A sophisticated new phishing-as-a-service (PhaaS) platform, dubbed Starkiller, is revolutionizing the cybercrime landscape by enabling threat actors to bypass traditional phishing defenses and even circumvent multi-factor authentication (MFA). Unlike conventional phishing kits that rely on static, easily detectable copies of login pages, Starkiller dynamically loads genuine brand login pages and acts as a covert intermediary between the victim and the legitimate website. This innovative approach allows attackers to capture not only usernames and passwords but also sensitive MFA codes, effectively neutralizing robust security measures and significantly lowering the barrier to entry for less skilled cybercriminals. The service’s advanced capabilities, detailed in an analysis by security firm Abnormal AI, mark a concerning evolution in the sophistication of phishing operations, mirroring the trend towards commoditized, enterprise-grade tools within the cybercrime underworld.
The core functionality of Starkiller lies in its ability to circumvent the typical pitfalls of phishing attacks. Historically, phishing websites have been rudimentary replicas of legitimate login pages, often hosted on temporary domains and quickly flagged by security researchers and anti-abuse teams. Starkiller, however, sidesteps this by using cleverly disguised URLs that, upon clicking, load the target brand’s actual website. The service then acts as a reverse proxy, sitting between the victim and the legitimate site. This means that when a user enters their credentials or MFA codes, Starkiller relays this information to the real website while simultaneously logging the sensitive data for the attacker. This seamless relay ensures that the victim believes they are interacting directly with the legitimate service, even though their data is being intercepted and transmitted through the attacker’s infrastructure.
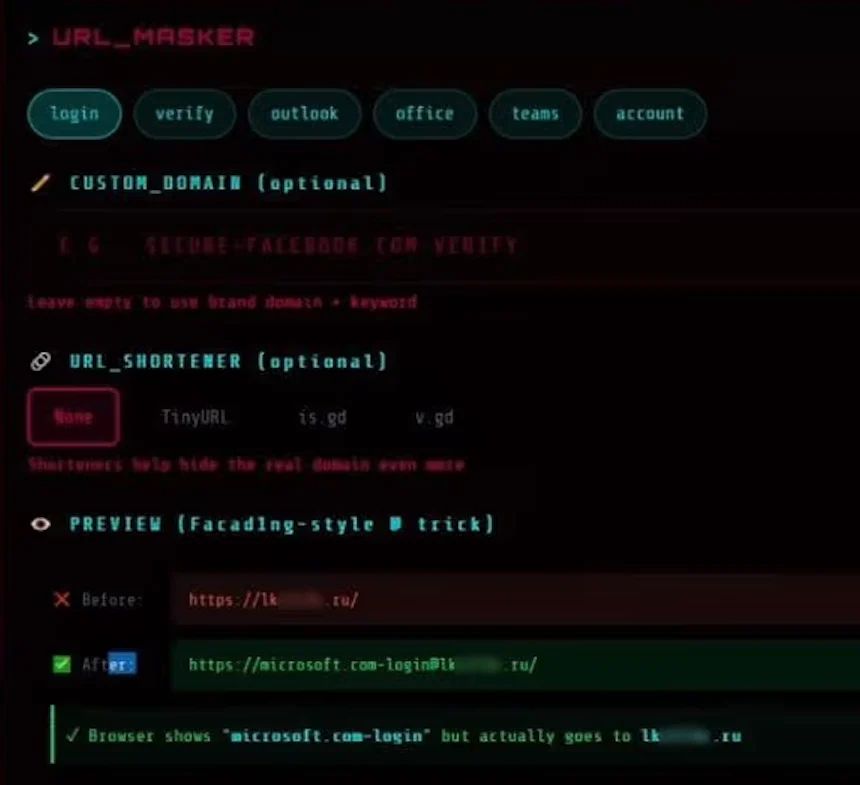
The operational mechanism of Starkiller is particularly concerning due to its technical sophistication and ease of use for its customers. According to Abnormal AI’s analysis, users of Starkiller can select a specific brand to impersonate, with popular targets including Apple, Facebook, Google, and Microsoft. The service then generates a deceptive URL designed to visually mimic the legitimate domain. A prime example cited involves targeting Microsoft users with a link structured as "login.microsoft.com@[malicious/shortened URL here]". This URL exploits a long-standing trick where the portion of a URL preceding the "@" symbol is interpreted by browsers as the username, while the content following it is considered the actual landing page. This clever masking ensures that the user sees what appears to be a legitimate Microsoft login page, obscuring the fact that the traffic is being routed through the attacker’s servers. The image provided by Abnormal AI illustrates this, showing a phishing link ending in a ".ru" domain, further emphasizing the deceptive nature of the campaign. The service also integrates with various URL shortening services, adding another layer of obfuscation to its malicious links.
Once a target URL is selected, Starkiller provisions a Docker container. Within this container, a headless Chrome browser instance is launched. This headless browser then navigates to and loads the genuine login page of the targeted service. As researchers Callie Baron and Piotr Wojtyla of Abnormal AI explained in their blog post, this container functions as a man-in-the-middle reverse proxy. It meticulously forwards all user inputs – keystrokes, form submissions, and session tokens – to the legitimate website. Simultaneously, it captures the legitimate site’s responses and relays them back to the victim, maintaining the illusion of a direct connection. This process means that every piece of information entered by the victim passes through the attacker’s controlled infrastructure and is meticulously logged.
The capabilities offered by Starkiller extend far beyond simple credential harvesting. The platform provides attackers with real-time session monitoring, allowing them to effectively "live-stream" the victim’s screen as they interact with the phishing page. This provides attackers with an unprecedented level of insight into user behavior and potential vulnerabilities. Furthermore, Starkiller incorporates advanced features such as keylogger functionality to capture every keystroke, cookie and session token theft for direct account takeover, geo-tracking of targets, and automated Telegram alerts whenever new credentials are submitted. The service also boasts campaign analytics, offering operators metrics such as visit counts, conversion rates, and performance graphs, mirroring the dashboard experience of legitimate Software-as-a-Service (SaaS) platforms. This level of feature set, presented in a user-friendly interface, significantly democratizes advanced phishing techniques.
One of the most alarming aspects of Starkiller is its ability to effectively bypass MFA. When a victim clicks on a Starkiller-generated link, they are, in essence, authenticating with the real website through the attacker’s proxy. Any MFA codes entered by the victim are forwarded in real-time to the legitimate service. The attacker then captures the resulting session cookies and tokens, granting them authenticated access to the compromised account. As the Abnormal AI researchers highlighted, when the entire authentication flow, including MFA, is relayed in real-time, the security measures, despite functioning correctly, are rendered ineffective. This sophisticated technique circumvents the intended purpose of MFA, which is to add an additional layer of security beyond just credentials.
Starkiller is not an isolated offering but rather a component of a broader suite of cybercrime services provided by a threat group known as Jinkusu. This group actively maintains a user forum where its customers can collaborate, share techniques, request new features, and troubleshoot their phishing deployments. One particularly concerning add-on feature is the ability to harvest email addresses and contact information from compromised sessions, which can then be used to build targeted lists for subsequent phishing campaigns. This integrated ecosystem of cybercrime tools underscores the professionalization and strategic planning within these threat groups.
The implications of Starkiller are profound for the cybersecurity landscape. This service represents a significant leap forward in phishing technology, moving beyond static pages to dynamic, interactive proxies that leverage legitimate infrastructure. Its apparent success is likely to inspire copycat services, as it offers a compelling alternative to the logistical headaches and constant vigilance required to manage multiple phishing domains and evade detection. By eliminating the need for extensive technical expertise in server configuration, domain management, and certificate acquisition, Starkiller drastically lowers the barrier to entry for aspiring cybercriminals. Traditional detection methods, such as domain blocklisting and static page analysis, become significantly less effective against this dynamic approach.
In conclusion, Starkiller embodies a worrying trend towards the commoditization of sophisticated cybercrime tooling. The platform’s ability to combine URL masking, real-time session hijacking, and effective MFA bypass provides low-skill cybercriminals with attack capabilities that were previously the domain of highly skilled and resourced adversaries. This escalation in phishing infrastructure, as highlighted by Abnormal AI, demands a renewed focus on developing adaptive and more resilient security measures to counter these evolving threats. The continuous innovation in phishing-as-a-service platforms like Starkiller necessitates a proactive and collaborative approach from security professionals and organizations worldwide to stay ahead of these increasingly sophisticated cyber threats.