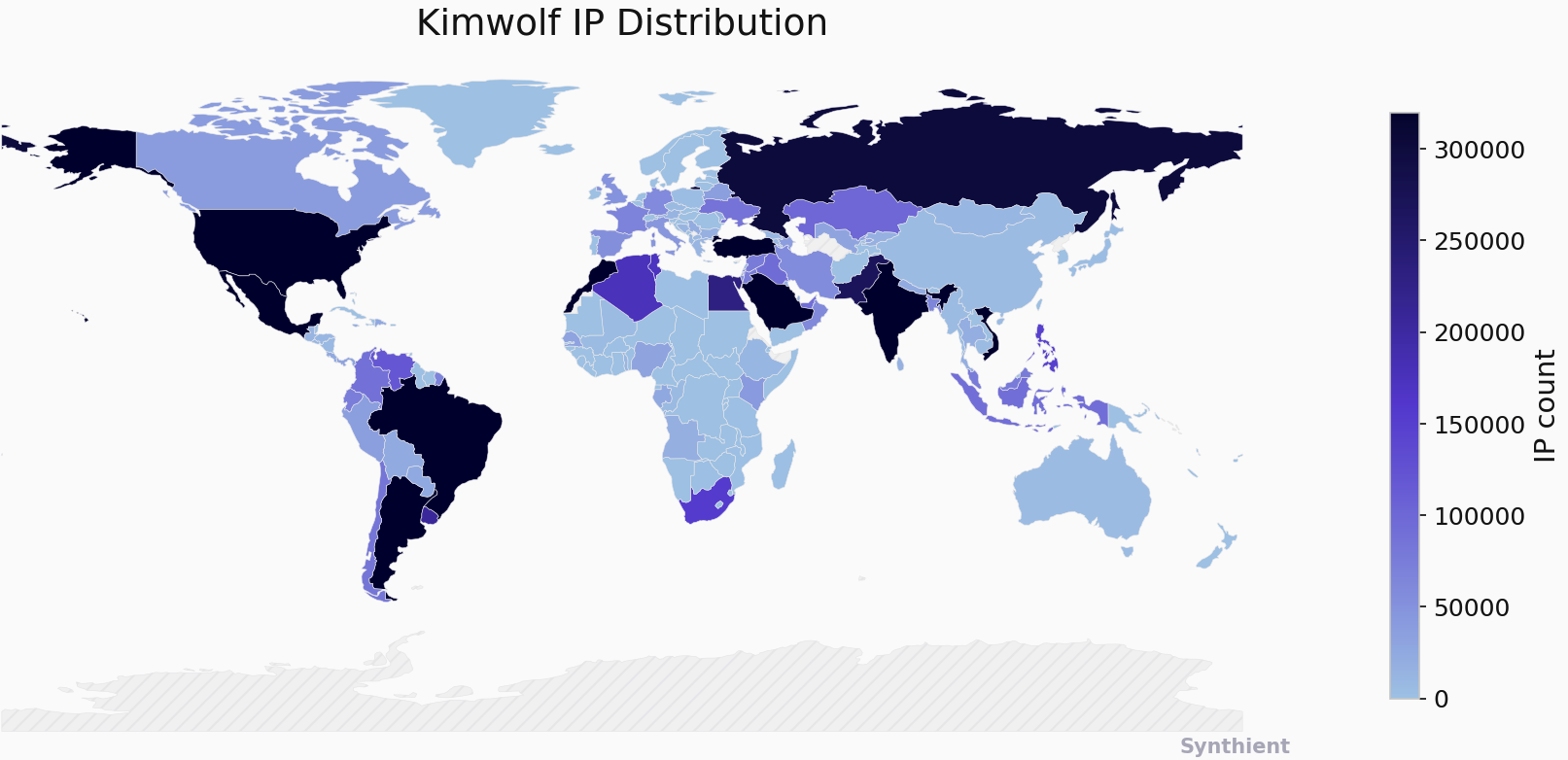
The Kimwolf botnet has experienced explosive growth in recent months, infecting an estimated over 2 million devices globally. This sophisticated malware forces compromised systems to relay malicious internet traffic, including ad fraud, account takeover attempts, and mass content scraping, while also participating in crippling Distributed Denial-of-Service (DDoS) attacks capable of taking down websites for extended periods. However, Kimwolf’s most alarming characteristic is its insidious propagation method: it effectively tunnels through residential proxy networks, infiltrating the local networks of proxy endpoints and infecting devices shielded by users’ firewalls and routers.
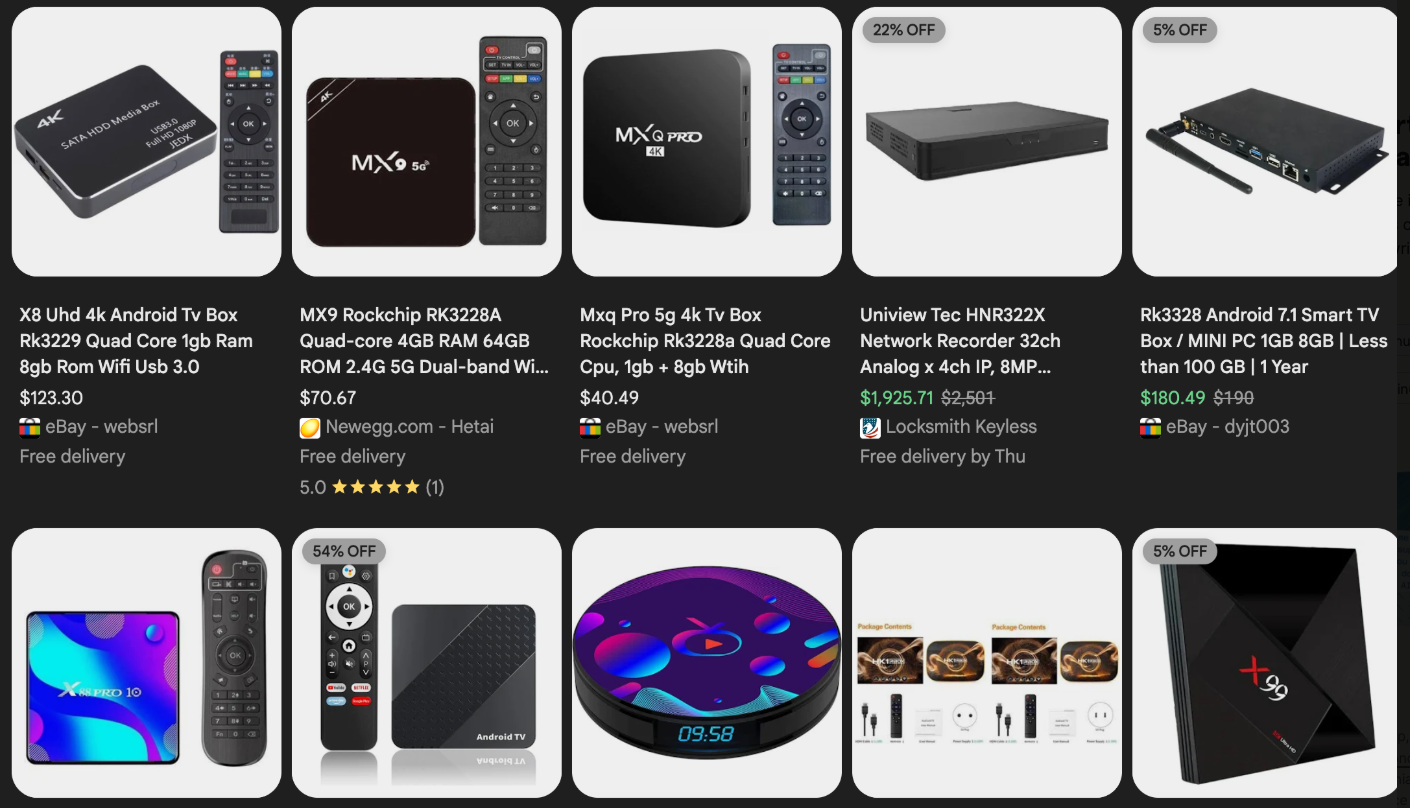
Residential proxy networks, typically sold for anonymizing and localizing web traffic, are often bundled with dubious mobile apps and games. More critically, they are commonly installed via unofficial Android TV boxes purchased from third-party sellers on major e-commerce platforms like Amazon, BestBuy, Newegg, and Walmart. These devices, ranging from $40 to $400, are advertised under numerous no-name brands and model numbers, often promoting free streaming of subscription video content. The hidden cost of this convenience is the risk of infection, as these TV boxes constitute a significant portion of the estimated two million Kimwolf-infected systems.

Kimwolf also effectively infects various internet-connected digital photo frames, readily available on e-commerce sites. Research published in November 2025 by Quokka highlighted severe security flaws in Android-based digital picture frames utilizing the Uhale app, including Amazon’s best-selling digital frame at the time. These photo frames and unofficial Android TV boxes present two major security risks. Firstly, a substantial number come with pre-installed malware or require users to download unofficial Android app stores and malware to function as advertised for video piracy. The most common of these infections turn devices into residential proxy nodes, resold to others. Secondly, these devices often rely on internet-connected microcomputer boards lacking any built-in security or authentication. This means that any device on the same network can potentially be compromised with a single command.
The convergence of these security issues became apparent in October 2025 when Benjamin Brundage, a 22-year-old computer science student and founder of the security firm Synthient, began closely monitoring Kimwolf’s expansion and interacting with its apparent creators. Brundage suspected Kimwolf was an Android-based variant of Aisuru, a botnet previously, and possibly incorrectly, blamed for record-smashing DDoS attacks. Kimwolf’s rapid growth stems from its exploitation of a critical vulnerability in many large residential proxy services. The core weakness lies in these services’ insufficient measures to prevent customers from forwarding requests to internal servers of individual proxy endpoints.
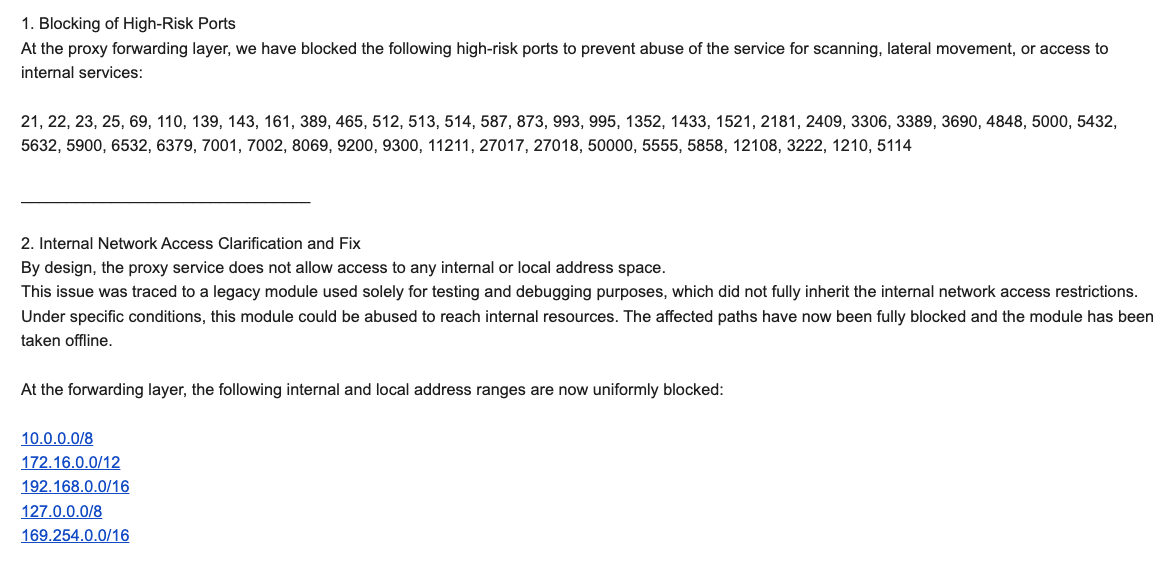
Most proxy services implement basic safeguards against "going upstream" into local networks by denying requests for RFC-1918 private IP address ranges (10.0.0.0/8, 192.168.0.0/16, and 172.16.0.0/12). These ranges are fundamental to home and office networks, enabling multiple devices to share a single public IP address. However, Brundage discovered that Kimwolf operators could bypass these restrictions by altering their Domain Name System (DNS) settings to match RFC-1918 address ranges. Brundage’s research, detailed in a security advisory to nearly a dozen residential proxy providers, revealed that attackers could send carefully crafted requests to current or local network devices, actively exploiting this for malware deployment.
Similar to the digital photo frames, many residential proxy services operate on mobile devices running apps with hidden components that turn user phones into proxy nodes, often without explicit consent. Synthient’s report indicates that key Kimwolf actors are monetizing the botnet through app installs, selling proxy bandwidth, and offering DDoS functionality. The report warns of growing interest among threat actors in gaining unrestricted access to proxy networks for infection, network access, or data theft, highlighting the risks posed by unsecured proxy networks as viable attack vectors.
Further investigation by Brundage into unofficial Android TV boxes, heavily represented in the Kimwolf botnet, revealed another significant factor in its rapid spread: the default enablement of Android Debug Bridge (ADB) mode. ADB is a diagnostic tool intended solely for manufacturing and testing, allowing remote configuration and firmware updates. However, leaving it enabled creates a security nightmare, as these devices constantly listen for and accept unauthenticated connection requests. A simple command like "adb connect" followed by the device’s local IP address and port 5555 can grant unrestricted "super user" administrative access.
By early December, Brundage identified a direct correlation between new Kimwolf infections and proxy IP addresses offered for rent by IPIDEA, identified as the world’s largest residential proxy network. Brundage reported that Kimwolf had nearly doubled in size in the preceding week by exploiting IPIDEA’s proxy pool, a claim confirmed by Synthient’s observation of approximately 2 million IPIDEA addresses exploited by Kimwolf in the week prior. Brundage noted Kimwolf’s remarkable ability to rapidly rebuild itself to millions of infected systems by tunneling through IPIDEA’s proxy endpoints after takedown efforts. Synthient’s analysis of IPIDEA’s proxy pool revealed that over two-thirds of the exposed devices were Android devices vulnerable to compromise without authentication.
Brundage shared his findings with affected proxy providers on December 17, aiming to allow them several weeks to address the vulnerabilities before public disclosure. Many of these providers were resellers of IPIDEA’s service. KrebsOnSecurity had previously contacted IPIDEA for comment regarding its apparent benefit from the Aisuru botnet’s shift towards installing proxy programs. An IPIDEA employee, "Oliver," denied any association with the Aisuru botnet, citing verification of IP traceability and supplier agreements, and asserting IPIDEA’s commitment to compliant operations.
However, on the same day Oliver’s email was received, Brundage received a response from IPIDEA’s security officer, "Byron." Byron acknowledged a legacy testing and debugging module that, under specific conditions, could be abused to access internal resources. He stated that these paths had been blocked, the module taken offline, and that IPIDEA had implemented mitigations to block DNS resolution to internal IP ranges and traffic on high-risk ports. Brundage concluded that IPIDEA appeared to have patched the vulnerabilities, noting he had not observed Kimwolf targeting other proxy services.
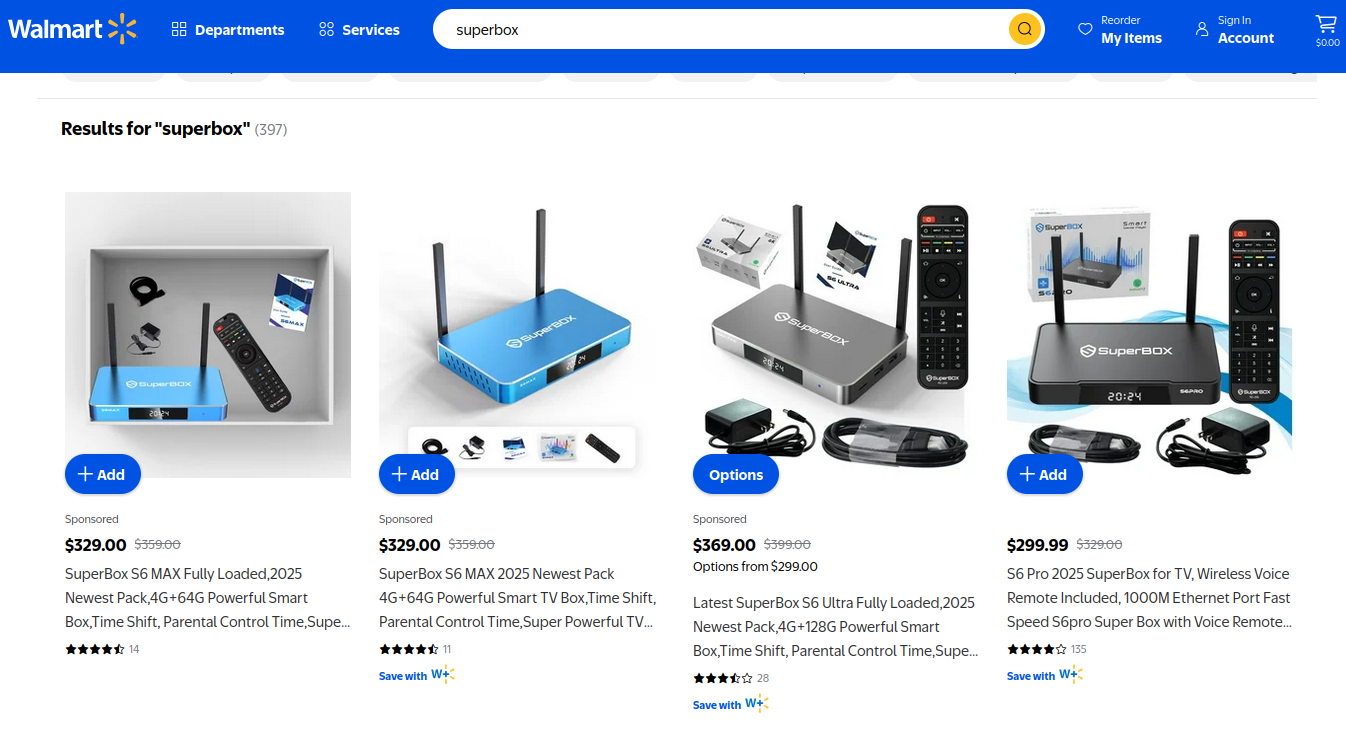
Riley Kilmer, founder of Spur.us, a firm specializing in identifying and filtering proxy traffic, corroborated Brundage’s findings, confirming that IPIDEA and its affiliates allowed unfiltered access to local LANs. Kilmer specifically mentioned the Superbox, an unofficial Android TV box, which leaves Android Debug Mode running on localhost:5555. Because Superbox utilizes IPIDEA proxies, a malicious actor could exploit this to install unwanted software development kits.
Both Brundage and Kilmer suggest that IPIDEA may be a reincarnation of the 911S5 Proxy service, which operated from 2014 to 2022 and was popular on cybercrime forums before imploding after a data breach was disclosed. Research from the University of Sherbrooke in 2022 highlighted 911S5’s potential threat to internal corporate networks, enabling access to shared resources and probing of local area networks (LANs). The U.S. Department of the Treasury later sanctioned the alleged creators of 911S5. Kilmer also noted IPIDEA’s sister service, 922 Proxy, marketed as a successor to 911S5.
Oxylabs, another proxy provider notified by Synthient, acknowledged implementing security modifications to address the reported vulnerabilities, though they stated there was no evidence of Kimwolf exploiting their network.
The practical implications of the Kimwolf botnet are significant. A scenario where a guest using your Wi-Fi, with a phone infected by a residential proxy app, could expose your home’s public IP address for rent. Malicious actors could then use this IP to tunnel into your local area network (LAN) and scan for devices with ADB enabled, potentially infecting devices like digital photo frames and unofficial Android TV boxes. Another nightmare scenario involves attackers modifying your router’s settings via proxy networks to use malicious DNS servers, redirecting your web browsing, reminiscent of the 2012 DNSChanger malware.
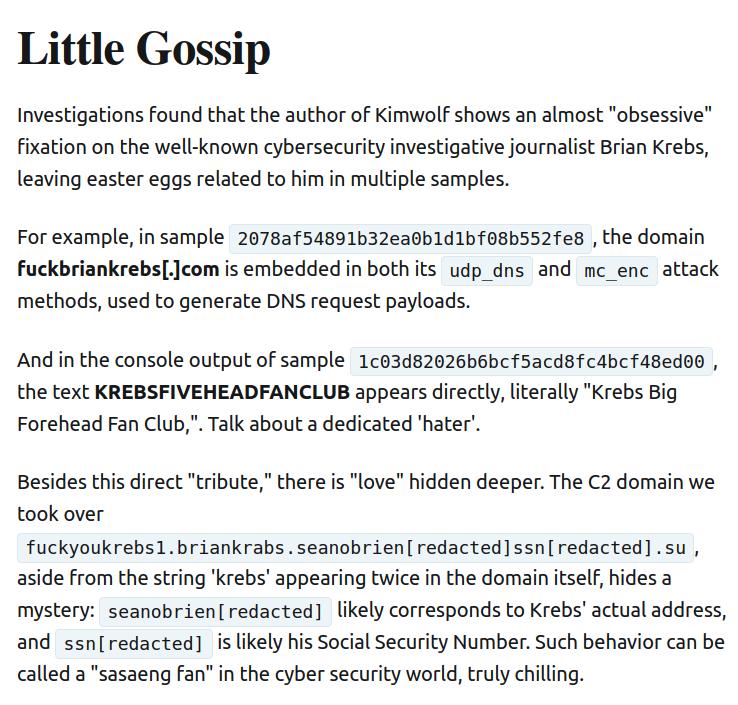
Much of the initial reporting on Kimwolf comes from the Chinese security firm XLab, which first chronicled the Aisuru botnet. XLab began tracking Kimwolf on October 24, noting its control servers swamping Cloudflare’s DNS servers with lookups for specific domains, which briefly topped Cloudflare’s list of most sought-after domains, surpassing Google and Apple. XLab’s analysis suggests that Kimwolf’s primary infection targets are TV boxes in residential environments, and accurately measuring its scale is challenging due to dynamic IP allocation and devices not being online simultaneously. XLab also noted an apparent "obsessive fixation" on the author of the KrebsOnSecurity articles, with "easter eggs" related to their name embedded in the botnet’s code and communications.
XLab’s findings indicate Kimwolf infected between 1.8 and 2 million devices, with significant concentrations in Brazil, India, the United States, and Argentina. While misattributing some early Kimwolf activities to Aisuru was an error, Brundage’s data confirms IPIDEA’s proxy service was massively abused by Kimwolf.
A frustrating aspect of threats like Kimwolf is the difficulty for average users to detect infected devices on their internal networks. Identifying and removing residential proxy malware requires specialized tooling and knowledge beyond typical consumer capabilities. However, Synthient offers a website where users can check if their public IP address has been observed among Kimwolf-infected systems. Brundage has also compiled a list of unofficial Android TV boxes most represented in the Kimwolf botnet, urging users to remove such devices from their networks.

Chad Seaman of Akamai Technologies stresses the need for consumers to be wary of these devices and residential proxy schemes, emphasizing that the notion of a secure LAN is outdated. He highlights that apps can compromise networks, and the threat extends beyond Android devices to include Mac, Windows, and iPhones.
In July 2025, Google filed a lawsuit against the "BadBox 2.0 Enterprise," a botnet of over ten million unsanctioned Android streaming devices engaged in advertising fraud. This followed a June 2025 advisory from the FBI warning of cybercriminals gaining unauthorized access to home networks through pre-configured malware or malicious app downloads during setup. The FBI identified BADBOX 2.0 as a successor to the original BADBOX campaign disrupted in 2024.
Lindsay Kaye of HUMAN Security, who worked on BADBOX investigations, stated that BADBOX botnets and their associated residential proxy networks were detected due to their significant role in advertising fraud, ticket scalping, retail fraud, account takeovers, and content scraping. Kaye advises consumers to stick to reputable brands for connected devices and be cautious about app installations. Utilizing a "Guest" Wi-Fi network on wireless routers is also recommended to isolate guest devices from the local network.
Despite a vocal pro-piracy segment downplaying the risks, it’s crucial to recognize that most buyers of these devices are not security experts and are attracted by the promise of "free" content, unaware of the associated risks. The entertainment industry’s lack of visible pressure on e-commerce vendors to stop selling insecure and actively malicious hardware, largely intended for video piracy, is a significant concern. These TV boxes pose a public nuisance due to their bundled malicious software and lack of built-in security, making them attractive targets for cybercriminals. Part II of this series will delve into clues left by those who have profited most from Kimwolf.