Most crypto users believe that their funds stay secure as long as their private keys are protected, but as a rising number of sophisticated scams demonstrate, this fundamental assumption is increasingly being challenged by insidious tactics like address poisoning, which allows attackers to steal assets without ever gaining access to a victim’s private key. This alarming trend underscores a critical vulnerability not in the cryptographic strength of blockchain, but in the human element and the interfaces we use to interact with it.
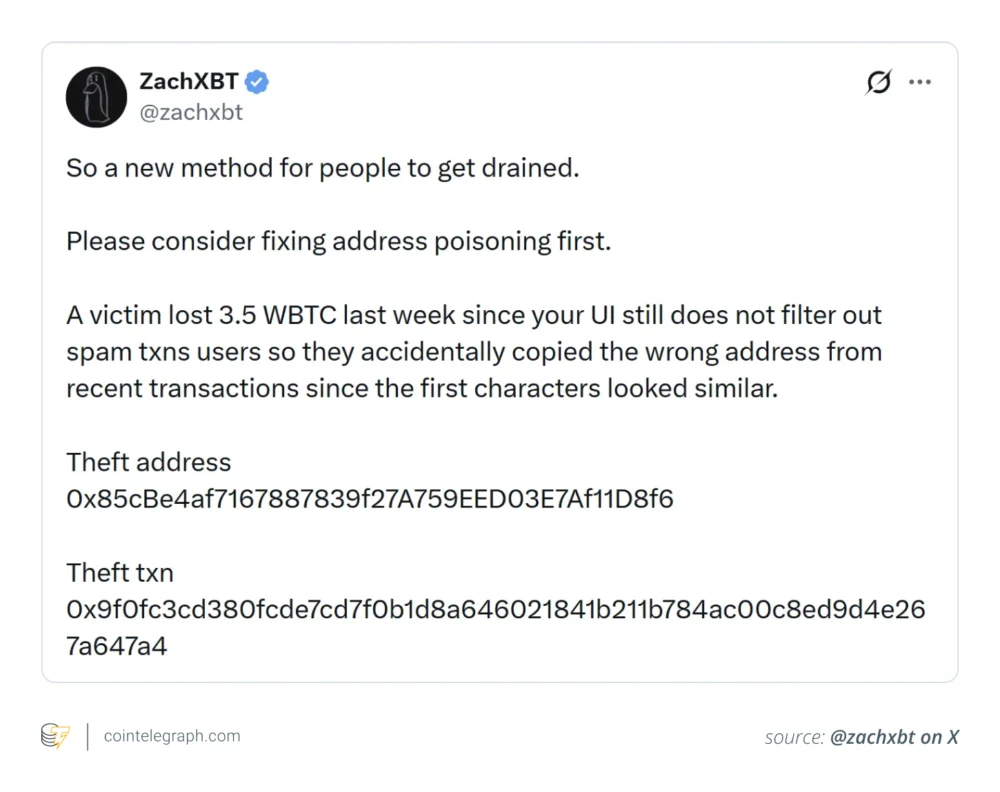
In a stark reminder of this danger, February 2026 saw a sophisticated phishing scheme leverage address poisoning to target a Phantom Chat feature, resulting in the successful draining of approximately 3.5 Wrapped Bitcoin (wBTC), an amount valued at over $264,000 at the time. This incident wasn’t an isolated case; in 2025, an even more devastating loss occurred when a victim lost a staggering $50 million in Tether’s USDt (USDT) after inadvertently copying a poisoned address from their transaction history. Such high-profile incidents serve as glaring evidence of how seemingly minor issues like poor interface design and deeply ingrained user habits can converge to facilitate massive financial losses in the crypto space.
The gravity of this threat has prompted prominent crypto figures, including Binance co-founder Changpeng “CZ” Zhao, to publicly urge wallet providers to implement stronger safeguards against address poisoning. Their calls highlight a growing recognition that true crypto security extends beyond the technical invulnerability of private keys and must encompass a robust defense against social engineering and user interface vulnerabilities.
This article delves into the mechanics of address poisoning scams, meticulously explaining how they exploit fundamental aspects of user behavior rather than relying on private key theft. It details the sophisticated methods attackers employ to manipulate transaction histories, elucidates why this tactic proves remarkably effective on the transparent and immutable ledgers of public blockchains, and outlines practical, actionable steps that both individual users and wallet developers can adopt to significantly mitigate the risk of falling victim to this stealthy form of digital theft.
What Address Poisoning Really Involves
Unlike traditional hacks that attempt to compromise private keys through malware or exploit code flaws within smart contracts, address poisoning operates on an entirely different premise: it manipulates a user’s perceived transaction history to subtly deceive them into sending their valuable funds to an attacker-controlled address. The genius, and terror, of this scam lies in its simplicity and its exploitation of human trust.
The attack typically unfolds in a methodical, multi-step process:
- The Dusting Transaction: The attacker first identifies a target victim, often someone with a significant balance, and sends a minuscule amount of cryptocurrency (often referred to as "dust," typically fractions of a cent) from an attacker-controlled wallet to the victim’s wallet. The crucial element here is that the attacker’s wallet address is meticulously crafted to be a "lookalike" of an address the victim frequently interacts with, particularly one they have sent funds to in the past.
- Poisoning the History: Because all transactions on a public blockchain are recorded, this unsolicited dusting transaction appears in the victim’s wallet history. The attacker’s lookalike address is now prominently displayed as a "recent" transaction, often appearing alongside legitimate past transfers.
- The Trap: When the victim next intends to send funds, especially if they are making a repeat transfer to a known recipient, they might instinctively consult their transaction history to retrieve the recipient’s address. Instead of painstakingly verifying the full address string, they glance at the recent transactions, see an address that looks familiar (due to identical first and last few characters), and copy the poisoned lookalike address.
- The Irreversible Loss: The victim then pastes this poisoned address into their wallet’s send field, reviews the truncated address display, confirms the transaction, and signs it with their private key. Because the user willingly signed the transaction, the blockchain processes it as legitimate, and the funds are irrevocably sent to the attacker’s wallet.
Crucially, throughout this entire process, the victim’s wallet and private keys remain completely untouched and secure. The underlying blockchain cryptography itself remains unbroken, functioning precisely as designed. The scam thrives purely on human error, the inherent trust users place in their own transaction history, and the subtle manipulation of familiar patterns.

Did you know? Address poisoning scams have seen a significant surge in prevalence alongside the rapid growth of Ethereum layer-2 networks. The reason is largely economic: the substantially lower transaction fees on these scaling solutions make it incredibly cheap for attackers to mass-send "dust" transactions to thousands of potential victim wallets at once, dramatically increasing their chances of success at minimal cost.
How Attackers Craft Deceptive Addresses
The cornerstone of an address poisoning scam is the creation of a "lookalike" address that can easily be mistaken for a legitimate one. Crypto addresses, particularly on Ethereum-compatible chains, are lengthy hexadecimal strings, typically 42 characters long (e.g., 0x742d35Cc6634C0532925a3b844Bc454e4438f44e). This extended length is a security feature, making brute-forcing an address virtually impossible. However, it also creates a user experience challenge.
Most wallet interfaces, for the sake of brevity and readability, display only a truncated version of an address, such as 0x85c...4b7. This common UI pattern is precisely what scammers exploit. They craft fake addresses that possess identical beginnings and endings to the target’s frequently used legitimate addresses, while only the middle portion differs.
Consider these examples:
- Legitimate address (example format):
0x742d35Cc6634C0532925a3b844Bc454e4438f44e - Poisoned lookalike address:
0x742d35Cc6634C0532925a3b844Bc454e4438f4Ae(Notice the subtle ‘A’ instead of ‘4’ near the end, and potentially other changes in the middle.) - Another example (more common):
- Legitimate:
0xabc123...def456 - Poisoned:
0xabc123...ghi789...def456(whereghi789is a unique middle string the attacker controls, butabc123anddef456match the legitimate address’s prefix and suffix).
- Legitimate:
Scammers leverage sophisticated vanity address generators to craft these near-identical strings. These tools use significant computational power (often GPU-accelerated) to find addresses that match specific prefixes, suffixes, or even combinations of both. The goal is to create an address that, when truncated by a wallet, appears indistinguishable from the legitimate one at a quick glance. Once generated, this fake address appears in the victim’s transaction history thanks to the dusting transfer, creating the illusion of trustworthiness, especially since most users rarely take the time to verify the entire 42-character string before confirming a transaction.
Did you know? In response to the growing threat of address poisoning, some advanced blockchain explorers and wallet interfaces are now implementing features to automatically label or flag suspicious dusting transactions. These tools analyze transaction patterns, sender histories, and even known scammer databases to help users spot potential poisoning attempts before they inadvertently interact with their transaction history to initiate a transfer.
Why This Scam Succeeds So Well
The devastating effectiveness of address poisoning stems from a complex interplay of human psychology, interface design flaws, and the inherent properties of blockchain technology. There are several intertwined factors that make this scam particularly potent:
- Human Psychology and Habits: Users are creatures of habit. When making repeat transactions, most individuals will instinctively look for familiar patterns rather than re-verifying every single character of a lengthy address. They often check only the first few and last few characters, relying on visual cues. The pressure to complete transactions quickly, especially in volatile markets or during busy periods, further exacerbates this tendency to skim rather than scrutinize. This cognitive shortcut is precisely what the "lookalike" address exploits. Users often suffer from confirmation bias, seeing what they expect to see (their known recipient’s address) even when a subtle difference exists.
- Suboptimal Wallet User Experience (UX): Current wallet interfaces, while generally improving, often inadvertently contribute to the problem. The widespread practice of truncating addresses (e.g.,
0x...) without providing prominent, easy-to-use full-address verification tools is a major weakness. Furthermore, wallet transaction histories often display all incoming transactions by default, legitimate or not, without clear warnings or filtering options for unsolicited "dust." This means a malicious dusting transaction can sit right alongside legitimate past transfers, ready to be copied. The lack of visual distinction or warning between a known, whitelisted address and a newly encountered one adds to the confusion. - No Need for Technical Exploits: This is perhaps the most unsettling aspect. Address poisoning does not require breaking encryption, hacking a wallet’s private key, or exploiting a smart contract vulnerability. Because blockchains are public and permissionless by design, anyone can send tokens to any address. Wallets simply display all incoming transactions, including spam, and users tend to implicitly trust their own transaction history as a reliable source for recipient addresses. The vulnerability lies entirely in human behavior and user experience design, not in the cryptographic security or underlying code of the blockchain itself. The scam leverages the very transparency and immutability that are considered core strengths of blockchain.
The increasing complexity of the crypto ecosystem, with multiple chains, numerous token standards, and diverse wallet types, further adds to the cognitive load on users, making them more susceptible to such subtle deceptions.

Why Keys Aren’t Enough Protection
The common refrain in crypto is "not your keys, not your coins," emphasizing the paramount importance of private key security. Private keys are indeed critical; they control authorization, ensuring that only you, the rightful owner, can sign and approve transactions from your wallet. However, their function is limited to authorization, not verification of the destination. A private key cannot discern whether the address you’ve entered is the correct one, only that you have authorized a transfer to that address.
Blockchain’s core characteristics — permissionless access, the irreversibility of transactions, and trust minimization — mean that once a malicious transaction is signed and broadcast, it gets permanently recorded on the immutable ledger. There is no central authority to reverse or recall funds sent to the wrong address, even if it was done in error. In address poisoning scams, the user willingly signs the transfer to the attacker’s address. From the blockchain’s perspective, the system functions exactly as designed, and the flaw lies purely in human judgment and the method by which the destination address was selected.
Underlying psychological and design issues involve:
- Cognitive Load and Decision Fatigue: Users often manage multiple crypto assets across various platforms and networks. This complexity, combined with the need to stay vigilant against various threats, can lead to mental fatigue. When faced with a routine task like sending funds, users are more likely to take mental shortcuts.
- Confirmation Bias: People tend to interpret information in a way that confirms their existing beliefs or expectations. If a user expects to see a particular address in their history, they might subconsciously overlook subtle differences in a lookalike address.
- Lack of Standardized Verification Methods: Unlike traditional banking where recipient accounts have names and often require dual verification, crypto addresses are anonymous strings. There’s no universal, easy-to-use method for cross-referencing an address with a known recipient’s identity within most wallets.
- Over-reliance on Visual Cues: As discussed, truncated addresses are a major culprit. Users are trained by wallet UIs to trust these partial displays, making them vulnerable when the hidden middle characters are swapped.
- The "Copy-Paste" Habit: The ubiquitous nature of copy-pasting addresses, while convenient, removes the opportunity for manual verification and introduces risks if the source (like a poisoned transaction history) is compromised.
Did you know? In certain sophisticated cases, attackers don’t just use pre-generated vanity addresses. They automate address lookalike generation using powerful GPU-powered tools, allowing them to rapidly produce thousands of near-identical wallet addresses specifically tailored to match the prefixes and suffixes of high-value targets within minutes. This significantly increases their chances of hitting a "match" for a victim’s frequent transaction partners.
Practical Ways to Stay Safer
While address poisoning exploits human behavior rather than technical vulnerabilities, small yet significant changes in transaction habits and thoughtful interface design can drastically reduce the risk. Understanding and implementing a few practical safety measures can empower crypto users to avoid costly mistakes without requiring advanced technical knowledge.
For Users
Simple verification habits and transaction discipline can significantly reduce your chances of falling victim to address poisoning scams.
- Always Verify the Full Address: This is the golden rule. Before confirming any transaction, especially for large amounts, take the extra time to compare the entire 42-character destination address with the known, legitimate address. Copy-pasting the full address into a text editor and comparing it side-by-side with the correct address (from a trusted source, not your recent history) is a good practice.
- Utilize Address Books/Whitelists: Most modern wallets offer an address book feature where you can save and label frequently used addresses. Always use these whitelisted addresses for repeat transactions instead of copying from your transaction history. Once an address is saved, you know it’s correct.
- Perform Small Test Transactions: For very large transfers, consider sending a minuscule amount (e.g., $1 or the smallest possible unit of the asset) to the recipient’s address first. Once that test transaction is confirmed as received by the intended party, you can then proceed with the larger transfer, confident that the address is correct.
- Clear or Filter Transaction History: Regularly review your wallet’s transaction history. If your wallet allows it, hide "dusting" transactions or filter them out so they don’t clutter your view. Be suspicious of any incoming transactions you don’t recognize, especially those involving tiny amounts.
- Bookmark Trusted Sources: If you frequently interact with smart contracts or exchanges, bookmark their official addresses and URLs directly. Never rely on links from chat messages or search results that could be compromised.
- Be Wary of Unsolicited Transactions: Treat any incoming transaction you didn’t expect, especially small "dust" amounts, as a potential red flag. Do not interact with the sender’s address or assume it’s legitimate.
- Educate Yourself Continuously: Stay informed about new scam tactics. Security in crypto is an ongoing learning process.
For Wallet Developers
Thoughtful interface design and built-in safeguards can minimize user error and make address poisoning attacks far less effective, shifting the burden away from the user’s constant vigilance.
- Enhanced Address Display and Verification:
- Full Address Prominence: Always display the full address prominently when a user is about to send funds. Provide a clear, one-click button to copy the full address.
- Visual Differentiators: Implement visual cues (e.g., color coding, distinct icons) to highlight new or unsaved addresses versus those already in the user’s address book.
- "Diff" Highlighting: When an address is pasted, automatically compare it to known, frequently used addresses (if applicable) and visually highlight any differing characters to draw the user’s attention.
- Intelligent Transaction History Filtering:
- Hide Dust by Default: Offer an option, or make it default, to hide transactions below a certain value threshold to declutter history and obscure dusting attempts.
- Flag Suspicious Transactions: Implement algorithms to detect and flag potential dusting attacks with clear warnings within the transaction history.
- Categorization: Allow users to categorize or label transactions (e.g., "known contact," "exchange deposit").
- Robust Warning Mechanisms:
- New Address Warnings: Before sending to an address not in the user’s address book or one they haven’t transacted with recently, present a clear, unavoidable warning prompting them to double-check the full address.
- "Similar Address" Alerts: If a pasted address is very similar (e.g., same first/last few characters) to a frequently used legitimate address but not identical, trigger a specific alert.
- Promote Address Book Usage: Make the address book feature intuitive, easy to use, and encourage users to save addresses for repeat transactions. Perhaps integrate a "save to address book" prompt after a successful first transaction.
- Checksums and ENS Integration: Leverage technologies like Ethereum Name Service (ENS) for human-readable addresses, which are far less prone to poisoning. Encourage its adoption. For direct addresses, ensure checksums are correctly validated.
- In-App Educational Prompts: Provide short, contextual security tips within the wallet interface, especially around sending funds or interacting with transaction history.
Cointelegraph maintains full editorial independence. The selection, commissioning and publication of Features and Magazine content are not influenced by advertisers, partners or commercial relationships.