
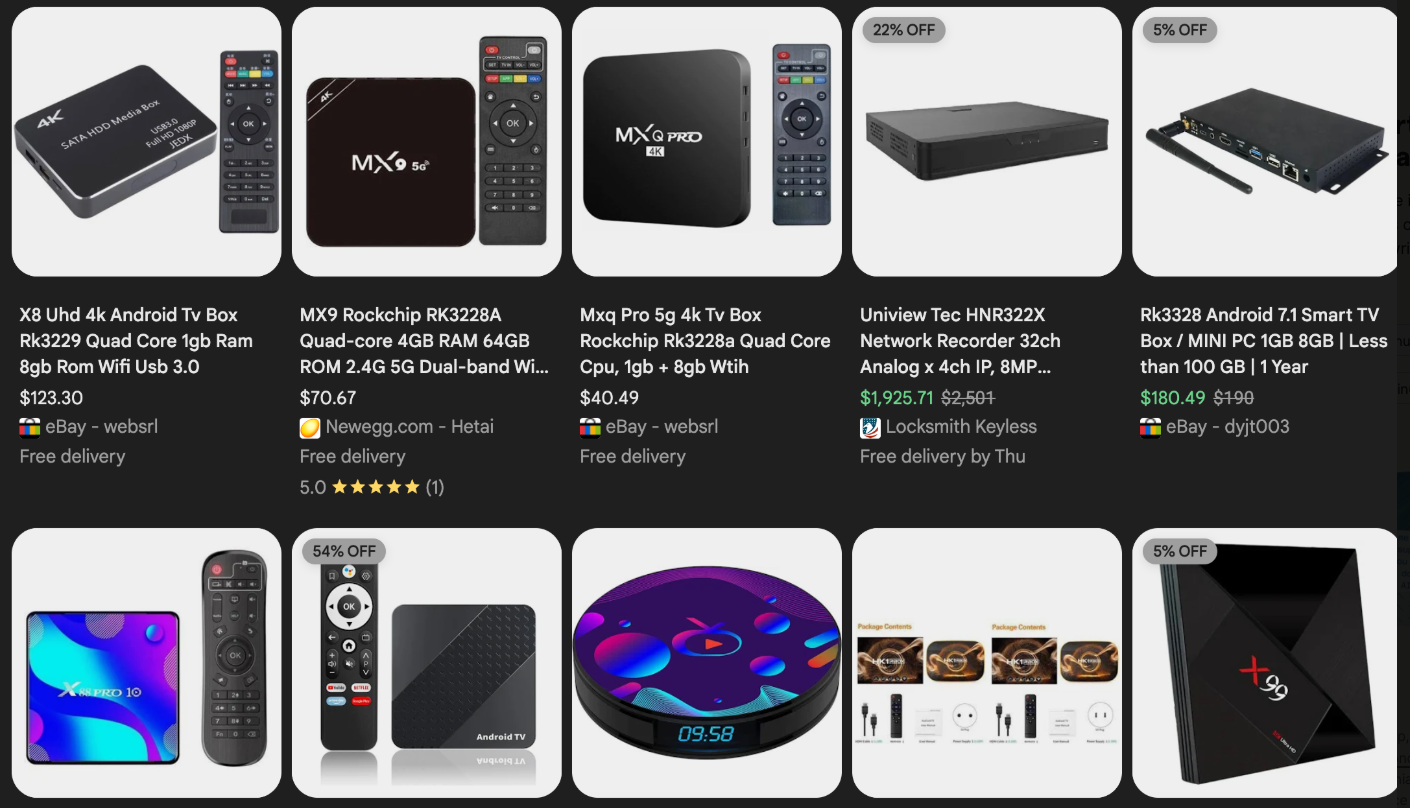
The primary vector for Kimwolf’s infection appears to be unofficial Android TV boxes and digital photo frames, frequently sold on major e-commerce platforms like Amazon, BestBuy, Newegg, and Walmart. These devices, often priced between $40 and $400 and marketed under numerous obscure brands, are frequently advertised as a means to stream subscription video content for free. However, the hidden cost is the pre-installed malware that transforms these devices into residential proxy nodes, effectively reselling users’ internet connections. A significant security flaw identified in these devices, and many residential proxy services, is the lack of robust security or authentication mechanisms. This allows attackers to exploit them with a single command if they are on the same local network.

Benjamin Brundage, founder of the security firm Synthient, has been instrumental in tracking Kimwolf’s proliferation. His research suggests Kimwolf is an Android-based variant of the Aisuru botnet. Brundage uncovered a critical vulnerability in numerous large residential proxy services, where insufficient safeguards allowed customers to forward requests to internal servers of proxy endpoints. While most services attempt to block access to private network address ranges (RFC-1918), Kimwolf operators exploited this by manipulating DNS settings to point to these internal ranges, granting them direct access to devices on local networks. This capability is actively being used to deploy malware.
Further compounding the threat, Brundage discovered that many of these unofficial Android TV boxes are shipped with Android Debug Bridge (ADB) mode enabled by default. ADB is a powerful diagnostic tool meant for manufacturing and testing, but when left active, it allows for unauthenticated remote configuration and firmware updates, creating a severe security risk. By simply connecting to a vulnerable device’s local IP address and port 5555, attackers can gain unrestricted administrative access. Brundage observed a direct correlation between new Kimwolf infections and proxy IP addresses offered for rent by IPIDEA, identified as the world’s largest residential proxy network. Synthient’s analysis indicated that over two-thirds of IPIDEA’s exploited proxy endpoints were Android devices requiring no authentication for compromise.
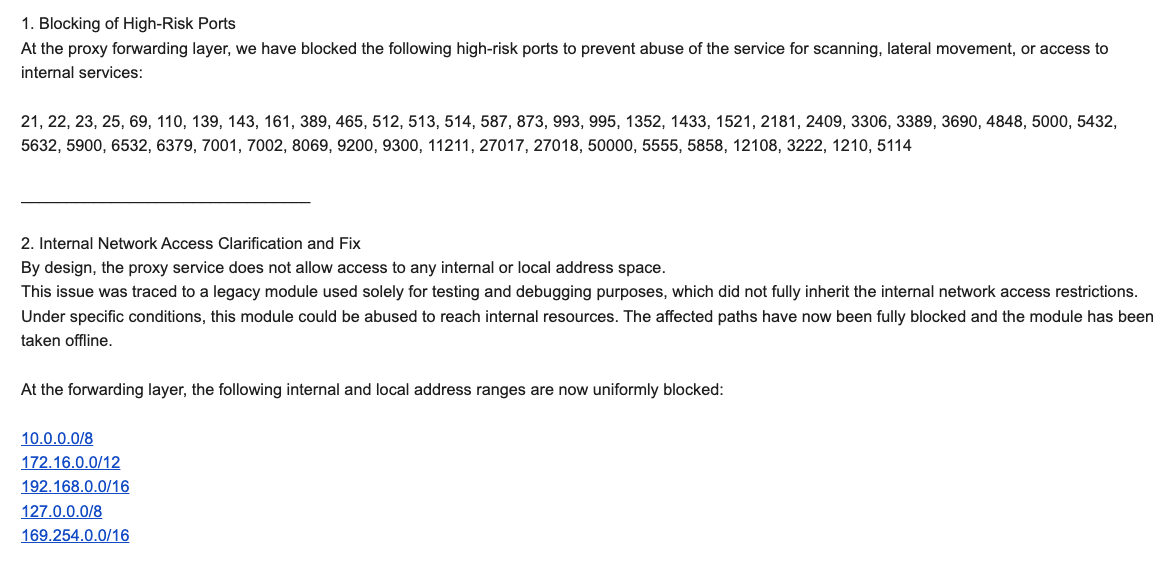
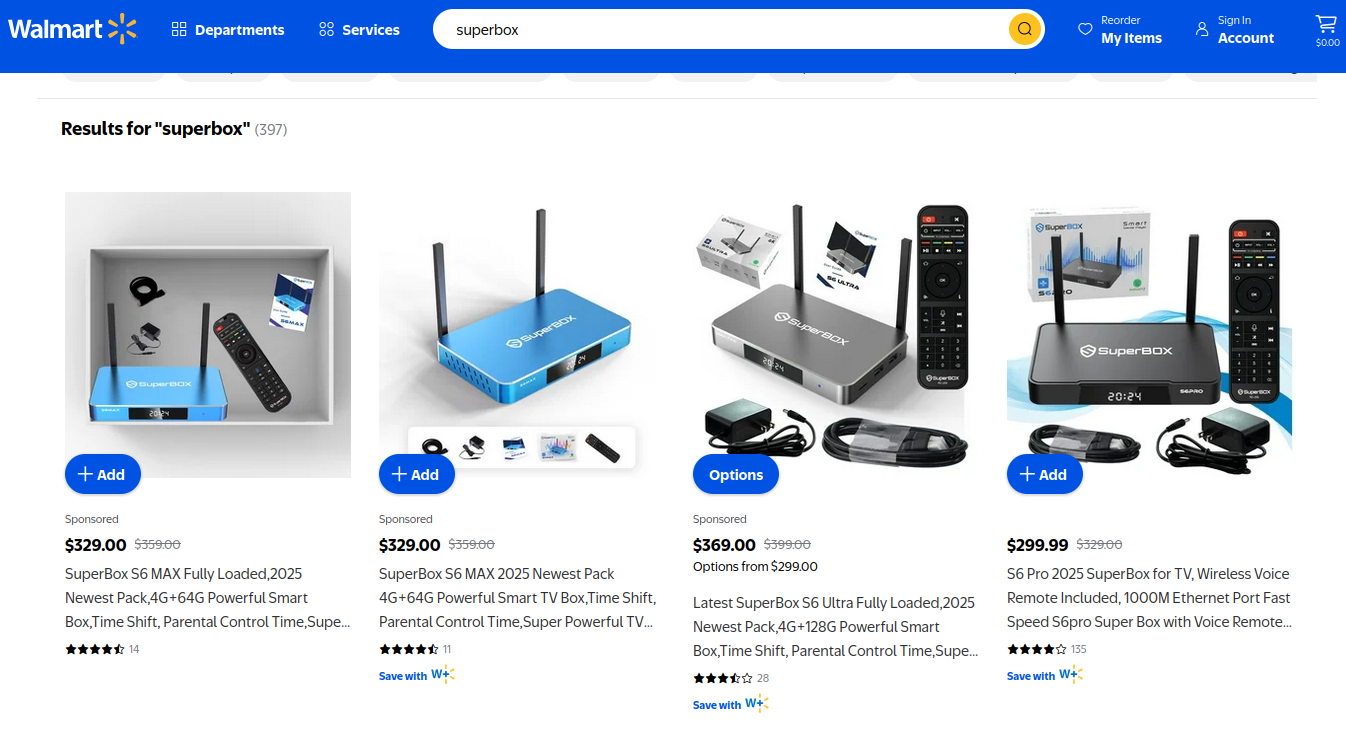
Synthient proactively notified 11 affected proxy providers about these vulnerabilities in mid-December 2025, aiming to allow them time to implement fixes before public disclosure. While many were resellers of IPIDEA, IPIDEA itself eventually acknowledged the issue. An IPIDEA security officer, "Byron," confirmed a legacy testing module had been exploited, allowing access to internal resources. IPIDEA claims to have since blocked these paths, taken the module offline, and implemented further mitigations against DNS resolution to internal IP ranges and traffic on high-risk ports. Riley Kilmer, founder of Spur.us, a firm specializing in proxy traffic identification, independently verified IPIDEA and its affiliates’ allowance of unfiltered LAN access. Kilmer specifically noted the Superbox, a popular unofficial Android TV box, leaves ADB running on localhost:5555, making it an easy target when integrated with IPIDEA proxies.
The origins of IPIDEA are closely linked to the notorious 911S5 Proxy service, which operated from 2014 to 2022 and was popular in cybercrime forums before imploding after a data breach. The U.S. Treasury later sanctioned 911S5’s alleged creators. Kilmer also pointed to IPIDEA’s sister service, 922 Proxy, as a direct successor to 911S5. While IPIDEA claims no association with the Aisuru botnet, Brundage’s data strongly suggests its proxy service was massively abused by Kimwolf, Aisuru’s Android variant.
The practical implications of the Kimwolf botnet are profound. A scenario where a guest uses your Wi-Fi, their infected phone turns your public IP into a rental proxy, and subsequently, attackers tunnel back into your local network to infect devices like digital photo frames and Android TV boxes, is alarmingly plausible. Furthermore, attackers could potentially hijack your router’s DNS settings, redirecting all your web traffic through malicious servers, reminiscent of the 2012 DNSChanger malware.
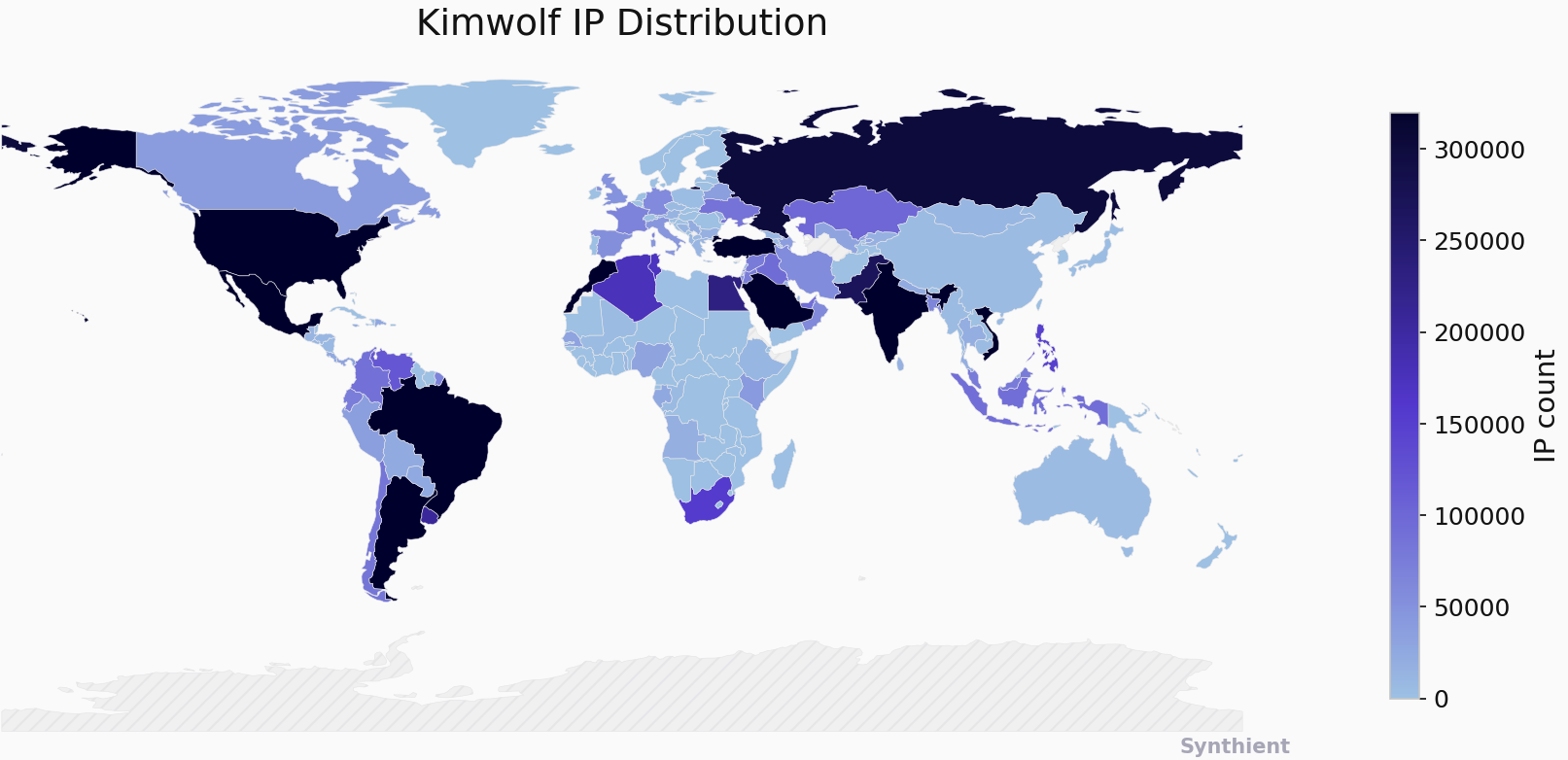
Chinese security firm XLab was among the first to chronicle the Aisuru botnet and later tracked Kimwolf’s emergence. They estimated Kimwolf had enslaved between 1.8 and 2 million devices, with significant concentrations in Brazil, India, the United States, and Russia. XLab’s research indicated that Kimwolf’s primary targets are TV boxes in residential environments, and the true scale of infection is difficult to precisely measure due to dynamic IP allocation and devices not being online simultaneously. XLab also noted the botnet author’s peculiar fixation on the author of this report, embedding "easter eggs" related to his name within the botnet’s code.
Identifying and removing Kimwolf infections is challenging for average users due to a lack of accessible tools and expertise for network traffic analysis. However, Synthient offers a website where users can check if their public IP address has been associated with Kimwolf infections. They have also compiled a list of unofficial Android TV boxes heavily represented in the botnet, urging users to remove such devices from their networks. Chad Seaman of Akamai Technologies emphasized the need for consumers to be highly skeptical of unofficial devices and residential proxy schemes, stating that the notion of a secure local network is outdated. He also highlighted that the threat extends beyond Android devices, with SDKs available for Mac, Windows, and iPhones.
This threat landscape is further underscored by Google’s lawsuit against "BadBox 2.0 Enterprise," a botnet of over ten million unsanctioned Android streaming devices involved in advertising fraud, and a prior FBI advisory warning of cybercriminals gaining unauthorized access to home networks through pre-configured malware or malicious app downloads during device setup. Lindsay Kaye of HUMAN Security, who worked on the BADBOX investigations, stressed the importance of sticking to reputable brands and being cautious about free or low-cost offers and app downloads. She also recommended utilizing guest Wi-Fi networks to isolate guest devices from the local network.
While a small segment of users advocates for flashing custom firmware onto infected devices, the majority of consumers purchasing these boxes are unaware of the inherent risks, attracted by the promise of "free" content. The entertainment industry’s limited visible pressure on e-commerce vendors to cease selling these insecure, actively malicious hardware devices, primarily marketed for video piracy, is a significant concern. These TV boxes serve as a public nuisance due to their bundled malware and lack of security, making them prime targets for cybercriminals. This report serves as a critical alert, highlighting the urgent need for increased consumer awareness and proactive security measures to combat the pervasive threat of botnets like Kimwolf.









