A sophisticated new phishing-as-a-service, dubbed "Starkiller," is revolutionizing cybercrime by enabling threat actors to bypass traditional detection methods and even multi-factor authentication (MFA) by dynamically proxying real login pages. Unlike conventional phishing kits that rely on static, often quickly detected copies of legitimate websites, Starkiller operates as a transparent intermediary, relaying user credentials and MFA codes directly to the genuine service while logging all interactions. This innovative approach significantly lowers the barrier to entry for aspiring cybercriminals and poses a substantial new threat to online security, as detailed in an analysis by the security firm Abnormal AI.
Traditionally, phishing operations have been characterized by the creation of deceptive copies of popular login pages. These static replicas are often easily identified and taken down by security researchers and anti-abuse teams. However, Starkiller introduces a paradigm shift. Instead of presenting a fabricated login page, it cleverly disguises malicious links to route traffic through the attacker’s infrastructure. This infrastructure then acts as a sophisticated proxy, loading the actual login page of the target brand. The victim interacts with what appears to be the legitimate website, but their every input – including usernames, passwords, and critically, MFA codes – is intercepted and relayed by Starkiller to the real service. Simultaneously, the legitimate service’s responses are forwarded back to the victim, creating an illusion of normal interaction.
The setup and deployment of traditional phishing kits often involve a significant amount of technical drudgery, including configuring servers, managing domain names, securing certificates, and setting up proxy services. Starkiller streamlines this entire process, offering a plug-and-play solution for cybercriminals. Customers of Starkiller can select a target brand – such as Apple, Facebook, Google, or Microsoft – and the service automatically generates a deceptive URL. This URL is designed to visually mimic the legitimate domain, making it incredibly difficult for users to discern its malicious nature.
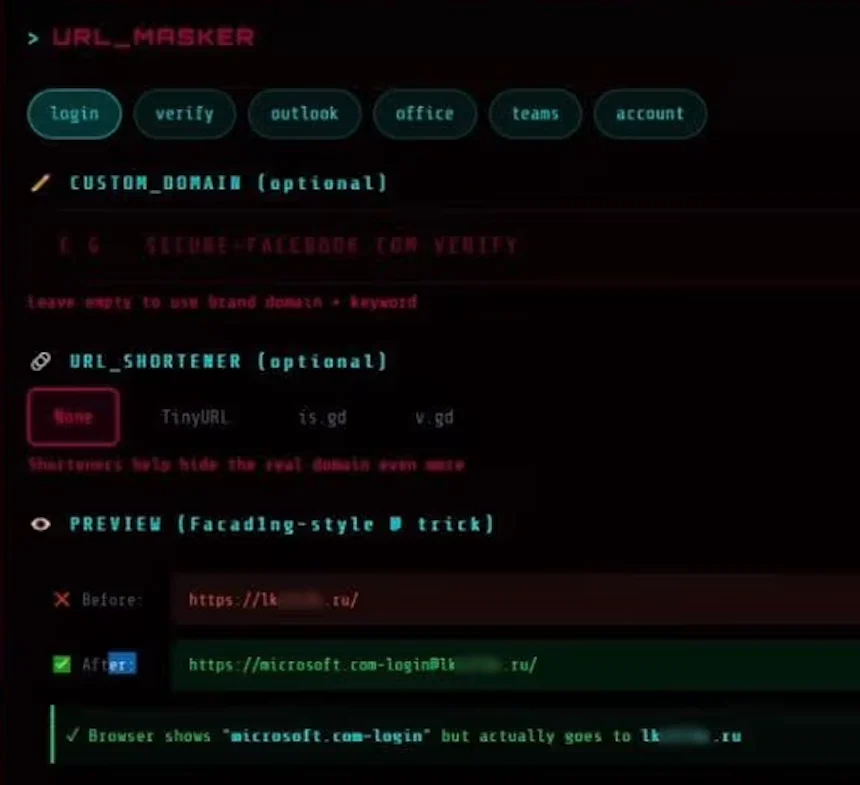
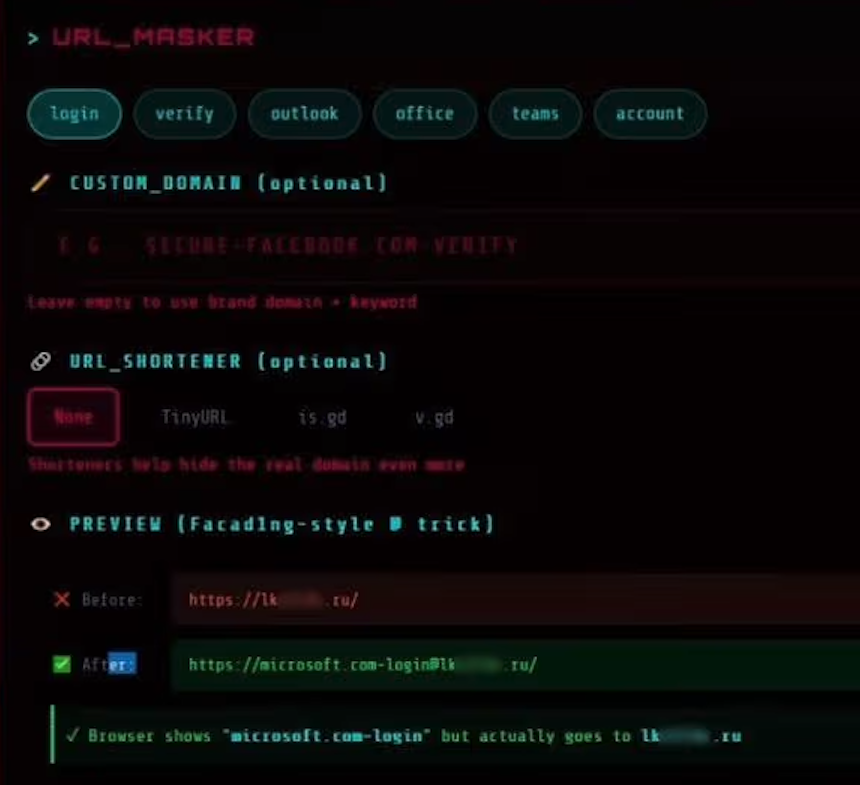
A prime example of Starkiller’s deceptive URL generation involves leveraging an old but effective trick with the "@" symbol. A phishing link targeting Microsoft users might appear as “login.microsoft.com@[malicious/shortened URL here].” In the context of a URL, everything preceding the "@" symbol is interpreted as username data by some systems, while the actual landing page is the domain that follows. This subtle manipulation can lead unsuspecting users to believe they are navigating to the legitimate Microsoft login page. The image provided by Abnormal AI illustrates this, showing a blurred-out malicious landing page with a .ru domain, demonstrating the service’s ability to integrate with various URL shortening services for further obfuscation.
Once a target URL is selected, Starkiller automates the deployment of its core infrastructure. The service utilizes Docker containers to run headless Chrome browser instances. These instances load the genuine login page of the targeted brand. According to Abnormal AI researchers Callie Baron and Piotr Wojtyla, the Docker container then functions as a man-in-the-middle reverse proxy. This setup allows the attacker-controlled infrastructure to intercept and forward all end-user inputs to the legitimate site, and then relay the legitimate site’s responses back to the victim. This means every keystroke, form submission, and session token is routed through the attacker’s systems and meticulously logged.
This real-time session monitoring capability is a significant advancement. Starkiller offers cybercriminals the ability to effectively "live-stream" the victim’s screen as they interact with the compromised session. This provides attackers with an unprecedented level of insight and control. Beyond simply capturing credentials, the platform incorporates a suite of advanced features. These include keylogger functionality for capturing every keystroke, the theft of cookies and session tokens for direct account takeover, geo-tracking of victims, and automated Telegram alerts whenever new credentials are obtained. Furthermore, Starkiller provides campaign analytics, mirroring the dashboards of legitimate SaaS platforms, with metrics such as visit counts, conversion rates, and performance graphs, allowing attackers to optimize their operations.
Perhaps the most alarming capability of Starkiller is its effectiveness in bypassing multi-factor authentication (MFA). Because the victim is essentially authenticating with the real site through the attacker’s proxy, any MFA codes or prompts are also relayed in real-time. The attacker captures the resulting session cookies and tokens, granting them authenticated access to the victim’s account. As Baron and Wojtyla explain, "When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed." This means that even users who have diligently implemented MFA are vulnerable to account compromise through this sophisticated phishing technique.
Starkiller is not an isolated offering but rather a component of a broader suite of cybercrime services provided by a threat group known as "Jinkusu." This group actively maintains a user forum where its customers can share techniques, request new features, and troubleshoot their phishing deployments. An additional "a-la-carte" feature allows for the harvesting of email addresses and contact information from compromised sessions, which can then be used to build targeted lists for future phishing campaigns.
The implications of Starkiller are profound. It represents a remarkable evolution in phishing tactics, one that is highly likely to be emulated by other cybercriminals due to its efficiency and effectiveness. By circumventing the need to manage multiple phishing domains and evading traditional detection methods like domain blocklisting and static page analysis, Starkiller significantly reduces the overhead and constant challenges faced by attackers. Moreover, it dramatically lowers the technical proficiency required to launch successful phishing attacks, democratizing sophisticated cybercrime for less skilled individuals.
In conclusion, Starkiller signifies a substantial escalation in the sophistication and accessibility of phishing infrastructure. It reflects a growing trend towards commoditized, enterprise-style tooling within the cybercrime ecosystem. The combination of advanced URL masking, real-time session hijacking, and the neutralization of MFA defenses equips low-skill cybercriminals with attack capabilities that were previously the domain of highly organized and technically proficient groups. This development underscores the urgent need for enhanced, dynamic, and adaptive security measures to combat evolving threats.









