For the past week, the sprawling and increasingly audacious Internet of Things (IoT) botnet known as Kimwolf has unleashed a crippling assault on The Invisible Internet Project (I2P), a vital decentralized, encrypted communications network designed to provide anonymity and robust security for online interactions. I2P users began reporting severe disruptions and widespread outages across the network concurrently with the Kimwolf botmasters’ desperate efforts to leverage I2P as a fallback command and control infrastructure, a move that appears to have been driven by mounting takedown attempts against their existing control servers.
Kimwolf, a formidable botnet that first emerged in late 2025, has rapidly infected millions of poorly secured Internet of Things devices, transforming them into unwilling participants in its malicious operations. These compromised devices, ranging from ubiquitous TV streaming boxes and digital picture frames to home and office routers, have been co-opted as relays for an unprecedented volume of malicious traffic, including distributed denial-of-service (DDoS) attacks of abnormally large scale, as previously documented by KrebsOnSecurity. The botnet’s ability to scale and its reliance on the vast, often overlooked, IoT ecosystem have made it a persistent and evolving threat.
I2P, by its very nature, is designed to offer a sanctuary for privacy-conscious individuals and organizations. It functions as a decentralized, privacy-focused network that empowers users to communicate and share information with a high degree of anonymity. The core principle of I2P lies in its sophisticated routing mechanism. As explained on the I2P website, data is meticulously routed through multiple encrypted layers across a global network of volunteer-operated nodes. This intricate process effectively obscures both the sender’s and the receiver’s geographical locations, creating a secure and censorship-resistant environment ideal for private websites, secure messaging, and clandestine data sharing.
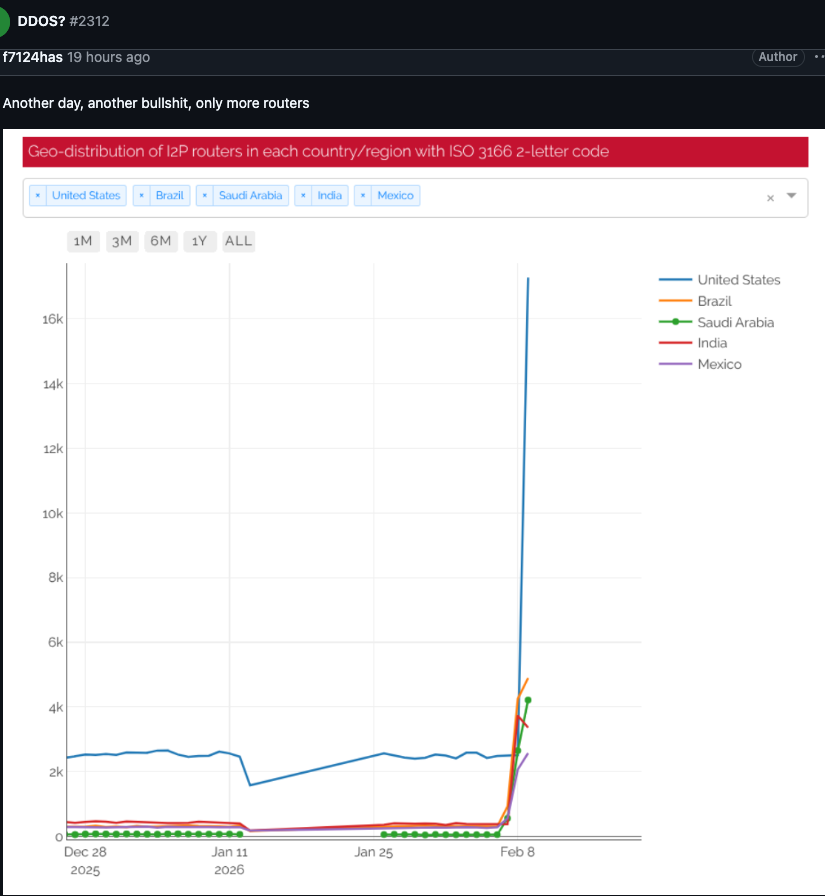
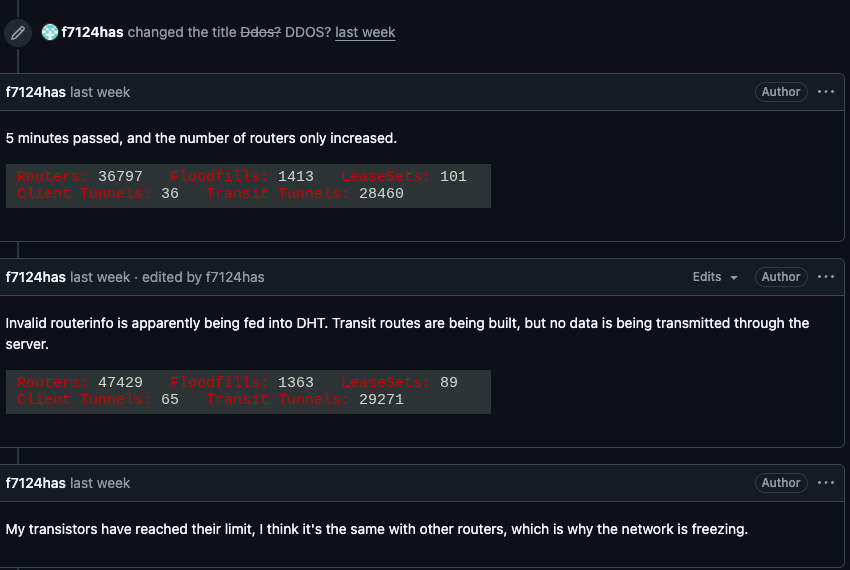
The first clear indications of the Kimwolf intrusion into I2P surfaced on February 3rd. I2P users took to the organization’s GitHub page to voice their growing alarm and frustration. They reported a sudden and overwhelming influx of tens of thousands of new routers, all seemingly attempting to join the network simultaneously. This deluge of new, malformed connections effectively choked the network, preventing legitimate users from establishing communication with established, healthy nodes. The reports detailed a rapidly escalating number of new systems joining the network, none of which were capable of transmitting data, leading to a complete breakdown in connectivity for the vast majority of users. The sheer volume of these illegitimate connections overwhelmed the network’s capacity to the point of complete collapse for many.
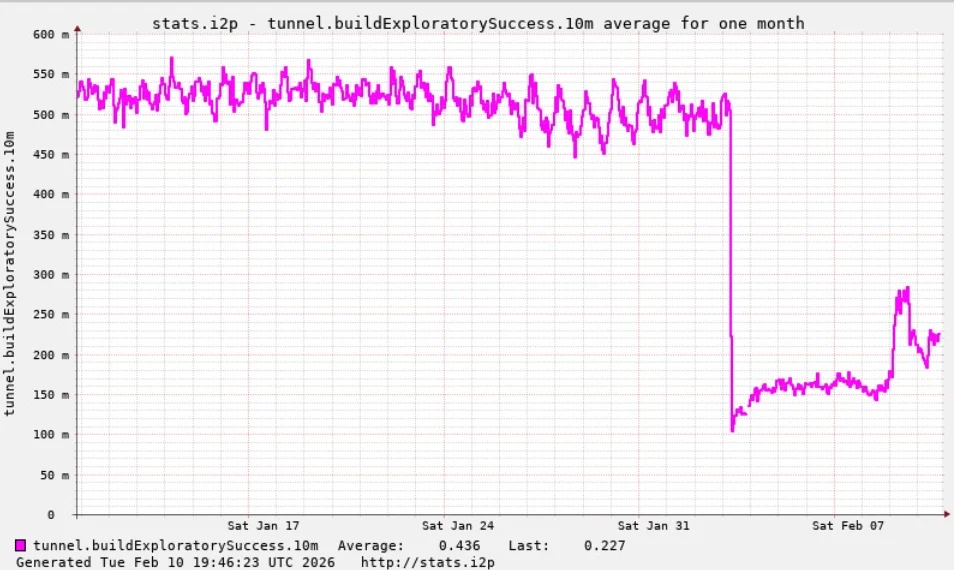
One distressed I2P user, grappling with the cascading failures, posed a critical question: "Looks like it. My physical router freezes when the number of connections exceeds 60,000." This sentiment was echoed by numerous other users who experienced similar performance degradation and complete connection failures, painting a grim picture of a network under siege. The subsequent analysis by I2P developers, visualized in accompanying graphs, starkly illustrated a dramatic and precipitous drop in successful connections on the I2P network, occurring precisely during the period when the Kimwolf botnet began its aggressive attempt to integrate itself as fallback communication channels.
The timing of these disruptions was not coincidental. On the very same day that I2P users began to experience widespread outages, the individuals orchestrating the Kimwolf botnet openly acknowledged their role in the chaos. In a post made to their private Discord channel, they confessed to having "accidentally" disrupted I2P. Their admission detailed a plan to integrate a staggering 700,000 Kimwolf-infected bots as nodes within the I2P network. This revelation provided irrefutable evidence that the crippling of I2P was a direct consequence of the botnet operators’ misguided attempt to expand their infrastructure.
While Kimwolf has gained notoriety as a potent instrument for launching disruptive DDoS attacks, the outages experienced by I2P this past week stem from a different, yet equally insidious, form of cyber warfare. This tactic is known as a "Sybil attack," a well-documented threat in peer-to-peer networks. In a Sybil attack, a single malicious entity can effectively subvert and disrupt a decentralized system by creating, controlling, and operating an overwhelming number of fake, pseudonymous identities. By flooding the network with these fabricated nodes, the attacker can manipulate its behavior, degrade its performance, and ultimately render it unusable for legitimate participants.
The sheer scale of the Kimwolf-infected routers attempting to join I2P far exceeded the network’s normal operational capacity. According to Wikipedia, the I2P network typically comprises approximately 55,000 computers distributed globally, with each participant functioning as both a router, relaying traffic, and a client. However, Lance James, the founder of the New York City-based cybersecurity consultancy Unit 221B and, notably, the original founder of I2P, provided a more current and sobering assessment. James indicated that the entire I2P network, on any given day, consists of between a mere 15,000 and 20,000 active devices. This stark contrast highlights the overwhelming magnitude of the Kimwolf intrusion, with the botnet attempting to inject a volume of nodes that dwarfed the network’s actual operational size by orders of magnitude. A graph shared by an I2P user on February 10th powerfully illustrates this phenomenon, depicting tens of thousands of routers, predominantly originating from the United States, suddenly attempting to join the network.
Benjamin Brundage, founder of Synthient, a startup specializing in tracking proxy services and the first to document Kimwolf’s unique and aggressive spreading techniques, shed further light on the botnet operators’ motivations. Brundage explained that the individuals behind Kimwolf have been actively attempting to construct a command and control (C2) network that is exceptionally resilient and difficult to dismantle. This strategic imperative arises from the ongoing, collaborative efforts of security companies and network operators worldwide to combat the botnet’s relentless spread. The operators’ objective is to create a C2 infrastructure that cannot be easily taken offline by conventional takedown operations.
Brundage further elaborated that the Kimwolf operators have been experimenting with utilizing I2P and a similar anonymity network, Tor, as potential backup C2 networks. While there have been no widespread reports of disruptions within the Tor network recently, the exploration of these privacy-enhancing technologies by malicious actors underscores a significant shift in their operational tactics. "I don’t think their goal is to take I2P down," Brundage stated, emphasizing the nuanced nature of the attack. "It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts."
The Kimwolf botnet has previously demonstrated its disruptive capabilities in other ways, creating significant challenges for major internet infrastructure providers. Late last year, Kimwolf orchestrated a complex maneuver that instructed millions of infected devices to utilize Cloudflare’s domain name system (DNS) settings. This tactic caused control domains associated with Kimwolf to repeatedly usurp the rankings of established internet giants like Amazon, Apple, Google, and Microsoft in Cloudflare’s public metrics of the most frequently requested websites. This incident highlighted the botnet’s ability to manipulate internet traffic at a fundamental level, impacting even the most robust infrastructure.
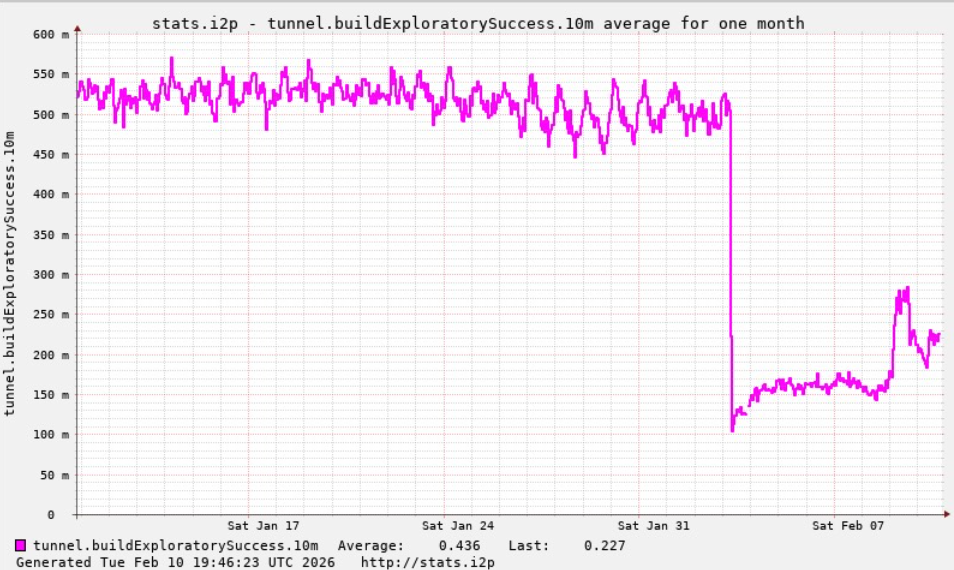
Despite the significant disruption, there is a glimmer of hope for the I2P community. Lance James reported that the I2P network is gradually recovering, currently operating at approximately half of its normal capacity. A new release is in the process of being deployed, which is anticipated to introduce stability improvements over the coming week, potentially mitigating the lingering effects of the Kimwolf assault.
On a more positive note for the broader cybersecurity landscape, Brundage revealed that Kimwolf’s overlords appear to have recently alienated some of their more competent developers and operators. This internal friction has seemingly led to a critical "rookie mistake" this past week, directly contributing to a significant drop in the botnet’s overall infected system count, exceeding 600,000 compromised devices. "It seems like they’re just testing stuff, like running experiments in production," Brundage commented, suggesting a lack of mature operational discipline within the botnet’s leadership. "But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing." This internal disarray within the Kimwolf operation may provide a crucial window of opportunity for law enforcement and cybersecurity researchers to further disrupt and dismantle the botnet.