A sophisticated new phishing-as-a-service (PaaS) known as Starkiller is revolutionizing the cybercrime landscape by allowing malicious actors to bypass traditional detection methods and effectively neutralize multi-factor authentication (MFA) by proxying legitimate login pages and user interactions. Unlike conventional phishing kits that rely on static copies of login pages, Starkiller dynamically loads the target brand’s actual website, acting as a stealthy intermediary between the victim and the legitimate service. This innovative approach allows attackers to capture not only usernames and passwords but also time-sensitive MFA codes, all while presenting a seemingly authentic browsing experience to the victim. The implications of this advanced phishing technique are far-reaching, significantly lowering the barrier to entry for novice cybercriminals and posing a formidable challenge to current cybersecurity defenses.
The operational brilliance of Starkiller lies in its ability to abstract away the technical complexities typically associated with setting up and maintaining phishing infrastructure. Aspiring scammers no longer need to grapple with configuring servers, domain names, digital certificates, or proxy services. Starkiller streamlines this process, offering a user-friendly platform where customers can select a brand to impersonate – with options ranging from tech giants like Apple, Facebook, and Google to major enterprise providers like Microsoft. The service then generates a deceptive URL designed to mimic the legitimate domain while cleverly routing all traffic through the attacker’s controlled infrastructure. This URL masking technique is crucial to its success.
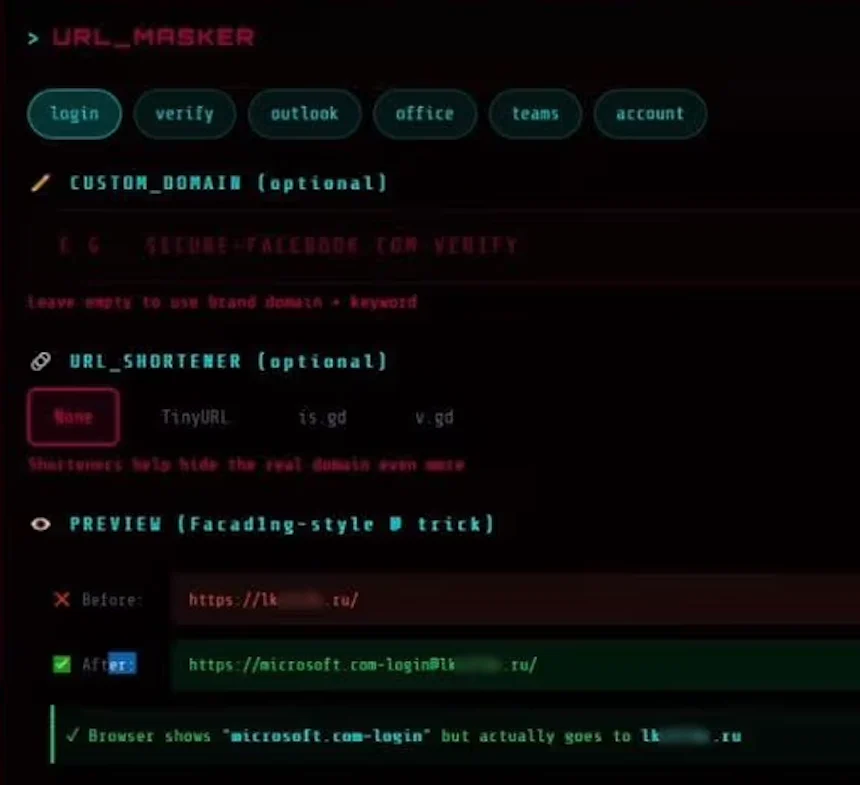
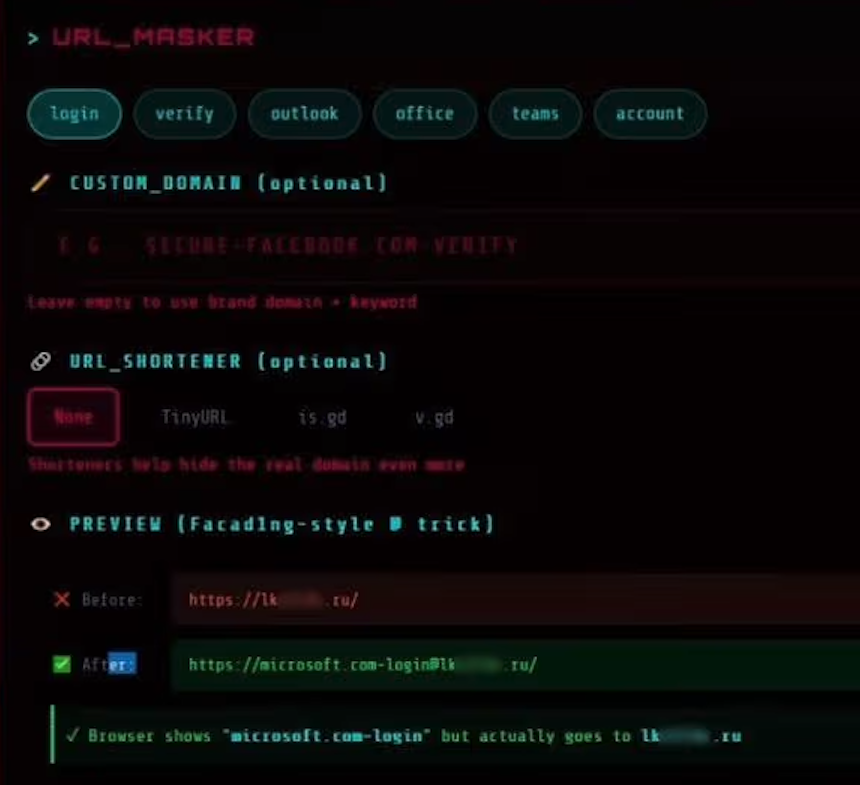
A prime example of Starkiller’s URL manipulation, as highlighted by the cybersecurity firm Abnormal AI, involves a deceptive link targeting Microsoft users. This link might appear as "login.microsoft.com@[malicious/shortened URL here]." The inclusion of the "@" symbol is an old but effective trick in URL parsing. In many web contexts, everything preceding the "@" symbol is interpreted as username data, while the actual landing page is determined by the content following it. This creates a visual illusion for the victim, making the link appear legitimate at first glance. The accompanying image from Abnormal AI illustrates this, showing a blurred malicious landing page that clearly ends in a .ru domain, indicating its foreign origin, and also showcasing the integration of various URL-shortening services to further obfuscate the true destination.
Once a target URL is selected by a Starkiller customer, the service automatically provisions a Docker container. Within this container, a headless Chrome browser instance is launched. This headless browser’s sole purpose is to load the authentic login page of the targeted service. Abnormal AI researchers Callie Baron and Piotr Wojtyla, in their detailed analysis, explain that this container then functions as a "man-in-the-middle reverse proxy." It acts as a conduit, meticulously forwarding every piece of data entered by the end-user – including keystrokes, form submissions, and session tokens – to the legitimate website. Crucially, it also captures and logs all of this information before relaying the legitimate site’s responses back to the victim. This intricate process ensures that the victim perceives their interaction as being directly with the real service, while their sensitive data is being intercepted and recorded by the attacker.
The capabilities offered by Starkiller extend far beyond simple credential harvesting. The service provides cybercriminals with real-time session monitoring, essentially enabling them to "live-stream" the victim’s screen as they navigate the phishing page. This allows attackers to observe the victim’s actions and tailor their attack in real-time. Furthermore, Starkiller incorporates a robust suite of features designed for comprehensive account takeover. These include:
- Keylogger Capture: Every keystroke entered by the victim is meticulously recorded.
- Cookie and Session Token Theft: Essential for direct account takeover, these stolen elements allow attackers to bypass further authentication steps.
- Geo-tracking of Targets: Understanding the victim’s location can be valuable for subsequent social engineering or to identify high-value targets.
- Automated Telegram Alerts: Attackers receive instant notifications via Telegram as soon as new credentials are captured, enabling swift exploitation.
- Campaign Analytics: Mirroring the dashboards of legitimate Software-as-a-Service (SaaS) platforms, Starkiller provides operators with crucial metrics like visit counts, conversion rates, and performance graphs, allowing them to optimize their phishing campaigns for maximum effectiveness.
Perhaps the most alarming aspect of Starkiller is its ability to circumvent multi-factor authentication (MFA). Because the victim is, in effect, authenticating with the real site through the attacker’s proxy, any MFA codes entered are also relayed in real-time to the legitimate service. The attacker then captures the resulting session cookies and tokens, granting them authenticated access to the account. As Baron and Wojtyla explain, "When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed." This means that even users diligently employing MFA are vulnerable to compromise through this advanced proxy-based phishing method.
The accompanying image titled "URL Masker" further illustrates Starkiller’s user interface, showcasing options for configuring the deceptive links. This highlights the service’s focus on providing a polished and customizable experience for its users.
Starkiller is not an isolated threat but rather a component of a broader cybercrime ecosystem operated by a threat group known as Jinkusu. This group maintains an active user forum where customers can exchange techniques, request new features, and seek assistance with their phishing operations. Jinkusu also offers ancillary services, such as an a-la-carte feature that harvests email addresses and contact information from compromised sessions, which can then be used to build target lists for future, more sophisticated phishing campaigns.
This Starkiller service represents a significant evolutionary leap in phishing tactics. Its apparent success is likely to inspire copycat operations from other cybercriminals, as it effectively eliminates the substantial upfront costs and ongoing management headaches associated with traditional phishing, such as constantly acquiring and rotating multiple phishing domains. Moreover, it poses a significant challenge to established phishing detection methods like domain blocklisting and static page analysis, which are rendered largely ineffective against dynamic, proxy-based attacks.
The researchers at Abnormal AI emphasize that Starkiller dramatically lowers the barrier to entry for novice cybercriminals. They conclude in their report that "Starkiller represents a significant escalation in phishing infrastructure, reflecting a broader trend toward commoditized, enterprise-style cybercrime tooling. Combined with URL masking, session hijacking, and MFA bypass, it gives low-skill cybercriminals access to attack capabilities that were previously out of reach." This commoditization of advanced cybercrime tools signals a worrying future where sophisticated attacks become more accessible, amplifying the global cybersecurity threat landscape.









