From inside a bustling money-laundering hub in Cambodia, an operative, his face illuminated by the glow of a smartphone, navigates a popular Vietnamese banking application. The app prompts him to upload a photograph linked to the account. With a tap, he selects an image of a man in his thirties. The next step is a crucial one: a video "liveness" check via the phone’s camera. Instead of presenting himself, the scammer holds up a static image of a woman, bearing no resemblance to the account holder. After a tense 90-second period, during which the app instructs him to reposition the face within the frame, he is granted access. This sophisticated bypass, demonstrated in a video shared by cyberscam researcher Hieu Minh Ngo, is made possible by a burgeoning black market of illicit hacking services readily available on Telegram. These tools are specifically designed to circumvent "Know Your Customer" (KYC) facial recognition and liveness checks, a critical layer of security for financial institutions.
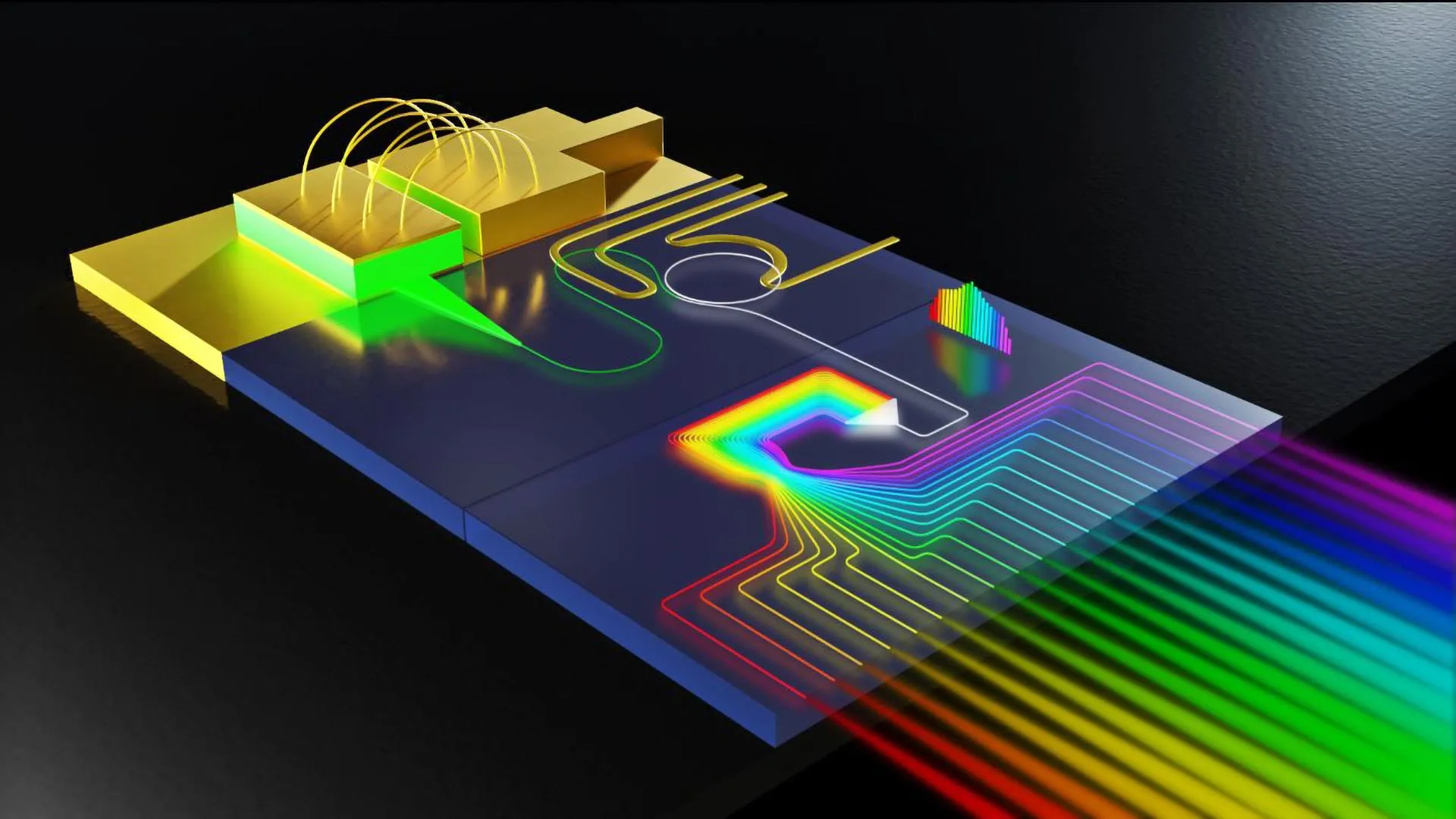
These safeguards are intended to verify that an account holder is a real person and that their live facial image matches the identity documents submitted during account opening. However, criminals are exploiting these systems to establish mule accounts and facilitate money laundering. The common tactic involves using a "virtual camera" instead of the device’s actual camera feed. This allows users to substitute the live video stream with pre-recorded videos or images, which can feature real people, sophisticated deepfakes, or even inanimate objects. This ongoing arms race between malicious actors and the financial services industry sees institutions implement enhanced security measures, only for criminals to devise new workarounds.
An extensive two-month investigation by MIT Technology Review earlier this year uncovered 22 public Telegram channels and groups, primarily in Chinese, Vietnamese, and English, openly advertising these bypass kits and stolen biometric data. The software kits employ a range of methods to compromise phone operating systems and banking applications, with the explicit claim of enabling users to circumvent compliance checks from major entities like cryptocurrency exchanges such as Binance and established banks like Spain’s BBVA. One Telegram account, since deleted, boasted a bio that read, "Specializing in bank services—handling dirty money. Secure. Professional. High quality," accompanied by a thumbs-up emoji. Many of these channels, boasting thousands of subscribers, featured bullet-point lists detailing their services, such as "All kinds of KYC verification services" and "It’s all smooth and seamless," often illustrated with videos purporting to showcase successful hacks. While Telegram stated that these accounts were removed for violating their terms of service, the ease with which such online marketplaces proliferate means that numerous channels offering similar tools remain active.
The surge in KYC bypasses coincides with the rapid expansion of the global "pig-butchering" cyberscam industry. Cryptocurrency platforms and banks worldwide are facing increasing scrutiny over the flow of illicit funds, including profits from these scams, through their systems. This has led to the tightening of banking regulations in countries like Vietnam and Thailand, where governments have intensified customer verification and fraud monitoring requirements and are pushing for more robust anti-money-laundering safeguards within the crypto sector. According to Chainalysis, a US blockchain analysis firm, approximately $17 billion was stolen globally in crypto scams and fraud in 2025, a significant increase from $13 billion in 2024. The United Nations Office on Drugs and Crime has also warned in a recent report that the expansion of Asian scam syndicates into Africa and the Pacific has dramatically scaled up industry profits.
This confluence of increased scrutiny and escalating revenue has propelled KYC bypasses to the forefront of the online marketplace for cyberscam and casino money launderers. While precise figures vary, cybersecurity researchers indicate a significant rise in these attacks. The biometrics verification company iProov estimated that virtual-camera attacks were over 25 times more prevalent worldwide in 2024 than in 2023. Sumsub, a provider of KYC services, reported that "sophisticated" or multi-step fraud attempts, including virtual-camera bypasses, nearly tripled among its clients last year. Three financial institutions named as targets on these Telegram channels – Binance, BBVA, and Revolut – acknowledged awareness of such bypasses, characterizing them as an industry-wide challenge. A Binance spokesperson stated they had "observed attempts of this nature to circumvent our controls" but asserted they had "successfully prevented such attacks and remain confident in our systems." BBVA and Revolut declined to comment on whether their safeguards had been breached. The true success rate of these bypasses is difficult to ascertain, as companies may not detect or report them until much later. Artem Popov, Sumsub’s head of fraud prevention products, emphasized the unseen nature of successful attacks, noting that "there’s always part of the story where it might be completely hidden from our eyes, and from the eyes of any company in the industry, using any type of KYC provider."
The advertisements for these exploits may appear straightforward, but the backend operations required to build a successful bypass are complex and often involve multiple techniques. Some channels offer services to "jailbreak" a physical phone, enabling scammers to trigger the use of a virtual camera (VCam) instead of the device’s built-in one at will. Other hacks involve injecting code, known as a "hooking framework," into a financial institution’s app. This framework manipulates the app to open the VCam, which can then be used to dupe KYC safeguards with fabricated images or videos in place of genuine, live footage of the account owner. Sergiy Yakymchuk, CEO of Talsec, a cybersecurity firm serving financial institutions, reviewed the details from the Telegram channels identified by MIT Technology Review and found them consistent with successful tactics employed against his banking and crypto clients. His team has received assistance requests for approximately 30 VCam-based hacks over the past year, a notable increase from fewer than 10 in 2023. Yakymchuk observes that hackers are increasingly compromising both the phone itself and the code of financial institution apps, then feeding the virtual camera a blend of stolen biometrics and deepfakes. He notes a shift from earlier, simpler methods: "Some time ago, it was enough to decompile the app of a bank and distribute this on Telegram, and that was everything you needed. Now it’s not enough, because you have KYC—and more and more things are needed."
For money launderers, KYC bypasses have become "essential for everything right now—because scam compounds need to move money," according to Ngo, the researcher who provided the demo video. A former convicted hacker now serving as a cybersecurity advisor for the Vietnamese government, Ngo now runs an anti-scam nonprofit and assists law enforcement in money laundering investigations. He explains the process in the context of pig-butchering scams: funds obtained from victims are channeled into bank accounts controlled or rented by money-laundering networks, colloquially known as "water houses." Money launderers then leverage KYC bypasses to access these accounts, rapidly redistribute the profits, and convert them into digital assets, typically stablecoins like Tether. These transactions are executed with extreme speed and under tightly orchestrated management. "They know, very clearly, the flow of how the banks verify or authenticate accounts," Ngo states.
The proliferation of cyberscam money laundering has led to increased scrutiny of financial institutions. In 2023, Binance pleaded guilty in US federal court for operating without adequate anti-money-laundering safeguards. Recent analysis by the International Consortium of Investigative Journalists revealed that following Binance CEO Changpeng Zhao’s guilty plea, over $400 million continued to flow to Binance from Huione Group, a Cambodia-based firm sanctioned by the US Treasury Department for being a "critical node" for money laundering in pig-butchering scams. Binance maintains it possesses "state-of-the-art security systems" that have prevented billions in fraud losses and processed over 71,000 law enforcement requests in 2025. However, John Griffin, a finance and blockchain expert at the University of Texas at Austin, expresses skepticism about the exchanges’ security, stating, "Even though they have all this press about ‘Oh, yes, we’ve changed this and that’—well, the proof is in the pudding. The criminals are still using your exchange. So there must be holes." Binance has contested Griffin’s findings, calling them "misleading at best and, at worst, wildly inaccurate." The exchange also suggests that some purported bypass services are scams themselves, casting doubt on the reported prevalence of successful bypasses. Engaging with such services, a spokesperson noted, "exposes individuals to significant security risks," and even when access appears granted, accounts are often already flagged by internal controls, rendering them non-functional for trading or withdrawals.
Regulators globally are attempting to adapt. In Thailand, where citizens’ bank accounts frequently serve as money mules for cyberscams originating in neighboring Myanmar and Cambodia, new legislation has enhanced KYC monitoring, imposed limits on daily transactions, and strengthened oversight bodies’ authority to suspend accounts. The US Financial Crimes Enforcement Network issued a warning against KYC deepfakes and the use of VCams in late 2024, urging platforms to monitor broader transaction patterns for signs of money laundering. For scammers, any new security or reporting requirements will undoubtedly increase the difficulty of their operations. However, as Ngo aptly concludes, "it’s not going to stop them. It’s just a matter of time."