
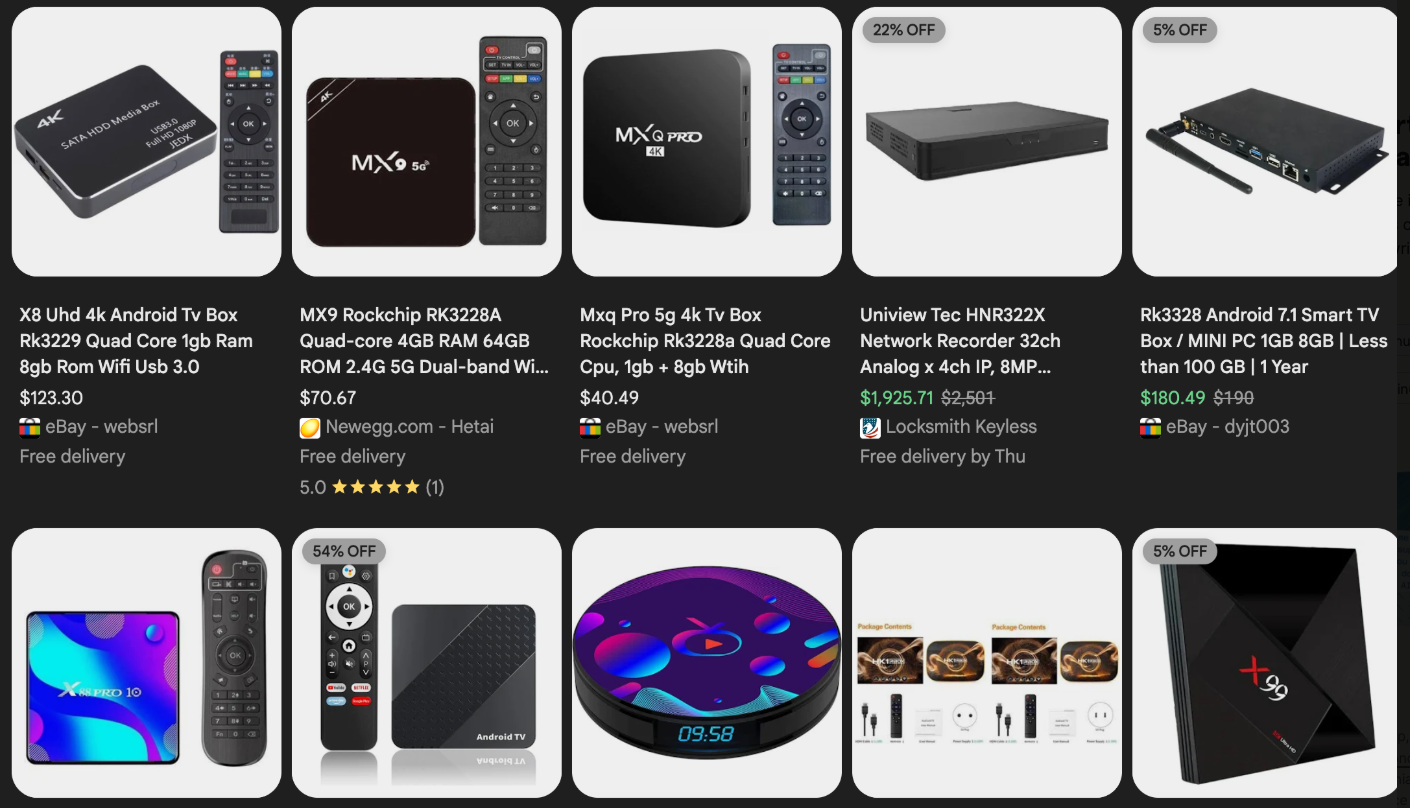
The digital landscape is under siege as the Kimwolf botnet, a rapidly expanding cyber threat, has infected over 2 million devices globally, fundamentally undermining the perceived security of internal networks. This sophisticated malware orchestrates a range of malicious activities, from ad fraud and account takeovers to large-scale data scraping and devastating Distributed Denial-of-Service (DDoS) attacks, capable of incapacitating websites for extended periods. The true insidious nature of Kimwolf lies not just in its scale, but in its stealthy propagation method: it leverages "residential proxy" networks to tunnel back into the local networks of unsuspecting users, breaching the presumed safety of home and office firewalls. These residential proxy networks, often marketed as tools for anonymizing and localizing web traffic, are frequently bundled with dubious mobile applications, games, and, alarmingly, unofficial Android TV boxes purchased from major e-commerce platforms like Amazon, BestBuy, Newegg, and Walmart. These devices, ranging from $40 to $400 and advertised under a multitude of obscure brands, often promise free access to subscription video content, but come with the hidden cost of becoming a node in a vast botnet. A significant portion of Kimwolf infections, over two-thirds according to security firm Synthient, are these Android TV boxes, which notoriously lack built-in security or authentication mechanisms.

The threat extends to Internet-connected digital photo frames as well. Researchers from Quokka detailed in November 2025 critical security flaws in Android-based digital picture frames utilizing the "Uhale" app, a vulnerability present even in Amazon’s top-selling frames as of March 2025. The core security issues with these devices and unofficial Android TV boxes are twofold: pre-installed malware, or the necessity of downloading unofficial apps and malware to achieve their advertised functionality, often turning the device into a resold residential proxy node. The second, and perhaps more critical, vulnerability is the reliance on microcomputer boards with no inherent security or authentication, allowing for simultaneous compromise of multiple devices on the same network with a single command.
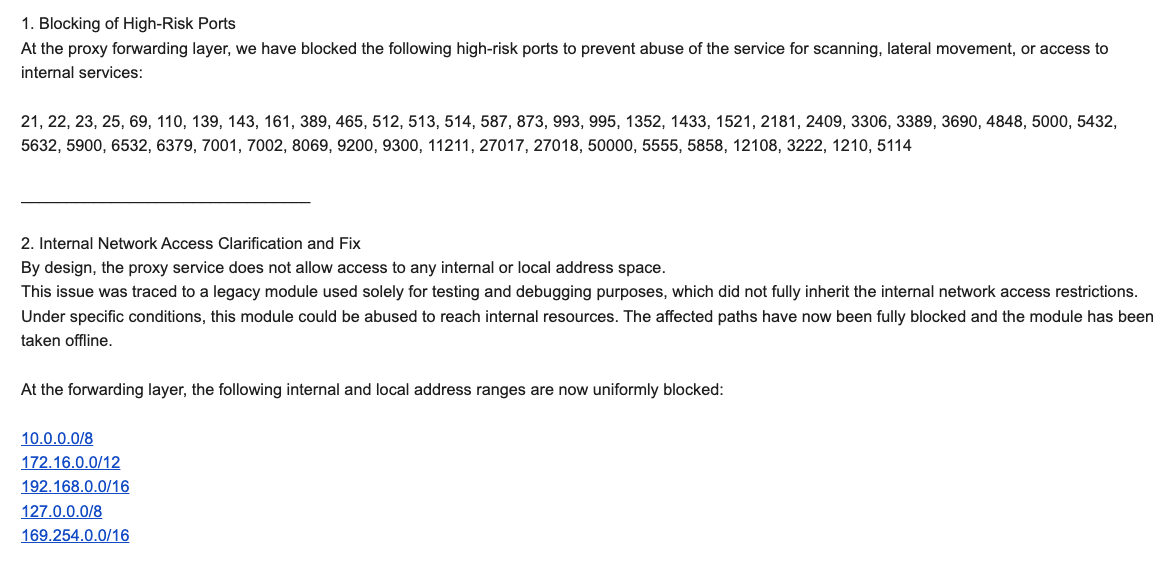
This alarming confluence of security failings became evident in October 2025 when Benjamin Brundage, a 22-year-old computer science student and founder of Synthient, began meticulously tracking Kimwolf’s proliferation. Brundage, whose firm specializes in detecting and analyzing proxy network abuse, suspected Kimwolf was an Android variant of the Aisuru botnet, previously misattributed for major DDoS attacks. Kimwolf’s explosive growth, Brundage explained, was facilitated by a critical flaw in numerous large residential proxy services: insufficient safeguards against customers forwarding requests to internal servers of proxy endpoints. While most proxy services block requests to RFC-1918 private IP address ranges (10.0.0.0/8, 192.168.0.0/16, and 172.16.0.0/12), crucial for home and office networks, Kimwolf operators exploited a loophole. By manipulating Domain Name System (DNS) settings to match these RFC-1918 ranges, they could directly communicate with devices on internal networks. Brundage’s advisory, sent to nearly a dozen proxy providers in mid-December 2025, highlighted this exploit: "It is possible to circumvent existing domain restrictions by using DNS records that point to 192.168.0.1 or 0.0.0.0," enabling attackers to send crafted requests to compromise devices. Many residential proxy services operate on mobile devices, often without explicit user consent, turning phones into proxy nodes through hidden components in games or VPN apps. Synthient’s report further reveals that Kimwolf actors are monetizing the botnet through app installs, selling proxy bandwidth, and offering DDoS capabilities, with an anticipated increase in threat actor interest in accessing proxy networks for malicious purposes.
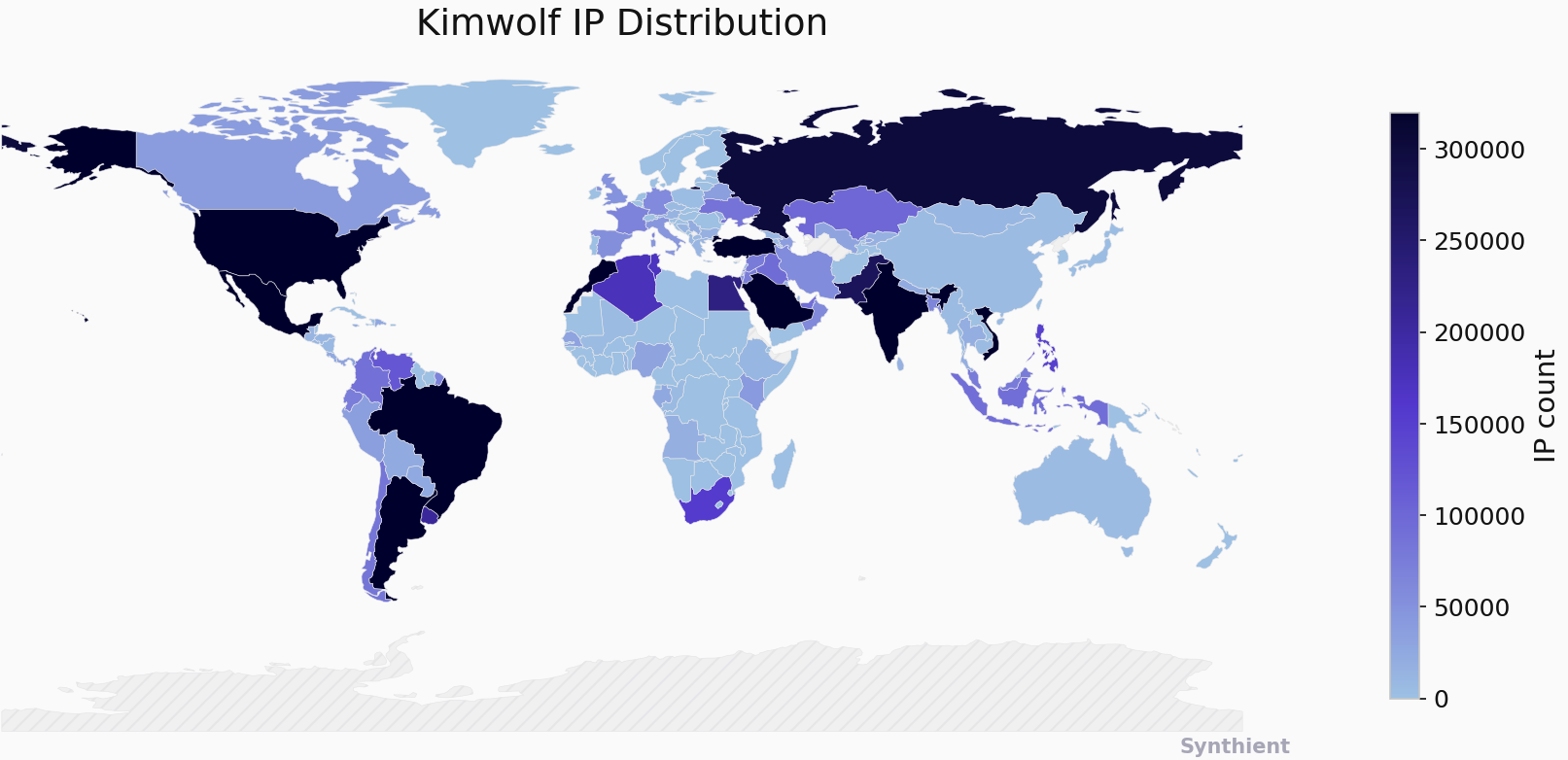
Further investigation by Brundage into unofficial Android TV boxes revealed another critical vulnerability: the default enablement of Android Debug Bridge (ADB) mode. ADB, a diagnostic tool intended for manufacturing, allows remote configuration and firmware updates, but when enabled by default, it creates a security nightmare by accepting unauthenticated connection requests. This allows attackers, through simple commands, to gain unrestricted administrative access to these devices. Brundage observed a direct correlation between new Kimwolf infections and proxy IP addresses rented by China-based IPIDEA, the world’s largest residential proxy network. By early December 2025, Kimwolf had nearly doubled in size by exploiting IPIDEA’s proxy pool, tunneling back through it to infect local networks. Attackers leveraged a specific passphrase, "krebsfiveheadindustries," to unlock malicious downloads. Synthient reported tracking approximately 2 million IPIDEA addresses exploited by Kimwolf in the week prior to December 30, 2025, with the botnet capable of rapidly rebuilding itself to millions of infected systems. Analysis of IPIDEA’s exploited proxy pool revealed that over two-thirds were unsecured Android devices.
Following the discovery of this significant overlap, Brundage notified 11 affected proxy providers on December 17, 2025, allowing them time to address the vulnerabilities before public disclosure. Many of these providers were resellers of IPIDEA. KrebsOnSecurity’s prior inquiries to IPIDEA in October 2025 regarding its alleged benefit from the Aisuru botnet were met with a denial from an IPIDEA employee, "Oliver," who claimed no association and emphasized their rigorous supplier vetting process. However, on the same day Oliver’s email was received, Brundage shared a response from IPIDEA’s security officer, "Byron," who acknowledged a vulnerability in a legacy testing module that had been exploited to access internal resources. IPIDEA claimed to have since patched this issue, blocked DNS resolution to internal IP ranges, and restricted traffic on high-risk ports. Brundage confirmed IPIDEA’s apparent fix, noting that Kimwolf actors had not targeted other proxy services. Riley Kilmer of Spur.us corroborated Brundage’s findings, confirming IPIDEA and its affiliates allowed unfiltered access to local LANs. Kilmer specifically pointed to the "Superbox" Android TV box, previously profiled by KrebsOnSecurity, which leaves ADB running on localhost:5555, facilitating infection when paired with an IPIDEA proxy.
Both Brundage and Kilmer suggest IPIDEA is a successor to the notorious "911S5 Proxy," a service that operated from 2014 to 2022 and was popular on cybercrime forums before its implosion following a data breach disclosure. Research from the University of Sherbrooke in 2022 had already highlighted 911S5’s ability to compromise internal corporate networks. The U.S. Treasury sanctioned alleged creators of 911S5 in July 2024, with the DOJ arresting a key figure. Kilmer also noted IPIDEA operates a sister service, "922 Proxy," marketed as a direct replacement for 911S5. Oxylabs, another proxy provider notified by Synthient, confirmed implementing security changes to block the identified vulnerabilities, though they stated no evidence indicated Kimwolf had exploited their network.
The practical implications of these vulnerabilities are profound. A seemingly innocuous act, such as allowing a guest to use your Wi-Fi, can lead to Kimwolf infection if their phone is compromised with proxy malware. This grants attackers access to your local area network (LAN), enabling them to scan for and infect devices with ADB enabled, such as digital photo frames and unofficial Android TV boxes. The scenario can escalate to attackers modifying router settings to direct traffic through malicious DNS servers, mirroring past threats like the DNSChanger malware.
Chinese security firm XLab has also been instrumental in documenting Kimwolf, initially chronicling the Aisuru botnet. XLab’s latest report details Kimwolf’s tracking beginning October 24, 2025, with its control servers overwhelming Cloudflare’s DNS servers. Early Kimwolf domains dominated Cloudflare’s most sought-after domains list for weeks, surpassing even Google and Apple. XLab’s analysis indicates a misattribution of some early Kimwolf activities to Aisuru, with IPIDEA being heavily abused by Kimwolf. XLab estimates Kimwolf has infected between 1.8 and 2 million devices, with concentrations in Brazil, India, the United States, and Argentina. Measuring the botnet’s true scale is challenging due to dynamic IP allocation and varying device online times across global time zones. XLab researchers noted the Kimwolf author’s peculiar fixation on the author of this report, embedding "easter eggs" related to their name within the botnet’s code.
Determining if devices on a home network are vulnerable or infected with residential proxy malware is difficult for average users. The necessary tools and expertise for such network traffic analysis are beyond the scope of most consumers. Synthient offers a web page where users can check if their public IP address has been seen among Kimwolf-infected systems, and has compiled a list of high-risk unofficial Android TV boxes. Owners of these devices are strongly advised to remove them from their networks. Chad Seaman of Akamai Technologies urges consumers to be wary of these devices and residential proxy schemes, emphasizing that the notion of a secure internal network is outdated, as apps can compromise devices and open networks to external threats. Google’s lawsuit against "BadBox 2.0 Enterprise" in July 2025, targeting over ten million unsanctioned Android streaming devices involved in ad fraud, and an FBI advisory in June 2025 highlighting similar pre-purchase and setup infections, underscore the widespread nature of this threat. Lindsay Kaye of HUMAN Security advises sticking to reputable brands and being cautious about free or low-cost offers and app installations. Utilizing guest Wi-Fi networks for visitors can also prevent unauthorized access to local network resources. While some advocate for flashing custom firmware onto these devices, the majority of buyers are unaware of the inherent risks, seeking free content rather than understanding the security bargain they are making. The entertainment industry’s lack of visible pressure on e-commerce vendors to stop selling these insecure devices, which are largely marketed for video piracy, remains a significant concern. Part II of this series will delve deeper into the individuals behind Kimwolf.









