A sophisticated and rapidly expanding Internet-of-Things (IoT) botnet, dubbed "Kimwolf," has infiltrated over two million devices, turning them into unwitting participants in massive distributed denial-of-service (DDoS) attacks and conduits for a wide array of malicious internet traffic. What makes Kimwolf a particularly alarming threat to organizations is its insidious ability to scan the local networks of compromised systems, actively seeking out and infecting other vulnerable IoT devices. Recent research has uncovered a deeply concerning prevalence of Kimwolf within the networks of both government agencies and major corporations, highlighting a significant breach in organizational security.
The alarming growth of Kimwolf in the latter months of 2025 can be attributed to its exploitation of "residential proxy" services. These services, which are marketed to users seeking to anonymize and geographically localize their web traffic, often allow customers to route their internet activity through devices located anywhere in the world. The malware responsible for transforming these devices into proxy nodes is frequently bundled discreetly with seemingly innocuous mobile applications and games. Once installed, it forces the infected device to relay various forms of malicious and abusive internet traffic, including ad fraud, account takeover attempts, and large-scale content scraping.
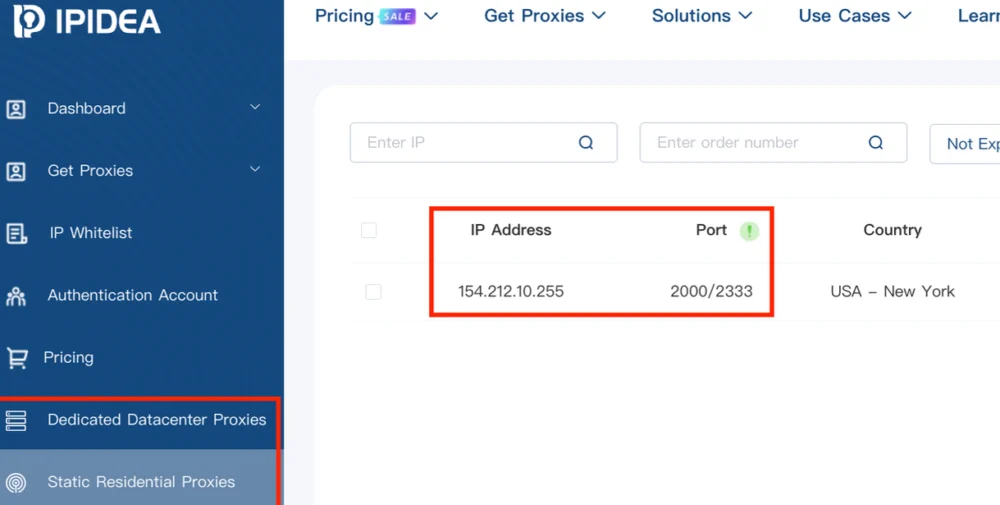
Kimwolf’s primary target for infection has been the Chinese-based residential proxy service, IPIDEA, which boasts millions of available proxy endpoints weekly. The operators of Kimwolf discovered a critical vulnerability: they could forward malicious commands to the internal networks connected to IPIDEA’s proxy endpoints. This allowed them to programmatically scan and infect other vulnerable devices residing on the same local network as these compromised proxy endpoints.
The vast majority of devices compromised through Kimwolf’s local network scanning capabilities have been unofficial Android TV streaming boxes. These devices, often based on the Android Open Source Project rather than the more secure Android TV OS or Play Protect certified Android devices, are typically marketed as a one-time purchase solution for accessing pirated video content from popular subscription streaming services. A significant concern is that many of these TV boxes come with residential proxy software pre-installed. Compounding this vulnerability, they often lack any robust security or authentication mechanisms, making them easily compromised by malware if direct communication is established.

While IPIDEA and other affected proxy providers have reportedly made efforts to block threats like Kimwolf from propagating upstream into their networks, with varying degrees of success, the Kimwolf malware continues to reside on millions of infected devices.
The intimate connection between Kimwolf, residential proxy networks, and compromised Android TV boxes might initially suggest a limited presence within corporate environments. However, recent findings from the security firm Infoblox paint a starkly different picture. A thorough review of their customer traffic revealed that an astonishing nearly 25 percent of their clients made a query to a Kimwolf-related domain name since October 1, 2025, the period when the botnet first began to emerge.
Infoblox’s analysis indicates that these affected customers are distributed globally and span a wide spectrum of industries, including education, healthcare, government, and finance. The firm clarified that this statistic signifies that nearly a quarter of their customers had at least one device acting as an endpoint for a residential proxy service targeted by Kimwolf operators. Such a device, potentially a smartphone or a laptop, could be co-opted by threat actors to scan the local network for vulnerable devices. Infoblox emphasized that a query indicates a scan was performed, not necessarily that new devices were successfully compromised. The success of this lateral movement would depend on the presence of vulnerable devices or the effectiveness of DNS resolution blocking.
Synthient, a startup specializing in tracking proxy services and the first to publicly disclose Kimwolf’s unique propagation methods on January 2nd, has observed an alarming number of IPIDEA proxy endpoints within government and academic institutions worldwide. Synthient’s research identified at least 33,000 affected internet addresses at universities and colleges, and nearly 8,000 IPIDEA proxies operating within various U.S. and international government networks.
In a webinar conducted on January 16th, experts from the proxy tracking service Spur delved deeper into internet addresses associated with IPIDEA and ten other proxy services suspected of being vulnerable to Kimwolf’s tactics. Spur’s investigation uncovered residential proxies present in approximately 300 government-owned and operated networks, 318 utility companies, 166 healthcare organizations or hospitals, and 141 companies within the banking and finance sectors.
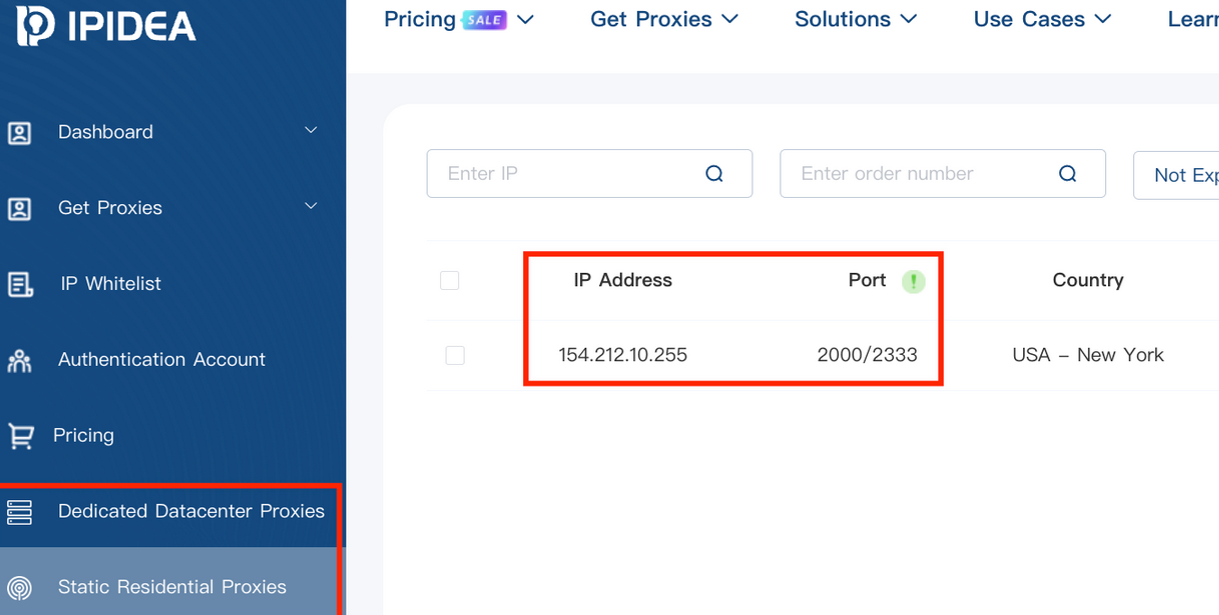
Riley Kilmer, Co-Founder of Spur, expressed significant concern regarding the presence of IPIDEA and similar proxy services within U.S. Department of Defense (DoD) networks, describing the situation as "terrifying." Kilmer speculated on how these enterprises might have configured their networks, suggesting that infected devices could potentially be segregated. However, he stressed the critical importance of awareness, noting that if a device has access to a proxy, then anything that device can access becomes accessible to the proxy.
Kilmer further highlighted Kimwolf’s demonstration of how a single residential proxy infection can rapidly escalate into substantial problems for organizations that harbor unsecured devices behind their firewalls. He explained that proxy services offer a deceptively simple pathway for attackers to probe other devices within an organization’s local network. "If you know you have [proxy] infections that are located in a company, you can choose that [network] to come out of and then locally pivot," Kilmer stated. "If you have an idea of where to start or look, now you have a foothold in a company or an enterprise based on just that."
This report marks the third in a series investigating the Kimwolf botnet. The upcoming installment will focus on the numerous individuals and companies based in China connected to the "Badbox 2.0 botnet." This collective designation refers to a vast array of Android TV streaming box models that are shipped with virtually no built-in security or authentication and come pre-installed with residential proxy malware.
Further Reading:
- The Kimwolf Botnet is Stalking Your Local Network
- Who Benefitted from the Aisuru and Kimwolf Botnets?
- A Broken System Fueling Botnets (Synthient)