Russian military intelligence operatives, operating under the guise of the "Forest Blizzard" threat group, have orchestrated a sophisticated and largely undetected espionage campaign by exploiting vulnerabilities in outdated internet routers to pilfer authentication tokens from Microsoft Office users across a vast network of over 18,000 compromised devices. This audacious operation, which has drawn sharp warnings from cybersecurity experts, allowed state-sponsored hackers to surreptitiously harvest sensitive credentials without deploying any malicious software or code, effectively bypassing conventional security measures. Microsoft, in a detailed security advisory, confirmed the broad scope of the campaign, identifying over 200 organizations and 5,000 consumer devices ensnared in this remarkably simple yet effective spying apparatus orchestrated by a Russia-backed actor.
Forest Blizzard, also known by the more notorious monikers APT28 and Fancy Bear, is widely attributed to the Russian General Staff’s Main Intelligence Directorate (GRU). This same group gained notoriety for its alleged interference in the 2016 U.S. presidential election through the compromise of the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee. The current operation, however, takes a different, more insidious approach.
Researchers at Black Lotus Labs, the threat intelligence division of the global internet backbone provider Lumen, meticulously documented Forest Blizzard’s activities. They observed that at its peak in December 2025, the surveillance network had infiltrated over 18,000 internet routers. The vast majority of these compromised devices were either end-of-life models, no longer receiving security updates, or significantly lagging in their patch management. A comprehensive report from Lumen details that the primary targets of this campaign were government agencies, including ministries of foreign affairs, law enforcement bodies, and third-party email providers, underscoring the strategic importance of the intelligence being sought.
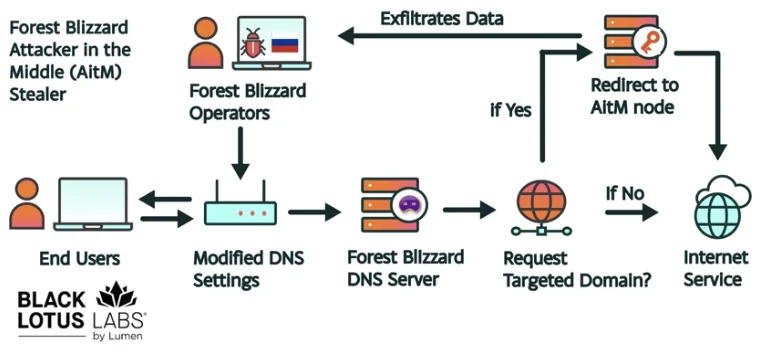
Ryan English, a security engineer at Black Lotus Labs, elucidated the ingenious, albeit low-tech, methodology employed by the GRU hackers. Rather than resorting to complex malware deployments, they exploited well-known vulnerabilities in common Small Office/Home Office (SOHO) routers, predominantly from manufacturers like Mikrotik and TP-Link. These exploits allowed them to modify the Domain Name System (DNS) settings of the routers, redirecting all DNS requests to servers under the attackers’ control.
The United Kingdom’s National Cyber Security Centre (NCSC), in a parallel advisory, detailed how these Russian cyber actors are leveraging router compromises for DNS hijacking operations. DNS acts as the internet’s phonebook, translating human-readable website names into numerical IP addresses. In a DNS hijacking attack, malicious actors intercept this process, effectively rerouting unsuspecting users to imposter websites designed to steal login credentials and other sensitive data.
English explained that the compromised routers were reconfigured to point to a network of virtual private servers managed by Forest Blizzard. Crucially, this configuration allowed the attackers to propagate their malicious DNS settings to every device connected to the local network. From this vantage point, they could intercept all OAuth authentication tokens transmitted by users. These tokens are a critical component of modern authentication systems, often issued after a user has successfully logged in and passed multi-factor authentication. By capturing these tokens, Forest Blizzard could gain direct access to victim accounts without the need to phish for individual credentials or one-time codes, representing a significant bypass of common security protocols.

"Everyone is looking for some sophisticated malware to drop something on your mobile devices or something," English remarked, highlighting the deceptive simplicity of the attack. "These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done."
Microsoft categorizes Forest Blizzard’s activity as DNS hijacking used to facilitate "post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." While targeting SOHO devices is not a novel tactic, Microsoft noted this as the first instance of Forest Blizzard employing DNS hijacking at such a massive scale to support AiTM of TLS connections after exploiting edge devices.
Danny Adamitis, another engineer at Black Lotus Labs, anticipates how Forest Blizzard might adapt in response to the increased scrutiny of their espionage operation. He pointed to a similar NCSC report in August 2025, after which the group rapidly shifted its tactics. Previously, Forest Blizzard had used malware to control a smaller, more targeted group of compromised routers. However, in the immediate aftermath of the NCSC advisory, the group abandoned the malware approach in favor of the widespread DNS redirection strategy now being exposed.
"Before the last NCSC report came out, they used this capability in very limited instances," Adamitis stated. "After the report was released, they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable."
The vulnerability of routers from manufacturers like TP-Link has not gone unnoticed by regulatory bodies. In the United States, TP-Link had previously faced discussions of a complete ban. More broadly, on March 23rd, the U.S. Federal Communications Commission (FCC) took a decisive step by announcing it would no longer certify consumer-grade internet routers manufactured outside the United States. This move by the FCC underscores the growing recognition of foreign-made routers as a significant national security threat, with poorly secured devices posing "a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
The FCC’s new policy, while aimed at bolstering national security, may limit the availability of new consumer-grade routers, with exceptions for devices like SpaceX’s Starlink satellite internet routers. The commission has indicated that router manufacturers can seek special "conditional approval" from the Department of War or the Department of Homeland Security, and the new policy does not retroactively affect previously purchased consumer-grade routers. This regulatory action, coupled with the revelations about Forest Blizzard’s sophisticated router exploitation, highlights the persistent and evolving challenges in securing the global digital infrastructure against state-sponsored cyber threats.









