Allison Nixon, a cybersecurity researcher known for her relentless pursuit of cybercriminals, found herself in the crosshairs of the very individuals she sought to expose. For years, Nixon, as chief research officer at Unit 221B, a cyber investigations firm, had been instrumental in dismantling criminal networks, particularly those associated with "The Com," a loosely affiliated group of online entities responsible for widespread violence and hacking campaigns. Her work, often conducted discreetly through online channels or pseudonyms, had led to the arrest of dozens of their members. However, her success came at a price, and she soon became a target herself.
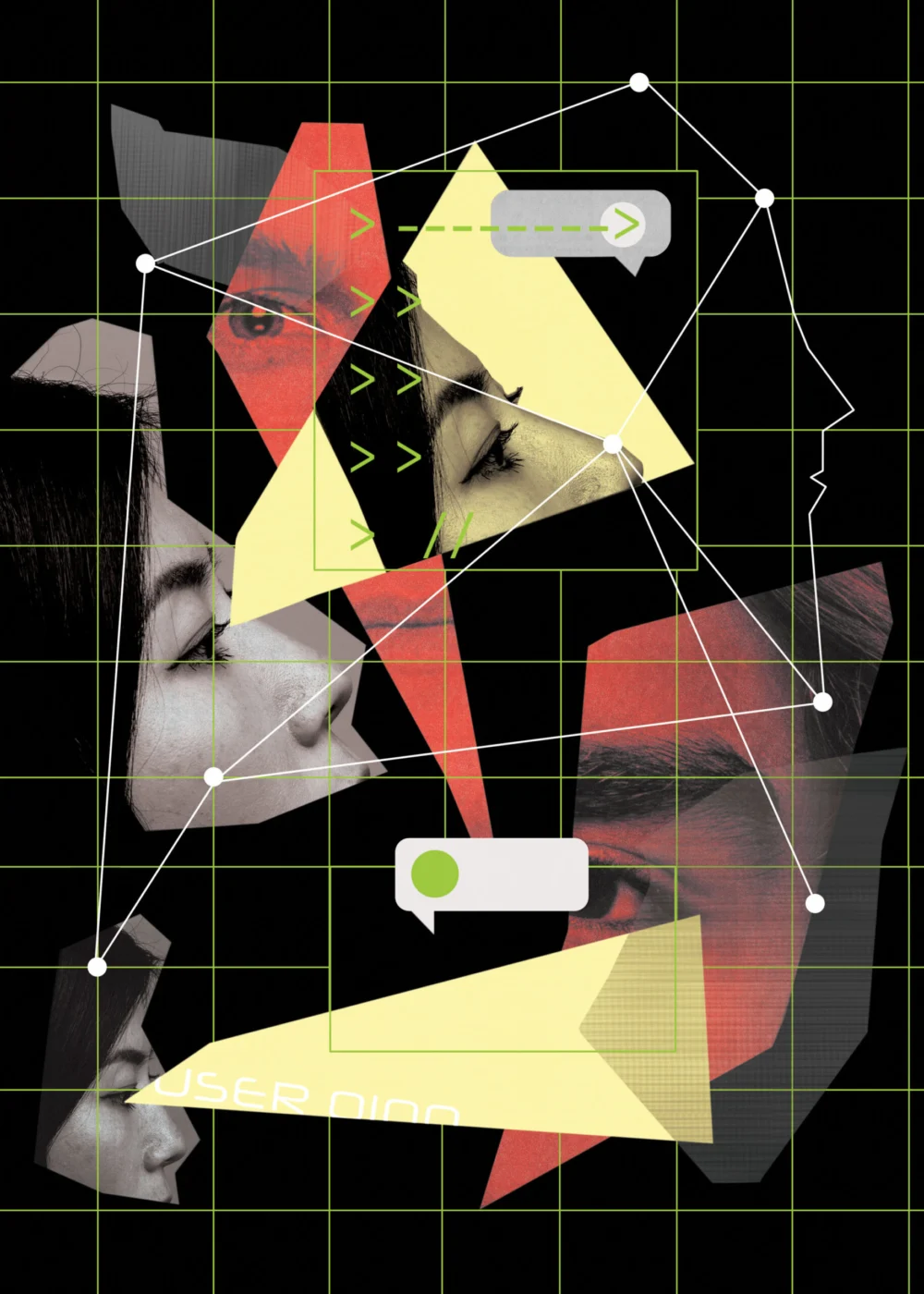
The threats began in April 2024, originating from anonymous online personas using handles like "Waifu" and "Judische" on platforms such as Telegram and Discord. These individuals issued chilling death threats against Nixon, employing violent and offensive language, including specific threats of gruesome harm. The harassment escalated with the creation and dissemination of AI-generated explicit images of Nixon, a clear attempt to intimidate and humiliate her.
Nixon’s dedication to cybersecurity began over a decade ago. While many in law enforcement and the cybersecurity community initially dismissed the Com and its members as mere teenagers engaged in childish pranks, Nixon recognized the burgeoning threat. She meticulously studied their activities, developing sophisticated strategies to unmask their online identities. Her early efforts allowed her to build a comprehensive understanding of their evolving tactics, from simple distributed denial-of-service (DDoS) attacks to more sophisticated SIM-swapping schemes, crypto theft, ransomware, and data breaches. This deep dive into their operations has been invaluable to law enforcement. Special Agent Ryan Brogan of the FBI attests to Nixon’s unparalleled skills, stating that she has helped identify and arrest over two dozen Com members since 2011. "If you get on Allison’s and my radar, you’re going [down]. It’s just a matter of time," Brogan remarked, emphasizing that no amount of digital anonymity can shield perpetrators from her persistent investigations.
Despite her extensive experience, Nixon was initially baffled by the sudden and intense hostility from the Waifu/Judische accounts. While she had previously spoken to the media about the Com, her interviews had focused on their broader impact, not on her specific efforts to bring their members to justice. The threats seemed to emerge from nowhere. Although she had briefly investigated the Waifu persona years prior due to his boasts about criminal activities, he had not been a current focus of her work when the threats began. This personal targeting, however, ignited a new resolve in Nixon: to unmask Waifu/Judische and hold them accountable for their admitted crimes. "Prior to them death-threatening me, I had no reason to pay attention to them," she stated.
The Com, a relatively unknown entity to the general public, represents a growing and significant threat. This online community, primarily composed of young individuals in North America and parts of Europe, has evolved into a formidable force in cybercrime. Unlike state-sponsored actors who are often constrained by international laws and the fear of retaliation, the anarchic nature of the Com allows its members to operate with a degree of impunity. Their criminal activities have escalated from disrupting websites to high-stakes operations like SIM swapping, which can hijack a victim’s phone service, and sophisticated crypto theft and data exfiltration. Major corporations such as AT&T, Microsoft, and Uber have been impacted by their campaigns. Beyond digital crimes, Com members have been implicated in offline violence, including kidnapping and physical assaults, and have even been linked to inciting or committing acts of extreme violence.
A cybersecurity researcher, who requested anonymity due to the sensitive nature of their work, likens the threat posed by the Com to that of major nation-states like Russia and China. This comparison stems not from their technological sophistication alone, but from their uninhibited approach to cyber operations, unbound by the international norms that govern state actors. "There’s only so far that China is willing to go; there’s only so far that Russia or North Korea is willing to go," the researcher explained, highlighting how fears of retaliation and adherence to international laws prevent states from unleashing their full cyber capabilities. The Com, however, operates without such inhibitions. The researcher also pointed out a common misconception: "It is a pretty significant threat, and people tend to… push it under the rug [because] it’s just a bunch of kids." Yet, the tangible impact of their actions, measured in staggering monetary losses, cannot be understated.

The Com does not operate from a single, centralized location. Instead, its members are dispersed across various web forums, Telegram channels, and Discord servers. This decentralized structure mirrors a lineage of online hacking subcultures that have emerged and evolved over the past two decades. Nixon likens this phenomenon to emerging from the "same primordial soup," tracing the Com’s roots back to "The Scene," an earlier community focused on pirating digital content.
Nixon’s deep dive into The Scene began in 2011, when its members were primarily engaged in hijacking gaming accounts, launching DDoS attacks, and operating booter services—tools that allow users to rent capacity for overwhelming servers with traffic. While financial gain was a motivator, notoriety was the primary driver. This dynamic shifted around 2018, coinciding with a surge in cryptocurrency values. The Com, also known as "the Community," emerged as a dominant subgroup within The Scene, redirecting its focus towards financial enrichment through cryptocurrency theft, data breaches, and extortion.
The COVID-19 pandemic further fueled the Com’s growth, a phenomenon Nixon attributes to a confluence of factors including social isolation, the forced migration of young people online for education, economic hardships, and persistent socialization challenges. Many Com members struggle to find employment due to a lack of skills or behavioral issues. A significant number have troubled home lives, face difficulties in adapting to school, and exhibit signs of mental illness. The Com provides a sense of camaraderie, support, and an outlet for their frustrations, while also offering a potential solution to their financial woes. This fertile ground has given rise to loosely knit cells such as Star Fraud, ShinyHunters, Scattered Spider, and Lapsus$, which collaborate on criminal enterprises, often targeting high-profile individuals and major tech companies, amassing millions through theft and extortion. The pursuit of dominance, power, and bragging rights remains a powerful motivator, even within profit-driven operations. The desire to "reach out and touch the people that think they’re untouchable" fuels their targeting of "big whales." Nixon observes that this ego-driven motivation often leads to impulsive decisions that ultimately undermine their financial schemes.
Allison Nixon, with her dark hair, wire-rimmed glasses, and unassuming demeanor, possesses a sharp intellect and an urgent drive to convey the gravity of the threats posed by groups like the Com. She speaks with a rapid cadence, her mind brimming with information she is eager to share. Her passion for her work is evident, and she takes evident satisfaction in seeing those she investigates brought to justice.
Her journey into cybersecurity investigations began in 2011 while working the night shift at SecureWorks. While her role involved responding to security alerts, Nixon harbored a desire to join the company’s counter-threats team, which focused on state-sponsored hacking groups. Lacking direct experience or connections, she carved her own path through sheer curiosity. Fascinated by the motivations and psychological drivers behind cybercriminal actions, she began exploring online forums where hackers congregated. A simple Google search for "hacking forums" led her to Hack Forums, a site where she was surprised to find members openly discussing their illicit activities. Her initial inquiries to a SecureWorks threat team member were met with dismissal; the site was deemed a haven for "script kiddies," or unskilled hackers.
This period saw a broader shift in cybersecurity focus away from cybercrime towards more sophisticated, state-sponsored hacking. However, Nixon’s inclination to explore uncharted territories was amplified by her colleague’s dismissiveness. Along with two other SecureWorks colleagues, she began studying these forums during their downtime, focusing on identifying individuals operating DDoS booters. Nixon found these forums remarkably accessible. Unlike threat intelligence teams requiring privileged access to victim networks, she could gather all the necessary information from public forums where hackers, under the illusion of anonymity, often made critical operational security (OPSEC) mistakes. These seemingly innocuous details—a city of residence, a school attended, a former workplace—when pieced together, could unravel the identities behind their online personas. "It was a shock to me that it was relatively easy to figure out who [they were]," she admitted.
Nixon found herself uniquely suited to the task, unbothered by the immature boasting and petty disputes that dominated these forums. "A lot of people don’t like to do this work of reading chat logs. I realize that this is a very uncommon thing. And maybe my brain is built a little weird that I’m willing to do this," she explained. "I have a special talent that I can wade through garbage and it doesn’t bother me."

She soon realized that not all forum members were mere script kiddies. Some demonstrated genuine ingenuity and "powerful" skills, which they were unfortunately applying to trivial purposes like hijacking gamer accounts. While researchers and law enforcement largely overlooked these activities, Nixon suspected they would eventually target more significant objectives—a prescient intuition. By the time these hackers moved on to more impactful crimes, Nixon had already amassed a substantial trove of data on them. Her DDoS research continued for two years until a pivotal moment in 2013 when cybersecurity journalist Brian Krebs was targeted in a swatting incident.
A collaborative effort involving around a dozen individuals from the security community, including Nixon, worked with Krebs to identify the perpetrator. Nixon was invited to contribute, analyzing pieces of the puzzle provided by Krebs. This investigation ultimately led to the identification of the culprit, although his arrest took another two years. Being invited to a dinner with Krebs and the other investigators marked a turning point for Nixon; she had found her community of like-minded individuals driven by a passion for the "love of the game."
Nixon’s next significant research focus emerged from an unexpected quarter: porn stars. In 2018, she observed a trend where social media accounts of adult film stars were being hijacked to promote crypto scams to their extensive follower bases. While the method of account hijacking remained elusive, Nixon offered her assistance to the affected actors in regaining control of their accounts, in exchange for access to their private messages during the period of compromise. These messages provided a crucial breakthrough, leading her to a forum where hackers discussed their methods. They had tricked some actors into revealing the mobile phone numbers of others, subsequently using a technique called SIM swapping to reset passwords for the social media accounts of these other stars, effectively locking them out.
SIM swapping involves redirecting a victim’s phone number to a SIM card controlled by the fraudster. This allows them to intercept calls and messages, including critical one-time security codes used for password resets and account verification. In some cases involving the porn stars, hackers manipulated telecom workers into performing SIM swaps under false pretenses, while in others, they bribed employees. This access enabled them to alter account passwords and exploit the compromised accounts for their crypto scams. Nixon was surprised by the relatively low-profit schemes these hackers pursued with such a powerful technique. At the time, SIM swapping was rarely employed for financial fraud, and, much like the earlier hackers on Hack Forums, these individuals seemed unaware of the full potential of the method they were using. Nixon anticipated this would change and that SIM swapping would soon become a major problem, prompting her to shift her research focus accordingly—a prediction that quickly materialized as fraudsters began to leverage the technique more aggressively.
Nixon’s ability to anticipate future trends has been a hallmark of her career. On numerous occasions, a hacker or hacking group would capture her attention for employing a novel hacking approach in a minor operation. She would then begin tracking their online communications, anticipating that they would eventually escalate to more significant activities. Her intuition proved consistently accurate. When these hackers later gained notoriety for impactful operations, they appeared to have emerged from obscurity to others, prompting investigations into their identities. However, Nixon would already possess a compiled dossier on them, and in some instances, had already unmasked their real identities. The Lizard Squad, for example, burst into headlines in 2014 and 2015 with a series of high-profile DDoS campaigns. However, Nixon and her colleagues had been monitoring its members individually for some time, leading the FBI to seek their assistance in identifying the group. "The thing about these young hackers is that they… keep going until they get arrested, but it takes years for them to get arrested," Nixon observed. "So a huge aspect of my career is just sitting on this information that has not been actioned [yet]."
During the Lizard Squad era, Nixon began developing tools to scrape and record hacker communications online. Years later, these tools would be applied to scrape the chatrooms and forums frequented by the Com. These channels contained a wealth of data that, while seemingly insignificant during a hacker’s nascent career, could prove critical for law enforcement investigations. However, this data was constantly at risk of deletion by Com members or takedown by law enforcement.
Nixon’s dedication to preserving this information led her to scrape and archive chatrooms she investigated over several years. It wasn’t until early 2020, upon joining Unit 221B, that she had the resources to systematically scrape the Telegram and Discord channels of the Com. She consolidated this data into a searchable platform accessible to other researchers and law enforcement. Unit 221B hired former hackers to assist in building the necessary scraping tools and infrastructure, resulting in eWitness, an exclusive, invitation-only platform. Initially seeded with Nixon’s own collected data, it has since been augmented by data scraped by other users, including information no longer available in public forums.

FBI Special Agent Ryan Brogan lauded eWitness as an invaluable tool, further enhanced by Nixon’s direct contributions. While other security firms also scrape criminal online spaces, they seldom share their findings. Brogan highlighted Nixon’s unique approach: her direct engagement with actors within chat spaces to elicit information that "would not be otherwise normally available." The data preservation project she initiated at Unit 221B coincided perfectly with the pandemic, the surge in Com membership, and the emergence of two concerning Com offshoots, CVLT and 764. She was able to capture their initial communications before law enforcement intervention led to the removal of their chat logs from public access. CVLT, pronounced "cult," reportedly emerged around 2019, focusing on sextortion and child sexual abuse material. 764, an offshoot of CVLT, was spearheaded by a 15-year-old named Bradley Cadenhead and focused on extremism and violence.
In 2021, Nixon’s observations of these groups led her to investigate sextortion practices within the Com. This form of sextortion has roots in activities dating back a decade, known as "fan signing," where hackers would extort individuals, often young women, into writing the hacker’s handle on a piece of paper as a trophy. This evolved into blackmailing victims into carving the hacker’s name onto their bodies or engaging in sexually explicit acts while being recorded. With CVLT, the demands escalated further, including carving names into skin or performing explicit acts for live-streaming. Nixon noted a concerning trend during the pandemic: a significant number of SIM swappers transitioned into involvement with child sexual abuse material and sadistic sextortion. While abhorrent, Nixon recognized an opportunity to leverage this for positive change. Frustrated by the lenient sentences often handed down to financial fraudsters due to the perceived non-violent nature of their crimes, she saw a path to secure harsher penalties by linking them to their sextortion activities.
It was at this juncture that Waifu, still not on Nixon’s immediate radar, would become entangled in her investigations. Waifu and his associates were implicated in a major hack involving AT&T customer call records in April 2024. Their group gained unauthorized access to numerous cloud accounts hosted by Snowflake, a data storage provider. One of these compromised accounts contained over 50 billion call logs from AT&T wireless subscribers. Among these records were call logs of FBI agents who were AT&T customers. Nixon and other researchers theorized that the hackers may have identified agent phone numbers through various means and then used reverse-lookup programs to identify the owners of numbers they called or that called them. Nixon’s number was among those identified, marking the beginning of her harassment.
Their recklessness escalated when they allegedly extorted nearly $400,000 from AT&T, promising to delete the stolen call records. Subsequently, they attempted to re-extort the telecom company, threatening to leak the records on social media if further payment was not made. They even tagged the FBI in their posts, a move Nixon described as "like they were begging to be investigated."
While the Snowflake breaches and AT&T data theft were making headlines, Nixon was unaware her number was among the stolen logs, nor that Waifu/Judische was a prime suspect. She was therefore perplexed by his sudden online taunting and threats. Over several weeks in May and June, a pattern emerged: Waifu or an associate would post a threat against Nixon, followed by an invitation to communicate online. Nixon surmised they believed she was assisting law enforcement in the Snowflake breach investigation and sought to draw her into dialogue to extract information about the authorities’ knowledge. However, Nixon was not yet collaborating with the FBI on that specific case. It was only after she began investigating Waifu for the threats that she became aware of his suspected involvement in the Snowflake hack.
This was not Nixon’s first encounter with Waifu. He had initially come to her attention in 2019 when he bragged about framing another Com member for a hoax bomb threat and later discussed his involvement in SIM-swapping operations. Waifu made a distinct impression on Nixon: he possessed clear technical skills, but also displayed immaturity, impulsivity, and emotional instability. His interactions within the Com were marked by a desperate need for attention. He boasted about his ability to hack through the night, fueled by Adderall and eschewing sleep. He was also notably reckless about protecting his personal information, revealing to another researcher that he lived in Canada, a claim that proved to be accurate, despite his assertion of superior OPSEC.
Nixon’s methodology for unmasking Waifu followed a general approach she employed for many Com members. She would cast a wide investigative net around a target and all associated online personas, then meticulously analyze their interactions to narrow the focus to individuals with the most significant connections. Often, the most valuable intelligence came from a target’s adversaries, whose online disputes revealed crucial details about their identity, personality, and activities. "The enemies and the ex-girlfriends, generally speaking, are the best [for gathering intelligence on a suspect]," she remarked with a hint of dark humor. "I love them."

During this period, Waifu and his group attempted to gather intelligence on Nixon by reaching out to other security researchers. They also attempted to mislead these researchers by planting false clues, mentioning other Canadian cybercriminals as potential suspects for Waifu’s activities. Nixon had not previously witnessed cybercriminals engaging in such sophisticated counterintelligence tactics. Amidst this subterfuge, Nixon and a collaborating researcher engaged in extensive consultation and cross-checking with other experts to verify the gathered clues, ensuring the accuracy of the information before sharing it with the FBI.
By July, Nixon and her collaborator were convinced they had identified their target: Connor Riley Moucka, a 25-year-old high school dropout residing with his grandfather in Ontario. On October 30, the Royal Canadian Mounted Police apprehended Moucka at his residence. According to an affidavit filed in Canadian court, a plainclothes officer visited Moucka’s home nine days prior to his arrest under a pretext. The officer secretly photographed Moucka, comparing it with an image provided by U.S. authorities. Moucka, appearing disheveled, opened the door and identified himself as "Alex," one of his aliases. Satisfied with the identification, the officer departed. During this period, Waifu’s online rants against Nixon intensified, as did his diversionary tactics. Nixon believes the police visit likely unnerved him.
Nixon declined to disclose the specific details of how Moucka was unmasked, stating only that he "made a mistake." Her reasoning was clear: "I don’t want to train these people in how to not get caught." The Canadian affidavit against Moucka revealed a disturbing array of alleged online threats beyond those directed at Nixon. These included musings about becoming a serial killer, plans to mail sodium nitrate pills to Black individuals in Michigan and Ohio, and intentions to obtain firearms to "kill Canadians" and provoke "suicide by cop." Prosecutors, listing Moucka’s aliases including Waifu and Judische, alleged that he and others extorted at least $2.5 million from at least three victims whose data they stole from Snowflake accounts. Moucka faces nearly two dozen charges, including conspiracy, unauthorized computer access, extortion, and wire fraud. He has pleaded not guilty and was extradited to the U.S. in July. His trial is scheduled for October, although hacking cases often conclude with plea agreements.
While authorities took months to arrest Moucka after Nixon and her colleague shared their findings, an alleged associate in the Snowflake conspiracy, U.S. Army soldier Cameron John Wagenius (known online as Kiberphant0m), was apprehended more swiftly. On November 10, 2024, Nixon’s team identified a mistake made by Wagenius, leading to his arrest on December 20. Wagenius has already pleaded guilty to two charges related to the sale or attempted sale of confidential phone records and is awaiting sentencing in March.
Nixon continues her investigation into sextortion practices within the Com. However, she notes that remaining members of Waifu’s group still taunt and threaten her. "They are continuing to persist in their nonsense, and they are getting taken out one by one," she stated, determined to continue her work "until there’s no one left on that side." Kim Zetter, a journalist specializing in cybersecurity and national security and author of "Countdown to Zero Day," contributed this report.