In a significant disruption that highlights the evolving tactics of sophisticated botnets, the massive Internet of Things (IoT) botnet known as Kimwolf has overwhelmed and severely degraded The Invisible Internet Project (I2P), a decentralized, encrypted communications network renowned for its anonymity and security features. This incident, which began approximately a week ago, saw I2P users reporting widespread network instability and connectivity issues. The timing of these disruptions coincided precisely with attempts by Kimwolf’s operators to leverage I2P as a fallback command and control (C2) infrastructure, aiming to evade ongoing takedown efforts targeting their primary C2 servers.
Kimwolf, a botnet that first emerged in late 2025, rapidly escalated its reach, compromising millions of internet-connected devices. These compromised systems, primarily insecure IoT devices such as TV streaming boxes, digital picture frames, and routers, were repurposed into an expansive network of relays for malicious traffic. The botnet has been historically associated with launching distributed denial-of-service (DDoS) attacks of abnormally large scale, as previously reported in related cybersecurity analyses.
I2P, by its design, offers users a robust platform for anonymous communication and information sharing. It operates by routing data through multiple layers of encryption across a network of volunteer-operated nodes. This intricate routing mechanism effectively obscures both the sender’s and receiver’s geographical locations, creating a secure and censorship-resistant environment conducive to private websites, messaging, and data sharing. The I2P website itself elaborates on these core functionalities, emphasizing its commitment to user privacy and security.
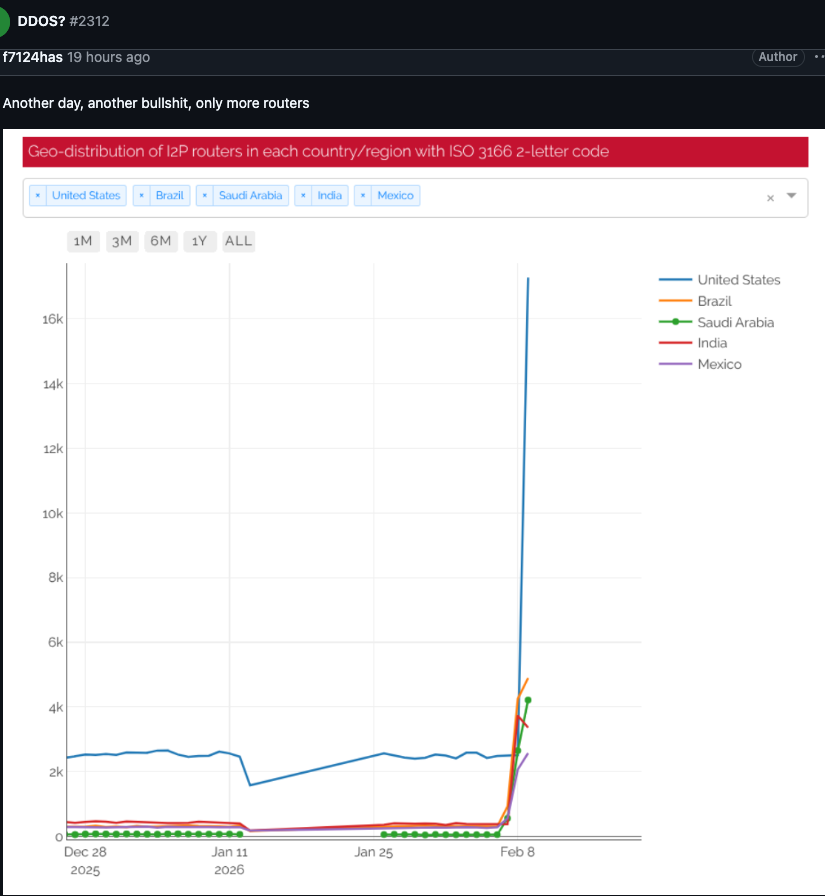
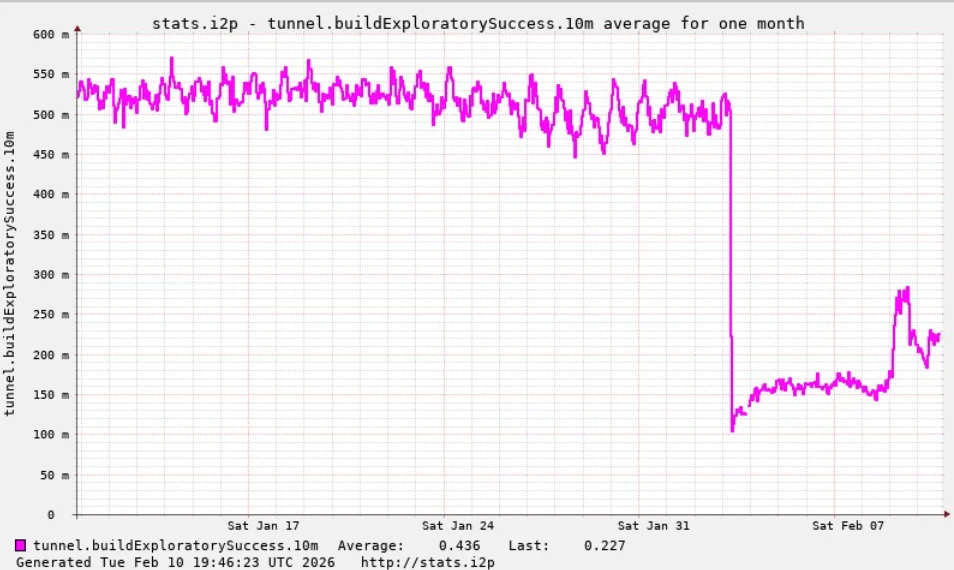
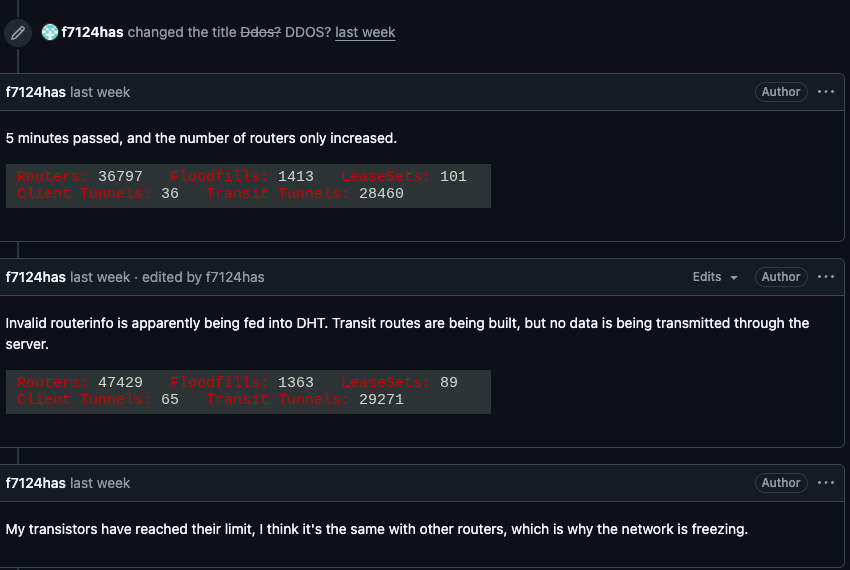
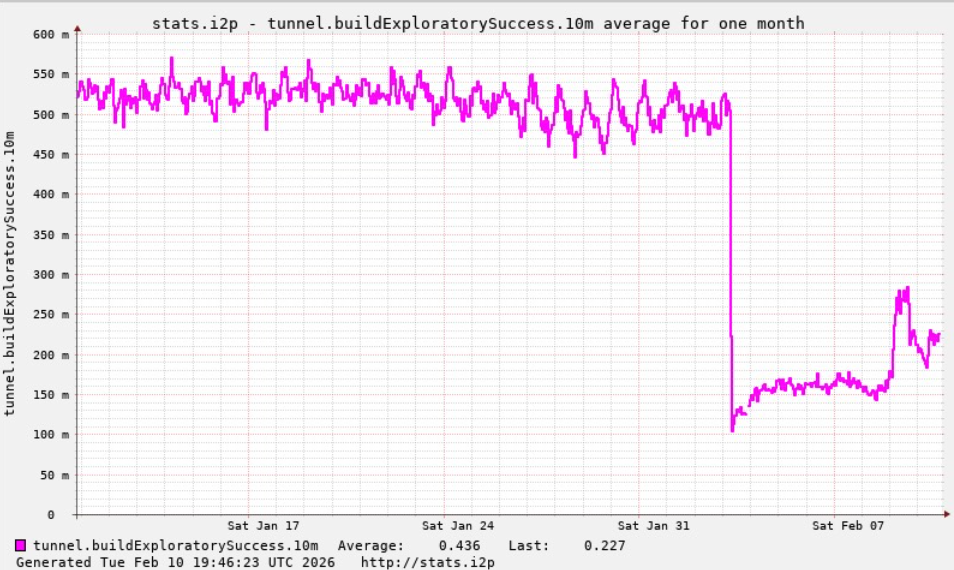
The crisis within I2P began to surface on February 3rd, when users began voicing their concerns on the project’s GitHub page. Reports detailed an alarming surge in the number of compromised routers attempting to join the network, leading to an overwhelming influx of traffic. This sudden and massive expansion of new, non-functional nodes effectively crippled the network’s ability to facilitate legitimate communications, preventing existing users from connecting with established, functional nodes. Users described a rapid increase in new systems joining the network that were incapable of transmitting data, ultimately leading to a complete inability for many to connect. One I2P user, observing the severity of the issue, questioned if the network was under attack, receiving a reply that confirmed their suspicions: "Looks like it. My physical router freezes when the number of connections exceeds 60,000."
Compellingly, the same day I2P users began experiencing these critical outages, the individuals orchestrating the Kimwolf botnet made a public announcement on their Discord channel. They admitted to having inadvertently disrupted I2P, detailing their plan to integrate approximately 700,000 Kimwolf-infected bots as nodes within the I2P network. This revelation confirmed the direct link between the botnet’s operational needs and the network’s degradation.
While Kimwolf is primarily recognized for its capacity to launch potent DDoS attacks, the network disruptions experienced by I2P are a classic example of a "Sybil attack." This type of attack, prevalent in peer-to-peer networks, involves a single malicious entity establishing and controlling a large number of pseudonymous identities or nodes to disrupt the system’s integrity. In this instance, the sheer volume of Kimwolf-infected routers attempting to join I2P far exceeded the network’s normal operational capacity. The I2P Wikipedia entry indicates that the network typically comprises around 55,000 computers globally, with each participant serving dual roles as a router and a client.
However, Lance James, founder of the New York City-based cybersecurity consultancy Unit 221B and the original founder of I2P, provided a more current estimate, stating that the I2P network currently consists of between 15,000 and 20,000 active devices on any given day. This suggests the influx of Kimwolf bots represented a disproportionately massive addition to the network’s actual operational size.
Benjamin Brundage, founder of Synthient, a startup specializing in tracking proxy services and the first to document Kimwolf’s unique propagation techniques, explained the strategic motivation behind the botnet operators’ actions. Brundage indicated that the Kimwolf operators have been actively attempting to construct a command and control network that is resistant to takedown attempts by collaborative security firms and network operators. Their experimentation with I2P and the similar anonymity network Tor was an effort to establish a resilient backup C2 infrastructure. While Tor has not recently experienced widespread disruptions, the Kimwolf operators’ foray into I2P had immediate and significant consequences.
Brundage elaborated, stating, "I don’t think their goal is to take I2P down. It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts." This underscores that the disruption was a byproduct of a strategic maneuver rather than a direct act of sabotage against I2P itself.
The Kimwolf botnet had previously created significant challenges for cybersecurity firms, notably Cloudflare, in late 2025. At that time, the botnet instructed millions of compromised devices to utilize Cloudflare’s DNS settings, leading to control domains associated with Kimwolf repeatedly outranking major entities like Amazon, Apple, Google, and Microsoft in Cloudflare’s public rankings of the most frequently requested websites.
Regarding the current state of I2P, Lance James reported that the network is still operating at approximately half of its usual capacity. A new software release is reportedly being deployed, which is expected to introduce stability improvements over the course of the following week.
On a more positive note for the cybersecurity community, Brundage highlighted that Kimwolf’s leadership appears to have recently alienated some of its more skilled developers and operators. This internal discord may have contributed to the "rookie mistake" observed this past week, which resulted in a significant decline of over 600,000 infected systems within the botnet’s overall count. Brundage characterized the situation as one where the operators are "just testing stuff, like running experiments in production." He concluded, "But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing." This suggests a potential unraveling of the Kimwolf botnet’s operational sophistication, driven by internal conflicts and a lack of experienced personnel.









