A financially motivated data theft and extortion group, identified as TeamPCP, has launched a sophisticated wiper attack with the explicit aim of disrupting systems operating within Iran’s temporal and linguistic sphere, leveraging a self-propagating worm that exploits vulnerabilities in inadequately secured cloud services. This campaign, which emerged over the past weekend, signifies a concerning escalation by the relatively new cybercrime entity, which has been actively compromising corporate cloud environments since December 2025. TeamPCP’s modus operandi involves targeting exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability, facilitating lateral movement within victim networks to exfiltrate authentication credentials. Subsequently, the group extorts victims through the Telegram messaging platform, creating a potent combination of data destruction and financial coercion.
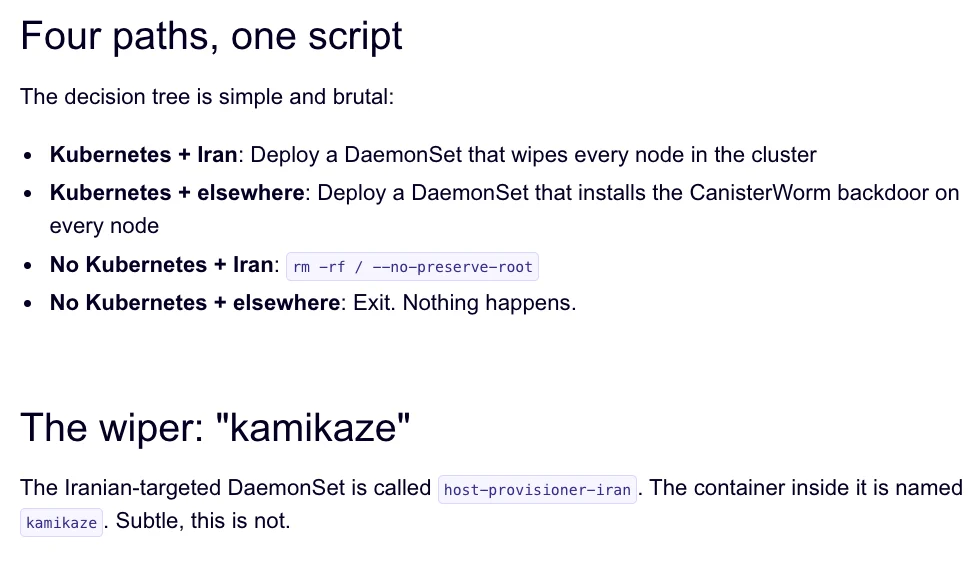
The technical underpinnings of this wiper attack are particularly noteworthy. Researchers at Aikido.dev, specifically security researcher Charlie Eriksen, have detailed how TeamPCP is orchestrating its campaigns through an Internet Computer Protocol (ICP) canister, a system of tamperproof, blockchain-based smart contracts. This infrastructure, which Aikido dubs "CanisterWorm," offers a high degree of resilience against takedown attempts due to its distributed nature. As long as the operators continue to pay the virtual currency fees, these canisters remain accessible, serving as command-and-control servers for their malicious activities. The CanisterWorm infrastructure is designed to deliver a payload that, upon detecting a system configured with Iran’s time zone or Farsi as its default language, initiates a data-wiping sequence. If the victim is within an Iranian Kubernetes cluster, the worm will proceed to destroy data across all nodes in that cluster. In scenarios where a Kubernetes cluster is not accessible, the wiper targets and wipes the local machine.
TeamPCP’s operational strategy, as highlighted by security firm Flare, centers on the weaponization of exposed control planes rather than the exploitation of individual endpoints. Their primary targets are cloud infrastructure, with a significant majority of compromised servers residing on Azure (61%) and AWS (36%), accounting for a combined 97%. Flare’s analysis, published in January, underscores that TeamPCP’s effectiveness stems not from novel exploits or proprietary malware, but from the large-scale automation and integration of well-established attack techniques. Assaf Morag of Flare articulated this, stating, "TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques. The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem."
A critical element of TeamPCP’s recent activities involved a supply chain attack executed on March 19th against Trivy, a vulnerability scanner developed by Aqua Security. The attackers successfully injected credential-stealing malware into official releases hosted on GitHub Actions. While Aqua Security has since removed the malicious files, security firm Wiz has reported that the attackers managed to publish tainted versions of Trivy capable of exfiltrating sensitive information, including SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets. This supply chain compromise appears to have provided TeamPCP with the necessary access and infrastructure to deploy the CanisterWorm and its associated wiper payload over the weekend.

The ICP canister used by TeamPCP is a pivotal component of their operation. These canisters, essentially smart contracts residing on the Internet Computer, encapsulate both code and data, offering a secure and tamperproof environment. Their ability to serve web content directly and their distributed architecture make them highly resistant to traditional takedown efforts. The group’s self-proclaimed successes are often shared within a Telegram group, where they boast about their ability to steal vast amounts of sensitive data from major corporations, including a significant multinational pharmaceutical firm.
Eriksen observed that following the second compromise of Aqua Security, TeamPCP initiated spamming GitHub accounts with junk messages. He speculated that this was a deliberate act to boost the visibility of their compromised code packages in GitHub searches, a tactic also noted by Risky Business reporter Catalin Cimpanu in his newsletter, "GitHub is Starting to Have a Real Malware Problem." Cimpanu detailed how attackers frequently resort to pushing meaningless commits or utilizing services that artificially inflate a repository’s popularity to keep malicious packages prominently displayed.
This recent wiper campaign is not the first major supply chain attack involving Trivy. In late February, Trivy was targeted by HackerBot-Claw, an automated threat that exploited misconfigured GitHub Actions workflows to steal authentication tokens. Eriksen suggests that TeamPCP likely leveraged the access gained from the initial attack on Aqua Security to carry out this latest operation. However, he cautioned that it remains uncertain whether the wiper successfully destroyed any data on victim systems, as the malicious payload was active for a limited duration over the weekend.
The dynamic nature of TeamPCP’s operations is further evidenced by their rapid modification and deployment of malicious code. Eriksen noted that when the malicious canister was not actively serving malware downloads, it was directing visitors to a Rick Roll video on YouTube. This erratic behavior leads Eriksen to believe that the "Iran thing" might be partly a means of generating attention, describing the group’s approach as "Chaotic Evil."
The increasing frequency of supply chain attacks, as documented by Cimpanu, highlights a growing trend among threat actors who are recognizing their efficiency. While security firms are adept at identifying these threats, Cimpanu emphasizes the crucial need for enhanced security measures from platforms like GitHub. He notes the inherent challenge in distinguishing malicious additions within forks and clones of legitimate repositories, posing a significant engineering problem for effective mitigation. The ongoing evolution of TeamPCP’s tactics, coupled with the inherent vulnerabilities in cloud infrastructure and open-source development platforms, presents a persistent and evolving threat landscape. The "CanisterWorm" attack serves as a stark reminder of the sophisticated methods employed by financially motivated cybercriminals to exploit global vulnerabilities and pursue their illicit objectives.









