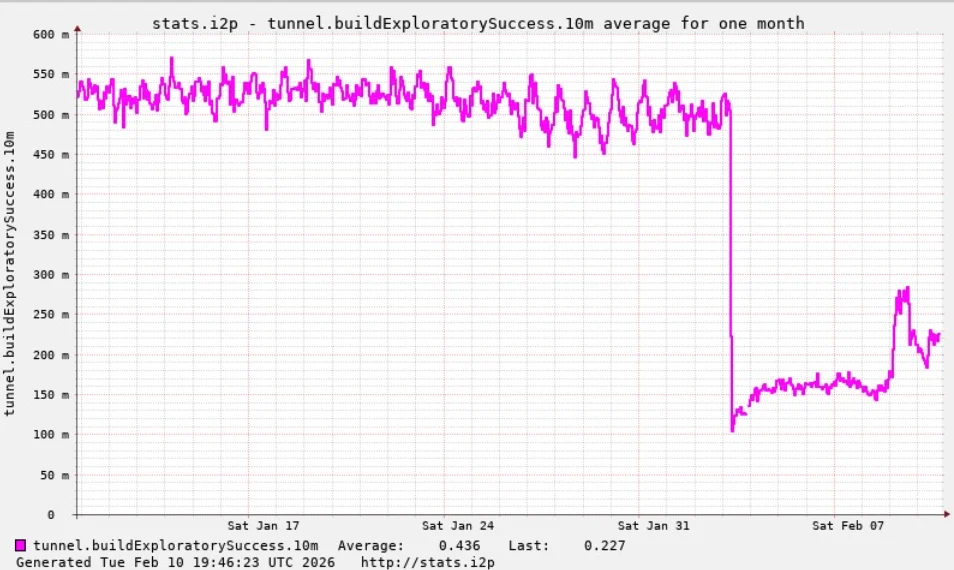
For the past week, the massive Internet of Things (IoT) botnet known as Kimwolf has been severely disrupting The Invisible Internet Project (I2P), a decentralized, encrypted communications network designed to anonymize and secure online communications. I2P users began reporting significant disruptions in the network around the same time the Kimwolf botmasters started relying on it as a refuge to evade aggressive takedown attempts against the botnet’s primary control servers. This coordinated effort by Kimwolf to leverage I2P has resulted in what security researchers are identifying as a sophisticated Sybil attack, overwhelming the privacy-focused network and impacting its functionality.
Kimwolf, a formidable botnet that first surfaced in late 2025, rapidly infected millions of poorly secured IoT devices. These compromised devices, ranging from ubiquitous TV streaming boxes and digital picture frames to home routers, were transformed into unwilling relays for malicious traffic. The botnet has been instrumental in launching abnormally large distributed denial-of-service (DDoS) attacks, as documented in previous reports of its disruptive capabilities. Its emergence marked a significant escalation in the threat posed by compromised IoT devices, highlighting the vulnerabilities inherent in the burgeoning connected ecosystem.
I2P, by its design, is a decentralized, privacy-focused network that empowers individuals to communicate and share information anonymously. Its architecture relies on routing data through multiple encrypted layers across a network of volunteer-operated nodes. This intricate process effectively conceals both the sender’s and the receiver’s locations, creating a secure, censorship-resistant environment suitable for private websites, messaging, and data sharing. The network’s strength lies in its distributed nature and the collective participation of its users.
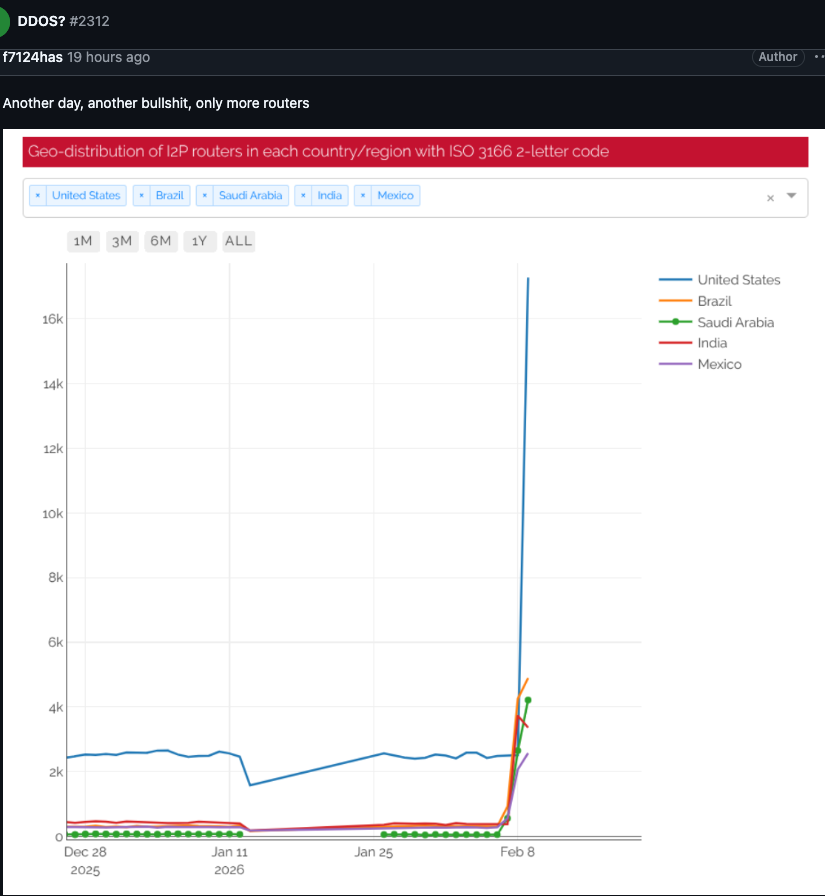
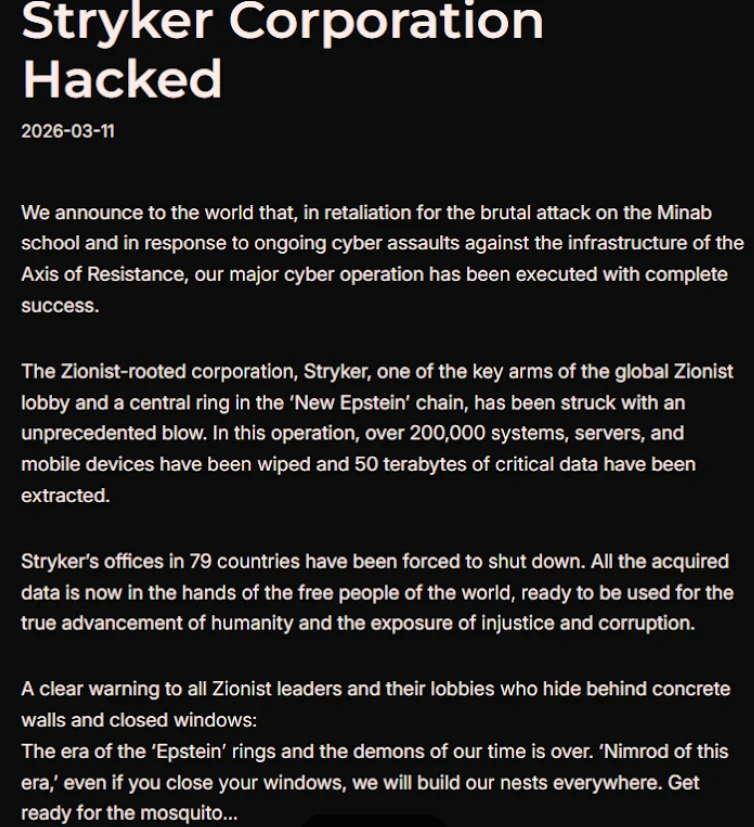
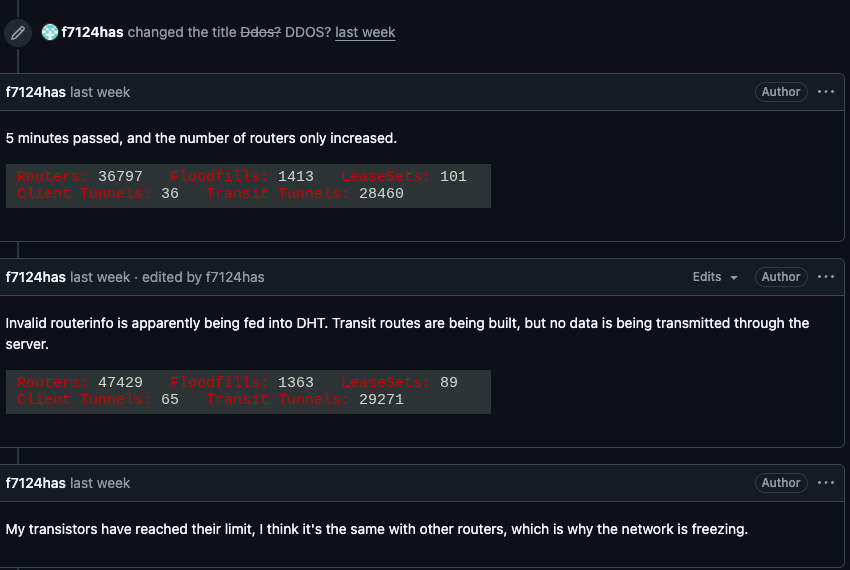
The cascade of issues within I2P began on February 3rd, when users started voicing their concerns on the organization’s GitHub page. They reported a sudden influx of tens of thousands of new routers overwhelming the network, rendering it impossible for existing users to establish connections with legitimate nodes. The reports detailed a rapidly increasing number of new systems joining the network that were demonstrably incapable of transmitting data. This mass infiltration of potentially compromised or manipulated systems, originating from the Kimwolf botnet, effectively crippled the network’s ability to function, preventing users from accessing its services.
One I2P user, in a desperate attempt to understand the cause of the outages, posed the question of whether the network was under attack. The response from another user was stark: "Looks like it. My physical router freezes when the number of connections exceeds 60,000." This observation underscored the severity of the network congestion and the direct impact on individual user hardware, suggesting the scale of the intrusion was beyond what the network was designed to handle.
Compounding the evidence of an attack, on the very same day I2P users began experiencing outages, the individuals in control of the Kimwolf botnet posted a chilling message to their Discord channel. They openly admitted to accidentally disrupting I2P after attempting to integrate approximately 700,000 Kimwolf-infected bots as new nodes within the I2P network. This confession, shared on a platform seemingly monitored by security researchers, confirmed the direct link between Kimwolf’s actions and the I2P network’s degradation.
While Kimwolf is primarily recognized as a potent tool for launching large-scale DDoS attacks, the disruptions experienced by I2P this past week are a distinct form of threat. These outages are attributed to what is known as a Sybil attack, a malicious tactic specifically targeting peer-to-peer networks. In a Sybil attack, a single entity aims to disrupt the system by creating, controlling, and operating a vast number of fake, pseudonymous identities. By flooding the network with these artificial nodes, the attacker can gain disproportionate influence and undermine the network’s integrity.
The sheer volume of Kimwolf-infected routers that attempted to join I2P this past week was many times the network’s normal operational size. I2P’s Wikipedia page indicates that the network typically comprises around 55,000 computers distributed globally, with each participant functioning as both a router and a client. However, Lance James, founder of the New York City-based cybersecurity consultancy Unit 221B and the original founder of I2P, provided a more current and realistic assessment. James stated that the entire I2P network currently consists of between 15,000 and 20,000 devices on any given day, making the influx of hundreds of thousands of Kimwolf nodes an overwhelming force.
Benjamin Brundage, founder of Synthient, a startup specializing in tracking proxy services and the first to document Kimwolf’s unique spreading techniques, elaborated on the motivations behind this aggressive maneuver. Brundage explained that the operators of Kimwolf have been actively attempting to construct a command and control (C2) network that is exceptionally difficult to dismantle. This endeavor is a direct response to the concerted efforts of security companies and network operators working collaboratively to combat the botnet’s proliferation.
Brundage further revealed that the Kimwolf controllers have been experimenting with utilizing I2P and a similar anonymity network, Tor, as backup C2 networks. While there have been no recent reports of widespread disruptions within the Tor network, this experimental phase with I2P has had tangible, negative consequences. "I don’t think their goal is to take I2P down," Brundage stated. "It’s more that they’re looking for an alternative to keep the botnet stable in the face of takedown attempts." This strategic shift highlights a growing trend of botnets seeking to establish resilient infrastructure in the face of persistent security countermeasures.
The Kimwolf botnet had previously presented significant challenges to major internet infrastructure providers. Late last year, it instructed millions of its infected devices to utilize Cloudflare’s domain name system (DNS) settings. This manipulation caused control domains associated with Kimwolf to repeatedly usurp the rankings of prominent technology giants such as Amazon, Apple, Google, and Microsoft in Cloudflare’s public metrics for the most frequently requested websites. This demonstrated Kimwolf’s ability to distort network traffic patterns and gain visibility through legitimate infrastructure.
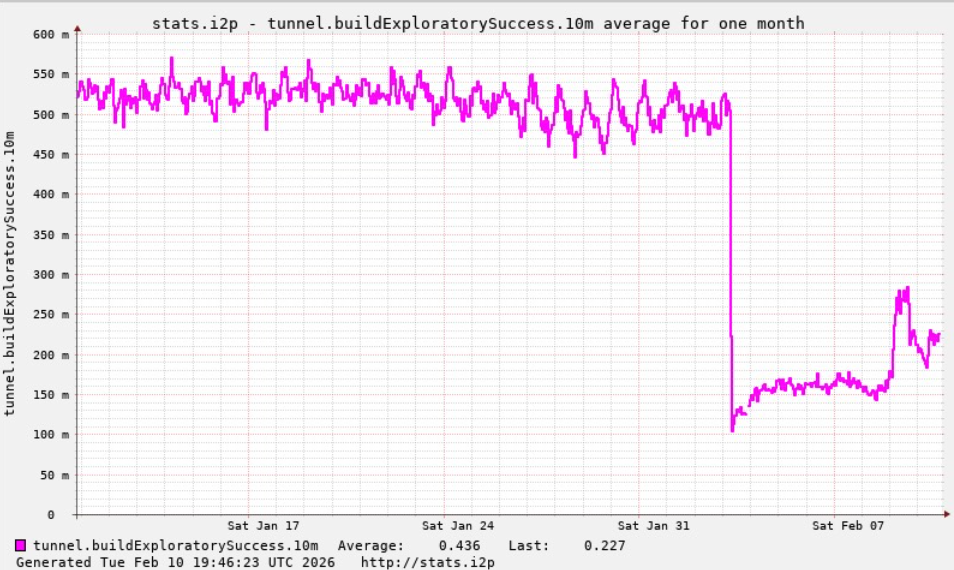
Regarding the current state of the I2P network, Lance James reported that it is still operating at approximately half of its normal capacity. However, a new release is currently being rolled out, which is anticipated to introduce stability improvements over the coming week for affected users. This indicates that the I2P community is actively working to mitigate the damage and restore full functionality.
On a more positive note for the cybersecurity landscape, Brundage shared that Kimwolf’s overlords appear to have recently alienated some of their more competent developers and operators. This internal friction has seemingly led to a critical error, a "rookie mistake" as Brundage described it, during the past week’s attempted infiltration of I2P. This misstep resulted in a significant drop in the botnet’s overall numbers, with more than 600,000 infected systems being lost. "It seems like they’re just testing stuff, like running experiments in production," Brundage observed. "But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing." This suggests a potential period of disarray within the Kimwolf operation, offering a window of opportunity for further disruption of their activities.