Kelp, a prominent liquid restaking protocol, operates at the cutting edge of Ethereum’s staking ecosystem, offering users the ability to restake their staked Ether (ETH) through platforms like EigenLayer and receive a liquid restaking token (LRT) in return. This LRT, in Kelp’s case rsETH, represents their underlying staked assets and accumulated rewards, while also providing liquidity and utility across various DeFi applications. The allure of liquid restaking lies in its promise of enhanced capital efficiency, allowing users to earn multiple layers of yield – from ETH staking, EigenLayer restaking, and then by deploying their LRTs in other DeFi protocols. However, this multi-layered complexity, while lucrative, also introduces new vectors for potential exploits, as tragically demonstrated by the recent breach.
The incident unfolded rapidly on Saturday, prompting an urgent response from the Kelp team. "Earlier today, we identified suspicious cross-chain activity involving rsETH. We have paused rsETH contracts across mainnet and several Layer-2s," the Kelp platform announced via an X (formerly Twitter) post. This swift action to halt contract operations is a standard, albeit drastic, measure taken by protocols in the event of an exploit to prevent further bleeding of funds and to contain the damage while investigations are underway. The pause effectively freezes all transfers, redemptions, and interactions with rsETH, locking user funds in place until a resolution can be found, leaving countless users in a state of uncertainty.
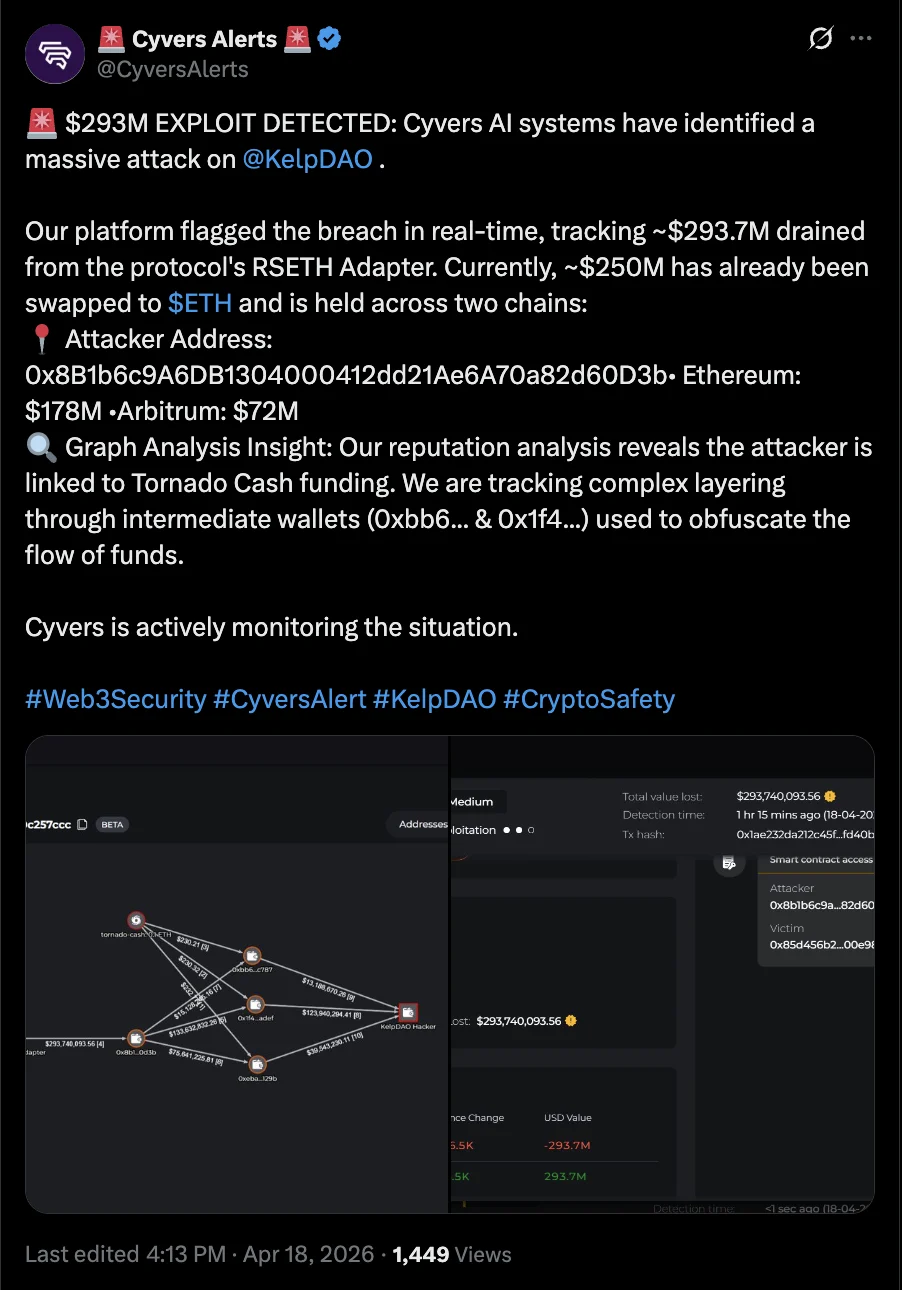
According to preliminary findings from blockchain security firm Cyvers, the attackers specifically targeted and exploited a vulnerability within the rsETH adapter bridge contract. This critical piece of software code is responsible for managing the rsETH token’s interoperability, particularly its movement across different blockchain networks and its integration with various DeFi applications. Bridge contracts are often complex and serve as vital conduits for value transfer, making them high-value targets for malicious actors. While the exact technical specifics of the exploit remain under investigation, such vulnerabilities often stem from logic errors, re-entrancy bugs, or improper handling of cross-chain messages, allowing attackers to mint unauthorized tokens or drain legitimate assets. The attacker successfully drained approximately $293 million in funds from the platform, marking one of the largest single exploits in the DeFi space in recent memory.
Further analysis by Cyvers revealed the sophisticated nature of the attacker’s operations. The perpetrator initiated the attack using an address that had been funded through Tornado Cash, a notorious crypto mixer. Tornado Cash allows users to obscure the origin and destination of their crypto transactions, making it exceedingly difficult for blockchain forensics experts to trace stolen funds. This choice of mixer immediately signaled a well-planned operation by experienced criminals. Compounding the challenge for recovery, Cyvers informed Cointelegraph that a significant portion of the stolen funds – estimated at around $250 million – had already been converted into Ether (ETH), the native cryptocurrency of the Ethereum layer-1 blockchain network. This conversion to ETH, a highly liquid and widely accepted asset, facilitates easier laundering and further obfuscation of the stolen assets, diminishing the chances of recovery for affected users and the protocol.

The impact of the Kelp hack was not confined to the protocol itself but reverberated throughout the interconnected DeFi ecosystem. Liquid restaking tokens like rsETH are designed for composability, meaning they can be used as collateral, liquidity, or yield-bearing assets across a multitude of other DeFi platforms. This interconnectedness, while enabling innovative financial products and greater capital efficiency, also creates a systemic risk where a vulnerability in one protocol can trigger a domino effect across others.
Decentralized finance giant Aave, a leading lending and borrowing protocol, was among the first to react. Recognizing the potential for systemic risk, Aave announced it had "frozen rsETH markets on Aave V3 and V4." Freezing markets on a platform like Aave means that users can no longer deposit rsETH as collateral, borrow against it, or withdraw it if it’s currently being used as collateral. This protective measure prevents further contagion, such as bad debt accumulating if the value of rsETH were to plummet or if attackers tried to manipulate its price within lending pools. According to Cyvers, at least nine other crypto protocols had exposure to rsETH, either through liquidity pools, lending markets, or other integrations, and subsequently moved to freeze activity on their platforms in response to the exploit. The exact identities of all affected protocols are still emerging, but the widespread disruption underscores the inherent fragility that can arise from DeFi’s highly interconnected nature.
Deddy Lavid, CEO of Cyvers, succinctly captured the gravity of the situation, telling Cointelegraph, "This is exactly the kind of incident that highlights the risks of composability in DeFi." His statement serves as a stark reminder that while composability is a cornerstone of DeFi’s innovation and growth, it also represents its Achilles’ heel from a security perspective. A single point of failure or a sophisticated exploit in one foundational component can compromise the integrity of an entire network of dependent applications, leading to widespread financial losses and a crisis of confidence. Cointelegraph reached out to Kelp for comment but did not receive a response by the time of publication, indicating the team was likely fully engaged in managing the crisis and investigation.
The Kelp hack is unfortunately not an isolated incident but rather the latest in a relentless string of cybersecurity breaches and exploits plaguing crypto platforms. The first quarter of 2026 alone saw crypto losses from hacks and scams total an alarming $482 million, according to various blockchain security analyses. This persistent onslaught of attacks highlights the ongoing challenges of securing complex, open-source blockchain protocols against increasingly sophisticated adversaries. From smart contract vulnerabilities to private key compromises and social engineering tactics, the attack vectors are diverse and constantly evolving.
A recent high-profile case that resonates with the Kelp incident is the exploit suffered by the decentralized cryptocurrency exchange Drift Protocol in April. This attack drained approximately $280 million from the platform, a sum comparable to the Kelp losses. However, the nature of the Drift Protocol exploit presented a different, equally concerning dimension of cyber threats. The Drift team’s post-mortem revealed a chilling narrative: the attack was not a simple smart contract bug but rather "took months of deliberate preparation," suggesting a sophisticated, long-term infiltration. The team further indicated that they were likely compromised by suspected North Korean state-affiliated hackers, a group notorious for their advanced persistent threats and their systematic targeting of crypto assets to fund national programs.

The Drift team’s update detailed how attackers allegedly met team members at a "major" crypto conference, subsequently collaborating with them for several months. During this period, the attackers reportedly deployed malware on developer machines, ultimately compromising the platform from within. This method underscores the growing threat of supply chain attacks and social engineering, where human elements and internal systems become the weakest links. Unlike a purely technical smart contract exploit, the Drift incident highlights the need for comprehensive security strategies that encompass not only code audits but also rigorous personnel vetting, secure development environments, and robust internal cybersecurity protocols.
The continuous barrage of multi-million-dollar hacks raises profound questions about the future security and sustainability of the DeFi sector. While the industry boasts transparency and decentralization, these attributes do not inherently guarantee immunity from sophisticated attacks. The economic incentives for hackers are immense, driving them to constantly seek new vulnerabilities. For users, these incidents erode trust, making them hesitant to engage with innovative but high-risk protocols. For developers, the pressure to secure their platforms against an ever-evolving threat landscape is immense, requiring continuous audits, bug bounty programs, and a proactive security posture.
The Kelp hack, specifically targeting a liquid restaking protocol, also brings into sharp focus the security implications of EigenLayer and the broader restaking narrative. As more value becomes locked in restaking protocols and their associated LRTs, they become increasingly attractive targets. Ensuring the robustness of these foundational layers and their derivatives is paramount for the long-term health of the Ethereum ecosystem. The industry must learn from these costly lessons, pushing for more stringent security standards, collaborative threat intelligence sharing, and the development of more resilient infrastructure to protect user funds and foster continued innovation. The $293 million vanished from Kelp serves as another painful reminder that in the fast-paced, high-stakes world of DeFi, security cannot be an afterthought; it must be an intrinsic, unyielding priority.







