A sophisticated cyberattack, attributed to an Iran-linked hacktivist group known as Handala, has crippled the global operations of Stryker, a leading medical technology company, prompting the send-home of thousands of employees and raising concerns about potential disruptions to healthcare supply chains. The attack, characterized as a "data-wiping" incident, has reportedly affected Stryker’s offices in 79 countries, with the perpetrators claiming to have erased data from over 200,000 systems, servers, and mobile devices. This incident marks a significant escalation in cyber warfare, targeting a critical sector of the global economy and potentially impacting patient care.
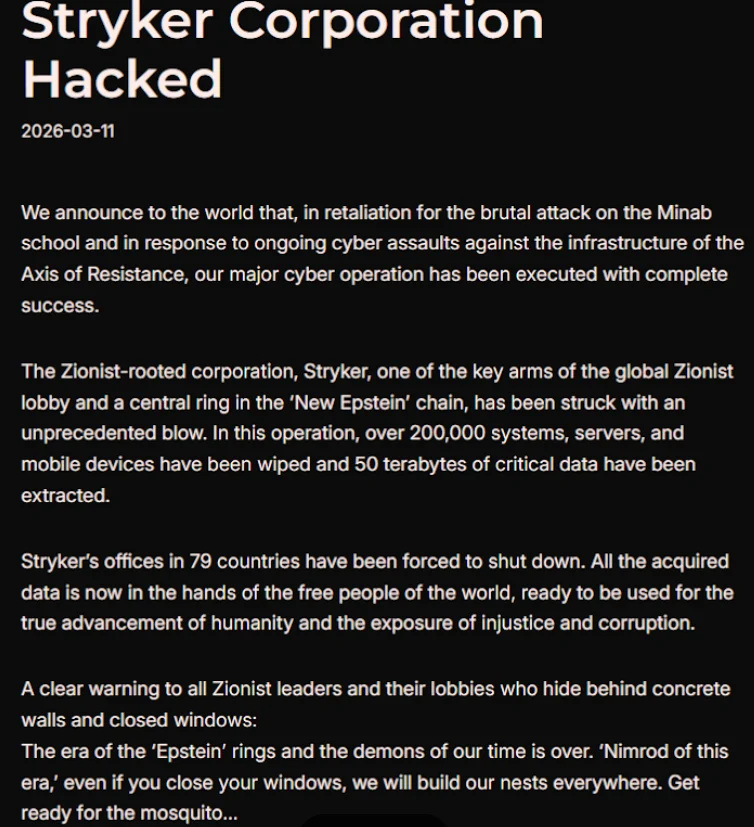
The hacktivist group Handala, which has been linked by cybersecurity researchers to Iran’s Ministry of Intelligence and Security (MOIS), stated on the Telegram platform that the attack was a direct retaliation for a missile strike on an Iranian school on February 28th, which resulted in the deaths of at least 175 people, predominantly children. While the group did not explicitly state the origin of the missile strike, a report by The New York Times, citing an ongoing military investigation, indicated that the United States was responsible for the deadly Tomahawk missile strike. This geopolitical context underscores the complex motivations behind modern cyberattacks, often blurring the lines between state-sponsored espionage, hacktivism, and retaliatory actions.
Stryker, a global medical and surgical equipment manufacturer headquartered in Kalamazoo, Michigan, with reported annual sales of $25 billion and a workforce of approximately 56,000 employees across 61 countries, has confirmed a "building emergency" at its U.S. headquarters. News reports from Ireland, where Stryker has its largest operational hub outside the U.S., detailed that over 5,000 workers were sent home. Employees in Ireland reported that any device connected to the company network was rendered inoperable, and personal devices with Microsoft Outlook installed had been wiped. Login pages on affected devices were allegedly defaced with the Handala logo, a stark visual indicator of the cyber intrusion.
The nature of the attack appears to go beyond traditional ransomware, which typically aims to extort payment for data recovery. Instead, Handala claims to have executed a "wiper attack," designed to permanently destroy data. However, a source familiar with the incident suggested that the attackers may have exploited a legitimate Microsoft service, Microsoft Intune, to issue a "remote wipe" command across all connected devices. Intune is a cloud-based device management solution used by IT departments to enforce security policies and control devices remotely. The theory of Intune’s misuse is further supported by reports of Stryker employees being urgently advised to uninstall the software.
Palo Alto Networks, in a recent profile of Iranian cyber activity, highlighted Handala’s operational modus operandi. The group, which emerged in late 2023, is believed to be an online persona of Void Manticore, an actor affiliated with Iran’s MOIS. Handala’s primary focus has historically been on targets in Israel, but it has expanded its scope to include other regions when serving a specific agenda. The group has previously claimed responsibility for attacks on fuel systems in Jordan and an Israeli energy exploration company. Palo Alto researchers characterized Handala’s recent activities as opportunistic and "quick and dirty," with a strategic emphasis on exploiting supply-chain vulnerabilities, such as targeting IT service providers to gain access to downstream victims. The posting of "proof" data is a common tactic to amplify credibility and intimidate targets.
Handala’s manifesto also referred to Stryker as a "Zionist-rooted corporation," possibly alluding to Stryker’s 2019 acquisition of the Israeli company OrthoSpace. This framing suggests a broader geopolitical motivation behind the cyber operation, aligning with narratives often promoted by Iran-aligned actors.
The implications of this attack extend far beyond Stryker’s internal operations, posing a significant threat to the healthcare sector. Stryker is a crucial supplier of medical devices and surgical supplies to hospitals worldwide. Healthcare professionals have already reported an inability to order essential surgical supplies normally sourced through Stryker. One anonymous expert described the incident as a "real-world supply chain attack," emphasizing that "pretty much every hospital in the U.S. that performs surgeries uses their supplies." This highlights the potential for cascading disruptions, where an attack on a single vendor can have far-reaching consequences for patient care.
The American Hospital Association (AHA) has acknowledged the reports of the cyberattack and is actively gathering information from hospitals and federal agencies to assess the potential impact. As of Wednesday, the AHA stated it was not aware of any direct disruptions to U.S. hospitals. However, John Riggi, the AHA’s national advisor, cautioned that this situation could evolve as hospitals evaluate their reliance on Stryker’s services and technology, particularly if the attack’s duration is prolonged.
A memo from Maryland’s Institute for Emergency Medical Services Systems indicated that Stryker itself had acknowledged a "global network disruption" impacting some of its computer systems. In response, several hospitals have taken the precautionary measure of disconnecting from Stryker’s online services, including LifeNet, a system that enables paramedics to transmit EKGs to emergency physicians for expedited treatment of heart attack patients. This decision, while aimed at safeguarding patient data and maintaining operational integrity, could lead to delays in critical cardiac care. The memo advised that in the absence of ECG transmission capabilities, radio consultation should be initiated.
This is a developing story, and further updates are expected as the full scope and impact of the attack become clearer. The incident serves as a stark reminder of the interconnectedness of global supply chains and the vulnerability of critical infrastructure to sophisticated cyber threats, particularly those with geopolitical undertones. The response from cybersecurity firms, government agencies, and the healthcare industry will be crucial in mitigating the immediate fallout and fortifying defenses against future attacks. The incident also raises questions about the security of widely used IT management tools and the potential for their weaponization by malicious actors. The global reliance on companies like Stryker for essential medical equipment underscores the need for robust cybersecurity measures not only within these companies but also throughout their entire supply chain.









