Microsoft, in a detailed blog post released today, revealed that it had identified over 200 organizations and an additional 5,000 consumer devices that fell victim to this clandestine and surprisingly straightforward spying network. The threat actor behind this operation is known as "Forest Blizzard," a group widely attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). This same group, also known by aliases such as APT28 and Fancy Bear, has a documented history of high-profile cyber intrusions, including the infamous compromises of the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee in 2016, which were aimed at interfering with the U.S. presidential election.
Researchers at Black Lotus Labs, the dedicated security division of the prominent Internet backbone provider Lumen, have been at the forefront of uncovering the intricacies of this operation. Their investigation revealed that at its peak activity in December 2025, Forest Blizzard’s surveillance network had ensnared an astonishing number of Internet routers. The vast majority of these compromised devices were either unsupported, end-of-life models, or routers that were significantly behind on crucial security updates. A comprehensive new report from Lumen further elucidates that the primary targets of these hackers were government agencies, including ministries of foreign affairs, law enforcement bodies, and third-party email providers, highlighting the strategic nature of their intelligence-gathering efforts.
Ryan English, a Security Engineer at Black Lotus Labs, explained the ingenious, yet disturbingly simple, methodology employed by the GRU hackers. Crucially, they did not need to install any malware on the targeted routers, which were predominantly older Mikrotik and TP-Link devices commonly marketed to the Small Office/Home Office (SOHO) segment. Instead, the attackers leveraged well-documented, known vulnerabilities to precisely modify the Domain Name System (DNS) settings of these routers. This modification involved redirecting DNS requests to DNS servers that were under the direct control of the hackers.
The United Kingdom’s National Cyber Security Centre (NCSC) has also issued a new advisory, corroborating these findings and detailing how Russian cyber actors are actively compromising routers to enable DNS hijacking operations. The NCSC emphasizes the fundamental role of DNS in enabling users to access websites by typing familiar domain names rather than their complex IP addresses. In a DNS hijacking attack, malicious actors intercept this process, covertly redirecting unsuspecting users to fraudulent websites meticulously designed to steal login credentials and other sensitive personal or corporate information.
English further elaborated on the technical execution of the attack. The routers compromised by Forest Blizzard were reconfigured to utilize DNS servers controlled by the attackers. These servers were hosted on a handful of virtual private servers, providing the hackers with a robust and flexible infrastructure. Once the DNS settings were altered, the malicious configurations could be propagated to all devices connected to the local network. From this vantage point, the attackers were able to intercept any OAuth authentication tokens transmitted by users on that network.
A critical aspect of this attack, and what makes it particularly alarming, is that these authentication tokens are typically transmitted after a user has successfully logged in and successfully completed multi-factor authentication (MFA). This means that the attackers could gain direct access to victim accounts without ever needing to resort to traditional phishing tactics to steal user credentials or one-time codes. This circumvents a significant layer of modern security.

"Everyone is looking for some sophisticated malware to drop something on your mobile devices or something," English remarked, highlighting the common misconception of how advanced cyber threats operate. "These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done." This statement underscores the effectiveness of exploiting fundamental network infrastructure flaws over complex, novel malware development.
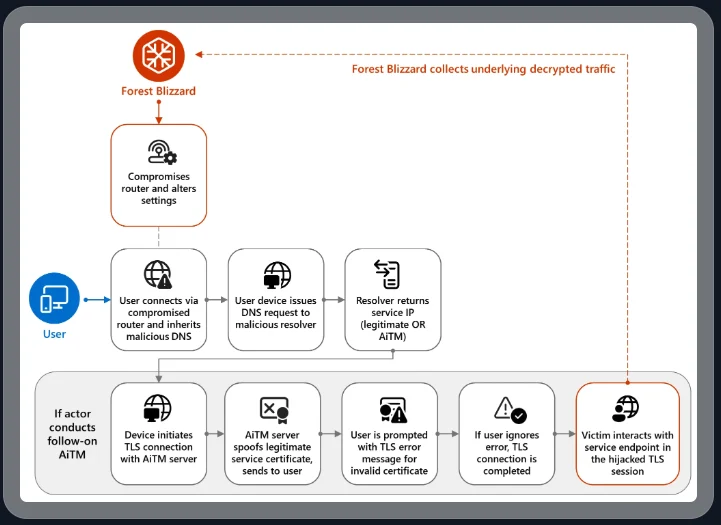
Microsoft has categorized the Forest Blizzard activity as the use of DNS hijacking to "support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." While the targeting of SOHO devices is not an entirely new tactic in the cyber threat landscape, this marks the first instance that Microsoft has observed Forest Blizzard employing DNS hijacking at such a large scale to facilitate AiTM attacks on TLS connections, following the exploitation of edge devices like routers.
Danny Adamitis, another engineer at Black Lotus Labs, expressed keen interest in observing Forest Blizzard’s response to the significant attention their espionage operation has garnered. He noted that the group had previously demonstrated a remarkable agility in adapting its tactics. Following a similar NCSC report in August 2025, which detailed Forest Blizzard’s use of malware to control a more targeted and smaller group of compromised routers, the group swiftly abandoned the malware-centric approach. Within a day of the NCSC report’s release, they transitioned to broadly altering DNS settings on thousands of vulnerable routers, showcasing their rapid evolution and resilience.
"Before the last NCSC report came out they used this capability in very limited instances," Adamitis told KrebsOnSecurity. "After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable." This statement illustrates the group’s willingness to scale their operations and exploit any available vulnerability once a particular tactic is exposed.
The implications of these findings are amplified by recent regulatory actions concerning router security. TP-Link, one of the router manufacturers whose devices were frequently targeted, had previously faced proposals for a complete ban in the United States. However, on March 23rd, the U.S. Federal Communications Commission (FCC) adopted a far more comprehensive approach. The FCC announced that it would no longer certify consumer-grade Internet routers that are produced outside of the United States, citing national security concerns.
The FCC explicitly warned that foreign-made routers had evolved into an untenable national security threat. They stated that poorly secured routers present "a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons." This broad policy aims to mitigate the risks associated with devices that may have inherent security weaknesses or backdoors.
Experts, however, have raised points of clarification regarding the practical impact of this new FCC policy. They note that few new consumer-grade routers would likely be available for purchase under this new regulation, with potential exceptions like Elon Musk’s Starlink satellite internet routers, which are manufactured domestically. The FCC has indicated that router manufacturers can apply for a special "conditional approval" from either the Department of Defense or the Department of Homeland Security. Importantly, this new policy does not retroactively affect any consumer-grade routers that have already been purchased and are currently in use. This ongoing saga highlights the critical need for robust router security and the constant vigilance required to defend against evolving cyber threats from state-sponsored actors.









