A sophisticated new phishing-as-a-service, dubbed Starkiller, is revolutionizing cybercrime by allowing attackers to bypass traditional detection methods and exploit even multi-factor authentication (MFA). Unlike conventional phishing kits that rely on static, easily identifiable copies of login pages, Starkiller employs a dynamic relay system. This innovative approach presents victims with seemingly legitimate login pages by loading the actual brand’s website, while discreetly acting as an intermediary. The service captures and forwards victim credentials, including usernames, passwords, and critically, MFA codes, to the legitimate site, simultaneously relaying the site’s responses back to the victim. This creates a seamless, yet deceptive, experience for the target, making detection significantly more challenging.
The operational complexity of traditional phishing kits often deters less technically inclined criminals. These kits require significant expertise in configuring servers, domain names, SSL certificates, and proxy services – a repetitive and arduous technical undertaking. Starkiller, however, abstracts away this complexity, offering a user-friendly platform for cybercriminals. According to an in-depth analysis by security firm Abnormal AI, Starkiller empowers its users to select a target brand, such as Apple, Facebook, Google, or Microsoft, and then generates a deceptive URL. This URL is designed to visually mimic the legitimate domain, but it cleverly routes traffic through the attacker’s infrastructure.
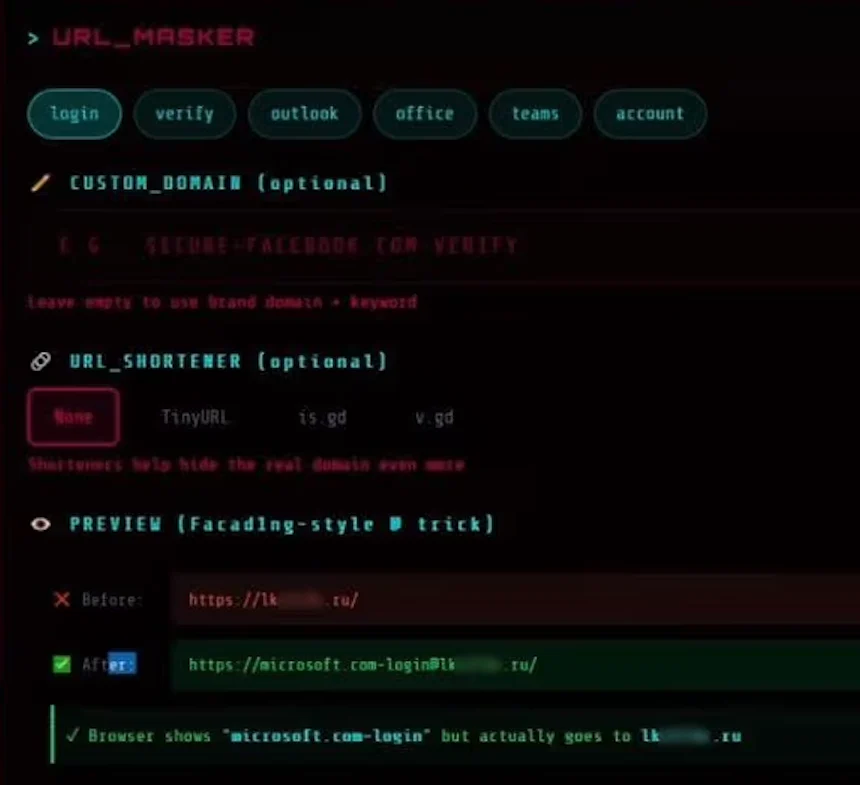
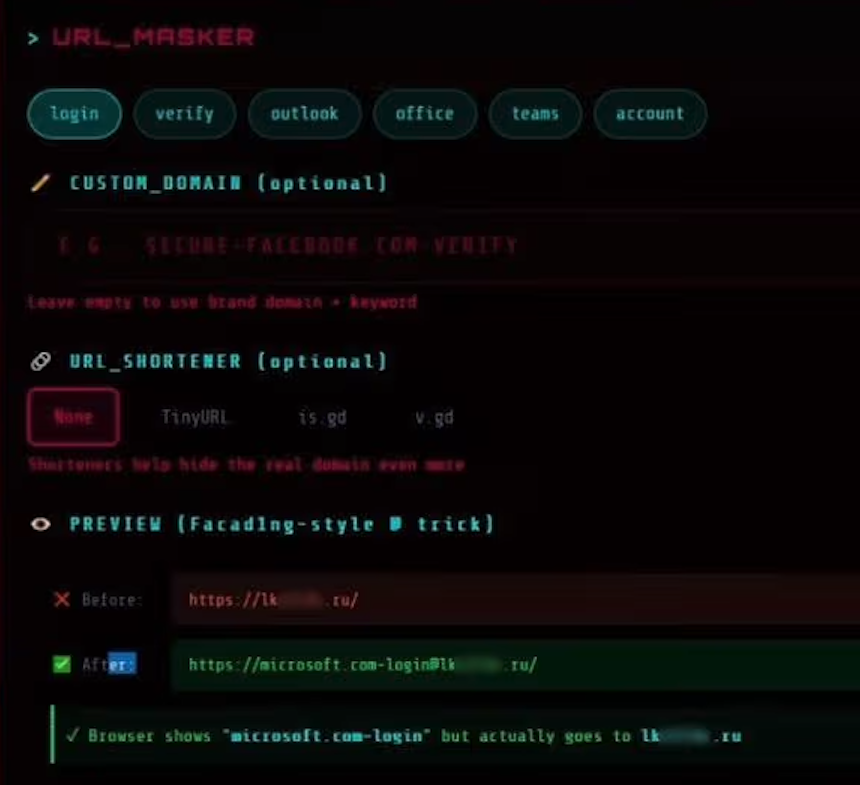
A prime example of Starkiller’s URL manipulation technique involves a phishing link targeting Microsoft customers. The generated link might appear as "login.microsoft.com@[malicious/shortened URL here]." This clever use of the "@" symbol in a URL is an old but effective trick. In URL parsing, any data preceding the "@" is interpreted as the username, while the data following it is considered the actual destination. Therefore, the victim, seeing "login.microsoft.com" at the beginning of the string, is led to believe they are interacting with the genuine Microsoft login page. The actual malicious landing page, however, is the domain that follows the "@" symbol, often a shortened or obfuscated URL, potentially ending in a less reputable top-level domain like ".ru" as observed in some examples. The service also boasts the integration of various URL-shortening services, further obscuring the true origin of the malicious link.
Upon selection of the target URL, Starkiller provisions a Docker container. Within this container, a headless Chrome browser instance is launched. This headless browser then navigates to and loads the genuine login page of the targeted brand. As described by Abnormal AI researchers Callie Baron and Piotr Wojtyla in their detailed blog post, this container functions as a man-in-the-middle reverse proxy. It intercepts all user inputs – keystrokes, form submissions, and session tokens – and forwards them to the legitimate website. Simultaneously, it captures the responses from the legitimate site and relays them back to the victim’s browser. This entire process occurs in real-time, with every piece of data passing through attacker-controlled infrastructure and being meticulously logged.
Starkiller provides its users with unprecedented real-time session monitoring capabilities. Attackers can effectively live-stream the victim’s screen as they interact with the compromised login page. This granular insight into user behavior allows for more targeted and effective exploitation. Beyond screen mirroring, the platform offers a comprehensive suite of features designed to maximize the success of phishing campaigns. These include:
- Keylogger Functionality: Every keystroke entered by the victim is captured and recorded.
- Cookie and Session Token Theft: Crucial for direct account takeover, stolen session cookies and tokens grant attackers authenticated access to the victim’s accounts.
- Geo-tracking of Targets: The service can pinpoint the geographical location of victims, potentially aiding in further social engineering or identifying high-value targets.
- Automated Telegram Alerts: Attackers receive instant notifications via Telegram whenever new credentials are compromised, enabling immediate action.
- Campaign Analytics Dashboard: Mimicking the sophistication of legitimate Software-as-a-Service (SaaS) platforms, Starkiller provides operators with detailed performance metrics. This includes visit counts, conversion rates, and performance graphs, offering insights into the effectiveness of their phishing campaigns.
Perhaps the most alarming capability of Starkiller is its ability to effectively neutralize multi-factor authentication (MFA). Because the victim is, in essence, authenticating with the real website through the Starkiller proxy, any MFA codes entered are also relayed in real-time to the legitimate service. The attacker, having captured the resulting session cookies and tokens from this process, gains fully authenticated access to the victim’s account. As Baron and Wojtyla explain, "When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed." This renders a critical security layer virtually useless.
The image accompanying this analysis showcases the "URL Masker" feature, highlighting the options available for configuring malicious links. This visual element underscores the user-friendly interface and the emphasis on creating deceptive URLs that are difficult for victims to discern as malicious.
Starkiller is not an isolated operation but rather part of a broader ecosystem of cybercrime services offered by a threat group known as Jinkusu. This group maintains an active user forum, fostering a community where customers can exchange techniques, request new features, and troubleshoot deployment issues. Jinkusu also offers a-la-carte features, such as the ability to harvest email addresses and contact information from compromised sessions. This harvested data can then be leveraged to build targeted lists for subsequent, more personalized phishing campaigns.
From a cybersecurity perspective, Starkiller represents a significant evolution in phishing tactics. Its apparent success is likely to inspire other cybercriminal organizations to adopt similar methodologies. The service offers a compelling advantage by eliminating the substantial upfront costs and the constant logistical challenges associated with managing multiple phishing domains. Furthermore, it effectively circumvents traditional phishing detection mechanisms, such as domain blocklisting and static page analysis, which are rendered obsolete by Starkiller’s dynamic and proxy-based approach.
Moreover, Starkiller drastically lowers the barrier to entry for novice cybercriminals. The platform’s user-friendly interface and automated processes mean that individuals with limited technical expertise can launch sophisticated phishing attacks with a high degree of success. This democratizes cybercrime, potentially leading to an increase in the volume and sophistication of attacks.
In conclusion, Starkiller signifies a substantial escalation in phishing infrastructure, mirroring a wider trend towards commoditized, enterprise-grade cybercrime tooling. The combination of advanced URL masking, seamless session hijacking, and the effective bypass of MFA capabilities empowers low-skilled cybercriminals with attack capabilities that were previously the domain of highly skilled and resourced threat actors. This development poses a significant and evolving threat to individuals and organizations alike, demanding continuous innovation in defensive cybersecurity strategies.









