A financially motivated data theft and extortion group, operating under the moniker TeamPCP, has unleashed a sophisticated wiper attack that aims to exploit the ongoing geopolitical tensions surrounding Iran, with the malware specifically targeting systems that utilize Iran’s time zone or have Farsi set as their default language. This aggressive campaign, which materialized over the past weekend, leverages a self-propagating worm that infiltrates poorly secured cloud services, posing a significant threat to Iranian infrastructure and data.
TeamPCP, a relatively new entrant in the cybercrime landscape, began its malicious activities in December 2025. Their modus operandi involves compromising corporate cloud environments by exploiting vulnerabilities in exposed Docker APIs, Kubernetes clusters, and Redis servers, as well as the React2Shell vulnerability. Once inside a victim’s network, the group engages in lateral movement, siphoning authentication credentials with the ultimate goal of extorting victims, often through communications on Telegram. The group’s operational efficiency and reach are further amplified by their strategic use of the Internet Computer Protocol (ICP) canister, a tamperproof, blockchain-based system that hosts both code and data, making their infrastructure highly resilient to takedown attempts. This innovative use of decentralized technology has led security researchers to dub their infrastructure "CanisterWorm."
The recent wiper campaign represents a concerning escalation in TeamPCP’s tactics. Security firm Flare, in a profile published in January, highlighted TeamPCP’s expertise in weaponizing exposed control planes rather than focusing on endpoint exploits. Their primary targets are cloud infrastructure, with Microsoft Azure (61%) and Amazon Web Services (AWS) (36%) accounting for a staggering 97% of their compromised servers. Assaf Morag of Flare noted that TeamPCP’s strength lies not in novel exploits but in the "large-scale automation and integration of well-known attack techniques." He elaborated, "The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem." This industrialization approach allows them to rapidly scale their operations and maximize their impact.
Adding another layer of complexity to TeamPCP’s operations, on March 19th, the group executed a supply chain attack against Trivy, a popular vulnerability scanner developed by Aqua Security. They successfully injected credential-stealing malware into official releases distributed via GitHub Actions. While Aqua Security has since removed the malicious files, the security firm Wiz confirmed that the attackers managed to publish compromised versions capable of exfiltrating sensitive information, including SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets.
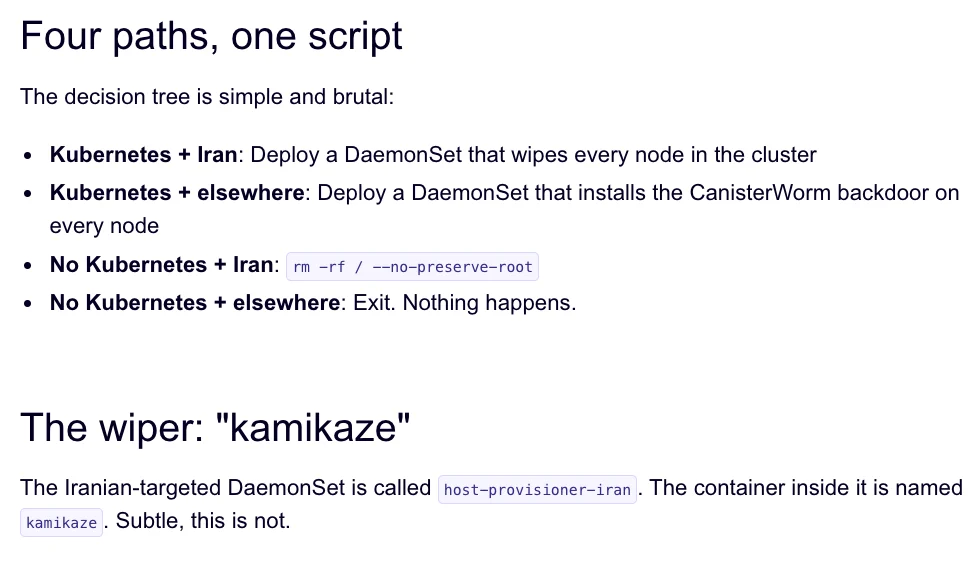
The same technical infrastructure used in the Trivy attack was subsequently leveraged to deploy the new wiper payload. Charlie Eriksen, a security researcher at Aikido, detailed in a blog post on Sunday how the wiper component checks the victim’s system for indicators of Iranian origin. If the user’s timezone and locale are identified as corresponding to Iran, and if the victim has access to a Kubernetes cluster, the malware is designed to systematically destroy data across every node within that cluster. In instances where a Kubernetes cluster is not accessible, the wiper will proceed to wipe the local machine. The visual representation of this malicious activity, as captured by Aikido, depicts the intricate paths the malware takes to identify and target its victims, emphasizing the deliberate nature of its design.

TeamPCP’s audacious activities extend beyond technical exploits; they are also actively bragging about their successes in a Telegram group. They claim to have pilfered vast amounts of sensitive data from major corporations, including a significant multinational pharmaceutical firm. Eriksen observed that after compromising Aqua Security for a second time, the attackers gained access to numerous GitHub accounts and began spamming them with irrelevant messages. This behavior, Eriksen suggests, is a deliberate attempt to showcase their extensive access and control. The credentials they have obtained are likely a fraction of their total haul, indicating a much broader and deeper compromise.
The spammed GitHub messages are also theorized to be a tactic to artificially inflate the visibility of malicious code packages in GitHub searches. Risky Business reporter Catalin Cimpanu, in a recent newsletter, pointed out that attackers frequently resort to pushing meaningless commits or utilizing services that artificially boost "stars" and "likes" on repositories to ensure their tainted code remains at the top of search results. This practice highlights a growing problem on platforms like GitHub, where malicious actors are exploiting the platform’s design to gain prominence.
This latest incident marks the second significant supply chain attack involving Trivy in as many months. At the end of February, Trivy was targeted by an automated threat known as HackerBot-Claw, which exploited misconfigured workflows in GitHub Actions to steal authentication tokens. Eriksen believes that TeamPCP likely utilized the access gained from the initial Aqua Security compromise to orchestrate this weekend’s attack. However, it remains uncertain whether the wiper successfully deleted any data, as the malicious payload was reportedly active for a limited period over the weekend.
Eriksen noted that TeamPCP has been dynamically updating and deploying their malicious code, rapidly introducing new features. When the malicious canister was not actively distributing malware, it was redirecting visitors to a Rick Roll video on YouTube. This erratic behavior suggests a degree of theatricality and an intent to provoke, with Eriksen speculating that the focus on Iran might be a deliberate ploy to garner attention and create a sense of chaos. He characterized the group’s actions as embodying a "Chaotic Evil" persona.
Cimpanu further observed that supply chain attacks are on the rise, as threat actors are increasingly recognizing their efficiency. His reporting has documented an alarming number of such incidents since 2024. He emphasized the need for enhanced security measures not only from security firms but also from platforms like GitHub. The inherent nature of platforms designed for copying and creating new versions of projects makes it a formidable challenge to detect malicious additions to legitimate repositories.
An update on March 23rd revealed that Wiz is reporting TeamPCP’s involvement in another supply chain attack, this time targeting the KICS vulnerability scanner from Checkmarx. The KICS GitHub Action was compromised between 12:58 and 16:50 UTC on that day, with credential-stealing malware being pushed. This latest incident underscores the persistent and evolving nature of TeamPCP’s attacks, demonstrating their continued ability to exploit trusted software supply chains to achieve their data theft and extortion objectives.









