A highly aggressive and unpredictable data extortion gang known as Scattered Lapsus ShinyHunters (SLSH) employs a chillingly effective, multi-pronged strategy to coerce payments from its victims, a strategy that goes far beyond traditional ransomware tactics. This group, characterized by its unruly and fluid English-speaking nature, distinguishes itself from more regimented, Russia-based cybercrime syndicates by its apparent disinterest in building a reputation of reliability. Instead, SLSH leverages a potent combination of data theft, public humiliation, and escalating personal attacks, including threats of violence and even "swatting" incidents against executives and their families. The ultimate goal, according to cybersecurity experts like Allison Nixon of Unit 221B, is to overwhelm victims psychologically, pushing them to pay not just to contain stolen data, but to halt the relentless and terrifying harassment. However, Nixon strongly advises against any engagement beyond a firm refusal to pay, arguing that any negotiation only fuels the group’s malicious endeavors and that, given SLSH’s fractured and unreliable history, the only truly "winning move" is to disengage entirely.
Unlike established ransomware affiliate groups that often operate with a degree of professional rigor, SLSH is described as an unruly and somewhat fluid English-language extortion gang. This lack of consistent behavior makes it difficult for victims to trust any assurances made by the group, particularly regarding the deletion of stolen data. Allison Nixon, director of research at the New York City-based security consultancy Unit 221B, has been meticulously tracking SLSH’s movements across various Telegram channels, observing how they shift their operational bases to continue their extortion and harassment campaigns. She highlights that SLSH deviates significantly from traditional data ransom groups in ways that render them untrustworthy. While many conventional Russian ransomware groups employ high-pressure tactics like publishing stolen data samples on dark web shaming blogs or notifying company journalists and board members, SLSH’s extortion escalates rapidly and intensely. Their tactics extend to direct threats of physical violence against executives and their families, disruptive Distributed Denial of Service (DDoS) attacks on victim websites, and persistent email-flooding campaigns, creating an environment of pervasive fear and disruption.
SLSH’s modus operandi often begins with sophisticated social engineering. The group is known to breach corporate networks through phishing attacks that target employees over the phone. By impersonating IT support staff, they persuade employees to visit fake, victim-branded credential harvesting sites. These sites are designed to capture Single Sign-On (SSO) credentials and Multi-Factor Authentication (MFA) codes. Once access is gained, SLSH members then register their own devices for MFA, effectively hijacking legitimate user accounts. Google’s security forensics firm, Mandiant, detailed this tactic in a January 30th blog post, noting that SLSH’s most recent extortion attacks, occurring in early to mid-January 2026, stemmed from such incidents. Victims typically discover the breach not through internal alerts, but when their organization’s name is publicly broadcast on one of SLSH’s ephemeral Telegram channels, where the group then initiates its threats, extortion demands, and harassment. This public shaming and pressure tactic is a deliberate strategy, according to Nixon, aimed at overwhelming the victim organization with manufactured humiliation, thus pushing them towards payment.
The psychological warfare employed by SLSH is particularly disturbing. Nixon reports that multiple executives from targeted organizations have been subjected to "swatting" attacks. This involves SLSH contacting emergency services with a false report of a bomb threat or hostage situation at the target’s home or workplace, with the intent of provoking a heavily armed police response. "A big part of what they’re doing to victims is the psychological aspect of it, like harassing executives’ kids and threatening the board of the company," Nixon explained to KrebsOnSecurity. "And while these victims are getting extortion demands, they’re simultaneously getting outreach from media outlets saying, ‘Hey, do you have any comments on the bad things we’re going to write about you.’" This orchestrated campaign of fear, public exposure, and personal threat is designed to create an untenable situation for the victim.

Unit 221B, in a blog post released concurrently with the news, strongly advocates against any negotiation with SLSH. The group’s history demonstrates a consistent pattern of making promises it has no intention of keeping, including the supposed deletion of stolen data. Nixon attributes the behavior of SLSH and similar extortion groups to their origins within "The Com," a loosely connected network of Discord and Telegram communities that function as a distributed social network facilitating rapid collaboration among cybercriminals. This environment, Nixon notes, tends to foster internal feuds, drama, lying, betrayals, and sabotage among group members. "With this type of ongoing dysfunction, often compounding by substance abuse, these threat actors often aren’t able to act with the core goal in mind of completing a successful, strategic ransom operation," Nixon wrote. "They continually lose control with outbursts that put their strategy and operational security at risk, which severely limits their ability to build a professional, scalable, and sophisticated criminal organization network for continued successful ransoms—unlike other, more tenured and professional criminal organizations focused on ransomware alone."
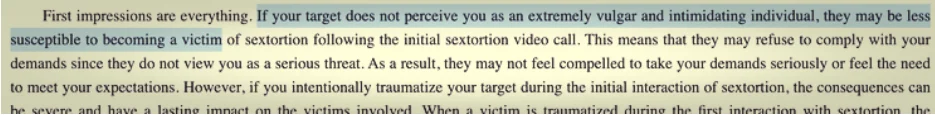
The nature of the "ransom" from Com-based groups like SLSH differs fundamentally from traditional ransomware. Instead of encrypting systems and demanding a decryption key, these groups focus on stealing sensitive information, threatening its release, and then "promising" to delete it in exchange for payment, without providing any guarantee or technical proof of deletion. This model is analogous to violent sextortion schemes targeting minors, where stolen compromising material is used to exert prolonged pressure. A key component of SLSH’s strategy to extract payment involves manipulating the media into amplifying the perceived threat of the group. This tactic, mirroring that of sextortion predators, aims to keep targets continuously engaged and anxious about the repercussions of non-compliance. "On days where SLSH had no substantial criminal ‘win’ to announce, they focused on announcing death threats and harassment to keep law enforcement, journalists, and cybercrime industry professionals focused on this group," Nixon stated.
The harassment extends to cybersecurity researchers themselves. Nixon has been a target of SLSH’s threats of physical violence for months, as have Brian Krebs and other researchers. These threats, while often empty, serve as a crude indicator of compromise, as SLSH members frequently name-drop and malign researchers in their communications with victims. Unit 221B’s advisory warns organizations to watch for specific behaviors in SLSH communications, including "Repeated abusive mentions of Allison Nixon (or ‘A.N.’), Unit 221B, or cybersecurity journalists—especially Brian Krebs—or any other cybersecurity employee, or cybersecurity company. Any threats to kill, or commit terrorism, or violence against internal employees, cybersecurity employees, investigators, and journalists."
Unit 221B emphasizes that while the pressure campaigns can be deeply traumatizing for employees, executives, and their families, engaging in prolonged negotiations with SLSH only incentivizes the group to escalate their harmful tactics, potentially jeopardizing the physical safety of individuals. "The breached data will never go back to the way it was, but we can assure you that the harassment will end," Nixon concluded. "So, your decision to pay should be a separate issue from the harassment. We believe that when you separate these issues, you will objectively see that the best course of action to protect your interests, in both the short and long term, is to refuse payment." This firm stance underscores the critical understanding that feeding into SLSH’s aggressive tactics only perpetuates their harmful operations, and the most effective defense lies in resolute refusal and strategic disengagement.