The shadowy figures behind the Kimwolf botnet, responsible for compromising over two million devices, have inadvertently provided a crucial clue in the ongoing investigation into the vast, China-based Badbox 2.0 botnet. A leaked screenshot, allegedly captured by Kimwolf operators, reveals an intimate look into the Badbox 2.0 control panel, offering compelling evidence that the Kimwolf masterminds, known by the aliases "Dort" and "Snow," have gained unauthorized access and potentially even control over a significant portion of Badbox 2.0’s infrastructure. This development is of particular interest to the FBI and Google, both of whom are actively pursuing the perpetrators of Badbox 2.0, and the revelations stemming from the Kimwolf crew’s boastful leak could significantly accelerate their efforts.
Our earlier reporting in 2026, specifically "The Kimwolf Botnet is Stalking Your Local Network," detailed the insidious methods employed by Kimwolf to propagate. The article highlighted that the overwhelming majority of Kimwolf-infected devices were unofficial Android TV boxes, often marketed as a one-time purchase solution for unlimited, albeit pirated, streaming content. The invasive nature of Kimwolf’s spread was a key warning, as it demonstrated an ability to exploit local networks and infect vulnerable devices without direct user interaction.
Further deepening the understanding of Kimwolf’s administration, our January 8th piece, "Who Benefitted from the Aisuru and Kimwolf Botnets?," cited multiple sources identifying "Dort" and "Snow" as the current leaders of the Kimwolf operation. The recent leak, shared by a former associate of Dort and Snow, provided a screenshot from the Badbox 2.0 control panel, purportedly taken by the Kimwolf operators themselves. This image, a critical piece of evidence, displays seven authorized users and their associated email addresses. Notably, one entry, "ABCD," logged in and positioned in the top right of the screenshot, is identified by the source as Dort’s account, indicating a successful intrusion and the addition of his email address to the Badbox 2.0 system.
The history of Badbox 2.0 predates Kimwolf’s emergence in October 2025. In July 2025, Google initiated a "John Doe" lawsuit against 25 unidentified individuals, accusing them of operating Badbox 2.0. Google described it as a colossal botnet comprising over ten million unsanctioned Android streaming devices, primarily engaged in advertising fraud. The investigation revealed that Badbox 2.0 not only compromised devices before their purchase but also utilized malicious apps downloaded from unofficial marketplaces to infect devices.
This legal action by Google followed a June 2025 advisory from the Federal Bureau of Investigation (FBI). The FBI’s warning detailed how cybercriminals were infiltrating home networks by pre-installing malware on devices or by embedding backdoors in required applications during the setup process, often through unofficial app stores. The FBI’s discovery of Badbox 2.0 stemmed from the disruption of the original Badbox campaign in 2024, which itself was identified in 2023 and primarily targeted Android TV boxes with pre-installed backdoor malware.
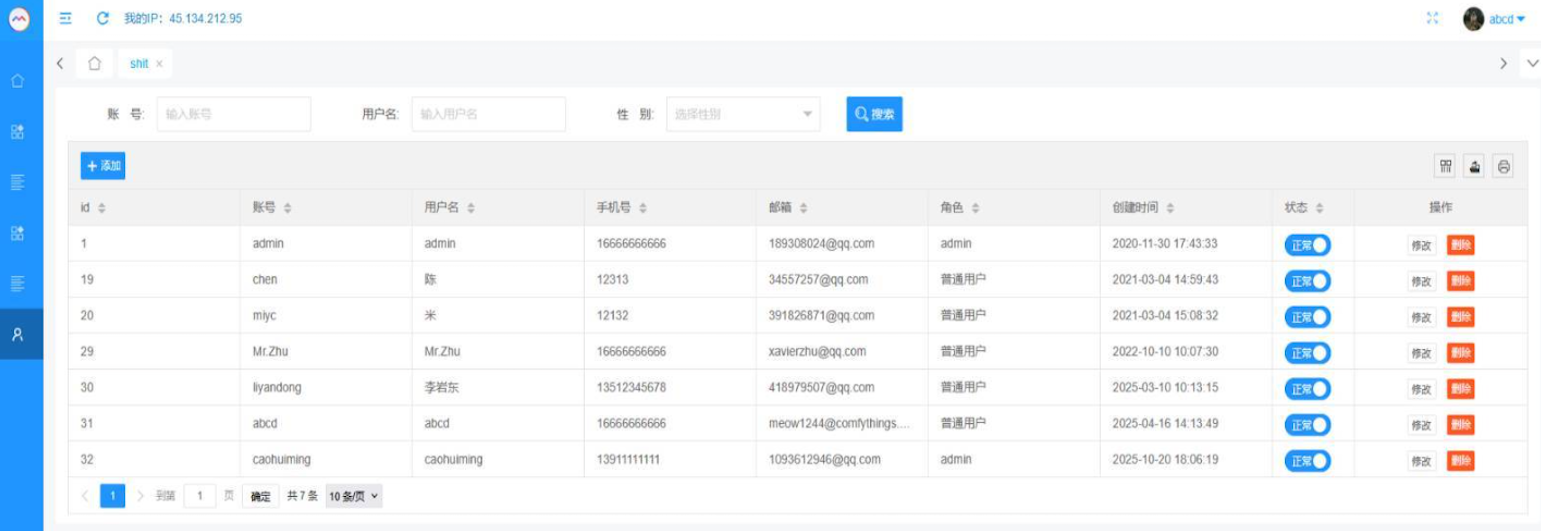
Initially, KrebsOnSecurity expressed skepticism regarding the claim of Kimwolf operators breaching the Badbox 2.0 botnet. However, a deeper dive into the email addresses present in the leaked screenshot, particularly those utilizing the qq.com domain, has provided substantial corroborating evidence.
CATHEAD: Unraveling the Connections
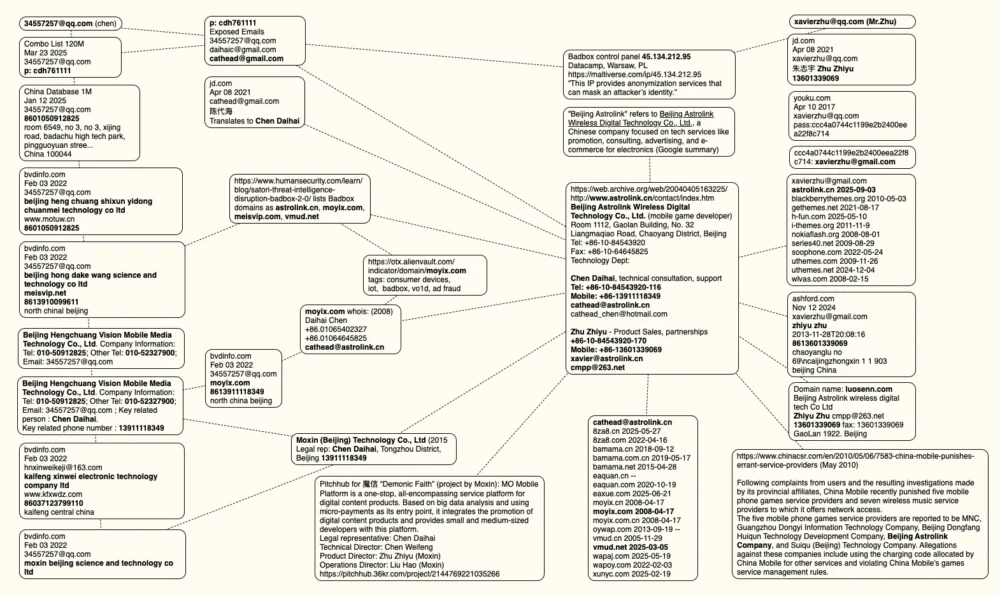
A key element in this investigation is the email address [email protected], listed as "Chen" in the Badbox 2.0 panel. Online searches connect this email to several China-based technology companies, including Beijing Hong Dake Wang Science & Technology Co Ltd., Beijing Hengchuang Vision Mobile Media Technology Co. Ltd., and Moxin Beijing Science and Technology Co. Ltd. The website for Beijing Hong Dake Wang, asmeisvip[.]net, was identified in a March 2025 report by HUMAN Security as a distribution and management site for the Badbox 2.0 botnet. Similarly, moyix[.]com, associated with Beijing Hengchuang Vision Mobile, is also linked to Badbox 2.0 operations.
Further investigation through the breach tracking service Constella Intelligence reveals that the email address [email protected] once used the password "cdh76111." This same password was also found to be associated with two other email accounts: [email protected] and [email protected]. Constella’s findings indicate that [email protected] was used to register an account on jd.com (China’s largest online retailer) in 2021 under the name "Chen Daihai." DomainTools.com confirms that the name Chen Daihai appears in the original registration records (dating back to 2008) for moyix[.]com, alongside the email address cathead@astrolink[.]cn. Notably, astrolink[.]cn is also listed among the Badbox 2.0 domains identified in HUMAN Security’s 2025 report. DomainTools further links cathead@astrolink[.]cn to the registration of over a dozen domains, including vmud[.]net, another domain flagged by HUMAN Security in connection with Badbox 2.0.
XAVIER: A Shared Digital Footprint
A cached version of astrolink[.]cn from archive.org reveals it to be the website of a mobile app development company named Beijing Astrolink Wireless Digital Technology Co. Ltd. An archived "Contact Us" page from 2007 lists Chen Daihai as a member of the company’s technology department. The other individual featured on this page is Zhu Zhiyu, whose email address is provided as xavier@astrolink[.]cn.
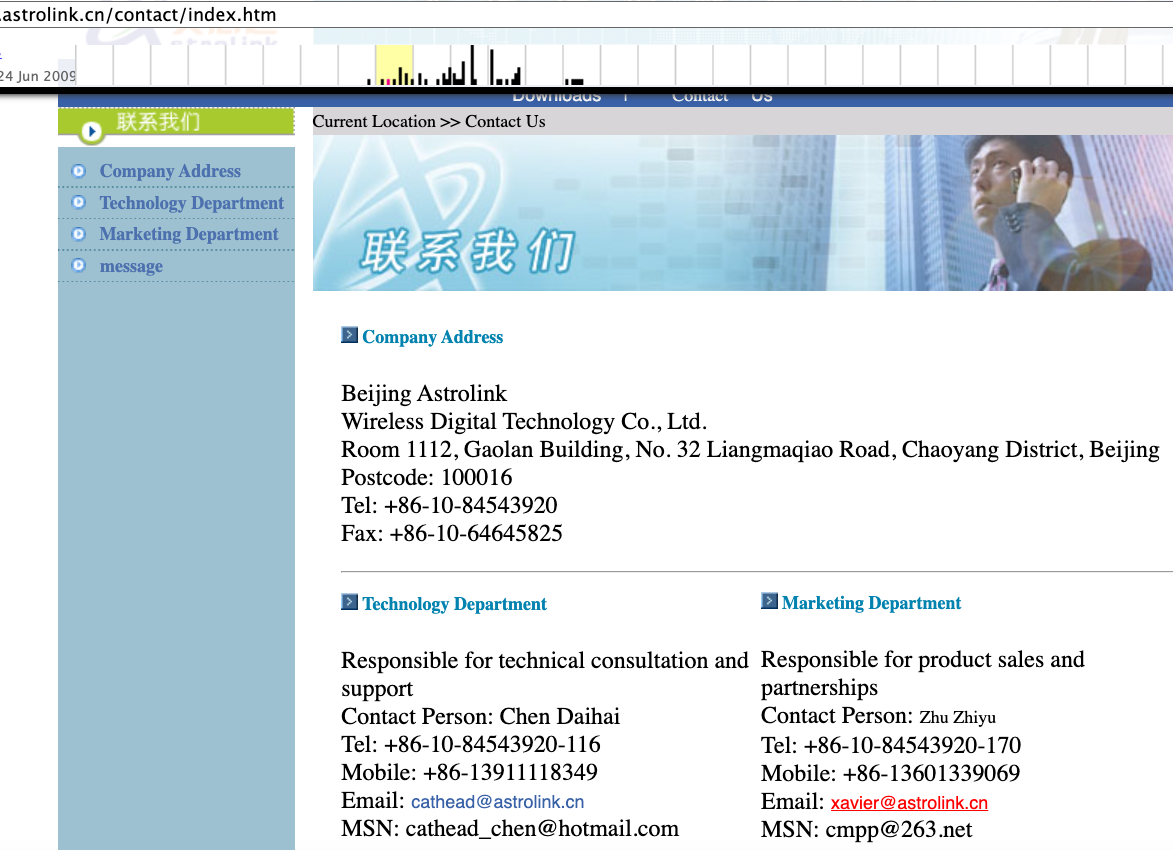
This connection is further solidified by the Badbox 2.0 control panel, which lists a user named "Mr.Zhu" with the email address [email protected]. Constella’s analysis of [email protected] reveals a jd.com account registered in the name of Zhu Zhiyu. A distinctive password used for this account matches the password used by [email protected]. DomainTools identifies [email protected] as the original registrant of astrolink[.]cn. This convergence of email addresses, associated names, and domain registrations strongly suggests a direct link between Chen Daihai and Zhu Zhiyu and the Badbox 2.0 botnet.
ADMIN: The Unidentified Administrator
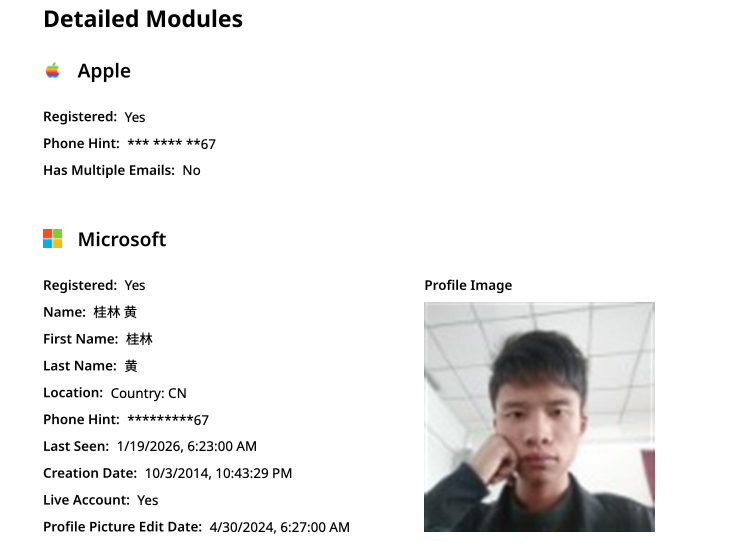
The earliest listed account in the Badbox 2.0 panel is "admin," registered in November 2020, using the email address [email protected]. DomainTools records from 2022 link this email to the domain guilincloud[.]cn, with the registrant name "Huang Guilin." Constella Intelligence associates [email protected] with the Chinese phone number 18681627767. Open-source intelligence platform osint.industries confirms this phone number is linked to a Microsoft profile created in 2014 under the name "Guilin Huang." The cyber intelligence platform Spycloud notes that this phone number was used in 2017 to create a Weibo account under the username "h_guilin."
While the remaining three users and their associated qq.com email addresses in the Badbox 2.0 panel are also linked to individuals in China, they do not exhibit any apparent connections to the entities operated by Chen Daihai and Zhu Zhiyu, nor to any other identifiable corporate structures. Attempts to solicit comments from these individuals, including Mr. Huang, were unsuccessful.
The presented mind map visually consolidates the search pivots conducted on the email addresses, company names, and phone numbers, strongly suggesting a significant connection between Chen Daihai, Zhu Zhiyu, and the operation of Badbox 2.0.
UNAUTHORIZED ACCESS: A Strategic Advantage
The implication that Kimwolf operators have gained direct access to the Badbox 2.0 botnet is a critical development, primarily due to the unique propagation methods of Kimwolf. The Kimwolf botmasters discovered a way to exploit residential proxy services, enabling them to relay malicious commands to vulnerable devices residing behind the firewalls of unsuspecting users on their local networks.
The primary targets of Kimwolf’s exploitation are Internet of Things (IoT) devices, particularly unsanctioned Android TV boxes and digital photo frames, which often lack any built-in security or authentication. This vulnerability means that any device that can be communicated with can be compromised with a single command. Our earlier reporting in January featured research from Synthient, a proxy-tracking firm, which alerted eleven residential proxy providers about the vulnerability of their endpoints to abuse for local network probing and exploitation. While most of these providers have since implemented patches to prevent such upstream access, the source of the Badbox 2.0 screenshot suggests that Kimwolf operators had a contingency plan: secret access to the Badbox 2.0 botnet control panel.
"Dort has gotten unauthorized access," the source stated. "So, what happened is normal proxy providers patched this. But Badbox doesn’t sell proxies by itself, so it’s not patched. And as long as Dort has access to Badbox, they would be able to load the Kimwolf malware directly onto TV boxes associated with Badbox 2.0." The exact method by which Dort gained access to the Badbox botnet panel remains unclear. However, it is highly probable that Dort’s current unauthorized access will be short-lived. Upon notifying the qq.com email addresses listed in the control panel screenshot, including inquiries about the seemingly rogue "ABCD" account, a copy of the image and the questions were sent, likely triggering security measures within the Badbox 2.0 infrastructure.









