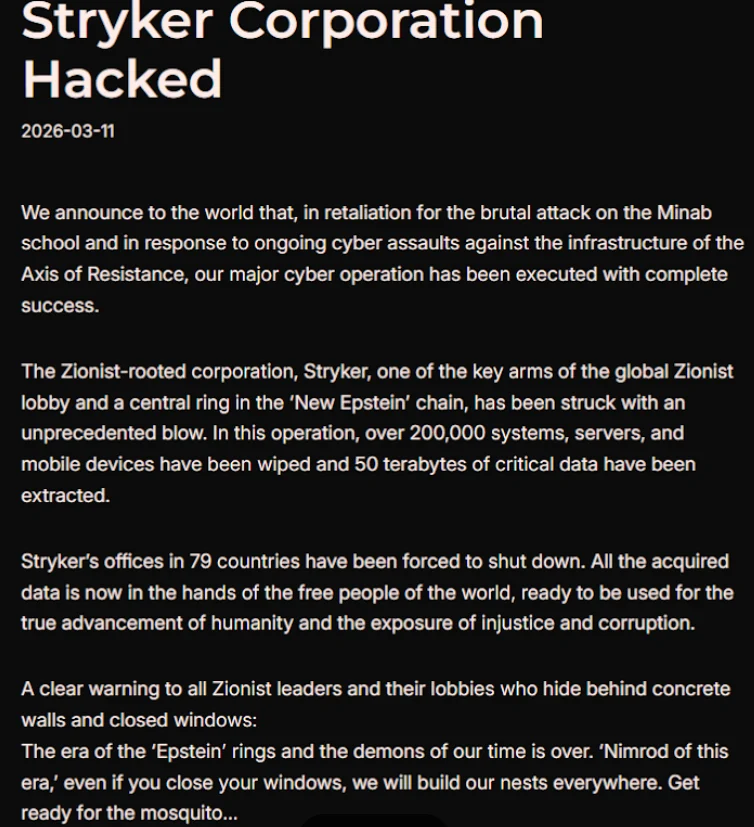
Handala, in a detailed statement disseminated via Telegram, asserted that Stryker’s operations across 79 countries have been forced into a shutdown. The group claims to have erased data from more than 200,000 systems, servers, and mobile devices belonging to the medical technology giant. The manifesto posted by Handala, which was accompanied by an image showing their insignia, declared, "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption." This rhetoric suggests a motive rooted in ideological activism, aiming to leverage the compromised data for broader political or social objectives.
The alleged wiper attack is framed by Handala as a retaliatory measure. The group stated their actions were in direct response to a missile strike that occurred on February 28th, which hit an Iranian school and resulted in the tragic deaths of at least 175 people, predominantly children. Adding a significant layer to this narrative, The New York Times reported on the same day as the Handala claim that an ongoing military investigation has concluded that the United States bears responsibility for this deadly Tomahawk missile strike. This linkage between the cyberattack and a high-profile geopolitical event suggests a deliberate and calculated response designed to exert pressure and signal disapproval.
The operational capabilities and affiliations of Handala have been a subject of recent scrutiny. Palo Alto Networks, a leading cybersecurity firm, profiled Handala among several Iran-linked hacker groups in a comprehensive report. Palo Alto Networks asserts that Handala has connections to Iran’s Ministry of Intelligence and Security (MOIS). According to their analysis, Handala first emerged in late 2023 and is believed to be one of multiple online personas utilized by Void Manticore, an actor identified as being affiliated with the MOIS. This association lends significant credibility to Handala’s claims and raises concerns about state-sponsored cyber activity.
Stryker, a company with a substantial global footprint, employs approximately 56,000 individuals across 61 countries, according to its official website. The impact of the Handala attack is clearly being felt at multiple levels of the organization. The aforementioned voicemail message at the Michigan headquarters, stating a "building emergency," is a stark indicator of the operational paralysis. Further details emerged from Ireland, where the Irish Examiner reported that Stryker employees are now relying on WhatsApp for critical updates regarding their return to work. An unnamed employee quoted in the report described a complete network outage, stating that "anything connected to the network is down, and that ‘anyone with Microsoft Outlook on their personal phones had their devices wiped.’" This suggests a broad and deep penetration of Stryker’s IT infrastructure.
The extent of the damage in Cork, Ireland, the company’s major hub, was further detailed by the Irish Examiner. Multiple sources confirmed that systems in the Cork headquarters were "shut down," and employee-held Stryker devices had been "wiped out." Critically, the login pages displayed on these compromised devices were reportedly defaced with the Handala logo, serving as a clear assertion of responsibility and a visual confirmation of the attack.
While wiper attacks are typically characterized by malicious software designed to systematically overwrite and destroy existing data on infected devices, the method employed in the Stryker incident appears to have been more sophisticated. A confidential source with direct knowledge of the attack, speaking to KrebsOnSecurity on condition of anonymity, suggested that the perpetrators may have leveraged a legitimate Microsoft service called Microsoft Intune to execute a "remote wipe" command across all connected devices. Intune is a cloud-based solution designed for IT departments to enforce security and data compliance policies, offering a centralized console for managing and monitoring devices regardless of their geographical location. The use of Intune for malicious purposes is particularly concerning, as it exploits a tool designed for legitimate IT management. Support for this theory can be found in online discussions, including a Reddit thread where individuals claiming to be Stryker employees reported being instructed to urgently uninstall Intune.
The targeting strategy of Handala, as outlined by Palo Alto Networks, primarily focuses on Israel, with occasional excursions beyond this scope when it aligns with a specific agenda. The security firm also notes that Handala has claimed responsibility for previous cyberattacks, including those targeting fuel systems in Jordan and an Israeli energy exploration company. These incidents highlight a pattern of opportunistic attacks, often characterized by swift execution and a focus on supply-chain vulnerabilities. Palo Alto researchers described Handala’s recent activities as "opportunistic and ‘quick and dirty,’ with a noticeable focus on supply-chain footholds (e.g., IT/service providers) to reach downstream victims, followed by ‘proof’ posts to amplify credibility and intimidate targets." This approach suggests a strategy of gaining initial access through service providers or IT infrastructure, thereby maximizing the potential impact on larger organizations.
The manifesto posted by Handala also revealed a potential ideological motivation behind the targeting of Stryker. The group referred to Stryker as a "Zionist-rooted corporation," which is likely an allusion to the company’s 2019 acquisition of OrthoSpace, an Israeli company. This characterization suggests that the attack may be part of a broader anti-Israel sentiment or a broader geopolitical agenda pursued by the Iran-aligned group.
This is a developing story, and further updates will be provided as more information becomes available. The implications of this attack extend beyond Stryker, highlighting the increasing sophistication and potential state sponsorship of cyber operations originating from Iran. The use of legitimate IT management tools for destructive purposes also presents a new challenge for cybersecurity professionals tasked with defending critical infrastructure and global corporations. The incident underscores the persistent threat posed by advanced persistent threats (APTs) and the evolving tactics employed by nation-state-backed hacking groups in the global cybersecurity landscape. The intertwining of cyber warfare with geopolitical events and ideological motivations continues to be a significant concern for international security.









