An Iran-linked hacktivist group known as Handala has claimed responsibility for a sophisticated data-wiping attack targeting Stryker, a prominent global medical technology company with a significant operational presence in Ireland. The attack has reportedly led to the shutdown of Stryker’s offices in 79 countries, impacting over 200,000 systems, servers, and mobile devices. This incident has sent ripples through the healthcare industry, raising concerns about potential supply chain disruptions and the security of critical medical infrastructure.
The fallout from the cyberattack became immediately apparent at Stryker’s largest hub outside the United States, located in Ireland. Over 5,000 workers at the Irish facilities were reportedly sent home as the company grappled with the widespread system outages. Meanwhile, a voicemail message at Stryker’s main U.S. headquarters in Kalamazoo, Michigan, cited a "building emergency," a euphemism for the ongoing cyber incident. Stryker, a major player in the medical and surgical equipment market, reported $25 billion in global sales last year, underscoring its critical role in the healthcare ecosystem.
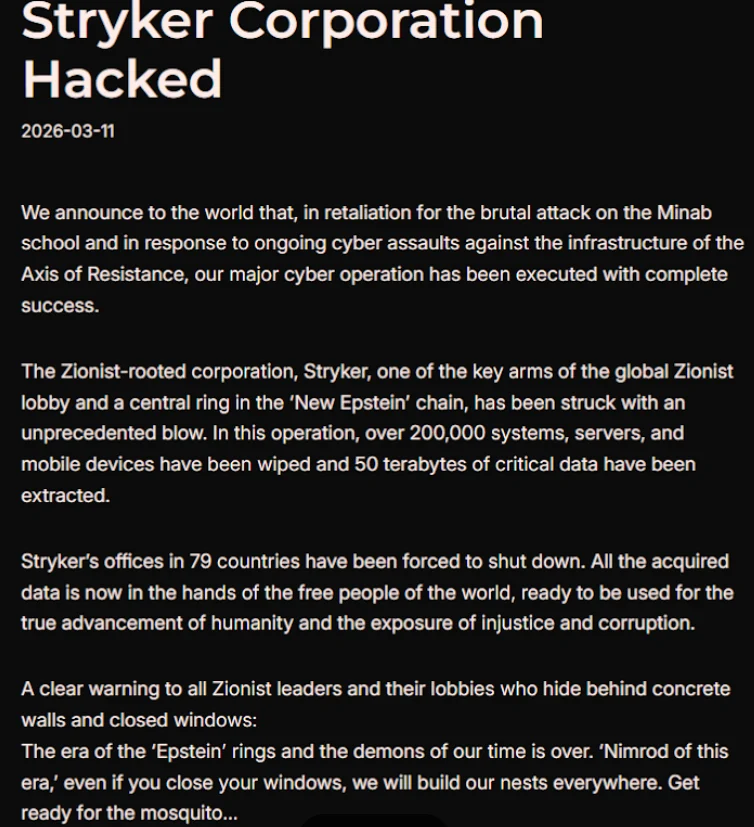
The Handala group, in a detailed statement published on Telegram, boasted about erasing data from an extensive network of Stryker’s digital assets. "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption," the group declared, framing their actions as a crusade against perceived corruption and injustice.
The attackers explicitly stated that the wiper attack was a retaliatory measure for a missile strike on an Iranian school on February 28th, which resulted in the tragic deaths of at least 175 people, primarily children. Subsequent reports from The New York Times, citing an ongoing military investigation, have attributed responsibility for this deadly strike to the United States. This connection highlights the increasingly complex geopolitical motivations behind cyber warfare.
The Handala group’s activities have been scrutinized by cybersecurity firms, including Palo Alto Networks. Their research links Handala to Iran’s Ministry of Intelligence and Security (MOIS). Palo Alto Networks indicates that Handala emerged in late 2023 and is believed to be one of several online personas employed by Void Manticore, an actor associated with the MOIS. This affiliation suggests a state-sponsored element behind the cyber aggression.
Stryker, which employs approximately 56,000 individuals across 61 countries, has been tight-lipped about the specifics of the attack. A media inquiry to their Michigan headquarters yielded a voicemail message referencing a "building emergency," offering little transparency to the public. The lack of direct communication has fueled speculation and concern among stakeholders.
Reports from Ireland paint a stark picture of the attack’s impact. Employees at Stryker’s Cork headquarters are reportedly communicating via WhatsApp for updates on when they can resume work. An unnamed employee quoted by the Irish Examiner described a complete network shutdown, with even personal devices running Microsoft Outlook being wiped. The login pages on affected devices have allegedly been defaced with the Handala logo, serving as a digital signature of the attack.
While wiper attacks typically involve malicious software designed to overwrite data, sources familiar with the Stryker incident suggest a more sophisticated method was employed. It is believed that the perpetrators leveraged Microsoft Intune, a cloud-based device management service, to execute a "remote wipe" command across all connected devices. This method allows for the rapid and widespread deletion of data across geographically dispersed endpoints. Evidence supporting this theory comes from online discussions, where some individuals claiming to be Stryker employees reported being instructed to urgently uninstall Intune.
Palo Alto Networks has previously characterized Handala’s cyber activities as primarily focused on Israel, with occasional forays into other regions when aligned with specific agendas. The group has also claimed responsibility for attacks on fuel systems in Jordan and an Israeli energy exploration company. Their modus operandi is described as opportunistic and "quick and dirty," often exploiting supply chain vulnerabilities, such as targeting IT service providers, to reach downstream victims. This strategy aims to amplify their credibility and intimidate targets.
The Handala group’s manifesto referred to Stryker as a "Zionist-rooted corporation," a descriptor that may stem from Stryker’s 2019 acquisition of the Israeli company OrthoSpace. This framing further underscores the geopolitical undertones of the attack.
The implications of this attack extend beyond Stryker’s internal operations, posing a significant threat to the healthcare supply chain. Stryker is a crucial supplier of medical devices and surgical equipment to hospitals worldwide. Healthcare professionals at major U.S. university medical systems have reported an inability to order essential surgical supplies normally sourced through Stryker, highlighting the immediate real-world consequences. One expert, speaking anonymously, described the incident as a "real-world supply chain attack," emphasizing that "pretty much every hospital in the U.S. that performs surgeries uses their supplies."
The American Hospital Association (AHA) is actively monitoring the situation. John Riggi, national advisor for the AHA, stated that while they are aware of the cyberattack and are exchanging information with hospitals and federal agencies, they are not yet aware of any direct impacts or disruptions to U.S. hospitals. However, he cautioned that this could change as hospitals assess their reliance on Stryker’s services and if the attack’s duration extends.
A memo from Maryland’s Institute for Emergency Medical Services Systems indicated that Stryker itself acknowledged a "global network disruption" impacting some of its computer systems. In response to the attack, several hospitals have proactively disconnected from Stryker’s online services, including LifeNet, a critical platform that allows paramedics to transmit EKGs to emergency physicians for expedited treatment of heart attack patients. This precautionary measure underscores the potential for cascading failures within the healthcare system. The Maryland EMS medical director advised that in the absence of ECG transmission capabilities, radio consultation and descriptive reporting of ECG findings should be initiated to ensure patient care continuity.
This is a developing story, and further updates will be provided as more information becomes available. The cybersecurity landscape continues to evolve, with critical infrastructure and essential services like healthcare increasingly becoming targets for sophisticated cyber threats with geopolitical motivations. The Stryker attack serves as a stark reminder of the vulnerability of interconnected systems and the potential for widespread disruption when these systems are compromised. The long-term impact on Stryker’s operations, its customers, and the broader healthcare industry remains to be seen as the company works to restore its systems and mitigate the damage caused by this significant cyber incident. The incident also prompts a re-evaluation of cybersecurity resilience and preparedness within the global medical technology sector and the healthcare providers that rely on it.









