In a comprehensive Question and Answer session, Ghosh and Upadhyay illuminated the fundamental differences between quantum and classical computing, dissected the unique security challenges posed by quantum technology, and outlined crucial steps for developers to fortify these nascent systems for widespread adoption.
What Distinguishes a Quantum Computer from its Traditional Counterpart?
Ghosh explained the foundational difference lies in the fundamental unit of information. Traditional computers operate on "bits," analogous to light switches that are definitively either "on" (represented by 1) or "off" (represented by 0). Programming these computers involves crafting algorithms and employing educated guesses to devise optimal solutions, which are then translated into machine-level instructions – a precise set of directives dictating the state of each bit.
Quantum computers, however, harness "qubits." These quantum bits are far more sophisticated, possessing the remarkable ability to exist in multiple states simultaneously, a phenomenon known as superposition. Furthermore, qubits can be interconnected in a profound way called entanglement, where the state of one qubit is intrinsically linked to the state of others, regardless of distance. By leveraging superposition and entanglement, quantum computers can process an exponentially greater volume of data compared to their bit-based counterparts, even when utilizing a similar number of qubits.
This exponential processing power holds immense promise for accelerating workflows across a multitude of industries. In the pharmaceutical sector, for instance, quantum computers can rapidly analyze vast datasets to predict the efficacy of novel drug candidates, dramatically streamlining the research and development pipeline. This could translate into billions of dollars in savings and shave years off the arduous process of drug discovery, testing, and fabrication.
What are the Principal Security Weaknesses Plaguing Current Quantum Computers?
Upadhyay highlighted a significant hurdle: the current lack of an efficient and scalable method for verifying the integrity of programs and compilers used by quantum computers, many of which are developed by third-party entities. This deficiency leaves users’ sensitive corporate and personal information vulnerable to a trifecta of threats: theft, tampering, and reverse engineering.
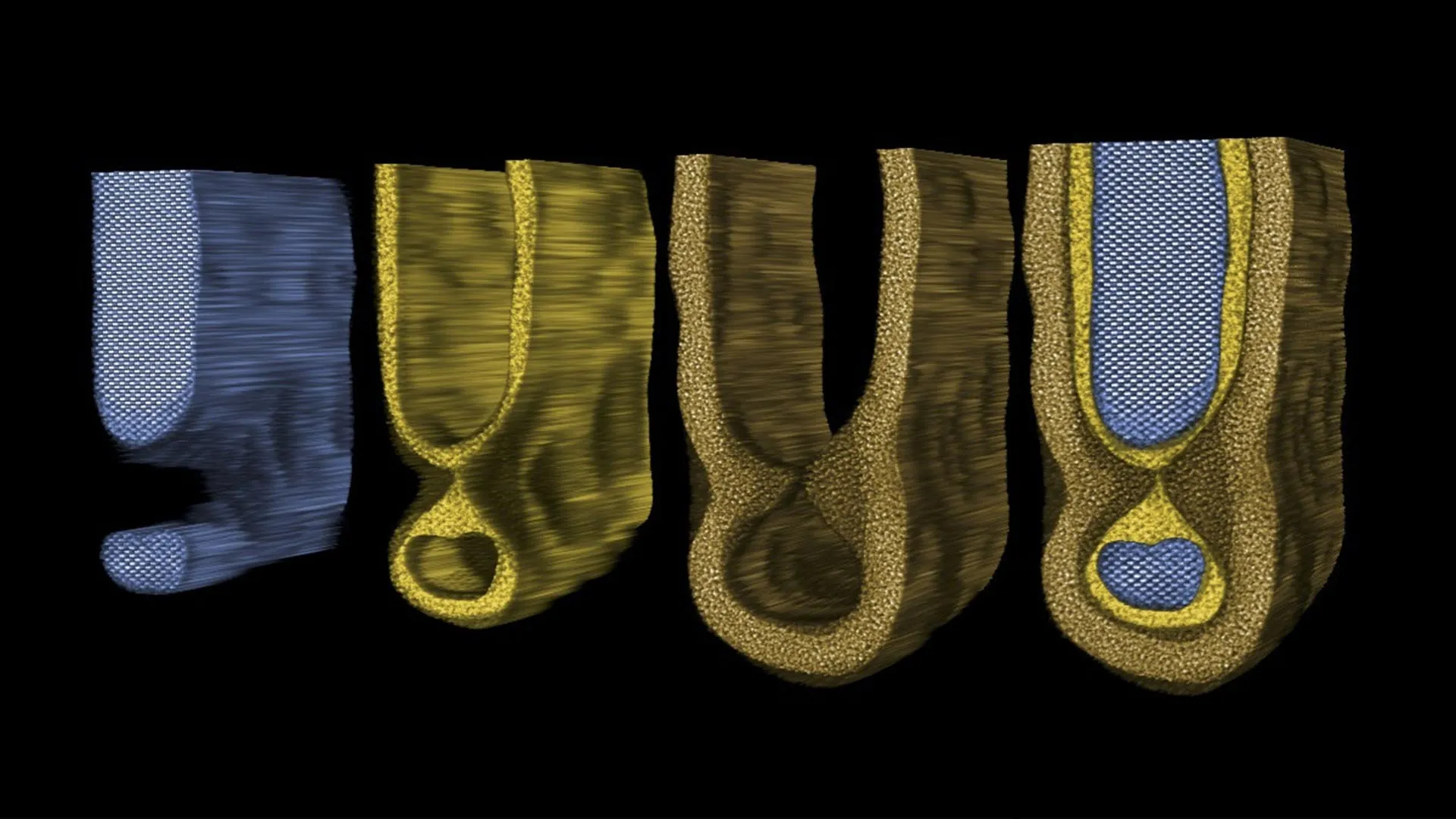
A core vulnerability stems from the direct integration of businesses’ intellectual property into the very circuits of quantum computing algorithms. These circuits are meticulously designed to process highly specialized problems involving proprietary client data and other sensitive information. If these circuits are compromised, attackers could gain access to invaluable company-created algorithms, sensitive financial positions, or even critical infrastructure details. Moreover, the very interconnectedness that empowers qubits to operate with such remarkable efficiency inadvertently creates a security Achilles’ heel. Unwanted entanglement, colloquially termed "crosstalk," can inadvertently leak sensitive information or disrupt computational processes when multiple users share the same quantum processor.
How are Commercial Quantum Providers Addressing Security Concerns? Are Traditional Security Methods Applicable?
Upadhyay emphasized that conventional security methodologies are ill-suited for the quantum realm. The fundamental differences in how quantum systems operate render traditional security protocols ineffective. Consequently, he believes many companies are ill-equipped to confront these emerging security faults. Presently, commercial quantum providers are primarily focused on ensuring the reliability and operational effectiveness of their systems. While such optimizations can indirectly mitigate certain security vulnerabilities, the unique assets of quantum computing – including circuit topology, encoded data, and hardware-embedded intellectual property systems – generally lack comprehensive end-to-end protection. Although the nascent nature of quantum computing currently disincentivizes widespread targeted attacks, this landscape is poised to shift dramatically as these powerful machines become increasingly integrated into industry and our daily lives, transforming them into prime targets for sophisticated cyber adversaries.
What Steps Can Developers Take to Enhance Security in Quantum Computers?
Ghosh advocated for a "ground-up" approach to quantum computer security. At the device level, developers must prioritize mitigating crosstalk and other forms of "noise" – external interference that can compromise information integrity or impede effective data transfer. At the circuit level, robust techniques such as scrambling and sophisticated information encoding are imperative to safeguard the data embedded within the system. Moving to the system level, hardware must be meticulously compartmentalized. This involves segmenting business data into distinct groups, implementing granular user access controls based on defined roles, and thereby layering additional protection onto sensitive information. Crucially, the development of novel software techniques and extensions is essential to enable the detection and fortification of quantum programs against an evolving array of security threats.
The researchers’ overarching hope is that their paper will serve as a catalyst, drawing the attention of experts from diverse fields – including mathematics, computer science, engineering, and physics – to the critical domain of quantum security, thereby fostering a collaborative effort to address this rapidly growing and vital area of research. This groundbreaking work was further supported by the U.S. National Science Foundation and Intel, underscoring its significance and potential impact. Additional co-authors, including Abdullah Ash Saki, who also recently completed his doctorate in electrical engineering at Penn State, contributed to this vital research.