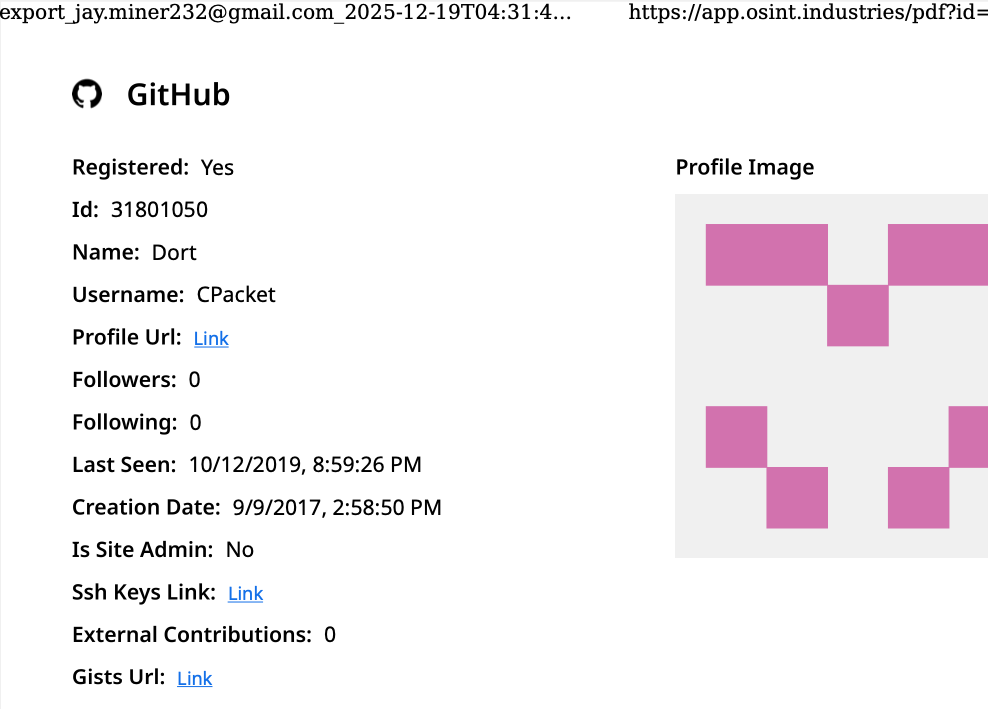
A public "dox" that surfaced in 2020 alleged that Dort was a teenager from Canada, born in August 2003, who operated under the aliases "CPacket" and "M1ce." Further investigation on the open-source intelligence platform OSINT Industries reveals a GitHub account associated with both the names Dort and CPacket. This account, created in 2017, was linked to the email address [email protected].
The cyber intelligence firm Intel 471 has provided further context, noting that the email address [email protected] was utilized between 2015 and 2019 to establish accounts on several cybercrime forums. These included Nulled, where the username was "Uubuntuu," and Cracked, where the user was "Dorted." Intel 471’s findings indicate that both of these accounts originated from the same Internet Protocol (IP) address associated with Rogers Canada, specifically 99.241.112.24.
Dort was once a highly engaged participant in the popular Microsoft game Minecraft. In this virtual arena, Dort achieved a degree of notoriety for developing "Dortware," a suite of software designed to facilitate cheating within the game. However, this early involvement in game modification appears to have been a precursor to more significant criminal endeavors, as Dort transitioned from manipulating game mechanics to enabling far more serious illicit activities.
Another alias associated with Dort is "DortDev." This identity was active in March 2022 on the chat server belonging to the notorious cybercrime collective known as LAPSUS$. Under this guise, Dort offered services for the creation of temporary email addresses and advertised "Dortsolver," a tool engineered to circumvent various CAPTCHA services, which are typically implemented to prevent automated abuse of online accounts. Both of these offerings were promoted in 2022 on SIM Land, a Telegram channel dedicated to SIM-swapping and account takeover schemes.
The cyber intelligence firm Flashpoint has cataloged posts from 2022 on SIM Land authored by Dort. These records indicate that Dort developed the disposable email and CAPTCHA bypass services in collaboration with another hacker who went by the handle "Qoft." In a conversation from 2022, Qoft referred to Dort as their "exclusive business partner," stating, "I legit just work with Jacob." In the same exchange, Qoft boasted that the duo had successfully stolen over $250,000 worth of Microsoft Xbox Game Pass accounts by creating a program that generated Game Pass identities in bulk, utilizing compromised payment card data.
The identity of "Jacob," whom Qoft identified as their business partner, has also been a subject of investigation. The breach tracking service Constella Intelligence has discovered that the password associated with [email protected] was reused by only one other email address: [email protected]. This discovery aligns with the 2020 doxing information that indicated Dort’s date of birth was August 2003 (8/03).
A search of [email protected] on DomainTools.com reveals its use in 2015 to register several domains themed around Minecraft. These registrations were all attributed to a Jacob Butler residing in Ottawa, Canada, and were associated with the Ottawa phone number 613-909-9727.
Constella Intelligence further indicates that [email protected] was employed to create an account on the hacker forum Nulled in 2016. Additionally, the same email address was used to establish the Minecraft account name "M1CE." By analyzing the password used for their Nulled account, it was found to be shared with the email addresses [email protected] and [email protected]. The latter email address is linked to a domain belonging to the Ottawa-Carleton District School Board, suggesting a potential connection to an educational institution.
Data compiled by the breach tracking service Spycloud suggests that at one point, Jacob Butler shared a computer with his mother and a sibling. This shared access might explain why their email accounts were linked to the password "jacobsplugs." Neither Jacob Butler nor any other members of the Butler household responded to requests for comment on these findings.
The open-source intelligence service Epieos has identified that [email protected] was used to create the GitHub account "MemeClient." Concurrently, Flashpoint has indexed a deleted anonymous post on Pastebin.com from 2017, which declared that MemeClient was the creation of a user named CPacket—one of Dort’s earlier online pseudonyms.
The intensity of Dort’s animosity stems from a January 2, 2026, article published by KrebsOnSecurity titled "The Kimwolf Botnet is Stalking Your Local Network." This report detailed research conducted by Benjamin Brundage, the founder of the proxy tracking service Synthient. Brundage had uncovered that the operators of the Kimwolf botnet were exploiting a little-known vulnerability in residential proxy services. This exploit allowed them to infect poorly secured devices, such as TV boxes and digital photo frames, that were connected to the internal, private networks of proxy endpoints.
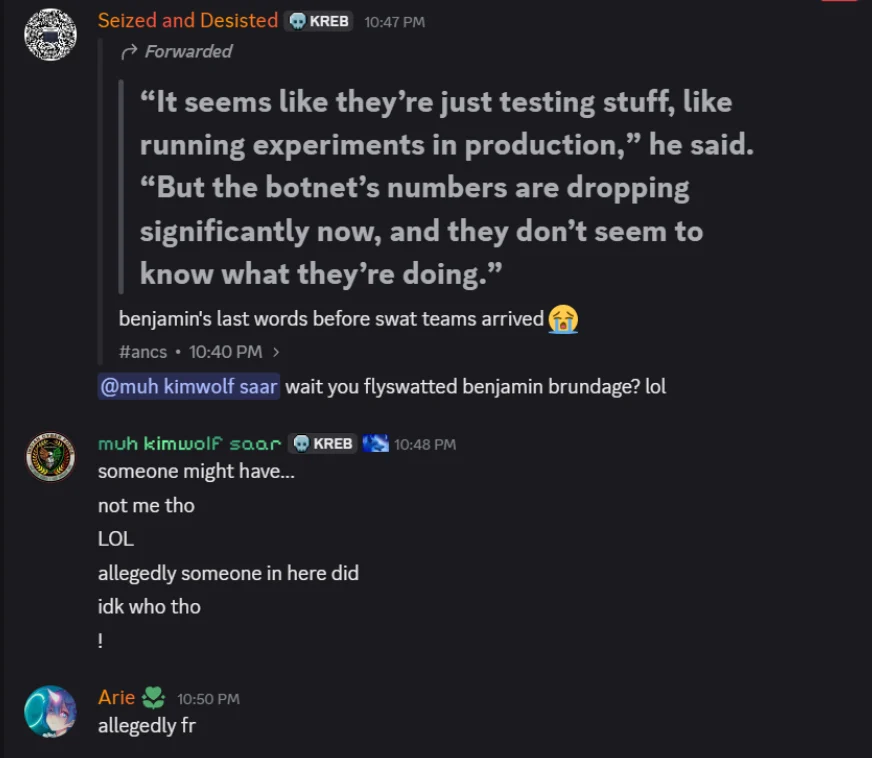
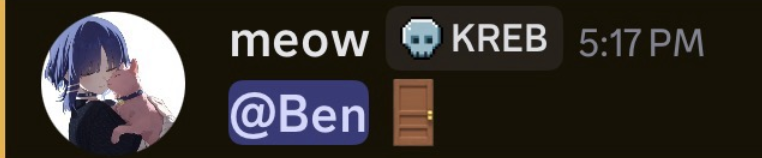
By the time this article was published, Brundage had already notified most of the affected proxy providers, who subsequently patched the vulnerabilities in their systems. This remediation effort significantly hampered Kimwolf’s ability to propagate. Within hours of the article’s release, Dort established a Discord server bearing this author’s name, which began publishing personal information and issuing violent threats against Brundage, KrebsOnSecurity, and other individuals.
Last week, Dort and associates utilized this same Discord server, then named "Krebs’s Koinbase Kallers," to orchestrate a swatting attack against Brundage. They again disseminated his home address and personal details. Brundage informed KrebsOnSecurity that local law enforcement officers visited his residence in response to a swatting hoax. This incident occurred concurrently with another server member posting an image of a door emoji and further taunting Brundage.
Subsequently, a participant on the server linked to a cringeworthy and explicit SoundCloud "diss track" recorded by DortDev. The track featured a pinned message from Dort stating, "Ur dead nigga. u better watch ur fucking back. sleep with one eye open. bitch." The diss track’s lyrics further intensified the threats, with lines like, "It’s a pretty hefty penny for a new front door. If his head doesn’t get blown off by SWAT officers. What’s it like not having a front door?" The implication was clear: Dort was actively wishing for and potentially inciting violence against Brundage.
With any luck, Dort will soon have an opportunity to provide firsthand accounts of such experiences.
Update, 10:29 a.m.: Jacob Butler has responded to requests for comment, engaging in a brief telephone conversation with KrebsOnSecurity. Butler stated that he had not noticed earlier requests for comment because he has largely been offline since 2021, following multiple swatting incidents at his home. He acknowledged creating and distributing a Minecraft cheat program in the past but asserted that he has not played the game in years and has not been involved in Dortsolver or any other activities attributed to the Dort nickname since 2021.
"It was a really old cheat and I don’t remember the name of it," Butler said of his Minecraft modification. "I’m very stressed, man. I don’t know if people are going to swat me again or what. After that, I pretty much walked away from everything, logged off and said fuck that. I don’t go online anymore. I don’t know why people would still be going after me, to be completely honest."
When questioned about his current occupation, Butler stated that he primarily stays at home and assists his mother, citing struggles with autism and social interaction. He maintains that an individual must have compromised one or more of his old accounts and is impersonating him online as Dort.
"Someone is actually probably impersonating me, and now I’m really worried," Butler said. "This is making me relive everything."
However, there are inconsistencies in Butler’s timeline. For instance, the voice of Jacob in the phone conversation bore a striking resemblance to the voice of the Jacob/Dort heard in a September 2022 Clash of Code competition between Dort and another coder, in which Dort ultimately lost. Around the six-minute and ten-second mark of the recording, Dort erupts into a string of profanities that mirrors the language used in the diss rap posted by Dortdev threatening Brundage. Dort’s voice is audible again around the sixteen-minute mark, and at approximately 26:00, Dort threatens to swat his opponent.
Butler, however, claims that the voice of Dort is not his own but rather that of an impersonator who likely cloned his voice. "I would like to clarify that was absolutely not me," Butler stated. "There must be someone using a voice changer. Or something of the sorts. Because people were cloning my voice before and sending audio clips of ‘me’ saying outrageous stuff."
Further reading on related topics:
- Jan. 8, 2026: Who Benefited from the Aisuru and Kimwolf Botnets?
- Jan. 20, 2026: Kimwolf Botnet Lurking in Corporate, Govt. Networks
- Jan. 26, 2026: Who Operates the Badbox 2.0 Botnet?
- Feb. 11, 2026: Kimwolf Botnet Swamps Anonymity Network I2P
- Mar. 19, 2026: Feds Disrupt IoT Botnets Behind Huge DDoS Attacks









