North Korea-linked threat actors are significantly escalating their sophisticated social engineering campaigns, primarily targeting entities within the cryptocurrency and fintech sectors. These malicious operations involve the deployment of advanced new malware families specifically engineered to harvest sensitive data and illicitly acquire digital assets, posing an intensified threat to global financial security and individual investors alike. A recent campaign, meticulously tracked by cybersecurity experts, underscores the evolving tactics of these state-sponsored groups, showcasing a dangerous blend of artificial intelligence and human deception.
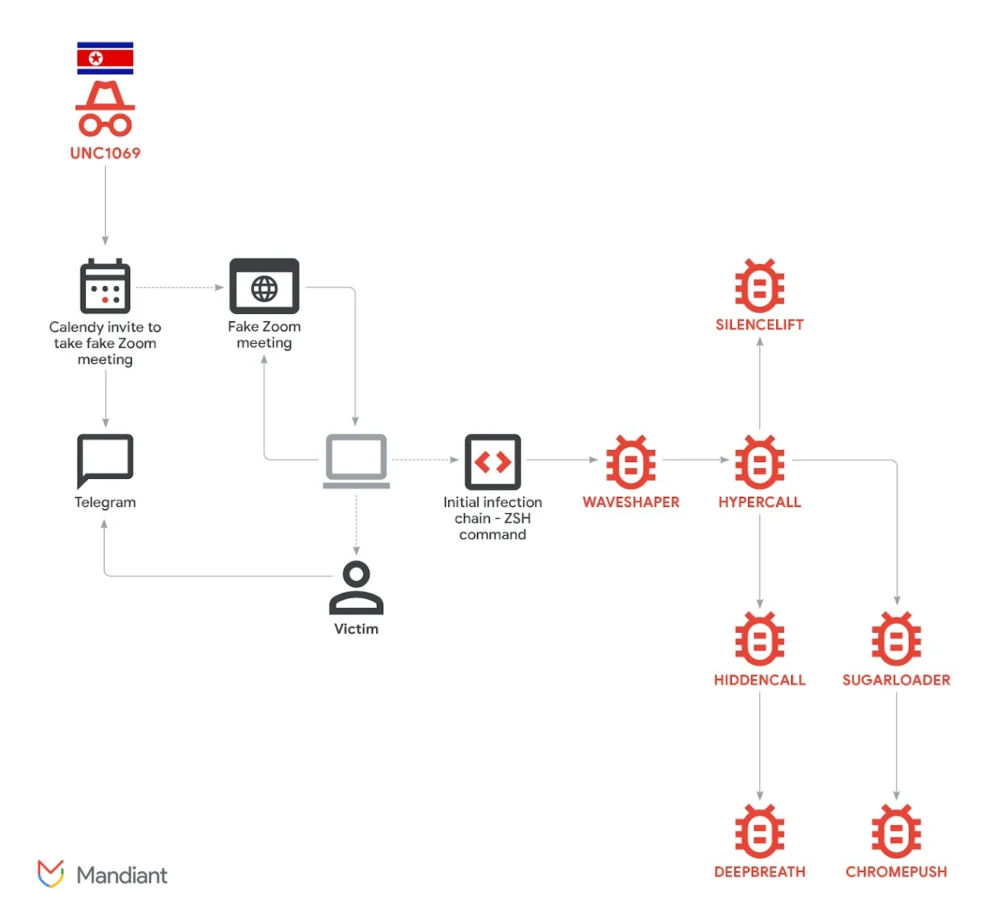
In a detailed report released by Mandiant, a leading US cybersecurity firm operating under Google Cloud, a threat cluster identified as UNC1069 was documented deploying no less than seven distinct malware families. The primary objective of these tools was the comprehensive capture and exfiltration of victim data. Mandiant’s findings, published earlier this week, highlight a tailored intrusion strategy that resulted in the introduction of a new suite of sophisticated tooling, including SILENCELIFT, DEEPBREATH, and CHROMEPUSH, all designed with specific capabilities to compromise host systems and extract valuable information.
The core of UNC1069’s success lies in its highly elaborate social engineering schemes. These campaigns often initiate through compromised Telegram accounts, leveraging trust and familiarity to engage targets. Once a rapport is established, victims are lured into fake Zoom meetings, a critical step where the attackers employ deepfake videos generated using advanced artificial intelligence tools. This innovative use of AI allows the threat actors to create convincing, albeit fabricated, video feeds, adding a layer of authenticity to their deceptive personas. During these bogus meetings, attackers frequently feign technical difficulties, such as audio problems, to manipulate victims into executing malicious commands under the guise of "troubleshooting."
This tactic, referred to as a "ClickFix attack," is particularly insidious. In one documented intrusion, a crypto founder’s compromised Telegram account was used to establish initial contact. The victim was then invited to a Zoom meeting where the attacker’s deepfake video feed purportedly experienced audio issues. The attacker then directed the unsuspecting user to run specific troubleshooting commands within their system. Unbeknownst to the victim, these seemingly innocuous commands contained an embedded, hidden instruction that initiated a full-blown infection chain. This single, stealthy command granted the attackers initial access, paving the way for the deployment of their sophisticated malware suite and subsequent data exfiltration. The psychological manipulation at play in these scenarios is profound, exploiting human empathy and a desire to be helpful, turning trust into a vulnerability.

Mandiant’s investigation revealed that this activity represents a notable expansion of UNC1069’s operational scope. While previously active, the group’s current efforts are primarily directed at a specific set of high-value targets: cryptocurrency firms, software developers, and venture capital companies. These entities are particularly attractive due to their direct access to digital assets, proprietary technology, and sensitive financial information. The malware deployed in these campaigns includes two newly identified and highly sophisticated data-mining viruses, CHROMEPUSH and DEEPBREATH. These tools are engineered to bypass critical operating system components, granting attackers deep access to personal data, system configurations, and ultimately, digital wallets and other valuable assets. SILENCELIFT, another key component, likely serves as a backdoor or loader, facilitating further compromise and persistent access.
The suspected North Korean ties of UNC1069 have been a subject of Mandiant’s tracking since 2018. However, the recent integration of AI advancements has significantly bolstered the malicious actor’s capabilities. For the first time, in November 2025 (as reported by Google Threat Intelligence Group), the group incorporated "AI-enabled lures in active operations," marking a dangerous new frontier in state-sponsored cyber warfare. This signifies a strategic pivot, leveraging the power of artificial intelligence to make social engineering more convincing, scalable, and difficult to detect. AI tools can generate hyper-realistic profiles, craft contextually relevant phishing messages, and create deepfake media that can fool even vigilant individuals, blurring the lines between reality and deception.
The persistent threat posed by North Korea-linked illicit actors to both crypto investors and Web3-native companies cannot be overstated. These state-sponsored hacking groups, collectively known for their aggressive and financially motivated cyber operations, include infamous entities like the Lazarus Group, Kimsuky, and APT38 (also known as Bluenoroff). Their primary motivation is to circumvent international sanctions and generate revenue for the North Korean regime’s weapons programs, particularly its nuclear and ballistic missile development. Cryptocurrency, with its decentralized nature and perceived anonymity, offers a convenient pathway for these groups to launder stolen funds and finance their illicit activities.
Historical incidents underscore the magnitude of this threat. In June 2025, a detailed Cointelegraph report highlighted how four North Korean operatives successfully infiltrated multiple crypto firms by posing as freelance developers. This elaborate scheme resulted in the theft of a cumulative $900,000 from these unsuspecting startups. These "fake IT workers" are part of a broader network, as highlighted by Binance CEO Changpeng "CZ" Zhao, whose "SEAL" team uncovered approximately 60 such individuals linked to North Korea, actively seeking employment within the crypto industry to gain insider access and facilitate future attacks.

Earlier in the same year, the notorious Lazarus Group, a prominent North Korean state-sponsored hacking entity, was linked to one of the largest crypto thefts on record, a staggering $1.4 billion hack. While the specific details of this particular breach were complex, it served as a stark reminder of the group’s capabilities and its relentless pursuit of digital assets. Other significant incidents attributed to North Korea include the $625 million Ronin Bridge hack in March 2022 and the $100 million Harmony Horizon Bridge exploit in June 2022, further illustrating the scale and sophistication of their operations. These attacks not only result in massive financial losses but also erode trust in the nascent Web3 ecosystem.
The use of compromised accounts, particularly from prominent figures like crypto founders, serves as a powerful initial vector. Once an attacker gains control of such an account, they can leverage the established reputation and network of the individual to launch highly credible social engineering attacks, making their deepfake-enabled Zoom calls and ClickFix scams far more effective. The victimology map provided by Mandiant and Google Cloud visually illustrates the widespread nature of these targeting efforts, encompassing various roles and companies within the crypto and tech landscapes.
To counter these evolving threats, robust cybersecurity measures are paramount. For individuals and companies operating in the crypto and fintech space, vigilance is no longer enough; proactive and adaptive defense strategies are crucial. This includes implementing strong multi-factor authentication (MFA) across all platforms, especially for sensitive accounts. Comprehensive security awareness training for all employees is essential to educate them about the latest social engineering tactics, including deepfakes, phishing, and ClickFix attacks. Organizations must scrutinize all unsolicited contact, verify identities through independent channels, and be inherently suspicious of unusual requests, particularly those involving system commands or software installations. Regular software updates and patching vulnerabilities are also critical, as is investing in advanced threat intelligence services that can provide early warnings about new malware families and attack vectors. The ongoing collaboration between cybersecurity firms like Mandiant and intelligence agencies is vital in dismantling these sophisticated networks and protecting the digital economy from state-sponsored threats.
In conclusion, the deployment of new crypto malware by North Korea-linked hackers, spearheaded by groups like UNC1069, signifies a dangerous escalation in cyber warfare. Their innovative use of AI-generated deepfakes and insidious social engineering tactics like ClickFix attacks presents a formidable challenge to the cybersecurity landscape. As these threat actors continue to evolve their methods to fund the North Korean regime, a concerted effort involving enhanced security protocols, continuous vigilance, and international cooperation remains the only effective defense against this persistent and ever-growing threat to digital assets and the broader financial ecosystem.