Ghosh, alongside Suryansh Upadhyay, who recently completed his doctorate in electrical engineering at Penn State, has co-authored a seminal research paper that meticulously details several critical security vulnerabilities inherent in contemporary quantum computing systems. Published online in the prestigious Proceedings of the Institute of Electrical and Electronics Engineers (IEEE), their study compellingly argues that the robust security of quantum computers cannot solely rely on software fortifications. Instead, the physical hardware underpinning these complex systems must be an integral component of any comprehensive defense strategy.
In an insightful Question and Answer session, Ghosh and Upadhyay elaborated on the fundamental principles of quantum computation, elucidated the unique security challenges they present, and outlined actionable steps that developers can implement to fortify these machines for their impending widespread adoption.
Q: What fundamentally differentiates a quantum computer from a conventional, traditional computer?
Ghosh: Traditional computing operates on the principle of bits, which can be visualized as light switches capable of being in either an "on" or "off" state. These states are assigned binary values: one for "on" and zero for "off." The process of programming a traditional computer involves employing algorithms, essentially sophisticated sets of instructions or educated guesses, to devise the most optimal solution to a given problem. This solution is then compiled into machine-level instructions – specific directions dictating which bits must represent one and which must represent zero – that the computer executes to perform a task.
Quantum computers, in contrast, are built upon the concept of quantum bits, or qubits. Qubits possess a far greater degree of versatility than their classical counterparts. They can represent not only a one or a zero, but also a combination of both states simultaneously, a phenomenon known as superposition. Furthermore, qubits can be intrinsically linked to one another through a process called entanglement. By harnessing the power of superposition and entanglement in their decision-making processes, quantum computers can process an exponentially larger volume of data compared to bit-powered computing systems, even when utilizing an equivalent number of qubits. This inherent capability makes quantum computers exceptionally valuable for optimizing workflows across a multitude of industries. For instance, in the pharmaceutical sector, quantum computing can drastically accelerate the analysis of vast datasets and the prediction of the efficacy of potential new drug candidates. This streamlined research and development process has the potential to save pharmaceutical companies billions of dollars and decades of intensive research, testing, and fabrication efforts.
Q: What are the primary security vulnerabilities currently confronting quantum computers?
Upadhyay: Presently, there is a significant lack of efficient methods for verifying the integrity of the programs and compilers used by quantum computers at scale, many of which are developed by third-party entities. This deficiency leaves users’ sensitive corporate and personal information exposed to potential theft, tampering, and unauthorized reverse engineering.
A substantial number of quantum computing algorithms embed businesses’ proprietary intellectual property directly within their circuits. These circuits are meticulously designed to process highly specialized problems involving sensitive client data and other confidential information. If these circuits are compromised or exposed, malicious actors could potentially extract invaluable company-created algorithms, reveal sensitive financial positions, or gain access to critical infrastructure details. Moreover, the very interconnectedness that enables qubits to operate with such remarkable efficiency inadvertently introduces a security vulnerability. Unwanted entanglement, a phenomenon known as crosstalk, can lead to inadvertent information leakage or disrupt computing functions when multiple users share the same quantum processor. This presents a unique challenge, as the core mechanisms that grant quantum computers their power also create avenues for potential breaches.
Q: What measures are current commercial quantum providers taking to address these burgeoning security concerns? Are they able to leverage the same security methodologies employed in traditional, classical computing systems?
Upadhyay: Classical security methods are fundamentally inadequate for securing quantum systems because quantum systems operate on principles that are drastically different from those of traditional computers. Consequently, we believe that many companies are ill-prepared to effectively address these emerging security faults. Currently, commercial quantum providers are primarily focused on ensuring the reliability and operational effectiveness of their systems. While advancements in system optimization can indirectly mitigate some security vulnerabilities, the unique assets inherent to quantum computing – such as circuit topology, encoded data, and hardware-encoded intellectual property systems – generally lack comprehensive end-to-end protection. Although quantum computers are still a nascent technology, which currently offers less incentive for attackers to target them, this landscape is rapidly evolving. As these powerful machines become increasingly integrated into various industries and our daily lives, they will undoubtedly transform into prime targets for sophisticated cyber threats. The current lack of robust, quantum-specific security frameworks leaves a significant gap that needs urgent attention.
Q: How can developers enhance the security posture of quantum computers?
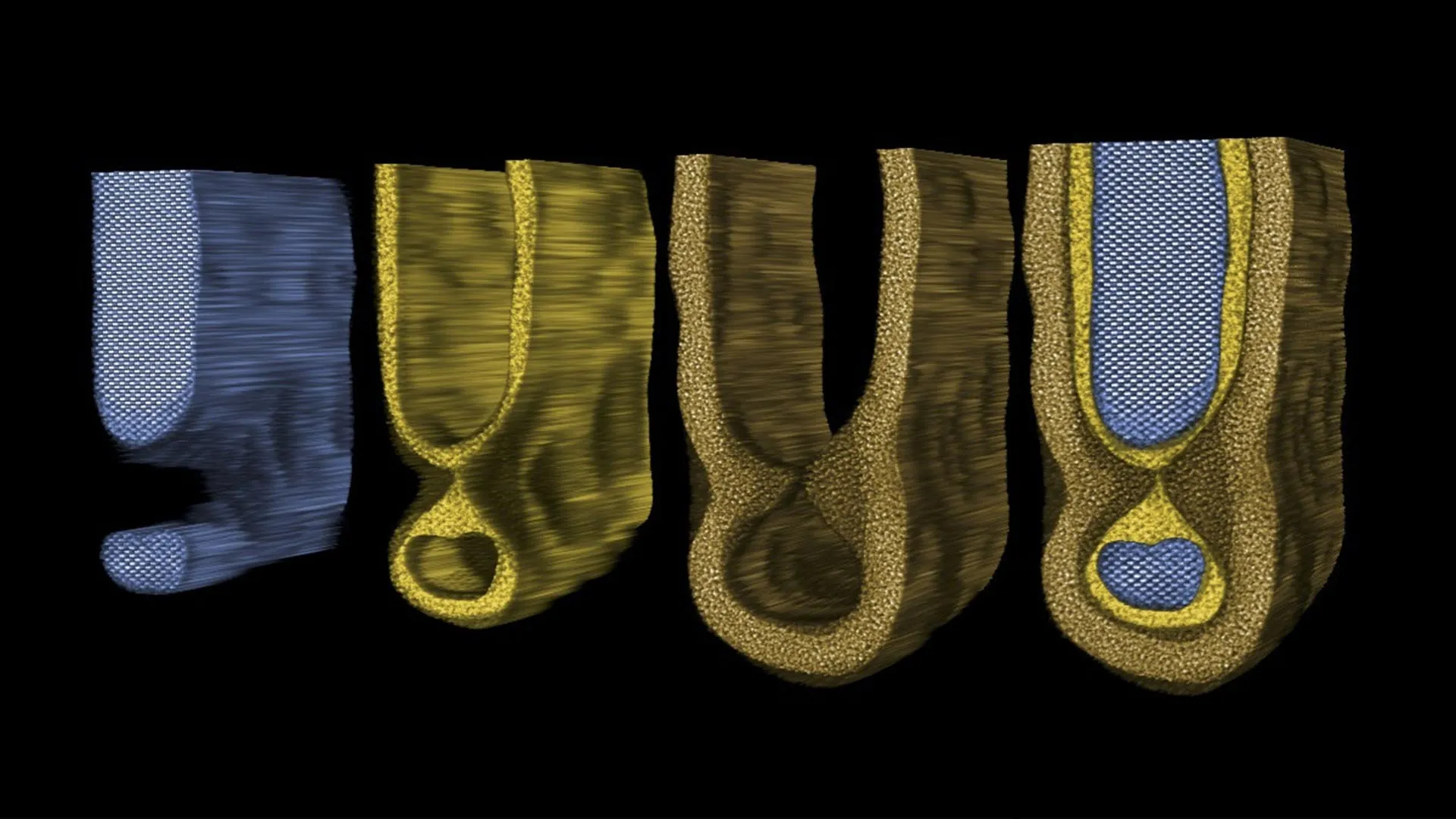
Ghosh: Safeguarding quantum computers requires a holistic, ground-up approach. At the foundational device level, developers must prioritize mitigating crosstalk and other sources of noise – external interference that can compromise information integrity or impede efficient data transfer. This involves designing hardware with inherent resilience to environmental factors and implementing sophisticated noise-reduction techniques.
At the circuit level, the implementation of advanced techniques such as scrambling and robust information encoding is paramount. These methods are crucial for protecting the sensitive data that is intrinsically embedded within the quantum system’s architecture. By obscuring and safeguarding the data at its most fundamental level, developers can create a significant barrier against unauthorized access and manipulation.
At the system level, a strategy of hardware compartmentalization is essential. This involves logically dividing sensitive business data into distinct segments. Users should then be granted specific access privileges based on their defined roles within the organization, thereby adding an extra layer of protection to critical information. Furthermore, the development of novel software techniques and extensions is vital. These innovations will be instrumental in detecting and fortifying quantum programs against an ever-evolving array of security threats, ensuring that the software running on these powerful machines is as secure as the hardware itself.
Our overarching aspiration with this research is to introduce experts from diverse fields – including mathematics, computer science, engineering, and physics – to the critical domain of quantum security. By fostering interdisciplinary collaboration and knowledge sharing, we aim to empower these researchers to make significant and effective contributions to this rapidly expanding and increasingly vital field.
Additional co-authors on this groundbreaking work include Abdullah Ash Saki, who recently earned his doctorate in electrical engineering from Penn State. This research received vital support from the U.S. National Science Foundation and Intel, underscoring the significance and potential impact of this investigation into the security of future computing paradigms. The implications of these findings are far-reaching, potentially shaping the future of cybersecurity in an era defined by quantum advancements.