The incident came to light on a Saturday, prompting IoTeX to issue a public statement via X (formerly Twitter), confirming that its dedicated team was "fully engaged, working around the clock to assess and contain the situation." The project emphasized its immediate response, indicating that while investigations were ongoing, preliminary assessments suggested the actual financial impact might be lower than some of the more sensational figures circulating within the crypto community. In a swift and coordinated effort to mitigate further damage and pursue recovery, IoTeX disclosed that it had already engaged with major cryptocurrency exchanges and established security partners. This collaboration aims to meticulously trace the movement of the potentially stolen funds and implement freezing mechanisms to prevent the attacker from liquidating or further dispersing the assets. "The situation is under control. We will continue to monitor closely and provide timely updates to the community," the project assured its stakeholders, aiming to instill confidence amidst the uncertainty.
The immediate market reaction to the news was discernible, with IoTeX’s native token, IOTX, experiencing a notable decline. Data from CoinMarketCap revealed an over 8% drop in the token’s price within a 24-hour window, settling around $0.0049. Such a rapid depreciation underscores the fragility of investor sentiment in the face of security vulnerabilities, particularly in the volatile cryptocurrency market where trust and perceived security are paramount. A token safe, in the context of a decentralized protocol like IoTeX, refers to a secure digital vault or multi-signature wallet designed to hold significant amounts of a project’s treasury, development funds, or other critical assets. The "unusual activity" typically signals unauthorized access or transactions that deviate from established operational norms, triggering immediate security protocols. For a decentralized identity protocol, which inherently relies on robust security and trust to manage sensitive user data and credentials on the blockchain, such an incident represents a significant challenge to its core value proposition.
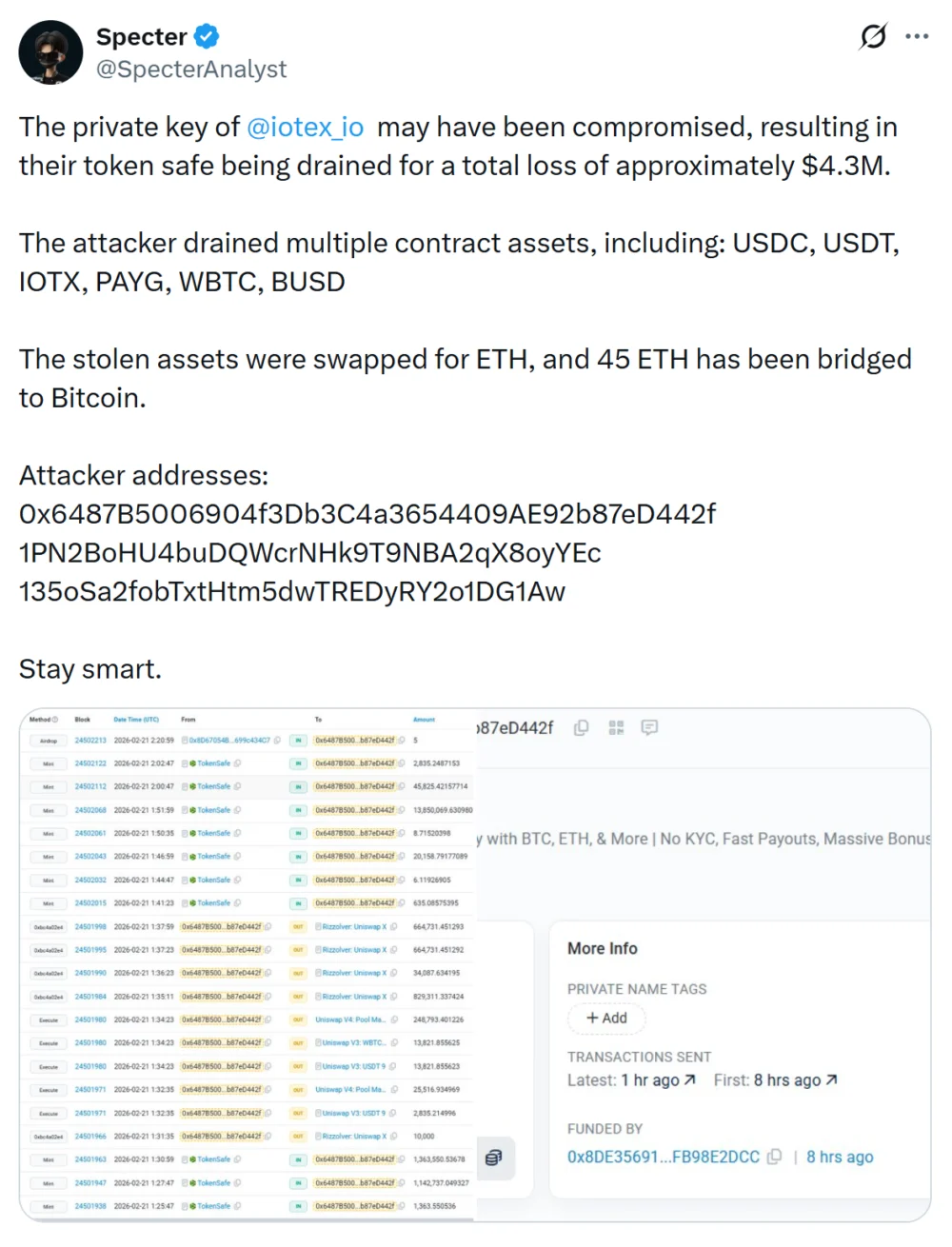
The official confirmation from IoTeX followed compelling claims from Specter, a renowned onchain investigator. Specter’s meticulous analysis pointed to a compromised private key associated with the affected token safe as the root cause of the breach. A private key is a highly sensitive, cryptographic code that grants full access and control over cryptocurrency assets stored in a digital wallet. Its compromise is akin to a physical key to a bank vault falling into the wrong hands, granting the perpetrator unfettered access to all linked assets. The onchain sleuth’s investigation revealed a multi-asset drain from the compromised wallet, encompassing a range of significant cryptocurrencies. These included USDC (USDC) and USDt (USDT), both prominent stablecoins pegged to the U.S. dollar, as well as IoTeX’s native token (IOTX) and wrapped Bitcoin (WBTC), a tokenized version of Bitcoin on other blockchains. The estimated total loss from these drained assets was approximately $4.3 million, a figure that stood in stark contrast to IoTeX’s initial assessment of "lower than circulating rumors," highlighting the potential for differing methodologies or ongoing investigations to yield varied estimates.
Specter’s analysis further detailed the attacker’s sophisticated post-heist strategy. The stolen funds were reportedly swapped into Ether (ETH), the native cryptocurrency of the Ethereum blockchain, known for its high liquidity and extensive decentralized finance (DeFi) ecosystem. Following this conversion, approximately 45 ETH was then bridged to the Bitcoin network. This multi-stage process of swapping assets and bridging them across different blockchains is a common tactic employed by sophisticated attackers to obscure the trail of funds, complicate tracing efforts, and make recovery significantly more challenging for law enforcement and security teams. Bitcoin, being the most decentralized and liquid cryptocurrency, often serves as a final destination for illicitly obtained funds, offering a degree of anonymity that attackers seek.
To substantiate the claims, the analyst publicly disclosed wallet addresses believed to be associated with the attacker, alongside granular transaction records. These records illustrated a pattern of rapid asset movements through various decentralized exchanges (DEXs) and successive token swaps. Such frenetic activity strongly suggested a deliberate and urgent attempt by the attacker to quickly convert the diverse stolen assets into more liquid and harder-to-trace cryptocurrencies, subsequently moving them across multiple blockchain networks to fragment the funds and create a complex web of transactions. This strategy is designed to overwhelm traditional forensic analysis and make it exceedingly difficult for any single entity to freeze or seize the entire haul. The publication of these onchain artifacts by Specter provides invaluable data for security partners and exchanges working to track and potentially recover the stolen assets.
This incident, while specific to IoTeX, resonates with a disturbing trend of security breaches plaguing the broader Web3 ecosystem. The industry has witnessed numerous high-profile hacks and exploits, ranging from smart contract vulnerabilities to private key compromises, underscoring the constant battle against increasingly sophisticated attackers. For instance, previous reports by Cointelegraph highlighted how CertiK traced $63 million in Tornado Cash deposits to a $282 million wallet compromise, illustrating the use of privacy-enhancing mixers to launder funds. Similarly, the SwapNet exploit drained up to $13.3 million from Matcha Meta users, another stark reminder of the persistent threats faced by DeFi platforms and their users. These incidents collectively underscore the critical need for continuous security audits, robust infrastructure, and rapid incident response mechanisms within every project operating in the blockchain space.
A particularly sobering statistic underscores the gravity of such security breaches: nearly 80% of cryptocurrency projects that fall victim to major hacks struggle significantly to recover, and many never fully regain their footing. This alarming recovery rate, as highlighted by Web3 security leaders, is often less about the immediate financial damage and more about the subsequent mismanagement of the crisis. Mitchell Amador, CEO of Immunefi, a leading bug bounty platform, has frequently pointed out that many project teams are woefully unprepared for breaches. This lack of preparedness often translates into delayed decision-making, poor communication strategies during the critical early hours post-attack, and a general inability to handle the ensuing chaos. Such missteps can dramatically worsen the financial losses and, crucially, shatter user confidence – an irreparable blow for any project built on trust and community.
Alex Katz, CEO of Kerberus, further elaborated on the long-term repercussions, noting that serious exploits create a cascade of negative effects that extend far beyond the initial financial drain. The reputational damage alone can be catastrophic, leading to a mass exodus of users who withdraw their funds, fearing future vulnerabilities. This outflow directly results in declining liquidity across the project’s ecosystem, making it less attractive for new users and investors. The long-term credibility damage is perhaps the most insidious consequence, as it erodes the fundamental trust required for a decentralized project to thrive. Once trust is compromised, rebuilding it is an arduous, often insurmountable task. Projects frequently find themselves in a downward spiral, struggling to attract developers, partners, and users, ultimately leading to stagnation or outright failure.
In light of these challenges, the IoTeX incident serves as a crucial reminder for all participants in the Web3 space. For IoTeX itself, the path to full recovery will depend not only on its technical prowess in containing the breach and pursuing the attacker but also on its ability to demonstrate unwavering transparency and an ironclad commitment to security moving forward. Rebuilding trust will necessitate a detailed post-mortem analysis, clear communication of enhanced security measures, and potentially, the implementation of robust insurance policies or security bounties to prevent future occurrences. The broader implications for decentralized identity protocols are also significant; as these systems aim to become foundational infrastructure for the digital future, their security integrity must be beyond reproach. The ongoing battle against sophisticated attackers demands continuous innovation in security, proactive threat intelligence, and a collaborative effort across the entire crypto industry to safeguard user assets and foster a resilient, trustworthy digital economy. The IoTeX team’s promise to "monitor closely and provide timely updates" is therefore not just a statement of intent, but a critical imperative for its survival and the continued evolution of decentralized identity.