The breach underscores the persistent and evolving threat of social engineering, a non-technical method of intrusion that preys on human psychology rather than software vulnerabilities. In this instance, attackers successfully manipulated an employee, likely through phishing, pretexting, or another form of psychological deception, to gain access to internal systems. This method bypasses even the most robust technical defenses if an employee is tricked into providing credentials or executing malicious actions. A company spokesperson confirmed to TechCrunch that the incident allowed hackers to obtain "a limited number of files," though the precise scope and number of affected users remain undisclosed publicly. Figure Technology has initiated the process of notifying affected parties, demonstrating its commitment to transparency and customer protection, and is offering free credit-monitoring services to anyone who receives a breach notification, a standard practice for companies dealing with such incidents.
Despite these immediate measures, the lack of specific details regarding the incident’s scope, including the exact number of affected users or the precise timeline of the intrusion and its detection, raises concerns among customers and industry observers. Cointelegraph reached out to Figure Technology for further comment but had not received a response by the time of publication, leaving many questions unanswered about the full impact of the breach. This opacity, while sometimes driven by ongoing investigations, can erode customer trust, particularly for a company operating in the sensitive financial and blockchain sectors where data integrity and security are paramount.
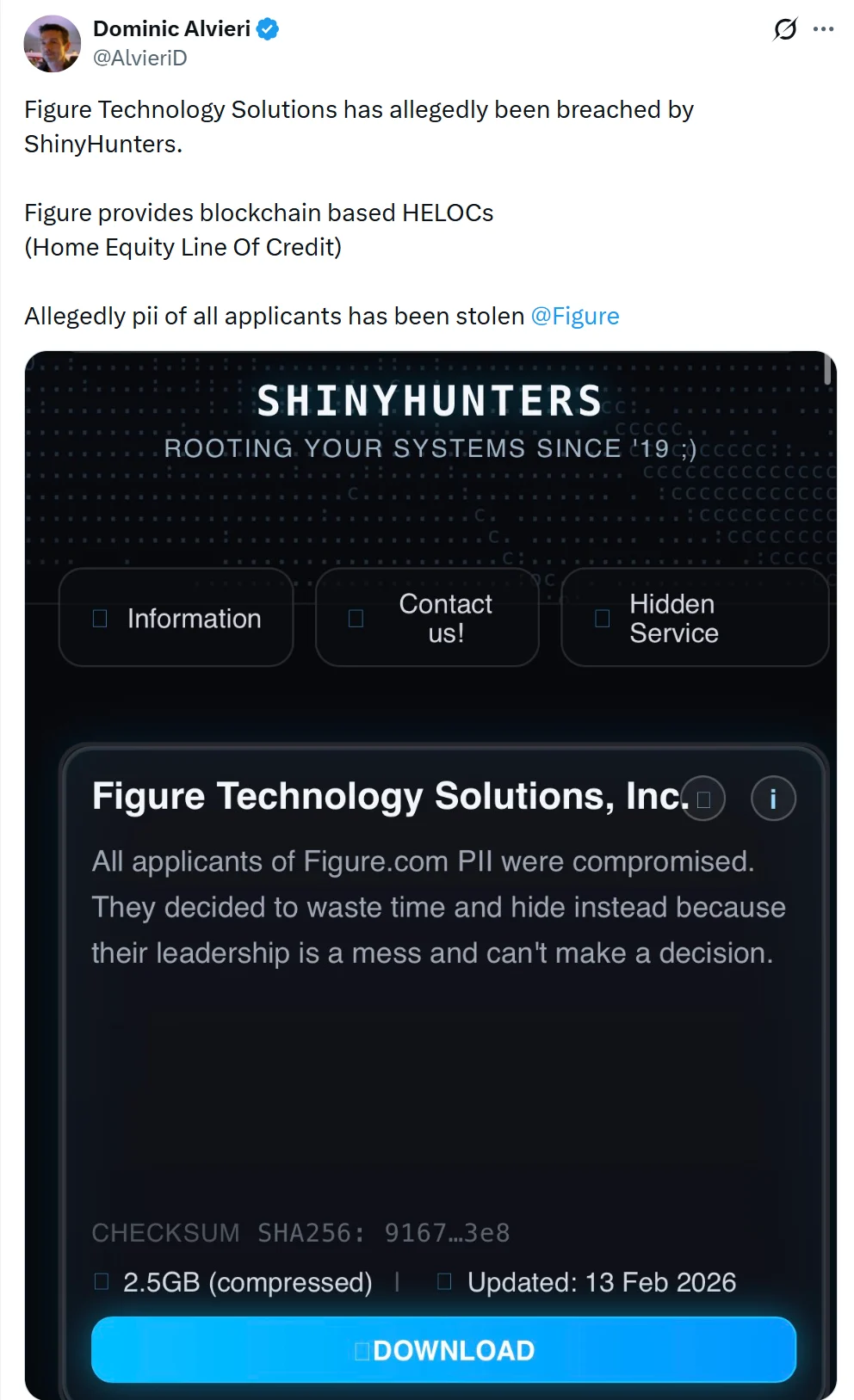
The responsibility for the breach was swiftly claimed by ShinyHunters, a notorious hacking collective known for its high-profile data theft and extortion attempts. The group announced its involvement on its dark-web leak site, explicitly stating that Figure Technology had declined to pay a ransom demand. In retaliation for the company’s refusal, ShinyHunters proceeded to publish approximately 2.5 gigabytes of data, which they alleged was exfiltrated directly from Figure’s systems. This modus operandi is characteristic of ShinyHunters, who have a history of targeting companies across various industries, stealing vast amounts of data, and then attempting to extort payments, releasing the data publicly if their demands are not met. Their previous victims include numerous well-known companies, solidifying their reputation as a significant threat actor in the cybercrime landscape. The sheer volume of data, 2.5 gigabytes, suggests a considerable collection of files, potentially including not just customer records but also internal documents, operational data, or other proprietary information that could be leveraged for further attacks or competitive intelligence.
TechCrunch, acting as an independent verifier, reviewed samples of the leaked material. Their analysis confirmed the severity of the breach, revealing that the stolen data included highly sensitive customer personal information. Specifically, the leaked files contained customers’ full names, home addresses, dates of birth, and phone numbers. This combination of data points is particularly dangerous as it forms a critical foundation for various types of identity fraud and highly targeted phishing attempts. With such comprehensive personal details, malicious actors can open new credit lines, apply for loans, access existing accounts, or engage in sophisticated spear-phishing campaigns that appear highly legitimate, tricking individuals into revealing even more sensitive information or granting access to financial accounts. The availability of this data on the dark web means that it can be bought and sold, potentially exposing affected individuals to long-term risks from various cybercriminals.
The incident at Figure Technology comes amidst a fluctuating landscape of cybersecurity threats within the crypto and Web3 space. As Cointelegraph previously reported, crypto phishing attacks linked to wallet drainers saw a notable drop in 2025, with total losses falling to $83.85 million. This represented an 83% decline from nearly $494 million in 2024, according to Web3 security firm Scam Sniffer. The number of victims also decreased significantly to about 106,000, down 68% year over year across Ethereum Virtual Machine (EVM) chains. Wallet drainers are malicious scripts or smart contracts designed to automatically transfer all assets from a user’s cryptocurrency wallet once they grant approval, often disguised as legitimate dApps or token approvals. While these statistics might suggest an improvement in security or user awareness, researchers caution against complacency. The drop in losses does not signify the disappearance of phishing threats but rather reflects a dynamic environment where losses often track market activity. During periods of heavy on-chain trading, such as Ethereum’s strongest rally in the third quarter of 2025, losses surged to $31 million, with monthly totals fluctuating widely from $2.04 million in December to $12.17 million in August. This indicates that while some forms of attacks might wane, others adapt and persist, and overall vigilance remains crucial. The Figure Technology breach, being a traditional data exfiltration rather than a direct on-chain exploit, highlights that even firms building on blockchain technology are still susceptible to conventional cybersecurity vulnerabilities that target their off-chain operations and human elements.
Moreover, the broader crypto security landscape is constantly evolving, with threats like supply chain attacks reshaping the threat environment. While the overall count of crypto hacks might fluctuate, the sophistication and impact of certain attack vectors, such as those targeting third-party software or services used by crypto projects, continue to pose significant challenges. These supply chain attacks can have a cascading effect, compromising multiple entities downstream from a single initial point of compromise. The Figure Technology breach, stemming from social engineering, reinforces that the "human element" remains one of the most vulnerable links in any security chain, often exploited to initiate more complex attacks.

Figure Technology’s journey as a blockchain innovator makes this breach particularly noteworthy. The company went public in September of the previous year, listing on the Nasdaq Stock Exchange, a significant milestone for a fintech firm leveraging blockchain. Its initial public offering (IPO) was priced at $25 per share, successfully raising $787.5 million and achieving an initial valuation estimated between $5.3 billion and $7.6 billion. This public listing brought increased scrutiny and regulatory obligations, requiring robust internal controls and cybersecurity measures to protect investor and customer data. The breach, therefore, not only impacts customer privacy but also potentially the company’s stock performance and investor confidence.
Just a month before the breach confirmation, Figure Technology further cemented its innovative standing by launching the On-Chain Public Equity Network (OPEN). This groundbreaking platform, built on Figure’s proprietary Provenance blockchain, allows companies to issue real shares directly on the blockchain. More impressively, it enables investors to lend or pledge those shares to one another without the need for traditional intermediaries such as brokers, custodians, or exchanges. OPEN represents a significant step towards democratizing and disintermediating capital markets, promising greater efficiency, transparency, and accessibility. However, a data breach, even if not directly affecting the Provenance blockchain itself, can cast a shadow of doubt over the overall security posture and trustworthiness of a company pushing such revolutionary financial technology. The perceived risk associated with the company’s security practices could inadvertently affect the adoption and trust in its blockchain-based innovations.
The implications of this breach extend beyond Figure Technology and its immediate customers, serving as a stark reminder for the entire fintech and blockchain industries. For companies, it underscores the critical importance of comprehensive cybersecurity strategies that go beyond technical defenses to include rigorous employee training programs aimed at combating social engineering tactics. Implementing multi-factor authentication, enforcing strong password policies, conducting regular security audits, and developing robust incident response plans are no longer optional but essential safeguards. Furthermore, fostering a security-aware culture where employees are empowered to identify and report suspicious activities is paramount.
For individuals who may be affected by the breach, proactive steps are crucial. These include closely monitoring credit reports and financial statements for any suspicious activity, placing a credit freeze or fraud alert with credit bureaus, changing passwords for online accounts, and being extremely vigilant against any unsolicited communications (emails, calls, texts) that appear to be from Figure Technology or other financial institutions. Such communications could be highly personalized using the leaked data, making them more convincing and dangerous. Victims should also be aware of the potential for vishing (voice phishing) or smishing (SMS phishing) attempts.
In conclusion, the data breach at Figure Technology, orchestrated by the notorious ShinyHunters through a social engineering attack, highlights the enduring vulnerability of even advanced financial technology firms to human-centric exploits. While the company’s swift response in notifying affected parties and offering credit monitoring is a necessary step, the broader implications for customer trust, the company’s reputation as a public entity and innovator, and the overall cybersecurity landscape in fintech and crypto are significant. It serves as a potent reminder that as financial technology advances and leverages sophisticated blockchain solutions, the fundamental security of personal data remains a critical and ongoing challenge, demanding continuous vigilance from both companies and individuals alike.
Cointelegraph is committed to independent, transparent journalism. This news article is produced in accordance with Cointelegraph’s Editorial Policy and aims to provide accurate and timely information. Readers are encouraged to verify information independently. Read our Editorial Policy https://cointelegraph.com/editorial-policy







