
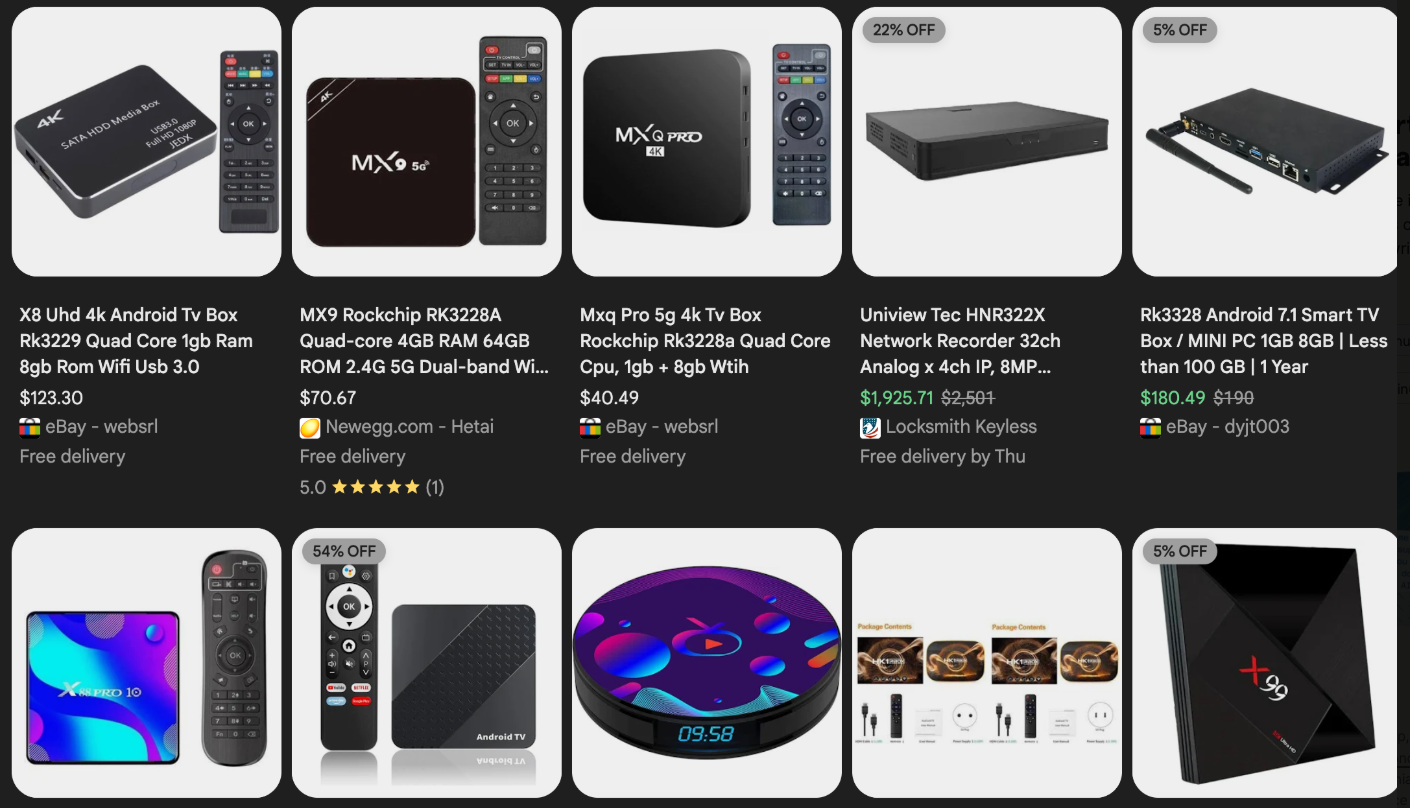
The security of your internal network, once a presumed sanctuary behind your Internet router, is now dangerously compromised by the rapidly expanding Kimwolf botnet, a sophisticated threat that has infected over two million devices globally and is actively exploiting vulnerabilities in residential proxy networks to infiltrate local area networks (LANs). This insidious malware orchestrates a wide array of malicious activities, including ad fraud, account takeover attempts, mass content scraping, and devastating distributed denial-of-service (DDoS) attacks capable of rendering websites inaccessible for extended periods. The core of Kimwolf’s alarming success lies in its ability to tunnel through residential proxy networks and emerge within the assumed safety of private networks, targeting devices hidden behind typical firewall protections. These residential proxy networks, often marketed as tools for anonymizing and localizing web traffic, are frequently bundled with dubious mobile applications and games, or pre-installed on unofficial Android TV boxes and digital photo frames purchased from major e-commerce platforms like Amazon, BestBuy, Newegg, and Walmart. These devices, ranging in price from $40 to $400 and peddled under numerous obscure brands, are frequently advertised as a means to stream subscription video content for free, a seductive offer that masks a significant security cost.

The alarming proliferation of Kimwolf is attributed to two primary security failings. Firstly, many of these unofficial Android TV boxes and digital picture frames come with malware pre-installed, or necessitate the download of unofficial Android App Stores and malware to function as advertised, often turning the device into a residential proxy node for resale. Secondly, and perhaps more critically, these devices rely on inexpensive, Internet-connected microcomputer boards that lack any inherent security or authentication mechanisms. This fundamental flaw means that any device on the same network can potentially compromise them with a single command, creating a critical entry point for malware.
The alarming synergy of these vulnerabilities was brought to light by Benjamin Brundage, a 22-year-old computer science student and founder of the security firm Synthient. Brundage’s research, conducted while studying for final exams, suggests Kimwolf is a new Android-based variant of the Aisuru botnet. He observed Kimwolf’s rapid growth by exploiting a glaring vulnerability in major residential proxy services. The critical weakness identified was the insufficient measures taken by these services to prevent customers from forwarding requests to internal servers of proxy endpoints. While most proxy services implement basic protections against "going upstream" into local networks by denying requests to RFC-1918 private IP address ranges (10.0.0.0/8, 192.168.0.0/16, and 172.16.0.0/12), the operators of Kimwolf discovered a method to circumvent these restrictions. By manipulating Domain Name System (DNS) settings to match these RFC-1918 ranges, attackers could directly communicate with devices on the internal networks of residential proxy endpoints. Brundage’s security advisory detailed how this allowed attackers to send carefully crafted requests to the current device or other devices on the local network, actively being exploited to drop malware.
This exploitation is exacerbated by the fact that many residential proxy services operate on mobile devices running apps with hidden components that turn the user’s phone into a proxy node, often without explicit consent. Synthient’s recent report highlights that Kimwolf operators monetize the botnet through app installs, the sale of residential proxy bandwidth, and the provision of DDoS functionality, anticipating increased interest from threat actors seeking unrestricted access to proxy networks for device infection, network access, or sensitive data acquisition.
Further investigation by Brundage into unofficial Android TV boxes revealed another critical vulnerability: the default enablement of Android Debug Bridge (ADB) mode straight from the factory. ADB is a diagnostic tool intended for manufacturing and testing, allowing remote configuration and firmware updates. However, its default activation creates a security nightmare, as these devices constantly listen for and accept unauthenticated connection requests. Brundage demonstrated that by simply issuing an "adb connect" command with a vulnerable device’s local IP address and port 5555, unrestricted "super user" administrative access could be gained almost instantaneously.
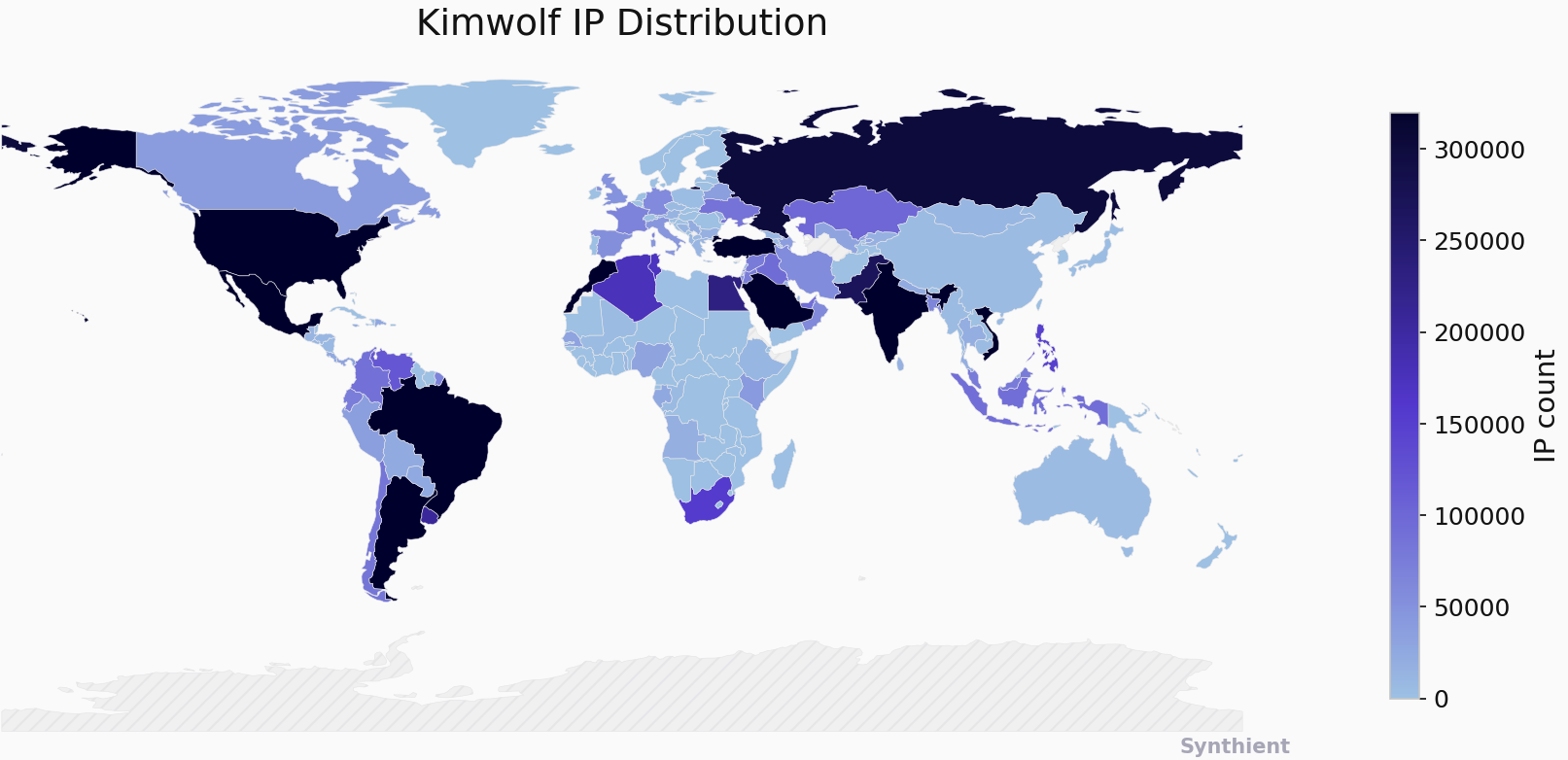
By early December, Brundage identified a direct correlation between new Kimwolf infections and proxy IP addresses offered for rent by IPIDEA, identified as the world’s largest residential proxy network. He observed Kimwolf doubling in size within a week by solely exploiting IPIDEA’s proxy pool. Synthient confirmed on December 1, 2025, that Kimwolf operators were tunneling through IPIDEA’s network and into the local networks of systems running its proxy software, dropping malware by directing infected systems to a specific internet address and using the passphrase "krebsfiveheadindustries" to unlock the malicious download. By December 30, Synthient was tracking approximately 2 million IPIDEA addresses exploited by Kimwolf in the preceding week, with the botnet demonstrating a remarkable ability to rebuild itself rapidly after takedown attempts, growing from near zero to two million infected systems within days by tunneling through IPIDEA endpoints. IPIDEA’s vast supply of new proxies, advertising access to over 100 million residential proxy endpoints globally, further fuels this threat. Synthient’s analysis of exposed devices within IPIDEA’s pool revealed that more than two-thirds were Android devices vulnerable to compromise without authentication.
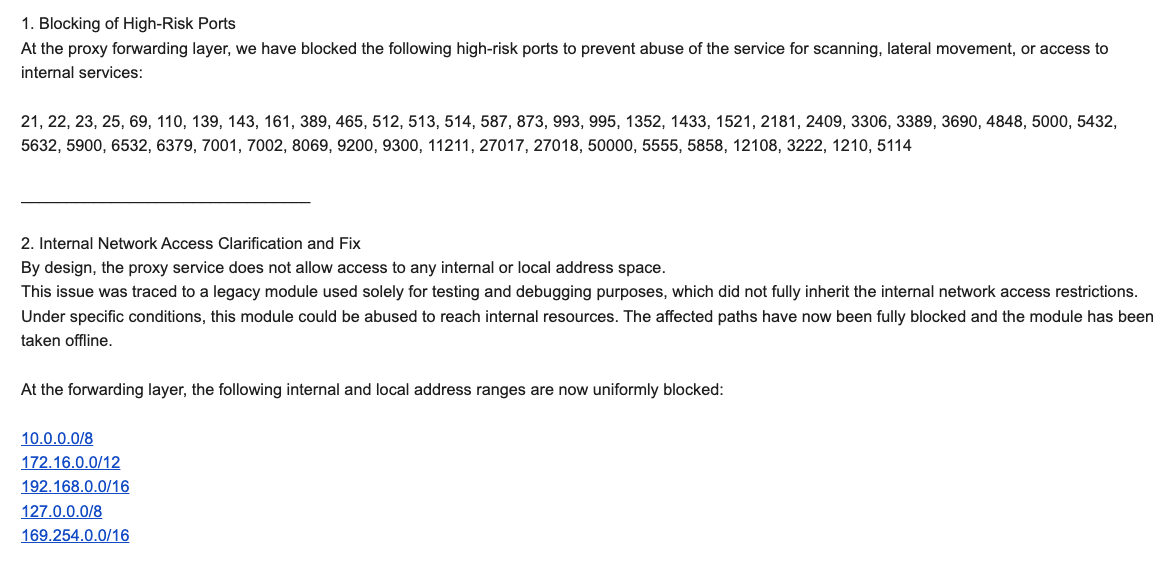
Brundage’s eagerness to publicize his findings was tempered by the desire to provide vulnerable proxy providers with an opportunity to patch the vulnerabilities. On December 17, he sent security notifications to 11 affected proxy providers, many of whom were resellers of IPIDEA. KrebsOnSecurity had previously sought comment from IPIDEA regarding its apparent benefit from the Aisuru botnet’s shift towards installing proxy programs. An IPIDEA employee, "Oliver," denied any association with the Aisuru botnet and asserted their rigorous supplier vetting process. However, on the same day Oliver’s email was received, Brundage shared a response from IPIDEA’s security officer, "Byron," who acknowledged the vulnerability. Byron explained that a legacy testing and debugging module, which did not fully inherit internal network access restrictions, was the cause. This module has since been blocked, taken offline, and IPIDEA has implemented multiple mitigations to block DNS resolution to internal IP ranges and to prevent forwarding traffic on high-risk ports. Brundage confirmed that IPIDEA appears to have patched the vulnerabilities, and he had not observed Kimwolf actors targeting other proxy services.
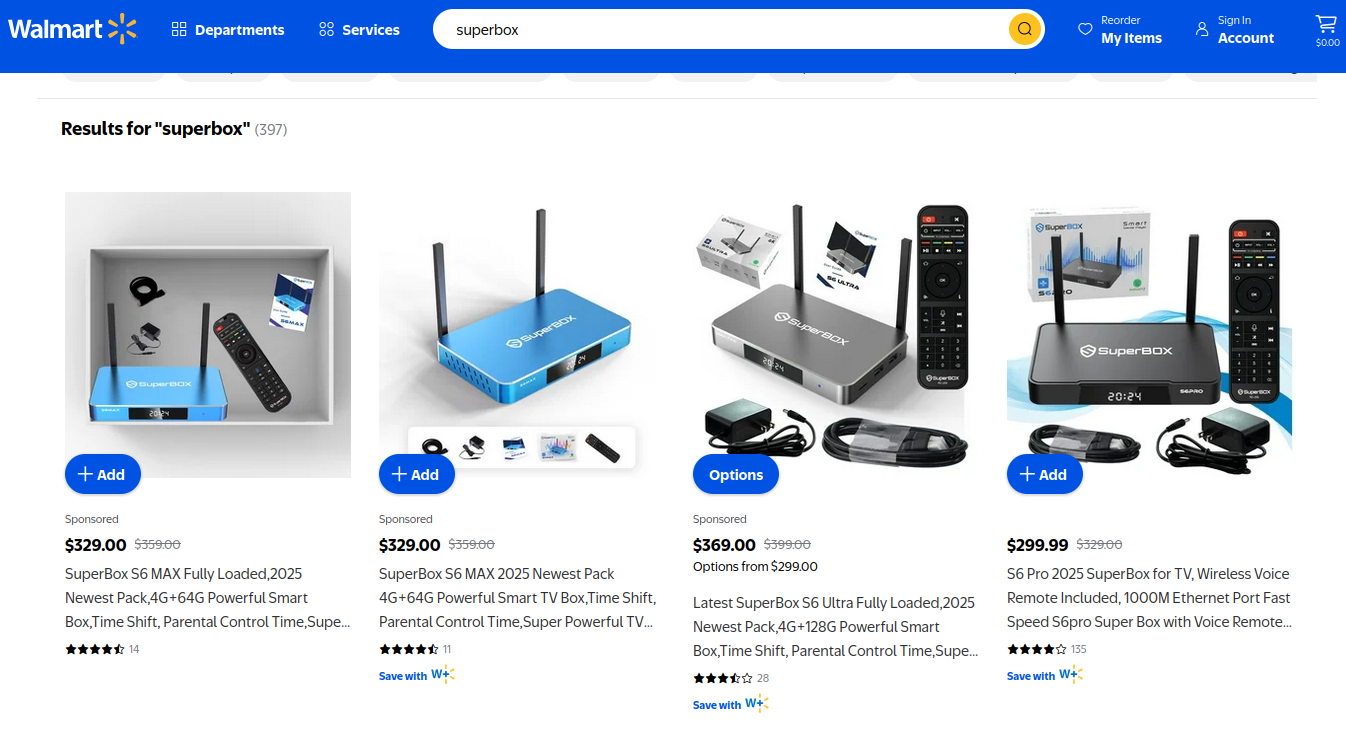
Riley Kilmer, founder of Spur.us, a firm specializing in identifying and filtering proxy traffic, corroborated Brundage’s findings, confirming that IPIDEA and its affiliates provided full, unfiltered access to the local LAN. Kilmer highlighted the Superbox, an unofficial Android TV box previously profiled, as particularly vulnerable, as it leaves Android Debug Mode running on localhost:5555. Since Superbox utilizes IPIDEA proxies, attackers can leverage this to install malicious SDKs. Both Brundage and Kilmer suggest IPIDEA is a reincarnation of the notorious 911S5 Proxy service, which operated from 2014 to 2022 and was popular on cybercrime forums before imploding after a data breach. The U.S. Treasury and Department of Justice later sanctioned and arrested the alleged creators of 911S5. Kilmer also pointed to IPIDEA’s sister service, 922 Proxy, as a direct alternative to 911S5. Oxylabs, another proxy provider notified by Synthient, confirmed implementing security changes to address the vulnerabilities, though they stated there was no evidence of Kimwolf exploiting their network.
The practical implications of the Kimwolf botnet are profound, demonstrating how easily a compromised device connected to your Wi-Fi can lead to an infection within your local network. A friend or family member visiting with an infected mobile phone, unknowingly turning their device into a residential proxy node, can expose your home’s public IP address to residential proxy providers. Attackers can then use this to tunnel back into your LAN, scanning for devices with ADB enabled. This could result in your digital photo frame and unofficial Android TV box becoming infected with Kimwolf, despite never intending for them to be exposed to the wider internet. Furthermore, attackers could leverage access to proxy networks to alter your router’s DNS settings, redirecting your web browser to malicious servers, echoing the widespread threat posed by the 2012 DNSChanger malware.
The Chinese security firm XLab has been instrumental in documenting Kimwolf’s rise, first chronicling the Aisuru botnet and subsequently tracking Kimwolf’s emergence. XLab reported that Kimwolf began actively tracking on October 24, with its control servers overwhelming Cloudflare’s DNS servers with lookups for specific domains. These domains topped Cloudflare’s chart of most sought-after domains for weeks, indicating the botnet’s extensive reach. XLab estimated Kimwolf had enslaved between 1.8 and 2 million devices, with significant concentrations in Brazil, India, the United States, and Argentina. They noted that the true scale of infection is difficult to measure due to dynamic IP allocation and devices not being online simultaneously. XLab also highlighted the Kimwolf author’s "obsessive fixation" on the author of this report, embedding "easter eggs" related to the author’s name within the botnet’s code and communications. XLab’s analysis confirmed that Kimwolf’s primary targets are TV boxes deployed in residential environments, and that early activities attributed to Aisuru may have been misattributed, with Kimwolf being the distinct Android variant.
Determining if devices on a home network are vulnerable or already infected with residential proxy malware is a significant challenge for average users. Isolating and removing such software requires technical expertise and tooling often beyond the consumer’s reach. Synthient offers a web page where visitors can check if their public IP address has been seen among Kimwolf-infected systems, and has compiled a list of unofficial Android TV boxes most represented in the botnet. Owners of these devices are strongly advised to remove them from their networks immediately, and to inform family and friends of the risks. Chad Seaman of Akamai Technologies urges consumers to be "paranoid of these crappy devices and of these residential proxy schemes," emphasizing that the notion of a secure LAN is outdated, as apps can compromise networks and grant access to countless random individuals. He also notes that the threat extends beyond Android devices, with proxy services offering SDKs for Mac, Windows, and iPhones.

The threat landscape is further complicated by the U.S. Department of Justice’s ongoing efforts against botnets like "BadBox 2.0 Enterprise," a botnet of over ten million unsanctioned Android streaming devices engaged in advertising fraud, as detailed in a Google lawsuit. The FBI has also issued advisories warning of cybercriminals gaining unauthorized access to home networks by pre-installing malware or infecting devices during setup. Lindsay Kaye of HUMAN Security, involved in BadBox investigations, stated that these botnets and proxy networks enabled extensive advertising fraud, ticket scalping, retail fraud, account takeovers, and content scraping. Kaye advises consumers to stick to name brands for connected devices and to be wary of free or low-cost offers, as well as the apps they install. Implementing a "Guest" Wi-Fi network on wireless routers is also recommended, as it allows guests internet access without granting them access to the local network. While some advocate for reflashing these devices with custom firmware, the majority of users purchasing these devices are not security experts and are unaware of the bargain they are making. The entertainment industry’s apparent lack of pressure on major e-commerce vendors to cease selling these insecure and actively malicious hardware devices, largely marketed for video piracy, contributes to this ongoing public nuisance. Future installments in this series will delve deeper into the individuals who appear to have built and profited most from Kimwolf.









