A sophisticated and financially motivated cybercrime group, known as TeamPCP, has unleashed a new wiper malware, dubbed ‘CanisterWorm,’ that specifically targets systems in Iran. This aggressive campaign, which surfaced over the weekend, leverages a self-propagating worm to exploit poorly secured cloud services, aiming to inflict data destruction on systems identified by their use of Iran’s time zone or the Farsi language setting. This development injects a new, destructive dimension into the ongoing geopolitical tensions involving Iran, demonstrating the evolving tactics of cybercriminals seeking to capitalize on conflict zones.
TeamPCP, a relatively new entrant in the cybercrime landscape, has been actively compromising corporate cloud environments since December 2025. Their modus operandi involves targeting exposed Docker APIs, Kubernetes clusters, Redis servers, and exploiting the React2Shell vulnerability. Once inside a network, the group exhibits a strong tendency for lateral movement, systematically siphoning authentication credentials with the ultimate goal of extorting victims, often via the Telegram messaging platform. This approach highlights a calculated strategy of leveraging existing vulnerabilities and misconfigurations within cloud infrastructure to achieve their illicit objectives.
The group’s preference for targeting cloud infrastructure over end-user devices is a key characteristic. Research by the security firm Flare in January painted a stark picture of TeamPCP’s operational focus, revealing that 97% of their compromised servers were hosted on major cloud platforms, with Microsoft Azure (61%) and Amazon Web Services (AWS) (36%) bearing the brunt of these attacks. Flare’s analysis, authored by Assaf Morag, emphasized that TeamPCP’s strength lies not in novel exploit development but in the "large-scale automation and integration of well-known attack techniques." Morag described their methodology as an "industrialization of existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem." This underscores a pragmatic and efficient approach to cybercrime, focusing on maximizing impact through systematic exploitation of known weaknesses.
The recent wiper campaign is intricately linked to a supply chain attack orchestrated by TeamPCP on March 19th against Trivy, a popular vulnerability scanner developed by Aqua Security. In this attack, the adversaries managed to inject credential-stealing malware into official releases of Trivy distributed via GitHub Actions. While Aqua Security has since taken steps to remove the malicious files, the security firm Wiz noted that the attackers successfully published compromised versions of Trivy capable of exfiltrating sensitive information, including SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from unsuspecting users. This incident underscores the pervasive risks associated with supply chain attacks, where the compromise of a trusted software component can have far-reaching consequences for its entire user base.
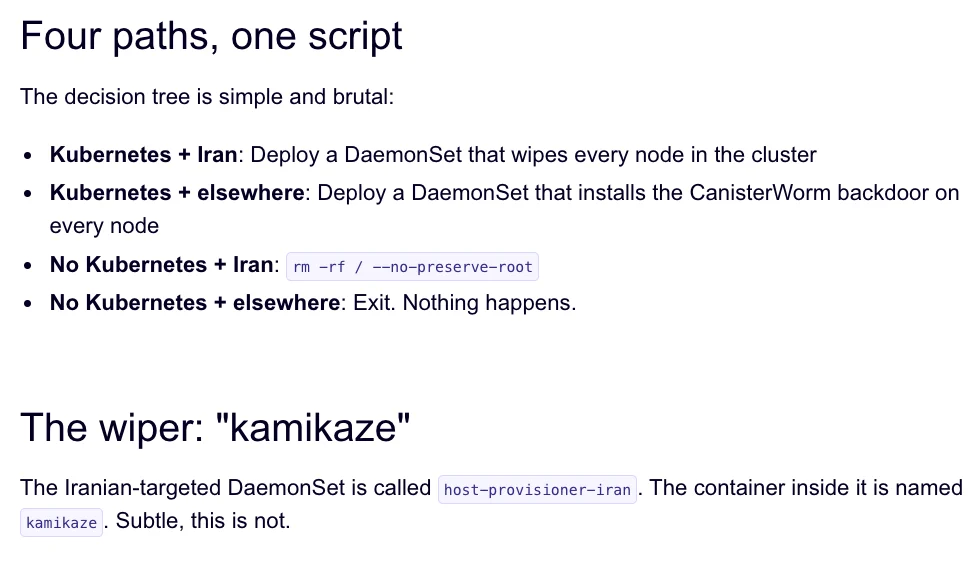
The same technical infrastructure that facilitated the Trivy attack was subsequently repurposed to deploy the ‘CanisterWorm’ payload. Charlie Eriksen, a security researcher at Aikido, detailed this operation in a blog post published on Sunday. Eriksen explained that the wiper component is designed to execute its destructive function only if it detects that a victim system is configured with Iran’s time zone or Farsi as its default language. If the infected system is part of a Kubernetes cluster, the malware is programmed to wipe data across every node within that cluster. In cases where a Kubernetes cluster is not accessible, the wiper defaults to eradicating data from the local machine. This targeted approach suggests a deliberate attempt to maximize disruption within Iranian digital infrastructure.

Aikido has referred to TeamPCP’s operational infrastructure as "CanisterWorm," a name derived from the group’s use of an Internet Computer Protocol (ICP) canister to orchestrate their campaigns. ICP canisters are essentially tamperproof, blockchain-based "smart contracts" that encapsulate both code and data. Their distributed architecture makes them highly resistant to takedown attempts, ensuring their continued accessibility as long as their operators maintain payment of virtual currency fees. This innovative use of blockchain technology for command-and-control infrastructure presents a new challenge for cybersecurity professionals seeking to disrupt malicious operations.
Evidence from TeamPCP’s communications on Telegram suggests the group is not only bragging about their exploits but also claiming to have exfiltrated vast amounts of sensitive data from major corporations, including a prominent multinational pharmaceutical firm. Eriksen observed that following their second compromise of Aqua Security, TeamPCP flooded numerous GitHub accounts with spam messages. He interpreted this as a blatant display of their extensive access and capabilities, suggesting that the publicly observed breaches are merely a fraction of their total compromised assets. This aggressive posturing could also serve a strategic purpose: to elevate the visibility of their tainted code packages within GitHub searches, thereby increasing the likelihood of further infections. This tactic aligns with observations by Risky Business reporter Catalin Cimpanu, who noted in a recent newsletter that attackers often employ meaningless commits or purchased social media engagement to ensure their malicious repositories remain at the top of search results.
This weekend’s wiper deployment marks the second significant supply chain attack involving Trivy in as many months. In late February, Trivy was targeted by HackerBot-Claw, an automated threat that exploited misconfigured GitHub Actions workflows to steal authentication tokens. Eriksen believes that TeamPCP likely leveraged the access gained from the initial Aqua Security compromise to execute this latest attack. However, he cautions that there is currently no definitive way to confirm if the ‘CanisterWorm’ wiper successfully destroyed any data, as the malicious payload was reportedly active for a limited duration over the weekend.
Eriksen further elaborated on TeamPCP’s dynamic operational approach, stating that they have been "taking [the malicious code] up and down, rapidly changing it adding new features." During periods when the malicious canister was not actively serving malware downloads, it was observed redirecting visitors to a Rick Roll video on YouTube. This erratic behavior, coupled with the group’s claims and aggressive tactics, leads Eriksen to speculate that the focus on Iran might be a deliberate attempt to gain attention, describing the group’s actions as embodying a "Chaotic Evil" persona.
Catalin Cimpanu’s reporting highlights a concerning increase in the frequency of supply chain attacks, as threat actors increasingly recognize their efficiency. Cimpanu’s work documents a significant number of such incidents since 2024, emphasizing the need for enhanced security measures not only from security firms but also from platform providers like GitHub. He points out the inherent difficulty in identifying malicious additions within cloned repositories on a platform designed for collaborative code development, suggesting that robust solutions will require significant engineering effort.
In an update on March 23rd, Wiz reported that TeamPCP had also infiltrated the KICS vulnerability scanner from Checkmarx, pushing credential-stealing malware to its GitHub Action between 12:58 and 16:50 UTC on the same day. This latest incident further underscores the widespread nature of TeamPCP’s campaign and their persistent efforts to exploit trusted software development pipelines. The continuous targeting of vulnerability scanners and development tools demonstrates a sophisticated understanding of the software supply chain and its inherent vulnerabilities, making them a significant and evolving threat to the global digital landscape.









