At the heart of the quantum threat lies the potential for advanced quantum computers to undermine the cryptographic foundations upon which Bitcoin and other cryptocurrencies are built. Owens elaborated on this theoretical risk, explaining that a sufficiently powerful quantum computer, leveraging algorithms like Shor’s algorithm, could theoretically derive a private key from its corresponding public key. This capability would be catastrophic, allowing an attacker to impersonate the legitimate owner of a Bitcoin address, forge a valid signature for a transaction, and ultimately steal funds without the owner’s consent. Such a scenario would represent a fundamental breach of trust and security, collapsing the integrity of the entire network.
However, Owens’s pivotal argument is that this existential threat is not uniformly distributed across all Bitcoin holdings. He firmly stated that "not all wallets are equally vulnerable to this risk." In a reassuring clarification for many investors, he added, "In fact, most wallets are not vulnerable today. Funds are at risk only when public keys are exposed on-chain." This distinction is critical and forms the bedrock of understanding Bitcoin’s current resilience against quantum attacks.
Owens identified two primary mechanisms through which Bitcoin wallets could become exposed to quantum risk: firstly, wallets whose public keys are already visible on the blockchain, and secondly, wallets whose public keys are revealed only at the moment of spending. This differentiation highlights varying degrees of vulnerability and the dynamic nature of the threat.
For wallets with already visible public keys, the risk is more immediate. This category primarily includes older transaction types, particularly those using Pay-to-Public-Key-Hash (P2PKH) addresses, which were prevalent in Bitcoin’s early days. In a P2PKH transaction, while the address itself is a hash of the public key, the full public key is typically revealed on the blockchain when the funds associated with that address are first spent. Once the public key is broadcast, it becomes permanently recorded on the immutable ledger. If a quantum computer were to exist today with the capability to perform Shor’s algorithm efficiently, it could theoretically target these already-exposed public keys, compute their corresponding private keys, and then drain the funds. This "quantum window" for these older transaction types effectively never closes once the public key is revealed, leaving funds perpetually exposed to a future quantum adversary. Estimating the exact percentage of UTXOs (unspent transaction outputs) that fall into this category is complex, but it represents a non-trivial portion of Bitcoin’s historical transaction set.
The second category, wallets whose public keys are revealed only at the time of spending, represents a significantly lower and more dynamic risk. Modern Bitcoin transaction types, such as those leveraging Segregated Witness (SegWit) like Pay-to-Witness-Public-Key-Hash (P2WPKH) or the even newer Taproot (P2TR), are designed to keep the public key hidden until a transaction is broadcast to the network. In these cases, the public key is not made visible on the blockchain until the user initiates a spend. This creates a much narrower "quantum window." For an attacker to exploit this, they would need to observe a pending transaction, rapidly apply a quantum algorithm to derive the private key from the newly revealed public key, and then broadcast a fraudulent transaction to steal the funds before the legitimate transaction is confirmed by miners and included in a block. This requires an almost instantaneous quantum computation and network propagation, making it a far more challenging attack vector than targeting already-exposed keys. The legitimate transaction typically propagates and gets confirmed within minutes, leaving a very small window for a quantum attacker to act.
The broader threat of quantum computing to cryptocurrencies has been a topic of fervent discussion for years, often framed as an inevitable "inflection point" that could redefine digital security. Theorists have long posited that advanced quantum computers could break the encryption securing sensitive data, reveal user keys, and compromise financial systems. However, critics argue that the immediacy of this threat is often overstated. Many experts contend that practical, fault-tolerant quantum computers capable of breaking Bitcoin’s specific cryptographic algorithms are still decades away from viability. Furthermore, they suggest that more centralized and higher-value targets, such as the vast networks of banking giants and national security systems, would likely be "cracked" by quantum adversaries long before the decentralized Bitcoin network becomes a primary target. These traditional systems often rely on similar cryptographic primitives and present a more concentrated reward for attackers.

Countering perceptions that Bitcoin Core developers might be "ignoring and gatekeeping" quantum-related proposals, such as the soft fork BIP 360, Owens’s research found compelling evidence to the contrary. He specifically noted that "the pace of proposals has accelerated meaningfully since late 2025," indicating a proactive and engaged community. This refutes any notion of complacency, highlighting a robust and ongoing effort within the development ecosystem. "Contrary to some public criticism, our review found substantial developer work addressing the question of quantum vulnerabilities and mitigations," Owens stated. He underscored the depth of this engagement, asserting that "The ecosystem now has a concrete and maturing set of proposals spanning the full problem surface. These proposals are not theoretical. They are being actively developed, reviewed, and debated by some of the most experienced contributors in the Bitcoin ecosystem."
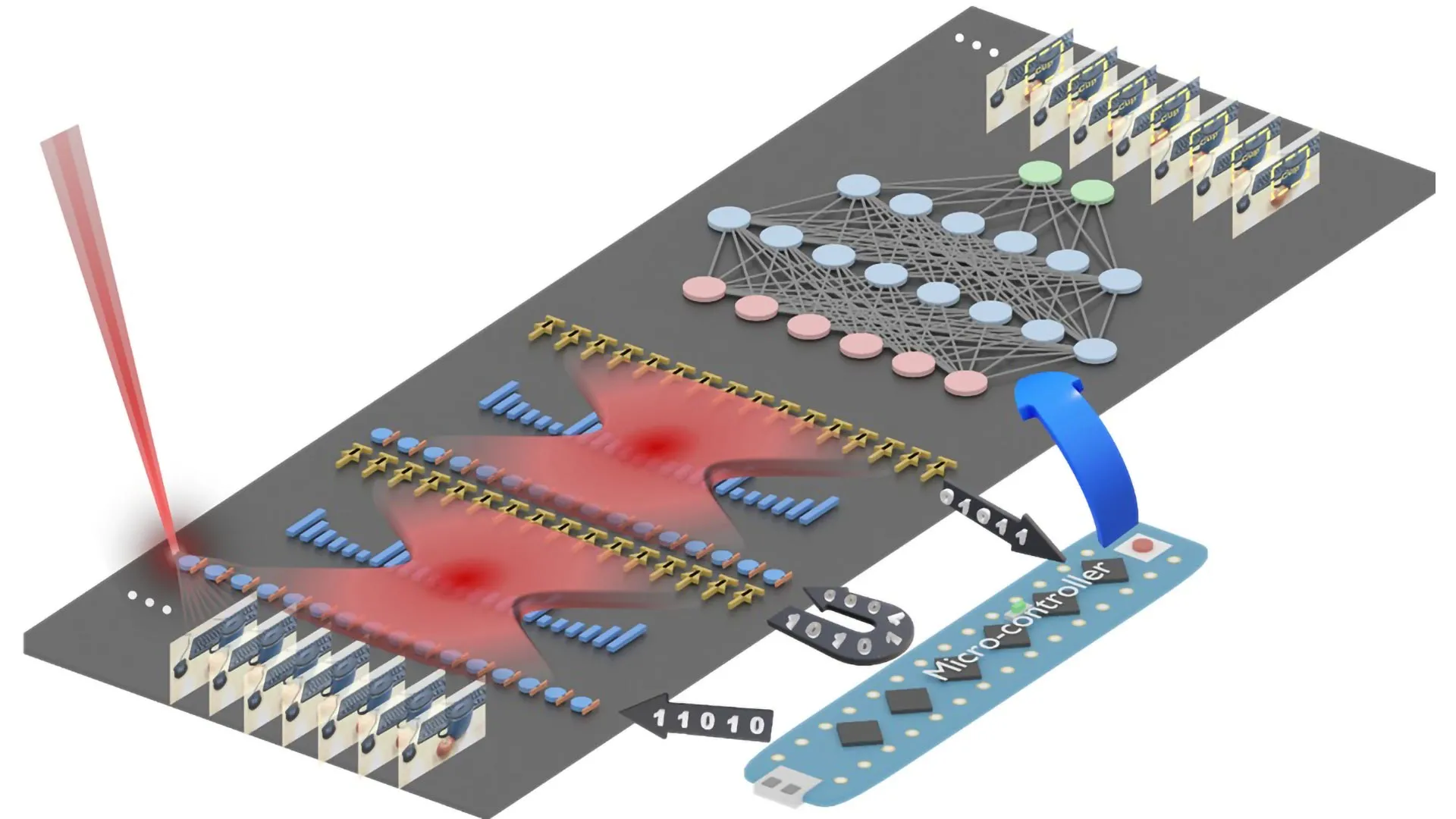
These efforts include exploring various post-quantum cryptographic schemes. The challenge lies in replacing Bitcoin’s current Elliptic Curve Digital Signature Algorithm (ECDSA) with quantum-resistant alternatives, such as hash-based signatures (e.g., Lamport or Merkle signatures) or lattice-based cryptography. Hash-based signatures, while theoretically quantum-resistant, often come with trade-offs, such as larger signature sizes and the potential for statefulness (meaning a private key can only be used a limited number of times). Developers are working to find solutions that minimize these impacts while maintaining Bitcoin’s core principles of security, decentralization, and scalability.
Other industry participants have also contributed to the discourse on potential solutions. Prominent Bitcoin analyst Willy Woo, for instance, suggested last November that holding Bitcoin in a SegWit wallet for several years could help mitigate quantum-related risks. His reasoning aligns with Owens’s analysis: SegWit transactions delay the exposure of public keys until the moment of spending, thereby shrinking the "quantum window" during which an attacker could potentially act. By keeping funds in SegWit addresses and avoiding spending them until absolutely necessary, investors can significantly reduce the time their public keys are vulnerable on the blockchain, buying crucial time for the network to implement comprehensive post-quantum upgrades.
Despite the concerted efforts of developers, the decentralized nature of Bitcoin presents unique governance challenges for implementing any universal post-quantum solution. Owens acknowledged this inherent difficulty, stating, "Bitcoin has no CEO, no board, and no central authority that can mandate a software update." Any significant change to the protocol, such as integrating new cryptographic algorithms, requires widespread consensus among miners, node operators, developers, and users. This process, typically achieved through a soft fork, can be protracted and contentious, as evidenced by past debates over block size or SegWit activation.
However, Owens also highlighted a crucial factor that distinguishes the quantum threat from previous internal disputes over Bitcoin’s economic direction: its external, technical, and universal impact. "The nature of this particular threat — external, technical, and universal in its impact — aligns incentives in a way that past disputes over Bitcoin’s economic direction did not," he explained. Unlike debates about block size or transaction fees, which might pit different factions against each other, the quantum threat imperils the very existence and security of all Bitcoin holdings. This shared existential threat creates a powerful unifying incentive: "Every honest participant in the network, from miners to holders to exchanges, has a direct financial interest in the network’s continued security." This alignment of interests suggests that when a viable, well-vetted post-quantum solution emerges, the community will be strongly motivated to adopt it, overcoming potential governance hurdles more readily than in other instances.
For investors grappling with the perceived long-term risk of quantum computing, Owens offered a straightforward and reassuring takeaway: "For investors, the key takeaway is straightforward: the risk is real but recognized, and the people best positioned to address it are working on it." This encapsulates the current state of affairs, emphasizing that while the threat is not to be dismissed, it is neither ignored nor insurmountable. The Bitcoin ecosystem, renowned for its resilience and adaptability, is actively preparing for a post-quantum future. The proactive research, development, and vigorous debate within the developer community demonstrate a clear commitment to safeguarding the network’s long-term security. While a fully functional, attack-capable quantum computer remains a theoretical construct for now, the ongoing work ensures that Bitcoin is not merely waiting for the future but is actively building a more quantum-resistant foundation. This forward-looking approach underscores the robustness and self-correcting nature of the world’s leading cryptocurrency, aiming to ensure its integrity far into the quantum age.