The clandestine world of anonymized communication and sophisticated botnet operations has collided, with the massive Internet of Things (IoT) botnet known as Kimwolf severely disrupting The Invisible Internet Project (I2P), a decentralized, encrypted network designed for privacy and security. For the past week, users of I2P have reported significant outages and performance degradation, coinciding with the Kimwolf botmasters’ attempts to leverage I2P as a fallback command and control infrastructure to evade ongoing takedown efforts.
Kimwolf, a formidable botnet that emerged in late 2025, rapidly infected millions of insecure IoT devices, transforming them into unwitting participants in a distributed denial-of-service (DDoS) attack machine. These compromised devices, ranging from smart TVs and digital picture frames to routers, have been instrumental in launching abnormally large DDoS attacks, as previously documented in reports detailing the botnet’s impact. The botnet’s success stems from its ability to exploit poorly secured IoT devices, turning them into a vast, distributed proxy network.
I2P, on the other hand, represents a cornerstone of the decentralized internet, offering users a robust platform for anonymous communication and data sharing. Its core functionality relies on a multi-layered encryption system that routes traffic through a network of volunteer-operated nodes. This intricate routing process effectively conceals the geographical locations of both the sender and the receiver, creating a secure and censorship-resistant environment for private websites, messaging, and file sharing. The I2P website elaborates on this architecture, emphasizing its design for robust privacy and freedom from external interference.
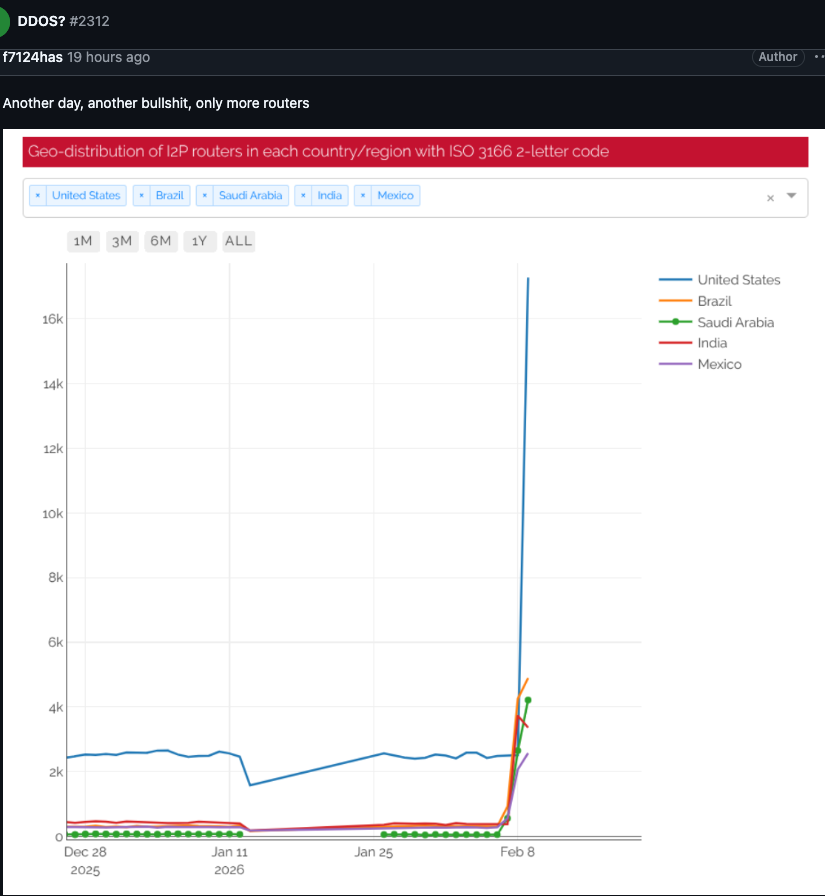
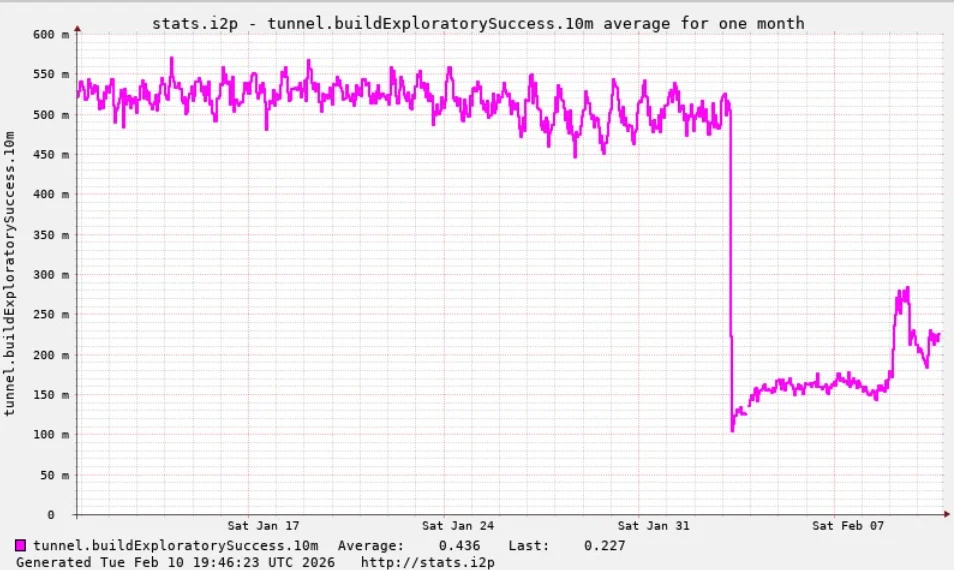
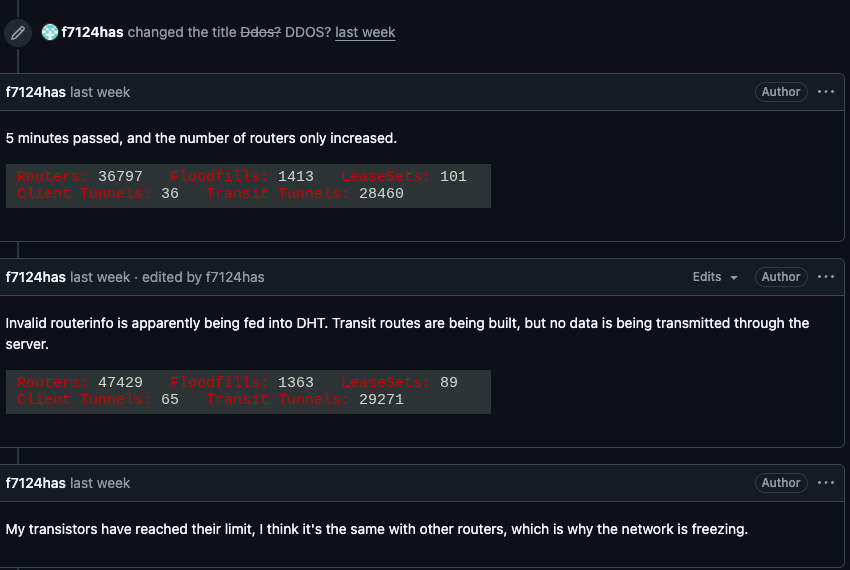
The disruption within I2P began to manifest around February 3rd, when I2P users started voicing their concerns on the project’s GitHub page. Reports flooded in detailing an overwhelming influx of tens of thousands of new routers, which were effectively preventing legitimate users from establishing connections with established nodes. Users described a rapid increase in new systems joining the network, none of which were capable of transmitting data, leading to a complete breakdown in connectivity for many. An accompanying image from the GitHub thread visually depicted these user complaints, highlighting the sudden and dramatic surge in network activity.
The situation escalated as users struggled to maintain connections. One I2P user explicitly inquired if the network was under attack, receiving a grim confirmation: "Looks like it. My physical router freezes when the number of connections exceeds 60,000." This sentiment was echoed by others experiencing similar performance issues, indicating a coordinated and overwhelming assault on the network’s capacity.
Adding a layer of transparency, or perhaps a stark display of hubris, the individuals controlling the Kimwolf botnet themselves posted on their Discord channel, admitting to the disruption. They confessed to accidentally overwhelming I2P after attempting to integrate approximately 700,000 Kimwolf-infected bots as nodes within the network. This admission, captured in a screenshot, directly links the Kimwolf operation to the I2P outages, revealing a deliberate, albeit perhaps poorly executed, strategic move.
While Kimwolf is primarily known for its prowess in launching large-scale DDoS attacks, the current disruption falls under the category of a Sybil attack. This type of attack, prevalent in peer-to-peer networks, involves a single malicious entity creating and controlling a vast number of pseudonymous identities to overwhelm and destabilize the network. The sheer volume of Kimwolf-infected routers attempting to join I2P far surpassed the network’s normal operational scale. According to I2P’s Wikipedia entry, the network typically comprises around 55,000 computers worldwide, with each participant acting as both a router and a client.
However, Lance James, founder of the cybersecurity consultancy Unit 221B and the original founder of I2P, provided a more nuanced perspective on the network’s current size. James estimates that the active I2P network consists of a significantly smaller number, between 15,000 and 20,000 devices on any given day. This smaller, more intimate network size makes it even more susceptible to the overwhelming force of hundreds of thousands of new, malicious nodes. A graph shared by an I2P user on February 10th powerfully illustrated this point, showcasing a dramatic surge of tens of thousands of routers, predominantly from the United States, attempting to join the network simultaneously.
Benjamin Brundage, founder of Synthient, a startup specializing in tracking proxy services and an early documenter of Kimwolf’s unique propagation methods, shed light on the botnet operators’ motivations. Brundage explained that the Kimwolf operators are actively working to establish a resilient command and control (C2) infrastructure that is difficult for security firms and network operators to dismantle. Their experimentation with I2P and the Tor anonymity network represents a strategic effort to create a decentralized, censorship-resistant C2 system. While Tor has not reported similar widespread disruptions, Brundage suggests that Kimwolf’s operators view these networks as vital for maintaining the botnet’s stability amidst escalating takedown attempts.
"I don’t think their goal is to take I2P down," Brundage stated, emphasizing that the primary objective is to secure their operational continuity. "It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts."
This is not the first instance of Kimwolf causing widespread network instability. Late last year, the botnet created significant challenges for Cloudflare by directing millions of infected devices to utilize Cloudflare’s DNS settings. This maneuver led to control domains associated with Kimwolf repeatedly outranking major tech giants like Amazon, Apple, Google, and Microsoft in Cloudflare’s public rankings of the most frequently requested websites, highlighting the botnet’s ability to manipulate internet traffic flows.
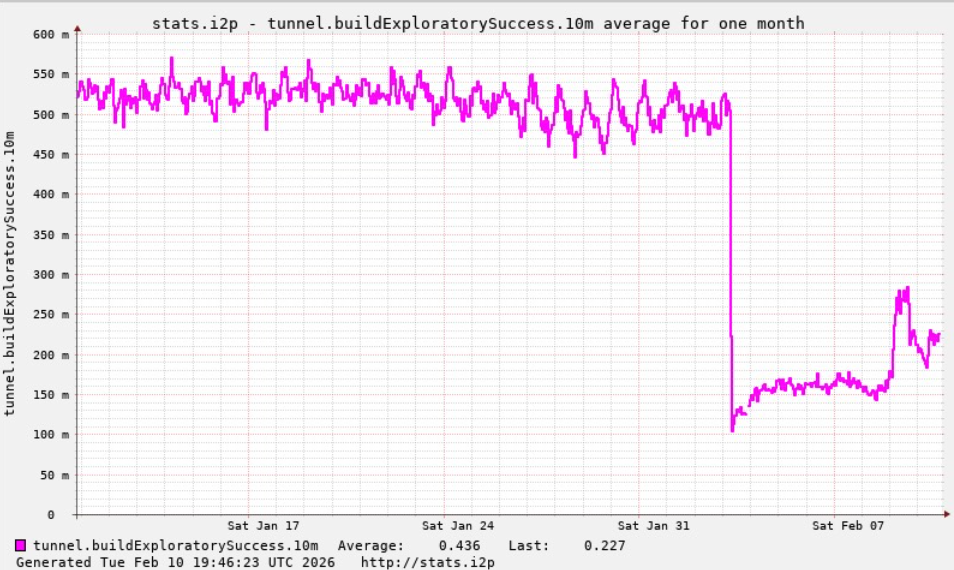
Despite the current turmoil, James indicated that the I2P network is gradually recovering, operating at approximately half of its normal capacity. A new release is reportedly being deployed, which is expected to introduce stability improvements over the coming week, offering some relief to affected users.
On a more optimistic note for the cybersecurity community, Brundage observed that the Kimwolf operation appears to be experiencing internal strife. He suggested that some of the botnet’s more competent developers and operators may have recently departed, leading to amateurish mistakes like the I2P incident. This "rookie mistake" has reportedly resulted in a significant decline in the botnet’s overall size, with over 600,000 infected systems being lost.
"It seems like they’re just testing stuff, like running experiments in production," Brundage remarked, highlighting a chaotic and potentially unsustainable operational approach. "But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing." This internal disarray, coupled with the exposed vulnerability of their C2 infrastructure, suggests that while Kimwolf remains a threat, its operators may be struggling to maintain their control and operational efficiency. The I2P incident serves as a stark reminder of the interconnectedness of the digital landscape and the far-reaching consequences of sophisticated cyberattacks.