For the past week, the massive "Internet of Things" (IoT) botnet known as Kimwolf has been significantly disrupting The Invisible Internet Project (I2P), a decentralized, encrypted communications network meticulously designed to anonymize and secure online communications, leading to widespread outages and raising serious concerns about the vulnerability of privacy-focused infrastructure. I2P users began reporting severe disruptions in the network’s functionality around the same time the botmasters behind Kimwolf reportedly began leveraging it to evade persistent takedown attempts against the botnet’s control servers. This symbiotic exploitation, where a malicious actor weaponizes a privacy tool for its own survival, highlights a growing and concerning trend in the cyber threat landscape.
Kimwolf, a botnet that first surfaced in late 2025, rapidly escalated to infect millions of poorly secured IoT devices. These compromised devices, ranging from ubiquitous TV streaming boxes and digital picture frames to essential home routers, have been repurposed as relays for malicious traffic and have been instrumental in launching abnormally large distributed denial-of-service (DDoS) attacks. The botnet’s sheer scale and the insidious nature of its propagation through the interconnectedness of IoT devices make it a formidable adversary. Its ability to leverage such a vast and often overlooked attack surface underscores the inherent security challenges posed by the burgeoning IoT ecosystem.
I2P, on the other hand, stands as a beacon of privacy and decentralization in the often-surveilled digital world. It is a privacy-focused network that empowers individuals to communicate and share information anonymously, shielding their identities and locations from prying eyes. The I2P network operates by meticulously routing data through multiple layers of encryption across a distributed network of volunteer-operated nodes. This intricate process effectively hides both the sender’s and the receiver’s geographical locations, creating a secure, censorship-resistant environment ideally suited for private websites, secure messaging, and confidential data sharing. The I2P website eloquently describes this architecture as a "secure, censorship-resistant network designed for private websites, messaging, and data sharing."
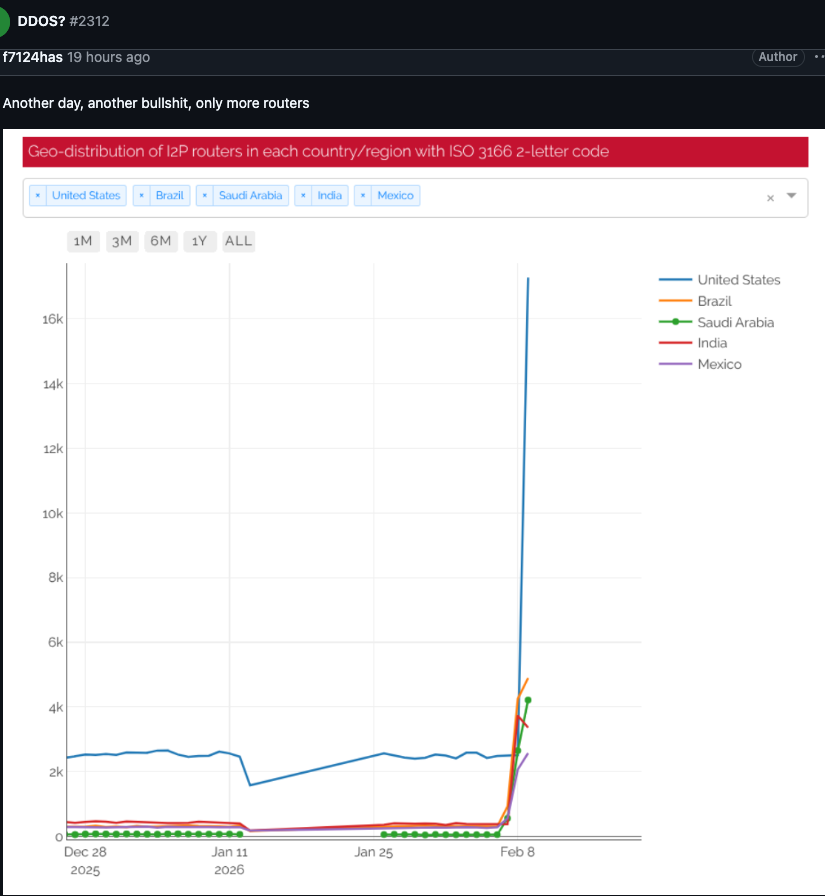
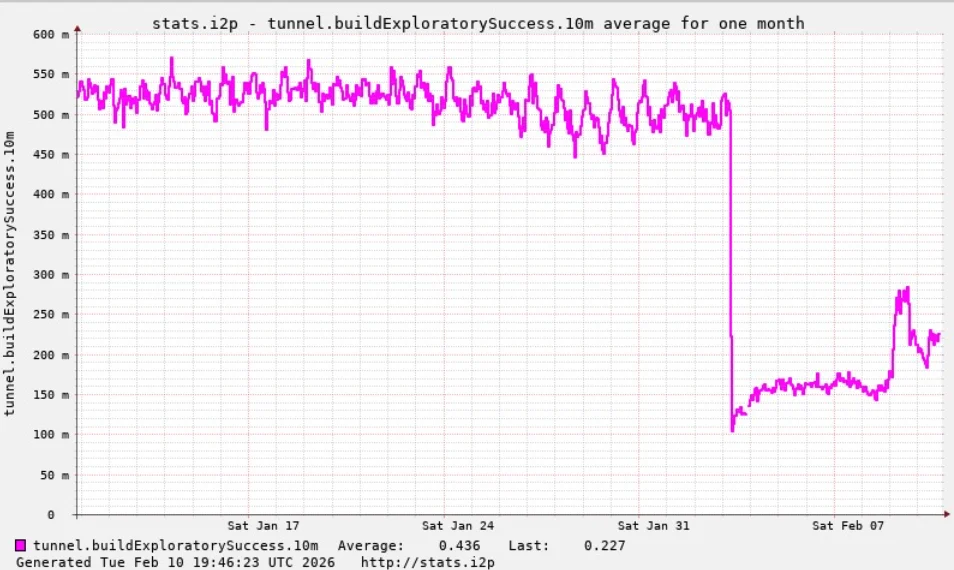
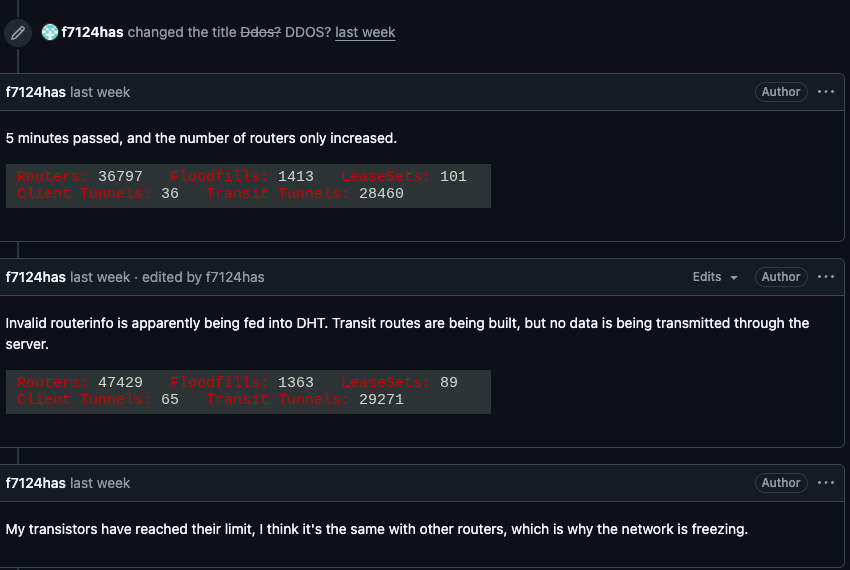
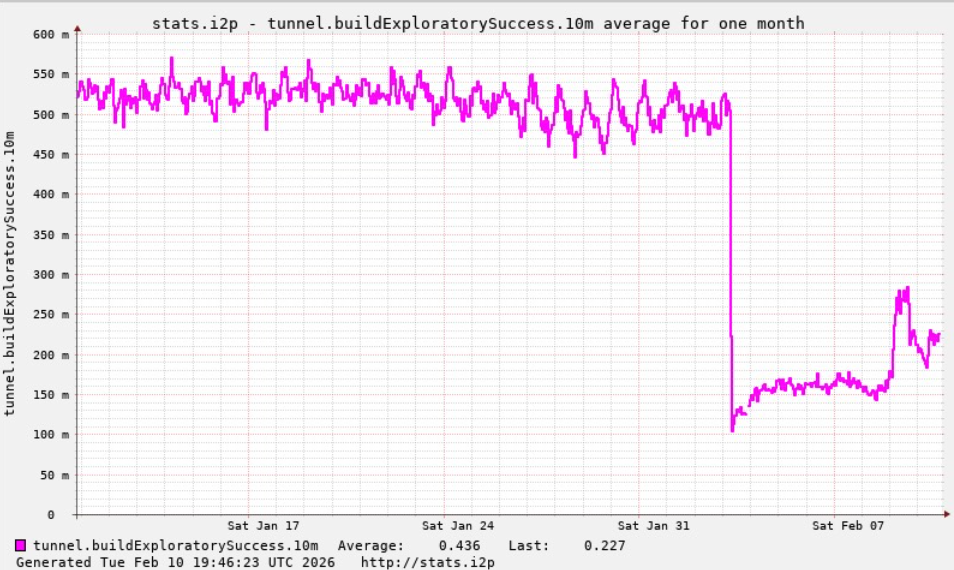
The catastrophic disruption began on February 3rd, when I2P users started voicing their distress on the organization’s GitHub page. They reported an overwhelming influx of tens of thousands of new routers suddenly flooding the network, effectively paralyzing legitimate communication channels and preventing existing users from connecting with trusted nodes. Users described a rapidly escalating number of new systems joining the network, all of which were incapable of transmitting data. This unprecedented mass ingress of compromised devices, orchestrated by the Kimwolf botnet, overwhelmed the network’s capacity to the point where even established users found themselves unable to establish connections. One user, articulating the severity of the situation, questioned if the network was under attack, to which another user responded with a chilling confirmation: "Looks like it. My physical router freezes when the number of connections exceeds 60,000."
Compounding the concern, the same day that I2P users began experiencing these crippling outages, the individuals reportedly in control of the Kimwolf botnet made a telling post to their private Discord channel. They openly admitted to having inadvertently disrupted I2P, explaining that their intention was to onboard approximately 700,000 Kimwolf-infected bots as nodes onto the I2P network. This admission directly links the botnet’s operational activities to the network’s severe degradation.
While Kimwolf is primarily recognized as a potent weapon for launching sophisticated DDoS attacks, the outages experienced by I2P this past week are a stark example of a "Sybil attack." This specific type of threat is particularly pernicious in peer-to-peer networks, where a single entity can severely disrupt the system by creating, controlling, and operating a vast number of pseudonymous identities. In essence, the Kimwolf botmaster(s) attempted to submerge the I2P network in a sea of fake, bot-controlled identities, overwhelming its capacity and rendering it inoperable for its intended purpose. The sheer volume of Kimwolf-infected routers attempting to join I2P was many times the network’s normal operational size. For context, I2P’s Wikipedia page indicates that the network typically consists of around 55,000 computers distributed globally, with each participant contributing by acting as both a router and a client.
However, Lance James, founder of the New York City-based cybersecurity consultancy Unit 221B and notably, the original founder of I2P, provided a more precise estimate. He informed KrebsOnSecurity that the actual number of active I2P devices on any given day hovers between 15,000 and 20,000. This makes the influx of hundreds of thousands of Kimwolf bots even more devastating, representing an astronomical increase in the network’s participant count.
Benjamin Brundage, founder of Synthient, a startup specializing in tracking proxy services, and the first to meticulously document Kimwolf’s unique spreading techniques, shed further light on the botnet’s motivations. Brundage explained that the Kimwolf operator(s) have been actively attempting to construct a command and control (C2) network that is highly resilient to takedown efforts by coordinated security companies and network operators. He revealed that the individuals in control of Kimwolf have been experimenting with utilizing I2P, and a similar anonymity network, Tor, as backup C2 infrastructure. While there have been no recent reports of widespread disruptions within the Tor network, this experimental phase with I2P has proven disastrous for its users.
Brundage posited that the primary objective of the Kimwolf operators is not necessarily to dismantle I2P itself, but rather to secure a stable and untraceable alternative for maintaining their botnet’s command and control infrastructure in the face of persistent takedown attempts. This strategic pivot highlights a growing trend of threat actors seeking to exploit privacy-enhancing technologies as a means of perpetuating their malicious operations.
The Kimwolf botnet had previously caused significant challenges for Cloudflare late last year. At that time, it began instructing millions of its infected devices to utilize Cloudflare’s domain name system (DNS) settings. This tactic led to control domains associated with Kimwolf repeatedly usurping the rankings of major entities like Amazon, Apple, Google, and Microsoft in Cloudflare’s public reports of the most frequently requested websites, demonstrating the botnet’s disruptive potential even without directly attacking these giants.
Despite the current turmoil, Lance James expressed cautious optimism, stating that the I2P network is still operating at approximately half of its normal capacity. He also indicated that a new release is being rolled out, which is expected to introduce stability improvements for users over the coming week.
Meanwhile, Brundage offered a ray of good news regarding the Kimwolf botnet’s operational capacity. He observed that Kimwolf’s overlords appear to have recently alienated some of their more competent developers and operators. This internal discord, he believes, led to a rookie mistake this past week, resulting in a significant drop of over 600,000 infected systems from the botnet’s overall numbers. "It seems like they’re just testing stuff, like running experiments in production," Brundage remarked, adding, "But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing." This internal strife and apparent lack of cohesive strategy within the Kimwolf operation might offer a temporary reprieve, but the underlying threat posed by sophisticated IoT botnets, and their potential to weaponize privacy infrastructure, remains a critical concern for the future of online security and anonymity.









