A shadowy and highly aggressive data extortion syndicate, operating under the moniker Scattered Lapsus ShinyHunters (SLSH), has cultivated a particularly insidious modus operandi. Their strategy for extracting ransoms from victimized corporations is characterized by a multi-pronged assault that extends far beyond the digital realm, encompassing relentless harassment, explicit threats, and even "swatting" incidents targeting executives and their families. Concurrently, they amplify their leverage by disseminating details of the data breach to journalists and regulatory bodies, creating a public relations nightmare for their targets. Reports indicate that some organizations, overwhelmed by the escalating personal attacks and the specter of widespread data exposure, are succumbing to the demands. However, a leading expert on SLSH warns that any engagement beyond a firm and unequivocal refusal to pay only serves to embolden the group, highlighting their notoriously volatile and untrustworthy history as a compelling reason to disengage entirely.
Unlike the more structured and disciplined ransomware affiliate groups that often originate from Russia, SLSH presents as a fractious and amorphous English-speaking extortion collective. Their operational style suggests a disinterest in cultivating a reputation for reliability or adhering to any semblance of a consistent code of conduct, which would typically foster a degree of trust in their promises to, for instance, destroy stolen data. This assessment comes from Allison Nixon, Director of Research at the New York City-based cybersecurity consultancy Unit 221B. Nixon has been meticulously tracking the movements of this criminal outfit and its individual members across various Telegram channels, which they utilize as platforms for extorting and harassing their victims. She points out that SLSH deviates significantly from traditional data ransom groups in ways that underscore the futility of trusting their assurances, particularly regarding the deletion of pilfered information.
While many established Russian ransomware operations have employed high-pressure tactics, such as maintaining dark web shaming blogs with countdown clocks or notifying media and corporate boards to compel payment for decryption keys or data deletion promises, SLSH’s extortion attempts escalate far more rapidly and severely. Nixon notes that SLSH’s harassment quickly transcends these conventional methods, escalating to threats of physical violence against executives and their loved ones, debilitating Distributed Denial-of-Service (DDoS) attacks against victim websites, and persistent email-flooding campaigns designed to overwhelm and disrupt operations.
SLSH is recognized for its entry vector, which frequently involves sophisticated phishing attacks targeting employees via phone calls. Once inside, they proceed to exfiltrate sensitive internal data. In a January 30th blog post, Google’s security forensics firm Mandiant detailed how SLSH’s most recent extortion campaigns, occurring in early to mid-January 2026, involved members impersonating IT staff. They contacted employees of targeted organizations, falsely claiming that the company was undergoing Multi-Factor Authentication (MFA) setting updates. The threat actor then directed employees to victim-branded credential harvesting sites to capture their Single Sign-On (SSO) credentials and MFA codes, subsequently registering their own device for MFA to gain persistent access.
Victims often first become aware of a breach when their organization’s name is publicly invoked on whatever ephemeral Telegram group chat SLSH is currently using to threaten, extort, and harass their targets. According to Nixon, this coordinated harassment, orchestrated across SLSH’s Telegram channels, is a deliberate strategy to overwhelm the victim organization by manufacturing a sense of public humiliation, thereby pushing them towards capitulation and payment. Nixon reports that multiple executives from targeted organizations have been subjected to "swatting" incidents. This involves SLSH fabricating a bomb threat or hostage situation at a target’s residence or place of work, with the explicit aim of provoking a heavily armed police response.
"A significant part of their strategy involves the psychological manipulation of victims," Nixon explained to KrebsOnSecurity. "This includes harassing executives’ children and threatening company boards. While these victims are receiving extortion demands, they are simultaneously being contacted by media outlets seeking comments on negative stories that are about to be published about them."

In a blog post published today, Unit 221B argues forcefully against any form of negotiation with SLSH, citing the group’s demonstrable history of making promises they have no intention of keeping. Nixon points out that all known members of SLSH originate from "The Com," a sprawling constellation of Discord and Telegram communities dedicated to cybercrime, functioning as a distributed social network that facilitates rapid collaboration. Nixon further elaborates that extortion groups stemming from The Com tend to foster internal feuds and drama, leading to pervasive lying, betrayal, credibility-destroying behavior, backstabbing, and mutual sabotage.
"With this ongoing dysfunction, often exacerbated by substance abuse, these threat actors frequently lose sight of the core objective of executing a successful, strategic ransom operation," Nixon wrote. "They consistently lose control through outbursts that jeopardize their strategy and operational security, severely limiting their capacity to build a professional, scalable, and sophisticated criminal organization capable of sustained successful ransoms – a stark contrast to more established and professional criminal organizations solely focused on ransomware."
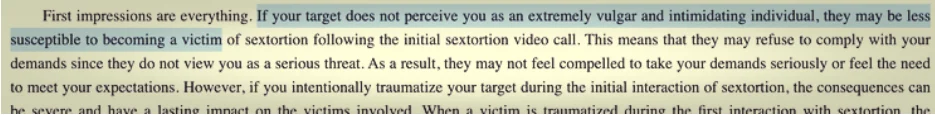
Invasions by well-established ransomware groups typically revolve around encryption/decryption malware that largely remains confined to the affected machine. In contrast, Nixon explains, ransoms demanded by Com-based groups often mirror the tactics employed in violent sextortion schemes against minors. Members of The Com steal damaging information, threaten its public release, and "promise" to delete it if the victim complies, without providing any guarantee or technical proof that they will honor their word.
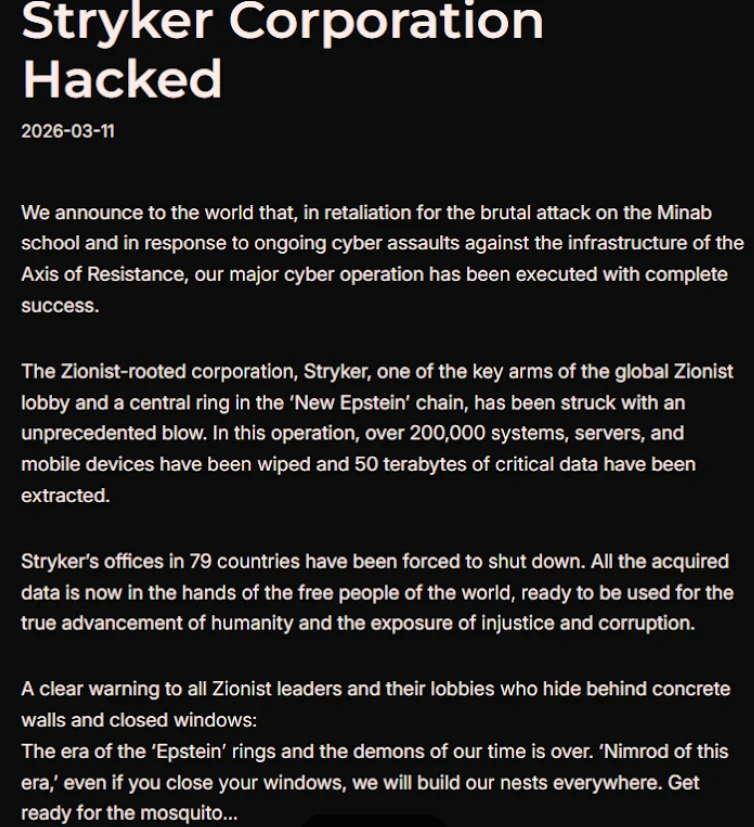
A critical element of SLSH’s strategy to coerce victims into paying, Nixon stated, involves manipulating the media to sensationalize the threat posed by the group. This approach, she noted, borrows heavily from the playbook of sextortion attacks, which aim to keep targets continuously engaged and anxious about the repercussions of non-compliance. "On days when SLSH lacked a significant criminal ‘win’ to announce, they focused on publicizing death threats and harassment to keep law enforcement, journalists, and cybersecurity professionals fixated on their group," she remarked.
Nixon herself has been a target of SLSH’s threats for months, with their Telegram channels frequently featuring explicit threats of physical violence against her, this publication’s author, and other security researchers. She views these threats not just as attempts to generate media attention and a facade of credibility, but also as valuable indicators of compromise, as SLSH members often name-drop and disparage security researchers even in their communications with victims.
"Be vigilant for the following behaviors in their communications to you or in their public statements," an advisory from Unit 221B reads. "Repeated abusive mentions of Allison Nixon (or ‘A.N.’), Unit 221B, or cybersecurity journalists – especially Brian Krebs – or any other cybersecurity employee or company. Any threats to kill, commit terrorism, or inflict violence against internal employees, cybersecurity employees, investigators, and journalists."
Unit 221B emphasizes that while the intense pressure campaign during an extortion attempt can be deeply traumatizing for employees, executives, and their families, engaging in protracted negotiations with SLSH only incentivizes the group to escalate the level of harm and risk, potentially jeopardizing the physical safety of employees and their families. "The breached data will never revert to its original state, but we can assure you that the harassment will cease," Nixon asserted. "Therefore, your decision to pay should be considered independently from the harassment. We believe that by separating these issues, you will objectively recognize that the optimal course of action to safeguard your interests, both in the short and long term, is to refuse payment."