Direct navigation, the practice of typing a domain name directly into a web browser, has become a significantly more perilous endeavor. Parked domains, typically comprising expired or dormant website addresses, or common misspellings of popular sites (known as typosquatting), are now overwhelmingly configured to ensnare users. Previously, encountering a parked domain meant a small chance of being led to a harmful destination. However, Infoblox’s recent extensive experiments paint a starkly different picture.
"In large scale experiments, we found that over 90% of the time, visitors to a parked domain would be directed to illegal content, scams, scareware and anti-virus software subscriptions, or malware, as the ‘click’ was sold from the parking company to advertisers, who often resold that traffic to yet another party," stated Infoblox researchers in their latest paper. This indicates a sophisticated, multi-layered ecosystem designed to monetize user missteps.
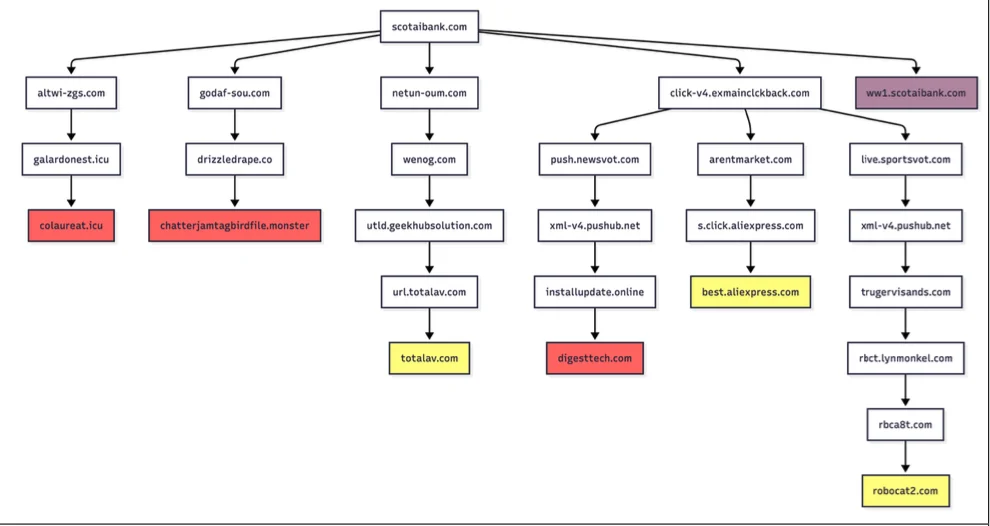
The research highlights a critical vulnerability: the deceptive practices employed by malicious actors who register domains that are mere characters away from legitimate and highly trafficked websites. For instance, customers of Scotiabank, upon mistyping the domain as "scotaibank[.]com," might encounter a benign parking page if they are using a Virtual Private Network (VPN). However, if they access the misspelled domain from a residential IP address, whether on a desktop or mobile device, they are immediately redirected to sites peddling scams, malware, or other unwanted content. This redirection occurs instantaneously, without any user interaction beyond the initial navigation.
One particularly alarming case identified by Infoblox involves a domain holder who manages a portfolio of nearly 3,000 lookalike domains. This portfolio includes domains like "gmai[.]com," which has been found to operate its own mail server. Consequently, emails intended for legitimate Gmail users that are mistakenly sent to "gmai[.]com" do not simply bounce back; they are intercepted by these scammers. The report further details how this specific domain has been instrumental in recent business email compromise (BEC) campaigns, often employing lures that suggest a failed payment and attach trojan malware.
The owner of "scotaibank[.]com" is linked to a common Domain Name System (DNS) server, "torresdns[.]com," and has established typosquatting domains targeting a wide array of popular internet destinations. This list includes major platforms such as Craigslist, YouTube, Google, Wikipedia, Netflix, TripAdvisor, Yahoo, eBay, and Microsoft. Infoblox has provided a de-fanged list of these typosquatting domains, where the periods have been replaced with commas to prevent accidental clicks.
David Brunsdon, a threat researcher at Infoblox, elaborated on the sophisticated redirection mechanisms employed. He explained that parked pages often initiate a chain of redirects. During this process, the visitor’s system is profiled through IP geolocation, device fingerprinting, and cookies to determine the most effective malicious destination. "It was often a chain of redirects – one or two domains outside the parking company – before threat arrives," Brunsdon noted. "Each time in the handoff the device is profiled again and again, before being passed off to a malicious domain or else a decoy page like Amazon.com or Alibaba.com if they decide it’s not worth targeting."
Brunsdon also pointed out a disconnect between the claims of domain parking services and the reality observed. While these services assert that the search results displayed on parked pages are relevant to the parked domains, Infoblox’s testing revealed that almost none of the displayed content bore any relation to the lookalike domain names they examined.
Another threat actor identified by Infoblox operates "domaincntrol[.]com," a domain that subtly differs from GoDaddy’s legitimate name servers by a single character. This actor has historically exploited typos in DNS configurations to direct users to malicious websites. However, Infoblox’s recent findings indicate a more targeted approach: the malicious redirect now only occurs when the query for the misconfigured domain originates from a visitor using Cloudflare’s DNS resolvers (1.1.1.1). All other visitors are presented with a page that refuses to load, suggesting a potential cat-and-mouse game with DNS providers.
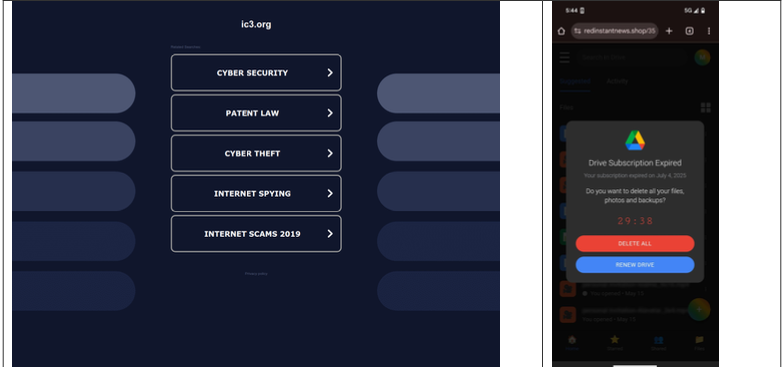
The pervasiveness of these malicious tactics extends even to variations of well-known government domains. In a concerning example, a researcher attempting to report a crime to the FBI’s Internet Crime Complaint Center (IC3) accidentally navigated to "ic3[.]org" instead of the correct "ic3[.]gov." Their device was swiftly redirected to a deceptive "Drive Subscription Expired" page. The report emphasizes that this could have easily resulted in the delivery of information-stealing malware or trojans, highlighting the unpredictable and dangerous nature of these redirects.
Crucially, the Infoblox report stresses that the malicious activity observed is not attributed to any single, identifiable perpetrator. The domain parking or advertising platforms themselves were not directly implicated in the malvertising documented. However, the study concludes that despite claims of working only with reputable advertisers, traffic to these parked domains was frequently funneled through affiliate networks, which then resold the traffic. This complex chain often meant that the final advertiser had no direct business relationship with the original parking companies, obscuring accountability.
Infoblox also raised concerns that recent policy adjustments by Google may have inadvertently amplified the risks associated with direct search abuse. According to Brunsdon, Google AdSense previously allowed ads to be placed on parked pages by default. However, in early 2025, Google implemented a setting that requires advertisers to actively opt-in to present their ads on parked domains. This change, while seemingly aimed at user protection, could have the unintended consequence of pushing malicious actors to seek out less regulated advertising channels or exploit the remaining vulnerabilities in the system. The shift necessitates that advertisers now must intentionally enable parked domain placements, rather than having to opt out, potentially making it easier for malicious actors to leverage these spaces if they can find willing advertisers or alternative ad networks.