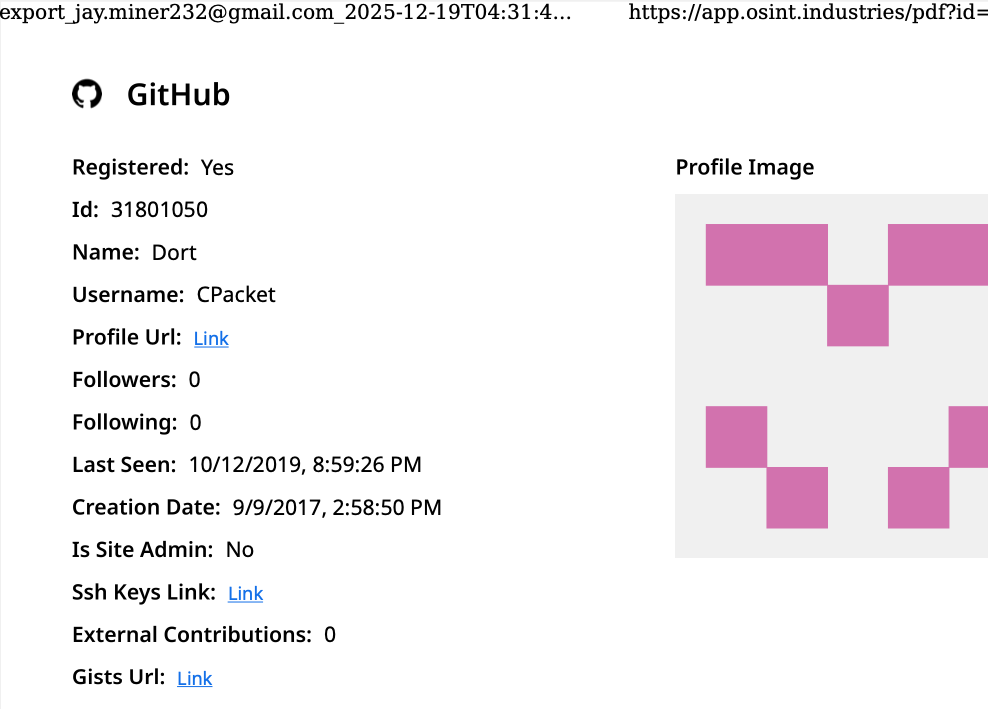
Initial intelligence, surfacing in a 2020 public doxing, painted Dort as a teenager from Canada, born in August 2003, who also operated under the monikers "CPacket" and "M1ce." A comprehensive search on the username "CPacket" via the open-source intelligence platform OSINT Industries yielded a GitHub account. This account, linked to both "Dort" and "CPacket," was established in 2017 and associated with the email address [email protected]. This email address has proven to be a crucial thread in unraveling Dort’s digital footprint.
The cyber intelligence firm Intel 471 has provided further insights, revealing that the email address [email protected] was instrumental in creating accounts on various cybercrime forums between 2015 and 2019. These platforms include Nulled, where the username "Uubuntuu" was employed, and Cracked, where the handle "Dorted" was used. Significantly, Intel 471 reports that both of these forum accounts originated from the same Internet Protocol (IP) address, specifically one registered to Rogers Canada (99.241.112.24). This geographical and service provider link suggests a consistent online presence originating from a specific Canadian locale.
Dort’s early online notoriety stemmed from the immensely popular Microsoft game, Minecraft. Within the game’s vibrant community, Dort was known for "Dortware," a software suite designed to facilitate cheating for players. This early foray into exploiting game mechanics marked a pivotal shift, transitioning Dort from recreational game manipulation to orchestrating more serious criminal enterprises. The skills honed in bypassing Minecraft’s security systems appear to have been a springboard for more sophisticated cybercrimes.
The alias "DortDev" also emerged, showcasing Dort’s active participation in March 2022 on the chat server of the notorious cybercrime syndicate known as LAPSUS$. During this period, Dort offered services for the creation of temporary email addresses, a common tool for obscuring online identities. Additionally, Dort advertised "Dortsolver," a sophisticated piece of code capable of circumventing various CAPTCHA services. These services were designed to thwart automated account abuse, a critical component for large-scale cybercriminal operations. Both of these offerings were prominently featured in 2022 on "SIM Land," a Telegram channel dedicated to the illicit activities of SIM-swapping and account takeovers.
The cyber intelligence firm Flashpoint has further corroborated these findings, indexing 2022 posts on SIM Land attributed to Dort. These posts indicate that Dort developed the disposable email and CAPTCHA bypass services in collaboration with another hacker identified by the handle "Qoft." In a revealing 2022 exchange, Qoft stated, "I legit just work with Jacob," directly referring to Dort as their exclusive business partner. This statement was part of a conversation where Qoft boasted about their combined efforts in defrauding Microsoft. They claimed to have amassed over $250,000 worth of Microsoft Xbox Game Pass accounts by developing a program that mass-generated Game Pass identities using compromised payment card data. This collaboration highlights Dort’s aptitude for both technical development and the monetization of illicit cyber activities.
The identity of "Jacob," Qoft’s business partner, has been a key focus. The breach tracking service Constella Intelligence uncovered a crucial link: the password associated with [email protected] was reused by only one other email address: [email protected]. This discovery aligns intriguingly with the 2020 doxing information that stated Dort’s date of birth was August 2003 (8/03), suggesting a potential age connection.
Further investigation using DomainTools.com for the email address [email protected] revealed its use in 2015 to register several Minecraft-themed domains. These registrations were all assigned to a "Jacob Butler" residing in Ottawa, Canada, and were associated with the Ottawa phone number 613-909-9727. This solidifies the geographical link to Canada and provides a concrete name.
Constella Intelligence’s data further shows that [email protected] was used to create an account on the hacker forum Nulled in 2016. The same email address was also used to create the account name "M1CE" on Minecraft. By pivoting off the password used for their Nulled account, researchers found it was shared across multiple email addresses, including [email protected] and, notably, [email protected]. This latter address is linked to the Ottawa-Carleton District School Board, indicating a connection to the Canadian educational system during Dort’s formative years.
Data indexed by the breach tracking service Spycloud suggests a familial connection, indicating that at one point, Jacob Butler shared a computer with his mother and a sibling. This shared access might explain why their email accounts were connected to the password "jacobsplugs." Despite extensive efforts, neither Jacob Butler nor any other Butler household members responded to requests for comment regarding these findings.
The open-source intelligence service Epieos has identified that [email protected] created the GitHub account "MemeClient." Concurrently, Flashpoint indexed a now-deleted anonymous Pastebin.com post from 2017, which declared "MemeClient" to be the creation of a user named "CPacket"—one of Dort’s earlier aliases. This cross-referencing of accounts and project creations further strengthens the link between these various online personas.
The motivation behind Dort’s aggressive retaliation becomes clearer when examining the events leading up to the current situation. On January 2, 2026, KrebsOnSecurity published an article titled "The Kimwolf Botnet is Stalking Your Local Network." This piece detailed research conducted by Benjamin Brundage, founder of the proxy tracking service Synthient. Brundage’s investigation uncovered that the Kimwolf botmasters were exploiting a little-known vulnerability in residential proxy services. This weakness allowed them to infect poorly defended devices, such as TV boxes and digital photo frames, that were connected to the internal, private networks of proxy endpoints.
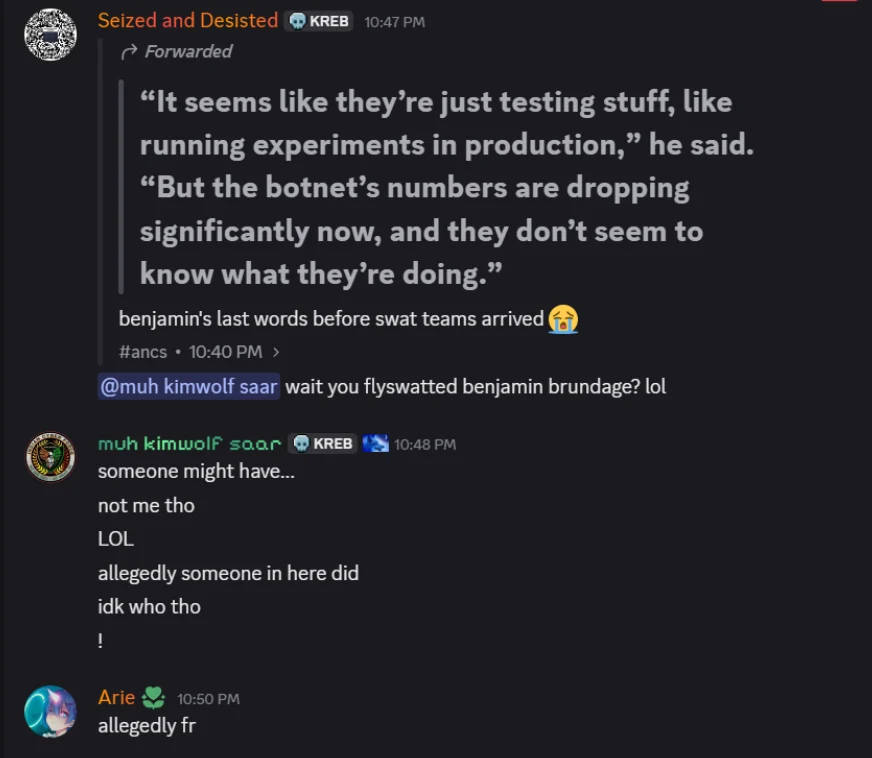
By the time the article went live, Brundage had successfully notified most of the vulnerable proxy providers, who subsequently patched their systems. This critical remediation process significantly hampered Kimwolf’s ability to propagate. Within hours of the article’s publication, Dort created a Discord server under the name of this author. This server immediately began disseminating personal information and issuing violent threats against Brundage, this author, and others involved.
In the subsequent week, Dort and their associates escalated their harassment campaign. They utilized the same Discord server, then named "Krebs’s Koinbase Kallers," to orchestrate a swatting attack against Benjamin Brundage. This involved reposting his home address and personal details. Brundage confirmed to KrebsOnSecurity that local law enforcement officers visited his residence in response to a swatting hoax, which coincided with another server member posting a door emoji and further taunting Brundage.
Adding a disturbing layer to the campaign, someone on the server linked to a crude Soundcloud diss track recorded by the user DortDev. The track, titled "larpgod," included a pinned message from Dort stating, "Ur dead nigga. u better watch ur fucking back. sleep with one eye open. bitch." The lyrics themselves were chilling, with lines like, "It’s a pretty hefty penny for a new front door… If his head doesn’t get blown off by SWAT officers. What’s it like not having a front door?" The implication of orchestrating or encouraging violent SWAT raids is clear and deeply concerning.
Despite the mounting evidence and the severity of the threats, Jacob Butler, when finally contacted, provided a different narrative. Butler spoke briefly with KrebsOnSecurity via telephone, stating he had not noticed earlier requests for comment because he had been largely offline since 2021, following multiple swatting incidents at his home. He acknowledged creating and distributing a Minecraft cheat years ago but insisted he had not played the game in years and was not involved in Dortsolver or any other activities attributed to the Dort nickname after 2021.
"It was a really old cheat and I don’t remember the name of it," Butler stated regarding his Minecraft modification. "I’m very stressed, man. I don’t know if people are going to swat me again or what. After that, I pretty much walked away from everything, logged off and said fuck that. I don’t go online anymore. I don’t know why people would still be going after me, to be completely honest."
When asked about his current occupation, Butler stated that he largely stays at home and assists his mother due to his struggles with autism and social interaction. He adamantly maintained that someone must have compromised his old accounts and is impersonating him online as Dort. "Someone is actually probably impersonating me, and now I’m really worried," Butler said. "This is making me relive everything."
However, Butler’s timeline presents significant discrepancies. For instance, the voice captured in his phone conversation with KrebsOnSecurity bore a striking resemblance to the voice of "Jacob/Dort" heard in a September 2022 Clash of Code competition recording. In that recording, around the six-minute mark, Dort erupts in a profanity-laced tirade that mirrors the aggressive language used in the diss rap threatening Brundage. Dort’s voice is audible again at approximately sixteen minutes, and at around the twenty-six-minute mark, Dort explicitly threatens to swat his opponent.
Butler dismissed this, claiming the voice in the recording was not his but that of an impersonator who likely cloned his voice. "I would like to clarify that was absolutely not me," Butler asserted. "There must be someone using a voice changer. Or something of the sorts. Because people were cloning my voice before and sending audio clips of ‘me’ saying outrageous stuff."
The ongoing investigation into Dort and the Kimwolf botnet continues, with authorities and researchers working to fully dismantle the network and bring those responsible to justice. The case of Dort highlights the evolving landscape of cybercrime, where young individuals with technical skills can rapidly ascend from gaming exploits to orchestrating large-scale criminal operations, posing significant threats to individuals and infrastructure alike. The claims of impersonation and voice cloning, while plausible in the realm of digital deception, are being scrutinized against the backdrop of a consistent pattern of malicious activity linked to the Dort persona. The question of who truly controls Kimwolf and the extent of Dort’s involvement remains a critical focus for cybersecurity professionals.









