A sophisticated new phishing-as-a-service (PhaaS) platform, dubbed "Starkiller," is revolutionizing the cybercrime landscape by enabling threat actors to bypass traditional detection methods and steal sensitive user data, including multi-factor authentication (MFA) codes. Unlike conventional phishing kits that rely on static copies of login pages, Starkiller dynamically loads the target brand’s legitimate website and acts as a clandestine intermediary. This innovative approach allows attackers to meticulously capture usernames, passwords, and crucially, MFA codes, while seamlessly relaying the target’s interactions back to the authentic site. The ramifications of this advanced technique are significant, potentially empowering less technically adept cybercriminals with potent attack capabilities previously reserved for more sophisticated actors.
The intricacies of deploying successful phishing operations have historically presented a steep learning curve for aspiring cybercriminals. The process demands considerable technical expertise in managing servers, domain registrations, SSL certificates, proxy services, and a host of other repetitive, yet crucial, technical configurations. Starkiller, however, dramatically lowers this barrier to entry. This cutting-edge phishing service empowers its users to select a target brand – encompassing popular platforms like Apple, Facebook, Google, and Microsoft – and then generates a deceptively crafted URL. This malicious link is designed to visually mimic the legitimate domain, thereby lulling unsuspecting victims into a false sense of security. However, beneath this veneer of legitimacy, the traffic is surreptitiously routed through the attacker’s own infrastructure.
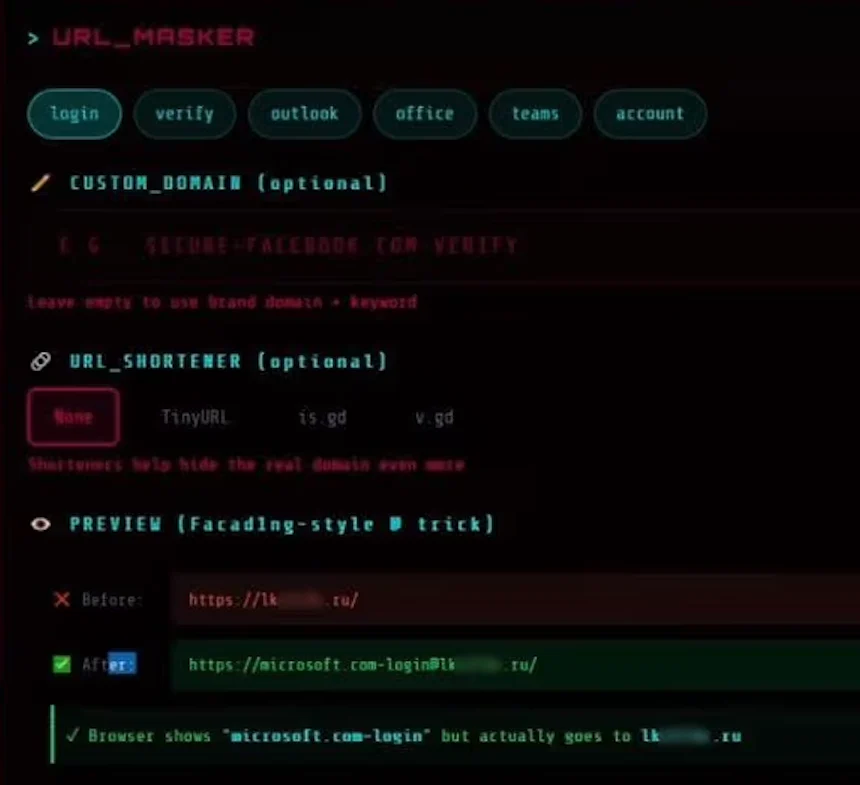
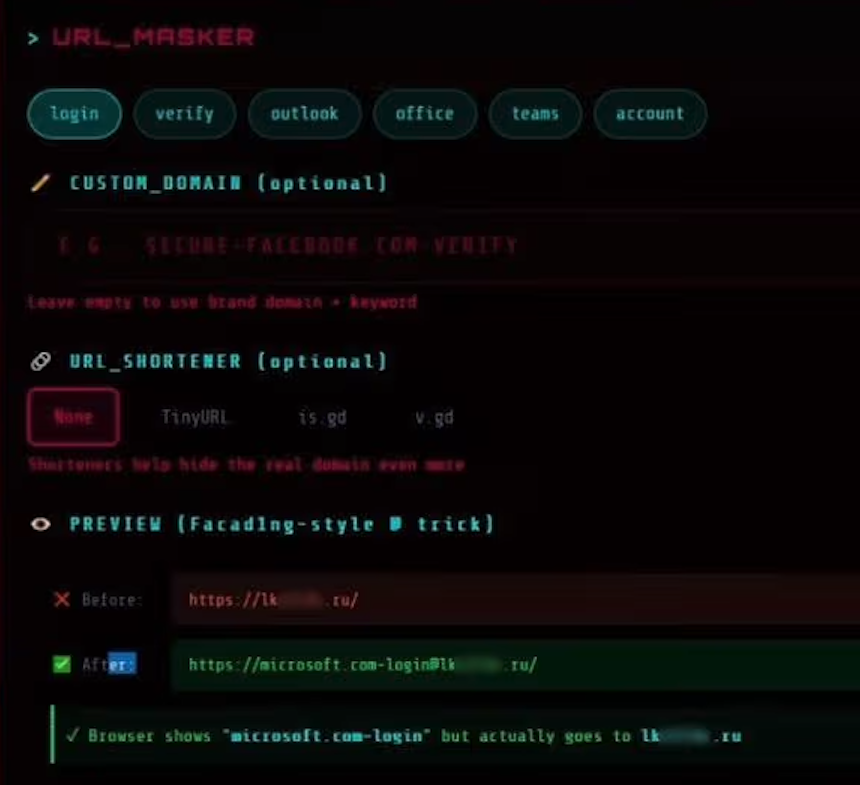
One particularly insidious tactic employed by Starkiller involves the manipulation of URL structures. For instance, a phishing link targeting Microsoft users might appear as "login.microsoft.com@[malicious/shortened URL here]". This clever exploitation of the "@" symbol within URLs is an age-old trick, but its effectiveness is amplified by Starkiller’s sophisticated proxying mechanism. In standard URL parsing, any content preceding the "@" symbol is interpreted as the username, while the actual landing page is what follows. When a victim clicks such a link, their browser, influenced by the deceptive URL structure, is tricked into believing they are navigating to the legitimate Microsoft login page. The image provided by Abnormal AI vividly illustrates this deceptive URL structure, with the actual malicious landing page blurred out, but clearly showing a ".ru" domain, indicating its origin. Starkiller further enhances its stealth by offering integration with various URL-shortening services, making the malicious links appear even more innocuous and harder to trace.
Upon selection of a target URL, Starkiller orchestrates the deployment of a Docker container. This container, running a headless Chrome browser instance, meticulously loads the genuine login page of the targeted service. Abnormal AI’s analysis reveals that this container then functions as a man-in-the-middle (MITM) reverse proxy. In this capacity, it intercepts every piece of data entered by the victim – including keystrokes, form submissions, and session tokens – and forwards these inputs to the legitimate website. Simultaneously, it captures the responses from the authentic site and relays them back to the victim, creating a seamless illusion of direct interaction. Callie Baron and Piotr Wojtyla, researchers at Abnormal AI, detailed this process in their blog post, emphasizing that "Every keystroke, form submission, and session token passes through attacker-controlled infrastructure and is logged along the way."
This intermediary role allows Starkiller to provide its customers with real-time session monitoring capabilities. Threat actors can effectively "live-stream" the victim’s screen as they interact with the compromised page, offering unprecedented insight into their actions. The platform’s feature set extends beyond mere observation, encompassing robust data exfiltration tools. These include keylogger functionality to capture every character typed, the theft of cookies and session tokens for direct account takeover, geo-tracking of targeted individuals, and automated Telegram alerts to notify operators immediately upon the capture of new credentials. Furthermore, Starkiller boasts campaign analytics, mirroring the dashboards found in legitimate Software-as-a-Service (SaaS) platforms, providing metrics such as visit counts, conversion rates, and performance graphs. This comprehensive suite of tools transforms phishing into a highly professionalized, data-driven operation.
Perhaps the most alarming aspect of Starkiller is its ability to circumvent multi-factor authentication (MFA). Because the victim is, in essence, authenticating with the real site through the attacker’s proxy, the MFA process functions as designed. However, the authentication tokens generated are then forwarded to the legitimate service in real-time by the attacker. This allows the attacker to capture the resulting session cookies and tokens, granting them authenticated access to the victim’s account. As Baron and Wojtyla explain, "When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed." This means that even users employing robust MFA security measures are vulnerable to account compromise.
The "URL Masker" feature within the Starkiller service offers users granular control over the configuration of the malicious links. Options are provided for tailoring the deceptive URLs, further enhancing their ability to evade detection and trick victims. The image illustrating this feature showcases the advanced customization available to Starkiller operators.
Starkiller is not an isolated entity but rather one component of a broader suite of cybercrime services offered by a threat group that identifies itself as "Jinkusu." This group actively maintains a user forum where its customers can engage in discussions about attack techniques, request new features, and seek assistance with deployment issues. An additional "a-la-carte" feature available within Jinkusu’s offerings is designed to harvest email addresses and contact information from compromised sessions, with the explicit intention of using this data to build targeted lists for subsequent phishing campaigns.
This Starkiller service represents a significant evolutionary leap in the realm of phishing. Its apparent success is highly likely to be emulated by other enterprising cybercriminals, especially given its ability to circumvent the traditional challenges and costs associated with managing multiple phishing domains and its effectiveness against established phishing detection methodologies like domain blocklisting and static page analysis. The service dramatically lowers the technical barrier to entry for novice cybercriminals, democratizing advanced attack capabilities.
In conclusion, Starkiller embodies a substantial escalation in the sophistication of phishing infrastructure, reflecting a concerning trend towards the commoditization of enterprise-level cybercrime tooling. By integrating advanced features such as URL masking, session hijacking, and MFA bypass, Starkiller effectively equips low-skill cybercriminals with attack capabilities that were previously unattainable, posing a formidable and evolving threat to individuals and organizations alike.