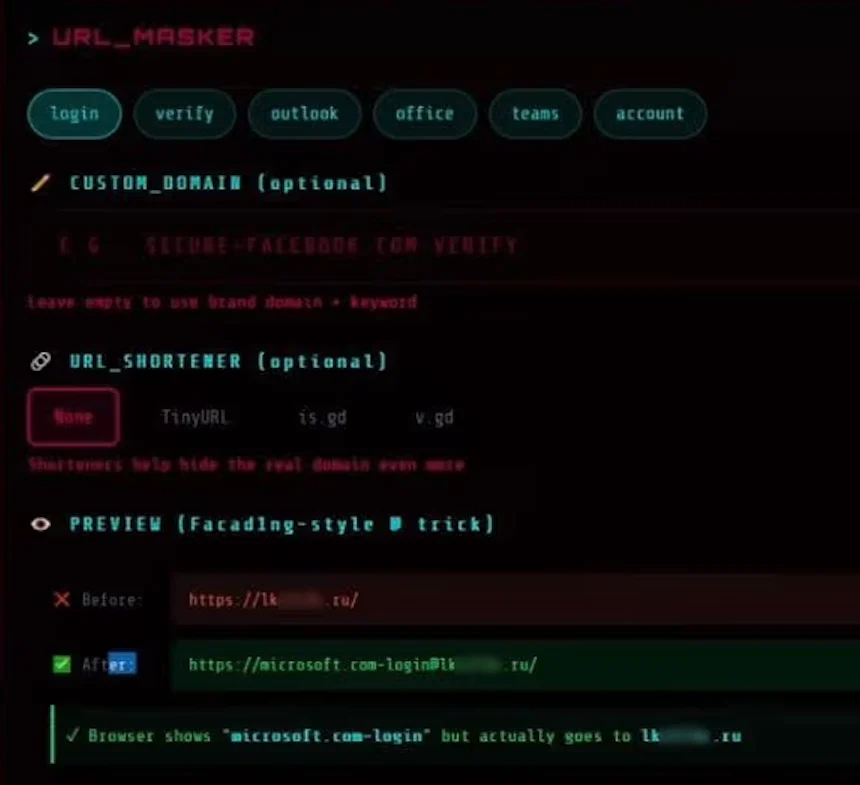
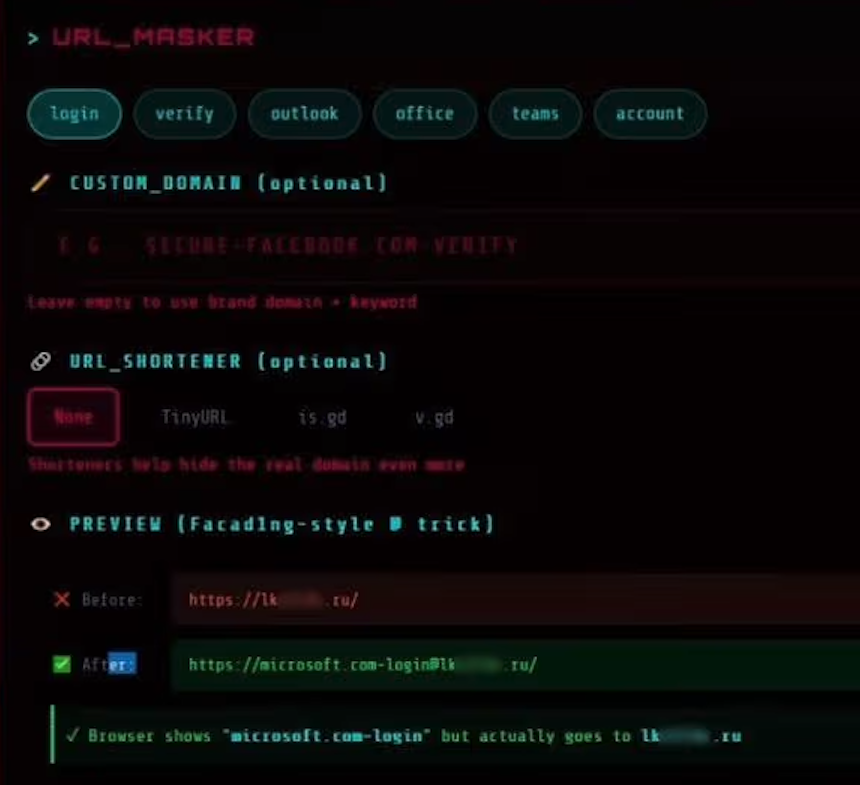
The core innovation of Starkiller lies in its ability to circumvent the common pitfalls faced by phishing operators. Historically, phishing websites were often easily identifiable as fake copies, quickly flagged and taken down by security researchers and anti-abuse teams. However, Starkiller sidesteps this by loading the actual login page of the target brand directly. This is achieved through cleverly disguised URLs that manipulate how web browsers interpret addresses. For instance, a phishing link targeting Microsoft might appear as "login.microsoft.com@[malicious/shortened URL here]". The "@" symbol in URLs is historically interpreted by browsers as a separator, with everything preceding it being treated as the username and everything after it as the actual domain. Starkiller exploits this by directing the user’s browser to a malicious domain that, from the victim’s perspective, still looks like the legitimate login page. This initial deception is crucial for luring victims into the trap.
The underlying technology powering Starkiller is equally impressive, reflecting a growing trend towards sophisticated, "enterprise-style" tooling within the cybercrime underground. According to an analysis by the cybersecurity firm Abnormal AI, Starkiller allows its customers to select a target brand from a list that includes major players like Apple, Facebook, Google, and Microsoft. Once a brand is chosen, the service generates a deceptive URL designed to visually mimic the legitimate domain while routing all traffic through the attacker’s infrastructure. This infrastructure is built using advanced technologies, including Docker containers that run headless Chrome browser instances. These instances load the real login page of the targeted service.
Abnormal AI researchers Callie Baron and Piotr Wojtyla detailed the mechanics of Starkiller in a blog post, explaining that the Docker container acts as a "man-in-the-middle reverse proxy." This means that every piece of data entered by the victim – keystrokes, form submissions, and session tokens – is first routed through the attacker’s controlled infrastructure. This data is meticulously logged, providing attackers with a comprehensive record of the victim’s interaction. Furthermore, Starkiller offers real-time session monitoring, allowing attackers to essentially "live-stream" the victim’s screen as they navigate the phishing page. This level of insight provides attackers with an unprecedented view into their target’s online activity.
The capabilities of Starkiller extend far beyond simple credential harvesting. The platform is equipped with a suite of advanced features designed to maximize the success and impact of phishing campaigns. This includes comprehensive keylogger functionality to capture every keystroke, the ability to steal cookies and session tokens for direct account takeover, and geo-tracking of victims. Perhaps most alarmingly, Starkiller provides automated Telegram alerts whenever new credentials are captured. This immediate notification system allows attackers to act swiftly, often before the victim even realizes they have been compromised. The service also includes campaign analytics, offering operators metrics such as visit counts, conversion rates, and performance graphs – features typically found in legitimate Software-as-a-Service (SaaS) platforms. This familiar interface lowers the barrier to entry for novice cybercriminals, making advanced attack capabilities accessible to a wider audience.
One of the most significant advancements demonstrated by Starkiller is its ability to effectively bypass multi-factor authentication (MFA). MFA is designed to add an extra layer of security by requiring users to provide a second form of verification, such as a code from a mobile app or an SMS message. Starkiller achieves this bypass by relaying the entire authentication flow in real-time. When a victim enters their username and password on the phishing page, Starkiller forwards this information to the legitimate website. Crucially, it also intercepts and relays the MFA code provided by the victim to the legitimate site. The legitimate site then authenticates the user and issues session cookies and tokens. Starkiller captures these authenticated session cookies and tokens, granting the attacker direct access to the compromised account. In essence, the MFA mechanism functions as designed, but the attacker is able to exploit the legitimate authentication process by acting as a real-time proxy. This renders MFA protections ineffective, even though the technology itself is functioning correctly.
The Starkiller service is part of a broader ecosystem of cybercrime offerings provided by a threat group known as "Jinkusu." This group actively maintains a user forum where customers can discuss techniques, request new features, and seek support for their phishing deployments. Jinkusu also offers additional "a-la-carte" features, such as tools to harvest email addresses and contact information from compromised sessions. This data can then be used to build more targeted lists for subsequent phishing campaigns, creating a continuous cycle of attacks.
The implications of Starkiller are profound for the cybersecurity industry. This service represents a significant evolution in phishing techniques, moving beyond rudimentary copy-paste operations to sophisticated, proxy-based attacks. The apparent success of Starkiller is likely to inspire other enterprising cybercriminals, leading to the proliferation of similar services. By avoiding the costs and complexities associated with managing multiple phishing domains and employing constant evasive maneuvers against detection systems, Starkiller offers a more efficient and effective phishing solution. Traditional detection methods like domain blocklisting and static page analysis become largely obsolete when the phishing service dynamically loads the legitimate website.
Abnormal AI researchers emphasize that Starkiller exemplifies a broader trend towards commoditized, enterprise-grade tooling within the cybercrime world. This shift significantly lowers the barrier to entry for individuals with limited technical expertise, granting them access to attack capabilities that were previously the domain of highly skilled threat actors. The report concludes that the combination of URL masking, session hijacking, and MFA bypass provided by Starkiller empowers low-skill cybercriminals with potent attack vectors, posing a considerable challenge to current cybersecurity defenses. The ongoing development and adoption of such advanced phishing services underscore the ever-evolving nature of cyber threats and the constant need for innovative security solutions.









