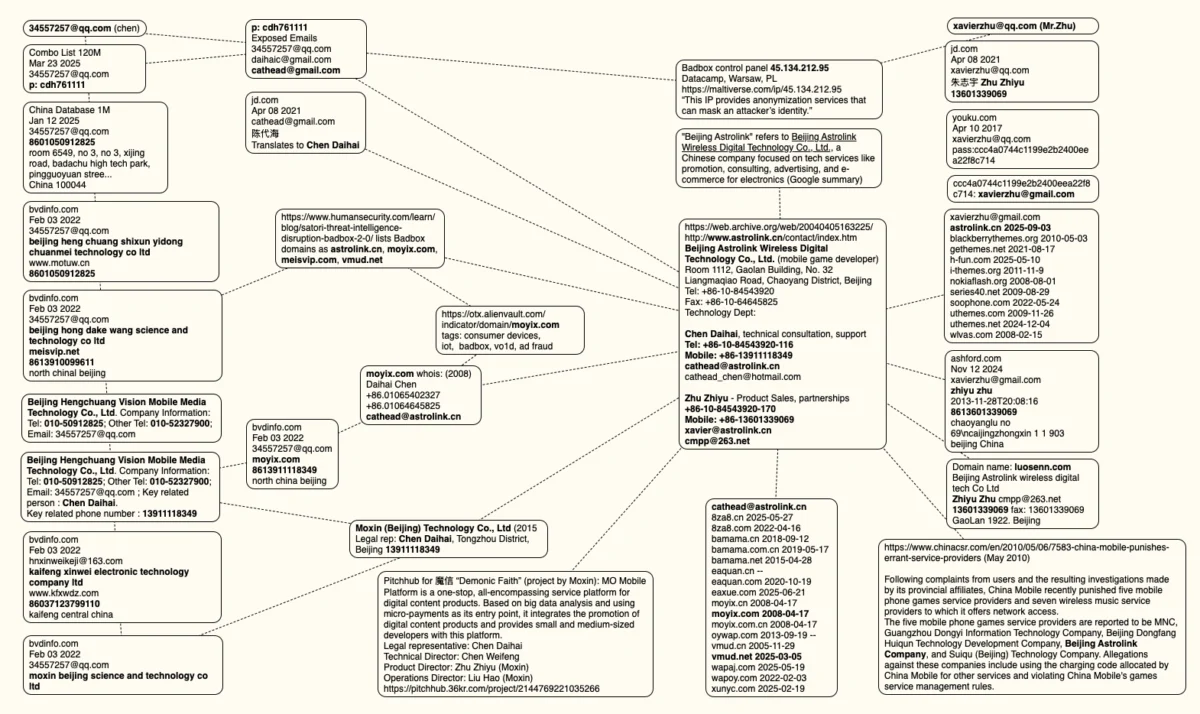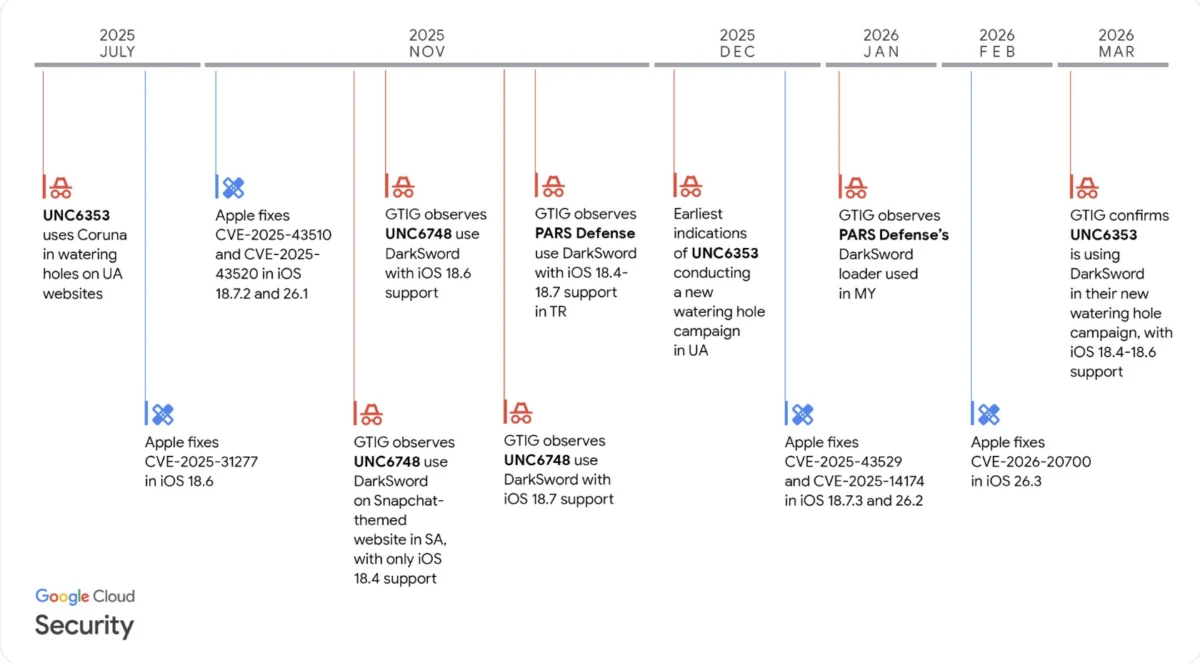
Ghostblade stands out due to its technical design and operational stealth. Written in JavaScript, a widely used web scripting language, it leverages browser-based vulnerabilities or deceptive tactics to initiate its rapid data theft capabilities. Once activated on a compromised iOS device, Ghostblade swiftly executes its malicious payload, siphoning sensitive data and immediately relaying it to command-and-control servers operated by the attackers. This rapid exfiltration mechanism is a key feature, allowing the malware to minimize its footprint and reduce the window of opportunity for detection by traditional security measures. The choice of JavaScript suggests an attack vector likely involving malicious websites, drive-by downloads, or sophisticated phishing campaigns that trick users into visiting compromised web pages or interacting with malicious scripts.
What makes Ghostblade particularly insidious is its design for evasion. According to Google Threat Intelligence researchers, this crypto-stealing malware does not operate continuously on the compromised device. Instead, it activates, performs its data extraction, and then ceases to function, remaining dormant until potentially re-triggered or until its objective is met. This intermittent operation makes it exceptionally difficult to detect through ongoing system monitoring or behavioral analysis, as it doesn’t leave a persistent, round-the-clock signature. Furthermore, the malware does not require the installation of additional plug-ins or extensions to function, simplifying its deployment and further reducing its detectable traces. Its ability to extract data and then ‘disappear’ makes forensic analysis a significant challenge for cybersecurity professionals attempting to trace its activity and understand its full scope.
Beyond its stealthy operational pattern, Ghostblade incorporates code specifically designed to delete crash reports from the compromised device. This seemingly minor detail has profound implications for cybersecurity. When an application or system component crashes, iOS typically generates a crash report that is, in many cases, automatically sent to Apple for analysis, aiding in the identification and patching of vulnerabilities. By systematically deleting these reports, Ghostblade effectively blinds Apple to its presence, preventing the company from receiving crucial telemetry that could flag the malicious software and accelerate the development of protective patches. This deliberate act of obfuscation demonstrates a high level of sophistication and a clear understanding of Apple’s diagnostic and security mechanisms by the threat actors behind DarkSword.

The scope of data accessible and exfiltrated by Ghostblade is alarmingly broad, painting a picture of comprehensive digital compromise. The malware can access and relay messaging data from popular communication applications, including Apple’s proprietary iMessage texting service, as well as third-party platforms like Telegram and WhatsApp. This access means that private conversations, sensitive shared information, and potentially even multi-factor authentication codes transmitted via these services could be intercepted. The implications for privacy and security are severe, opening doors to blackmail, identity theft, and further targeted attacks based on the content of these communications.
Moreover, the Google cybersecurity report details that Ghostblade can steal critical device and personal information beyond messaging data. This includes SIM card information, which can be leveraged for SIM-swapping attacks to gain control over phone numbers and associated accounts. It also targets identity data, which could encompass anything from personal identifiers to credentials, and multimedia data, potentially including photos and videos. Geolocation data, revealing the user’s physical movements and locations, is also vulnerable. Finally, the malware can access and potentially modify system settings, giving attackers a deeper foothold and greater control over the compromised device. The cumulative effect of such extensive data theft is devastating, exposing users to severe financial losses, identity fraud, and profound invasions of privacy.
DarkSword and its constituent components, like Ghostblade, represent the cutting edge of cyber threats identified by Google Threat researchers. Their discovery sheds critical light on the continually evolving methods employed by malicious actors to pilfer cryptocurrencies and other valuable digital assets from unsuspecting users. This ongoing arms race between attackers and defenders necessitates constant innovation in cybersecurity and proactive threat intelligence gathering from organizations like Google. The sophisticated nature of DarkSword suggests a well-resourced and highly skilled threat actor group, potentially state-sponsored or a major criminal enterprise, focusing on high-value targets or broad-scale exploitation.
This discovery also comes at a time when the overall landscape of crypto-related hacks is experiencing a notable shift. While the specific threat of Ghostblade is significant, broader trends in crypto losses suggest a pivot in attacker methodologies. Data from blockchain intelligence platform Nominis indicates that losses from crypto hacks in February fell sharply to $49 million, a significant decrease from the $385 million recorded in January. This reduction in direct code-based hacks on smart contracts or protocols reflects a crucial pivot from exploiting technical vulnerabilities to exploiting human error, a more insidious and often harder-to-defend vector.

Nominis’ report highlights a growing reliance on crypto phishing attempts, wallet poisoning attacks, and other social engineering tactics. These methods bypass the need for complex technical exploits by manipulating users themselves. Phishing, for instance, typically involves the creation of fake websites meticulously designed to mimic legitimate cryptocurrency exchanges, wallet services, or decentralized applications (dApps). These fraudulent sites often employ URLs that are nearly identical to their genuine counterparts, differing by only a single character or a subtle domain variation, effectively tricking users into believing they are on a trusted platform.
When an unsuspecting user accesses one of these fake websites, or clicks on an embedded element, the site can deploy malware (like Ghostblade, if delivered through a browser-based exploit), or, more commonly, prompt the user to input their private keys, seed phrases, or connect their wallet, thereby granting malicious actors direct access to their funds. These attacks often leverage a sense of urgency, fear, or greed, with scammers impersonating official support, offering fake airdrops, or warning of imminent account suspension to induce panicked compliance from victims.
Wallet poisoning is another increasingly prevalent tactic. This method involves malicious actors sending very small, often negligible, amounts of cryptocurrency to a victim’s wallet. The purpose is not to steal funds directly but to "poison" the transaction history with an address controlled by the attacker. Later, when the victim intends to send funds, they might inadvertently copy the attacker’s address from their transaction history instead of the legitimate recipient’s address, leading to funds being sent to the attacker. This relies on the victim’s habit of copying recent addresses and not meticulously verifying every single character of an address before confirming a transaction.
The shift towards exploiting human error emphasizes that even with robust underlying blockchain security and improved code auditing, the weakest link in the security chain often remains the individual user. Private users, in particular, bore the brunt of hacking, phishing, and other crypto-theft attempts in February, according to Nominis. This vulnerability stems from a combination of factors, including a lack of deep technical understanding of crypto security, susceptibility to social engineering, and the common human tendency to prioritize convenience over security.

To combat threats like Ghostblade and the broader spectrum of social engineering attacks, a multi-layered approach to security is paramount. For iOS users, maintaining the operating system and all applications up to date is crucial, as updates often include patches for newly discovered vulnerabilities. Users should exercise extreme caution when encountering unsolicited links, emails, or messages, even if they appear to come from trusted sources. Downloading applications exclusively from the official Apple App Store significantly reduces the risk of installing malicious software. Employing strong, unique passwords for all accounts and enabling two-factor authentication (2FA) wherever possible adds a critical layer of defense. Regularly reviewing app permissions and understanding what data applications are accessing can also help identify suspicious activity.
Against phishing and social engineering tactics, constant vigilance and education are the most powerful tools. Users must meticulously verify URLs before interacting with any website that requires wallet connection or sensitive information. Hardware wallets offer the strongest protection for storing cryptocurrencies, as private keys never leave the device. Never, under any circumstances, should private keys or seed phrases be shared with anyone or entered into any website. Users should cultivate a healthy skepticism towards unexpected offers, urgent alerts, or messages that pressure them into immediate action. Double-checking all transaction details, especially recipient addresses, before confirming any transfer is an essential habit. Furthermore, regularly revoking unnecessary token approvals for decentralized applications can mitigate the risk of approval scams. Utilizing reputable security tools, such as antivirus software and browser extensions that warn about known malicious sites, can provide an additional layer of protection.
The ongoing battle against cybercriminals is a dynamic one. While organizations like Google Threat Intelligence work tirelessly to identify and neutralize threats like Ghostblade and the DarkSword suite, the responsibility for individual security ultimately rests with the user. The evolution of attack vectors from complex code exploits to cunning psychological manipulation underscores that in the world of cryptocurrency, awareness, education, and proactive security measures are not just recommendations, but absolute necessities for safeguarding one’s digital assets and privacy.